
Microsoft’s May 2023 Patch Tuesday Addresses Three Zero-Day Vulnerabilities
Microsoft has released the May 2023 Patch Tuesday update and it addresses 40 security vulnerabilities. The patch addresses six critical vulnerabilities and three zero-day vulnerabilities, two of which are actively exploited.
The following is a list of vulnerability types covered in May’s Patch Tuesday:
- 12 Remote Code Execution (RCE) Vulnerabilities
- 9 Elevation of Privilege Vulnerabilities
- 8 Information Disclosure Vulnerabilities
- 5 Denial of Service (DoS) Vulnerabilities
- 5 Security Feature Bypass Vulnerabilities
- 1 Spoofing Vulnerability
Three Zero-Days Patched in Microsoft’s Update
This month, Microsoft’s Patch Tuesday addresses three zero-day vulnerabilities, one of which has been publicly disclosed, and two have been actively exploited in attacks.
The actively exploited zero-day vulnerabilities are:
- CVE-2023-29336 (CVSS Score: 7.8): This vulnerability is found in the Win32k Kernel driver, which allows attackers to elevate privileges to SYSTEM, Windows’ highest user privilege level. The vulnerability has been actively exploited, but there are no details on how it was abused.
- CVE-2023-24932 (CVSS Score: 6.7): This vulnerability is a Secure Boot bypass flaw used by a threat actor to install the BlackLotus UEFI bootkit. An attacker with physical access or administrative rights to a target device can exploit this vulnerability by installing an affected boot policy.
UEFI bootkits are a type of malware that infects a computer’s firmware and cannot be detected by security software because it loads during the initial stages of the booting process. A particular bootkit called BlackLotus has been available for purchase on hacker forums since October 2022, and its features have been evolving. In March, a report from ESET revealed that the malware was improved to bypass Secure Boot even on fully patched Windows 11 operating systems.
Microsoft has recently issued guidance on how to detect BlackLotus UEFI bootkit attacks and has released a security update to fix the vulnerability used by the bootkit. However, this update is not enabled by default, and additional steps are needed to mitigate the vulnerability. This vulnerability is a bypass for the previously fixed CVE-2022-21894 vulnerability.
Microsoft has also fixed one publicly disclosed zero-day vulnerability that was not actively exploited:
- CVE-2023-29325 (CVSS Score: 8.1): This vulnerability is found in Microsoft Outlook’s Windows OLE feature, which allows attackers to execute remote code on the victim’s machine by sending a specially crafted email. The exploit works when the victim opens the email with an affected version of Microsoft Outlook software or previews it in the Outlook application. However, the attacker must win a ‘race’ condition and take additional actions to exploit the flaw successfully.
Critical Vulnerabilities of May Patch Tuesday
The critical vulnerabilities addressed in May Patch Tuesday are described below:
- CVE-2023-24943 (CVSS score: 9.8): An attacker could send a specially crafted file over the network to achieve remote code execution when the Windows Message Queuing service is running in a PGM Server (Pragmatic General Multicast) environment. Because only PGM is vulnerable to CVE-2023-24943, Microsoft recommends that customers deploy and use newer technologies to mitigate the risk, such as Unicast or Multicast servers.
- CVE-2023-24941 (CVSS score: 9.8): An unauthenticated attacker could exploit CVE-2023-24941 over the network by making a specially crafted call to a Network File System (NFS) service, which would result in remote code execution. Mitigation methods for this vulnerability are available on Microsoft’s official update guide.
- CVE-2023-28283 (CVSS score: 8.1): The vulnerability could let an unauthenticated attacker perform code execution via a specially crafted set of LDAP (Lightweight Directory Access Protocol) calls, allowing them to execute remote code within the context of the LDAP service.
- CVE-2023-24903 (CVSS score: 8.1): An attacker could send a specially crafted malicious SSTP packet to an SSTP (Secure Socket Tunneling Protocol) server to exploit this vulnerability and achieve remote code execution on the server side.
- CVE-2023-24955 (CVSS score: 7.2): This critical vulnerability affects the SharePoint Server and, according to Microsoft, could allow an authenticated attacker to execute remote code as a Site Owner in a network-based attack.
Recommendations
We strongly recommend applying the patches as soon as possible to ensure the security of your environment. If you are currently unable to patch your vulnerable products, check for mitigation options provided by the vendor. For further information regarding the vulnerabilities mentioned in this update, see Microsoft’s Release Note.
Receive Alerts for Vulnerabilities with SOCRadar
SOCRadar’s Vulnerability Intelligence can provide further protection by identifying and monitoring potential security concerns such as vulnerabilities.
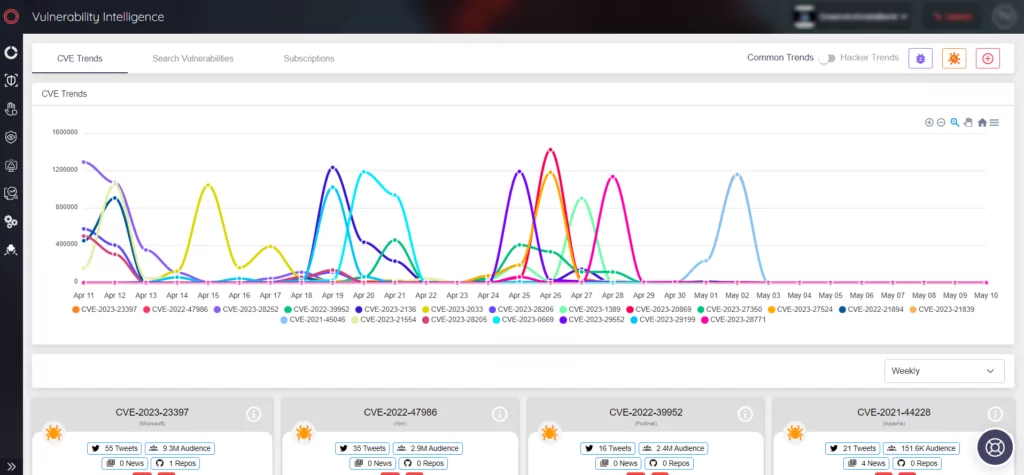
The platform provides actionable insights that can improve security measures and assist with patch management. To learn more and stay up-to-date on the latest vulnerabilities, sign up for a demo of SOCRadar platform.




































