Major Cyberattacks in Review: February 2023
As we enter March 2023, the world continues to face a surge in cyberattacks that threaten individuals, businesses, and government agencies. The last month has already witnessed some of the most significant cyber incidents, including data breaches and ransomware attacks that have impacted millions of people and organizations worldwide.
As the threat landscape continues to evolve, it is crucial to understand the nature of these cyberattacks, their implications, and the measures taken to mitigate their impact.
This blog post will look closely at some of the major cyberattacks in February 2023.
Threat Actors Stole the Source Code of GoDaddy for 3 Years
Major web host provider GoDaddy has revealed a multi-year attack on its cPanel shared hosting environment, which is thought to have been conducted by a highly skilled threat actor group. The attackers stole source code and installed malware on the company’s servers. Customers complaining that their sites were being used for arbitrary domain redirection led to the breach’s discovery in December 2022. GoDaddy has linked the breach to previous ones reported in November 2021 and March 2020. Additionally, the company has found proof that the same group has targeted other hosting providers globally in an effort to infect websites and servers with malware.
31M Indians Are at Risk of Identity Theft
RailYatri, an Indian Railways ticketing platform, experienced a data breach due to a misconfigured Elasticsearch server which was open to the public without a password or other security authentication. A cybersecurity expert discovered the issue in February 2020 and reported it to RailYatri, which initially denied ownership of the data. The server had over 700,000 logs with over 37 million entries.
The company called Indian Computer Emergency Response Team in 2020. After that, they managed to secure the data. However, on February 16, 2023, a new leak post was made on a hacker forum. The leaked data include email addresses, full names, genders, phone numbers, locations, and 37,000 invoices, which could expose users to identity theft and phishing.
Cloudflare Blocks Record-Breaking DDoS Attack Targeting Websites on its Platform
Cloudflare has reported blocking a record-breaking distributed denial-of-service (DDoS) attack that peaked at over 71 million requests per second (RPS) and targeted websites secured by its platform.
The attack used a botnet comprising over 30,000 IP addresses belonging to numerous cloud providers.
A well-known gaming provider, cryptocurrency firms, hosting companies, and cloud computing platforms were among the websites that were targeted.
Cloudflare recorded a 79% increase in HTTP DDoS attacks year-over-year in Q4 2022, and volumetric attacks lasting more than three hours surged by 87% compared to the previous three months.
Threat actors are using DDoS attacks to demand ransom payments from victims in Bitcoin. The major targeted verticals were aviation, education, gaming, hospitality, and telecom industries. Georgia, Belize, and San Marino were among the top countries targeted by HTTP DDoS attacks in Q4 2022.
Israeli university Technion hit by DarkBit ransomware group demanding $1.7M

Technion Institute of Technology, a leading research university in Israel, has been hit by a cyberattack launched by a new ransomware group called DarkBit. The attack has caused the Institute’s websites to be inaccessible.
The attackers left a ransom note demanding $1.7 million and promoting anti-Israel messaging, while the university blocked all communication networks in response to the attack.
The incident is currently under investigation, and while the attack may impact the university’s cyber systems, campus operations continue as usual.
You can read our Education Threat Landscape Report to learn more about cyberattacks targeting the education industry.
Ransomware Attack Affects Over 3M Patients in California

Several medical groups in California have informed over three million patients that threat actors may have stolen their sensitive health and personal data in a ransomware attack that occurred around December 1, 2022.
Regal Medical Group, Lakeside Medical Organization, ADOC Medical Group, and Greater Covina Medical were among the Southern California healthcare organizations affected.
The US Department of Health and Human Services is investigating the incident, which impacted 3,300,638 individuals.
The stolen information included patients’ social security numbers, addresses, diagnosis and treatment information, laboratory test results, prescription data, and more.
Ransomware gangs often target healthcare facilities because they assume they will pay the ransom, and it is unclear who is responsible for this attack.
Reddit Falls Victim to Phishing Attack, Leading to Unauthorized Access Of Internal Systems

