New Microsoft Exchange Zero-Day Vulnerabilities Could Lead to RCE, SSRF (ZDI-23-1578, ZDI-23-1579, ZDI-23-1580, ZDI-23-1581)
The discovery of four new zero-day vulnerabilities in Microsoft Exchange is raising concerns in the cybersecurity community. The vulnerabilities are high-severity, and pertain to Server-Side Request Forgery (SSRF) and Remote Code Execution (RCE) issues.

What Are the Vulnerabilities Affecting Microsoft Exchange?
All four of the zero-day vulnerabilities were uncovered by Piotr Bazydlo of the Trend Micro Zero Day Initiative (ZDI), which has opted for public disclosure in line with its responsible disclosure policy.
The ZDI advisory notes that these Microsoft Exchange vulnerabilities require authentication for successful exploitation, presenting a challenge for potential attackers. Nevertheless, it is important to acknowledge that threat actors can acquire credentials through various means, such as phishing, to meet this prerequisite.
Let’s explore the specifics of each vulnerability:
ZDI-23-1578 (Severity: 7.5, High): It is described as an Untrusted Data Deserialization vulnerability, which leads to Remote Code Execution. It occurs due to the ChainedSerializationBinder class failing to adequately validate user-supplied input, granting threat actors the opportunity to execute code on affected versions of Microsoft Exchange, operating within the SYSTEM context.
ZDI-23-1579 (Severity: 7.1, High): This vulnerability is described as a Server-Side Request Forgery (SSRF) issue. It resides in the DownloadDataFromUri method, which lacks proper URI validation before allowing access to resources, making it exploitable by threat actors to access sensitive information on affected Microsoft Exchange servers.
ZDI-23-1580 (Severity: 7.1, High): Identified as another Server-Side Request Forgery (SSRF) vulnerability, it pertains to the DownloadDataFromOfficeMarketPlace method, which fails to enforce proper URI validation. As a result, malicious actors can exploit it to gain unauthorized access to resources and sensitive information on impacted Microsoft Exchange servers.
ZDI-23-1581 (Severity: 7.1, High): It is the third Server-Side Request Forgery (SSRF) vulnerability found in Microsoft Exchange, among other zero-day vulnerabilities that were mentioned. It is associated with the CreateAttachmentFromUri method, which lacks the necessary URI validation before accessing resources. Threat actors can take advantage of this security vulnerability to access and retrieve sensitive information from affected Microsoft Exchange servers.
Are Patches Available?
Microsoft Exchange currently lacks official patches to address these security vulnerabilities. According to Microsoft, the severity of these vulnerabilities does not necessitate immediate patching, primarily due to their authentication requirement for further exploitation. The company stated they will make patches available in versions and updates as they deem appropriate.
How Can SOCRadar Help?
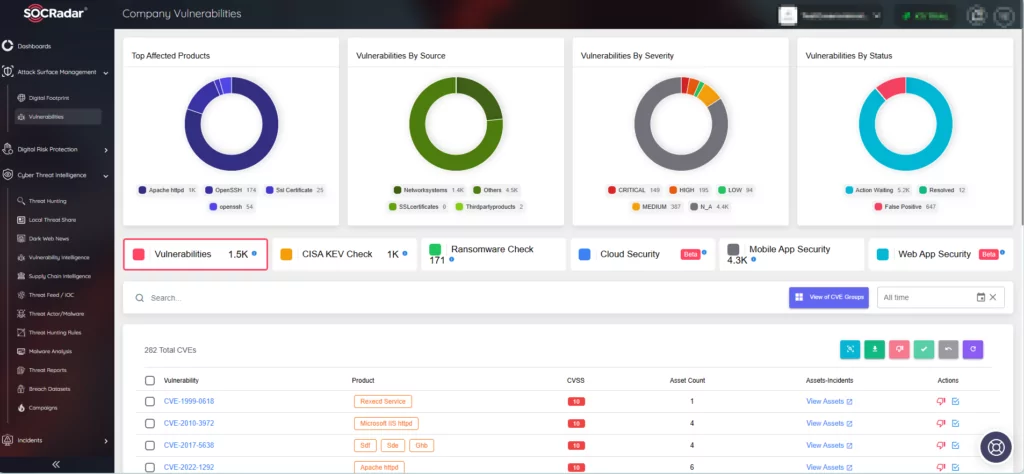
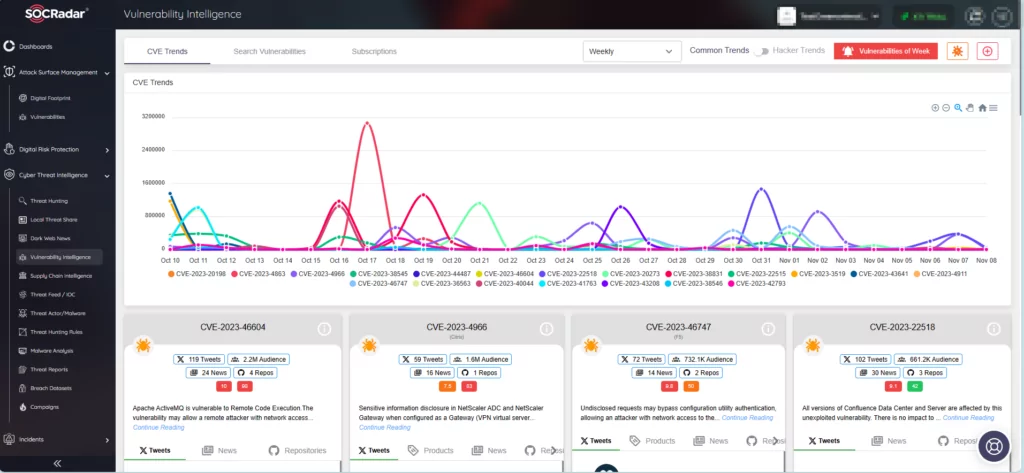
SOCRadar, equipped with its Attack Surface Management (ASM) module and Vulnerability Intelligence feature, empowers organizations to proactively address emerging threats and safeguards them from becoming a threat actor’s target.
The Vulnerability Intelligence module hosts a wealth of vulnerability information, continuously updated with the latest data, including available exploits and resources. Within the platform, you can track the entire lifecycle of vulnerabilities, from their exploitation to the availability of patches.
The Attack Surface Management module ensures constant monitoring of your digital assets. It promptly notifies your organization if it is vulnerable to identified vulnerabilities. SOCRadar’s timely alerts enable you to take proactive steps in mitigating potential risks.