
Microsoft Reveals How Storm-0558 Acquired the Signing Key: They Stole From a Crash Dump
Microsoft previously disclosed the successful thwarting of an attack orchestrated by Storm-0558, a threat actor based in China. The breach, reported on June 16, 2023, allowed the threat actors to infiltrate Microsoft accounts by exploiting consumer signing keys as their point of entry.
Storm-0558 has gained notoriety for primarily targeting government agencies in Western Europe, with its activities focusing on espionage, data exfiltration, and the acquisition of crucial credentials.
Most recently, Microsoft has released the results of the technical investigation it has been conducting. This update outlines the precise methods employed by the attackers during the breach. In this blog post, we will provide an overview of Microsoft’s findings.
Background of the Storm-0558 Attack
Initiated on May 15, 2023, the attack had repercussions on around 25 organizations, including government agencies and the associated consumer accounts of individuals connected to these entities.
The attack itself revolved around the exploitation of forged authentication tokens, facilitated by the illicit acquisition of a Microsoft account (MSA) consumer signing key. Utilizing these counterfeit tokens, the Storm-0558 attackers successfully breached customer email accounts through Outlook Web Access (OWA) and Outlook. Their tactics also exploited a token validation vulnerability, enabling them to impersonate Azure AD users and thereby gain access to enterprise email systems.
In response to this threat, Microsoft swiftly took action by blocking the use of forged tokens, replacing the compromised key, and engaging in collaborative efforts with the affected organizations to resolve the issue.
For more details on this incident, refer to our initial blog post on the subject: Joint CISA and FBI Advisory: APT Activity Targeting Outlook Online
How Did Storm-0558 Access the MSA Signing Key?
While investigating the method by which attackers gained access to the consumer signing key, Microsoft uncovered that threat actors had stolen it from a Windows crash dump.
Following a crash in the consumer signing system in April 2021, the MSA key was inadvertently leaked into a crash dump. A Microsoft engineer’s account had access to the debugging environment, which contained the crash dump with the key. Storm-0558 actors gained access to the dump after compromising the engineer’s corporate account.
Microsoft states that although crash dumps should not contain the signing key, a race condition allowed the key to be leaked into the crash dump.
Microsoft further states that, due to log retention policies, they do not have logs with specific evidence of the key’s exfiltration. Regardless, this is the most likely method by which Storm-0558 obtained the key.
Read Microsoft’s investigation results here for more details.
How Did Microsoft Respond to Storm-0558 Attacks?
Microsoft has taken several steps to address the situation. They have revoked all valid MSA signing keys and resolved the race condition issue responsible for the key’s inadvertent exposure in a crash dump.
In addition, Microsoft has bolstered its security measures with the following enhancements:
- Strengthened prevention, detection, and response for key material inadvertently included in crash dumps.
- Improved credential scanning to better identify the presence of the signing key in the debugging environment.
- Released enhanced libraries designed to automate key scope validation within authentication libraries and provided clarifications in related documentation.
For a comprehensive understanding of the additional measures implemented by Microsoft for MSA management, please refer to the full analysis.
Enhancing Security with SOCRadar
The CISA and FBI advisory from July 12, 2023 emphasizes improving organizational cybersecurity through recommended logging practices and enabling audit logging. Regular password resets, in addition to monitoring audit logs, can help to strengthen security measures.
In addition to these vital practices, SOCRadar offers a solution for proactive threat mitigation. The platform enables you to monitor the latest activities of threat actors, malware, and APT groups, allowing you to stay one step ahead of their malicious intentions with timely intelligence.
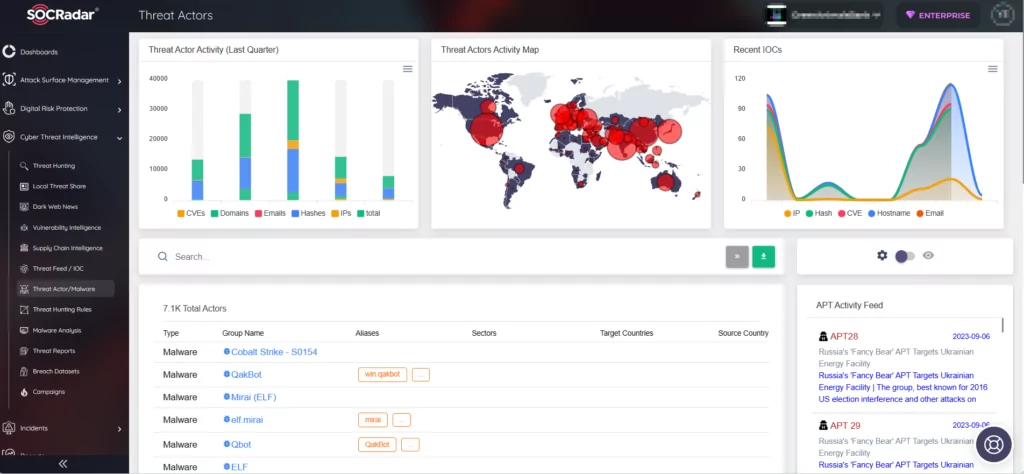
Leveraging the intelligence offered by the platform empowers you to effectively combat the threats posed by malicious actors and preempt their exploitation.



