On February 5, Reddit was attacked with a phishing scam, which allowed unauthorized access to internal systems, code, and documents.
In the phishing attack, attackers redirected an employee to a fake website resembling Reddit’s intranet portal to obtain their credentials and 2FA tokens. An attacker accessed Reddit’s internal systems with that employee’s credentials.
Reddit has suggested that users change their passwords and keep an eye out for any suspicious activity. Reddit’s announcement is available here.
Weee! Food Delivery Service Suffers Data Breach Exposing 11 Million Customer Records

The personal information of 11 million Weee! food delivery service customers were exposed to a data breach.
On February 6, the data was leaked by the threat actor “IntelBroker” on a breach forum. Weee! reported that the breach did not include payment information but exposed details such as names, email addresses, phone numbers, device operating system, order notes, dates, and delivery types of customers who ordered between July 12, 2021, and July 12, 2022.
To check if your information has been compromised and leaked online, you can visit SOCRadar Labs’ Account Breach.
Data Breach Exposes Personal Information of 20M Users of TruthFinder and Instant Checkmate
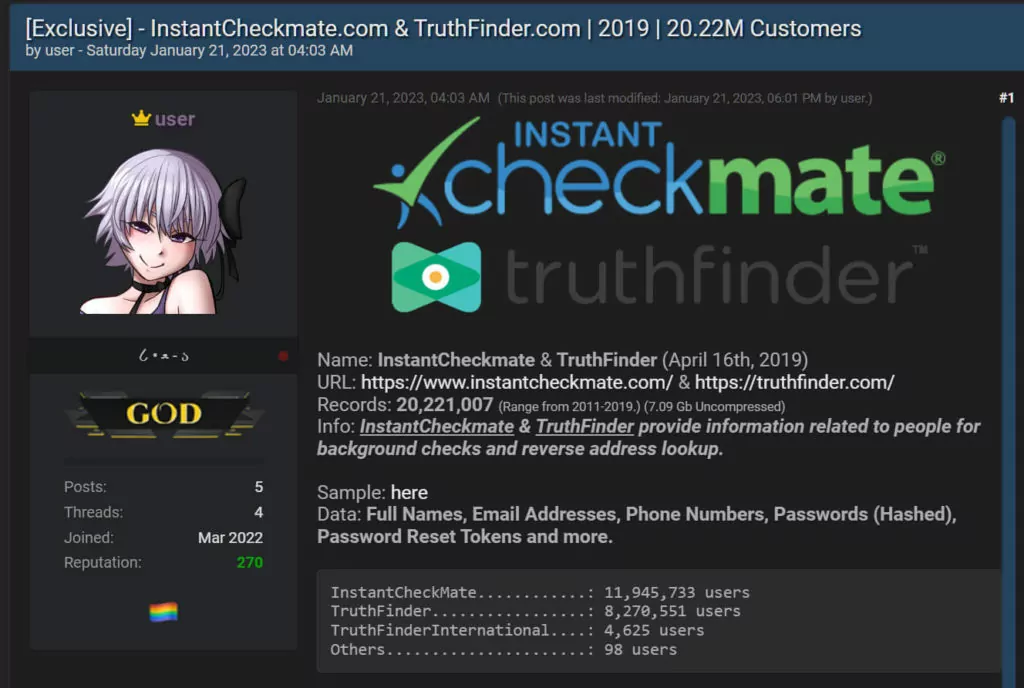
PeopleConnect, the holding company of background check services TruthFinder and Instant Checkmate, has disclosed a data breach in which hackers stole a backup database containing the personal data of 20 million users.
The exposed records were obtained prior to the backup’s creation in 2019 and were shared in the form of two 2.9 GB CSV files. The extracted dataset is 7 GB and includes various types of personal information, such as full names, phone numbers, email addresses, password hashes, and password reset tokens.




































