
New DDoS Service, Microsoft Defender Vulnerability, Network Access to Indian Bank, Princeton University Data Leak
In the last week, SOCRadar’s Dark Web Team uncovered critical developments, including a new DDoS service that claims Cloudflare evasion and advanced techniques. Illicit network access is up for sale for an Indian bank, and there is an alleged data leak from a U.S. university. Additionally, an article shared on a dark web forum details a Microsoft Defender vulnerability, enabling arbitrary code execution through PowerShell commands.
Get your free Dark Web Report and find out if your data has been compromised.
New DDOS Service is Detected
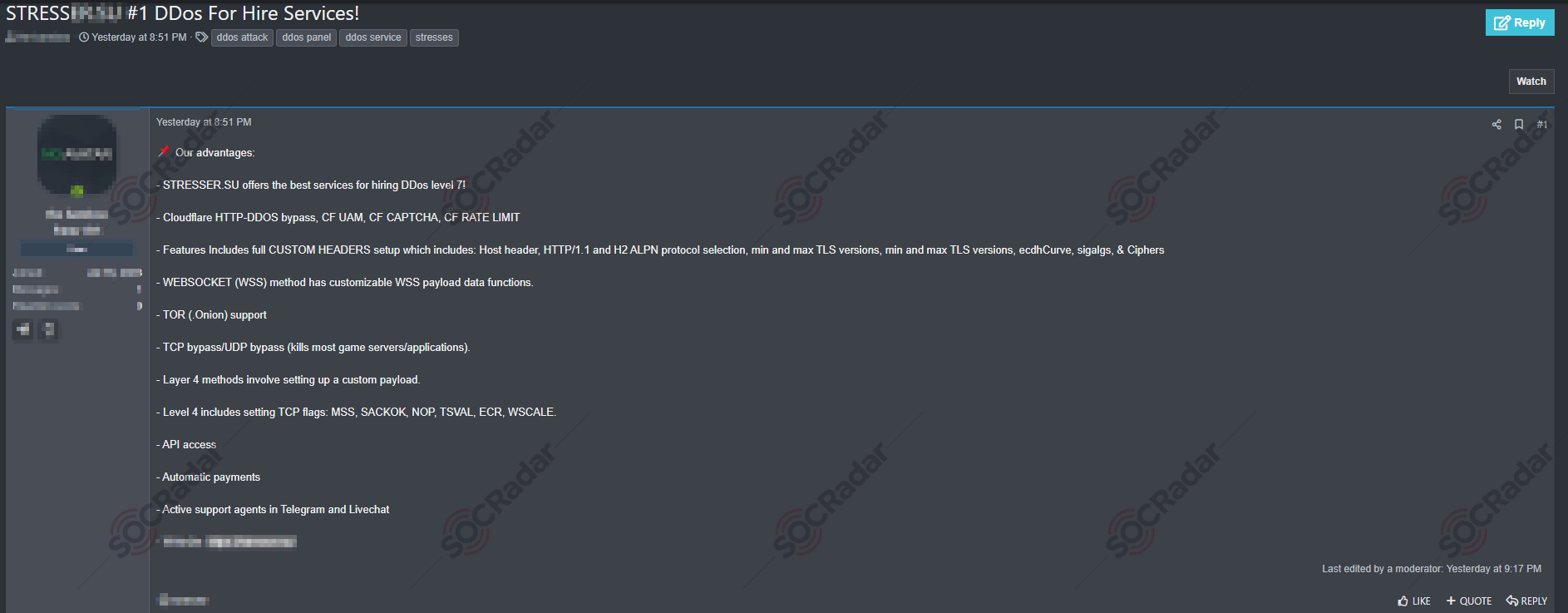
A threat actor on a hacker forum has announced a new DDoS service, STRESSER[.]SU, boasting high-level capabilities like Cloudflare bypassing, custom headers setup, and WebSocket method with customizable payloads. They claim to support the TOR network and offer advanced TCP/UDP bypass techniques, impacting game servers and applications. Additionally, the service features Layer 4 attack options with detailed TCP flag settings, API access, automatic payments, and active support through Telegram and live chat.
