
The Intricate Relationship Between Cybercrime and Cryptocurrency
In the digital age, cryptocurrency has been nothing short of revolutionary, promising a future of financial transactions that are faster, more secure, and unbound by traditional banking constraints. Yet, as with any innovation, there is a flip side. The attributes that make cryptocurrencies appealing to investors and consumers — decentralization, anonymity, and security — have also made them a weapon of choice for cybercriminals.
For cybercriminals, managing money has always posed a dilemma. Cybercriminals, distanced from their targets, cannot rely on physical cash. Traditional banks are risky, leaving traces that could lead to arrest. Instead, they’ve opted for alternatives like various online services, which offer transactions without the need for bank accounts or credit cards, maintaining their questionable anonymity. When cryptocurrencies emerged, they swiftly gained notoriety as a prime tool for cybercriminals upon their inception. Their rapid embrace by the underworld of cyberattacks is largely attributed to the anonymity they afford.
This blog post delves into the complex interplay between the burgeoning world of digital currencies and the shadowy realm of cybercrime, exploring how the latter exploits the former and what it means for the future of online security.
Anonymity and Decentralization
Cryptocurrencies, by design, offer anonymity attractive to those wishing to keep their financial activities private. However, this anonymity also provides a cover for cybercriminals, allowing them to execute fraudulent schemes, from ransomware to identity theft, with a reduced risk of detection.
While decentralization is celebrated for democratizing financial systems, it poses significant challenges for cybersecurity. Without a centralized system to monitor and regulate transactions, cybercriminals can operate with greater impunity, easily moving illicit funds across borders.
So much so that a Europol employee even stated that when Monero, a cryptocurrency unit, platform, and TOR were used together, investigations were blocked at a certain point. But in what scenarios does this anonymity help threat actors?
The Use of Cryptocurrency in Cybercrime
The first Dark Web Markets, such as Silk Road, which was founded in 2011 and can be considered the pioneer of Dark Web Markets, accepted Bitcoin as the payment method. Moreover, a few months after the launch of Silk Road, Bitcoin prices increased by 30 times, an issue that seemed too related to be a coincidence. Later, Monero ranked second after Bitcoin as one of the payment methods in these illegal markets. So, cryptocurrencies have been used extensively in the cybercrime landscape for over a decade.
Furthermore, the cryptocurrencies are becoming more private each day. Monero is especially renowned for its enhanced privacy features, particularly its utilization of “ring signatures” in transaction obfuscation, setting it apart from other cryptocurrencies. In this mechanism, when a user initiates a transaction, their signature is blended with those of other users, introducing ambiguity and making it substantially difficult for blockchain analysis to trace back the transaction. So, In addition to being a coin, its platform also works like a mixer in itself.
A mechanism that has the potential to provide such privacy naturally paves the way for some of the biggest cyber threats of recent years.
- Ransomware
One of the most notorious uses of cryptocurrency in cybercrime is ransomware. Ransomware attacks, one of today’s most important cyber security problems, especially for organizations, have also increased in parallel with the rise of cryptocurrencies. In ransomware attacks, victims’ data is encrypted by malicious software, and a ransom is demanded, typically in Bitcoin or other cryptocurrencies, exploiting the currencies’ untraceable nature.

LockBit’s leak website. Ransomware groups even have guides on “How To Buy a Cryptocurrency” on their leak websites.
We can even see this relationship in the decrease in ransomware revenues when the cryptocurrency volume decreases. Estimates suggest that since November 2021, the value of cryptocurrencies has plummeted by $2 trillion. Concurrently, expenses linked to cybercrimes, including ransomware demands and financial fraud, have seen a downturn.
- The Dark Web
The Dark Web, a part of the internet not indexed by traditional search engines and accessed only through special means like TOR Browser, uses cryptocurrencies as its currency of choice, as mentioned above. The dark web facilitates many underground markets and forums for illegal goods and services, all transacted through cryptocurrencies.
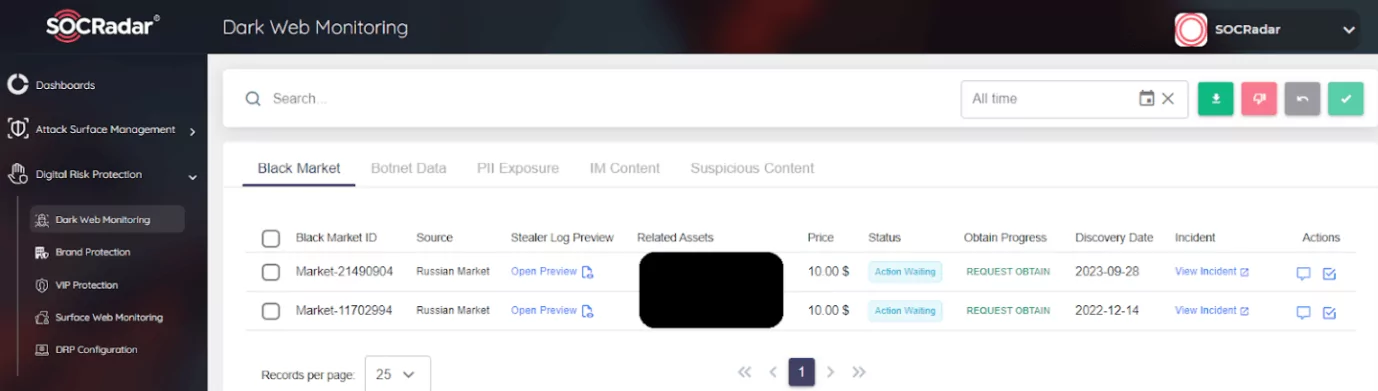
SOCRadar Dark Web Monitoring: Marketplaces are also monitored by SOCRadar.