Unauthorized Network Access Sale is Detected for an Indian Bank
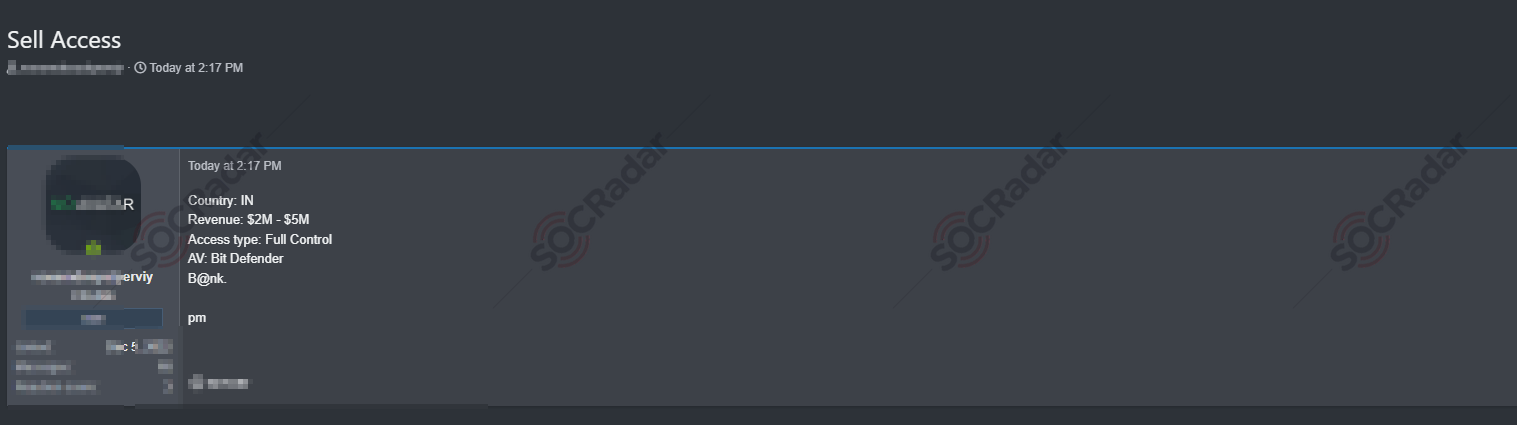
The SOCRadar Dark Web Team has detected the sale of unauthorized network access, allegedly belonging to an Indian bank with revenues between $2M and $5M. A threat actor on a hacker forum claims to offer “Full Control” access to this network, noting that the bank’s antivirus system is Bitdefender.
Data of Princeton University is Leaked
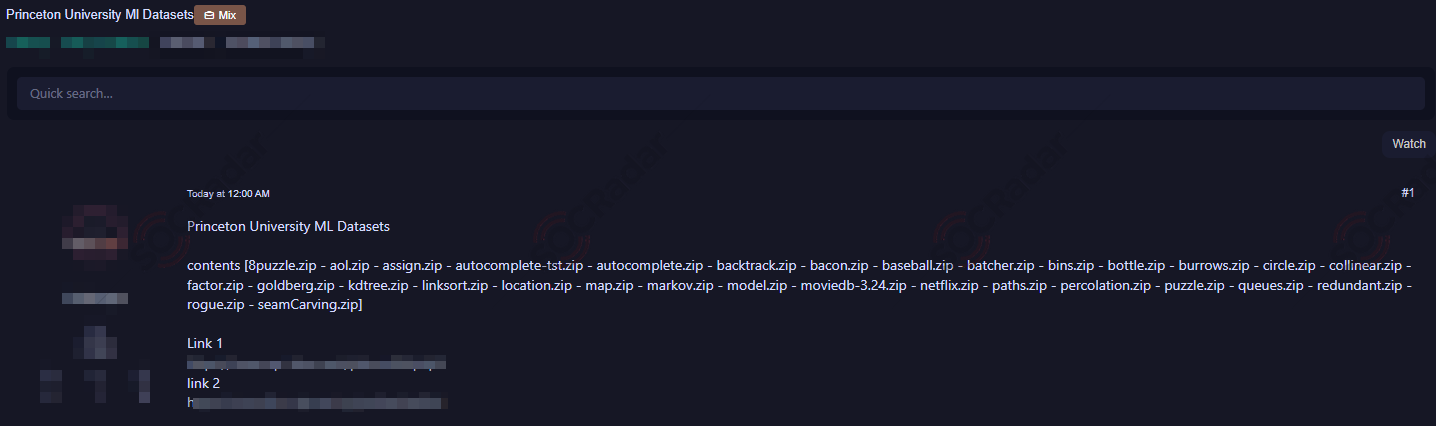
A new alleged data leak incident has been detected involving Princeton University. A threat actor on a hacker forum claims to have leaked various datasets, with file names indicating a wide range of subjects and applications.
An Article is Shared About Microsoft Defender API Arbitrary Code Execution Vulnerability
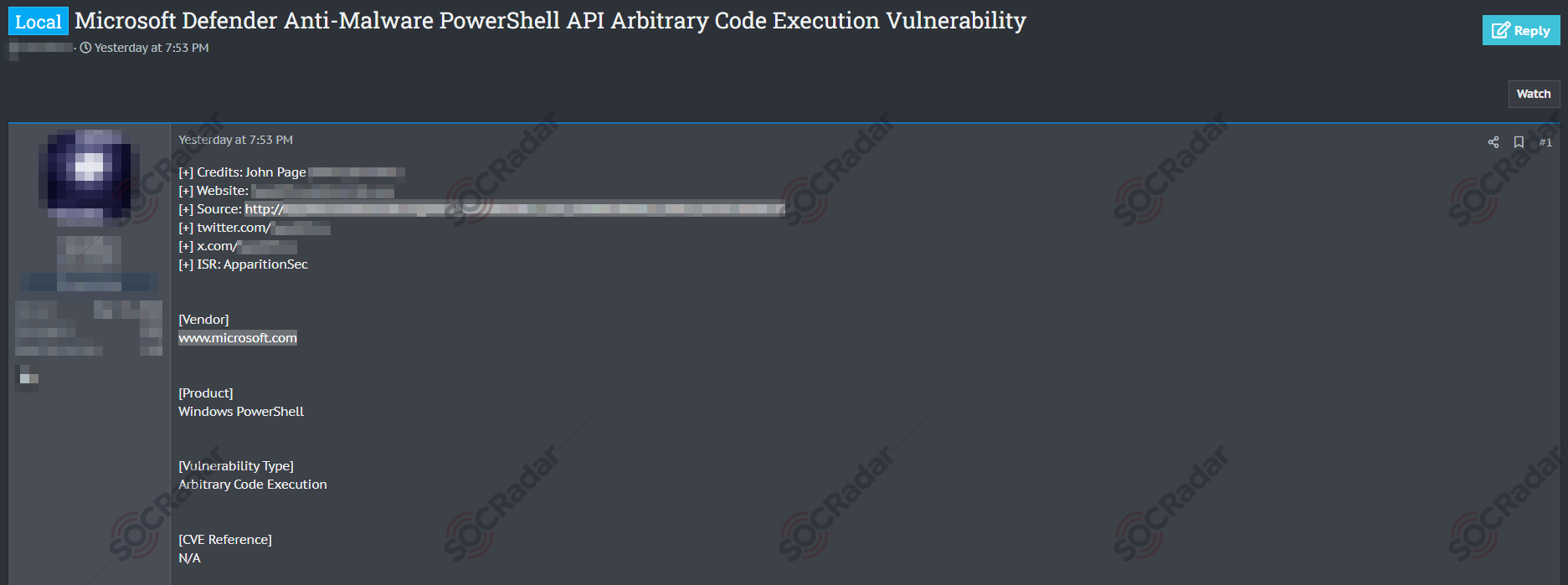
A recent article shared on a hacker forum has exposed a vulnerability in Microsoft Defender API, allowing arbitrary code execution. The issue involves Microsoft Defender Anti Malware and PowerShell APIs. The vulnerability can be exploited by manipulating PowerShell commands and requires an executable file with the same name as the parameter in a nearby location. Examples include using specific ‘powershell’ commands with strategically placed executable files, potentially leading to unintended code execution.
Powered by DarkMirror™
Gaining visibility into deep and dark web threats can be extremely useful from an actionable threat intelligence and digital risk protection perspective. However, monitoring all sources is simply not feasible, which can be time-consuming and challenging. One click-by-mistake can result in malware bot infection. To tackle these challenges, SOCRadar’s DarkMirror™ screen empowers your SOC team to follow up with the latest posts of threat actors and groups filtered by the targeted country or industry.



