Modern Dark Web Marketplaces are especially heavily reliant on cryptocurrency transactions, particularly Bitcoin, which some experts believe helps sustain the cryptocurrency market. For instance, the old Hydra Market’s trading volume soared to $5 billion over seven years up to 2022, with black market activities contributing $2.1 billion to the crypto market in 2021 alone.
Not Just a Tool But Also a Target
Cryptocurrency platforms and wallets, with their high-value contents, are prime targets for theft, experiencing numerous security breaches. Moreover, crypto mining, which is fundamental to the cryptocurrency ecosystem, akin to its very minting process, presents another avenue for earning digital currency.
Crypto platforms are targeted by hackers.
- Cryptojacking
Cryptojacking is the unauthorized use of someone else’s computer to mine cryptocurrency. It’s a silent and insidious form of cybercrime that can go undetected for extended periods, siphoning off processing power and electricity from unsuspecting victims. This section will dissect the mechanics of cryptojacking, its implications for individuals and businesses, and the broader impact on the digital ecosystem.
Cryptojacking operates by embedding malicious scripts into websites or distributing malware through phishing attacks. Once a computer or even a cloud computer, a digital asset, is infected, it begins mining cryptocurrency for the cybercriminals, often resulting in performance degradation and increased energy costs for the victim.
The extensive surface of infection arises from the inherently inclusive nature of cryptocurrencies. For instance, Monero’s ability to be mined using standard CPUs is a deliberate design choice rooted in the concept of democratizing cryptocurrency.
The prevalence of cryptojacking has grown in tandem with the rise of cryptocurrency’s popularity. This part will explore statistics and studies that shed light on the extent of cryptojacking and its position as a favored tactic among cybercriminals due to its low-risk and high-reward nature.
Cryptocurrency Laundry
We examined possible use cases in cybercrime and discussed where they provide anonymity, but the complexity does not end there. Cryptocurrency laundry stands out as a critical process wherein tumblers and mixers play a pivotal role. These services are specifically designed to obfuscate the origins of illicitly obtained cryptocurrencies, thereby complicating efforts to trace and combat cybercrime.
Tumblers and mixers operate by disassociating the identities of cryptocurrency holders from their transactions. When cybercriminals acquire cryptocurrencies illegally, they risk being tracked through the blockchain. Tumblers and mixers mitigate this risk by pooling and scrambling disparate cryptocurrency holdings.
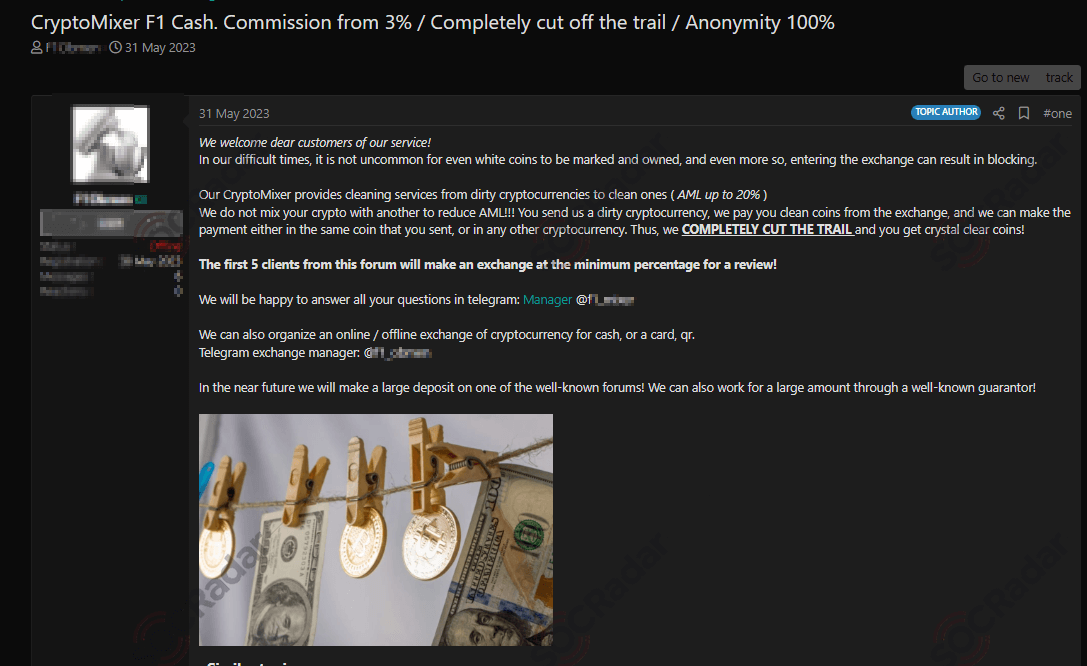
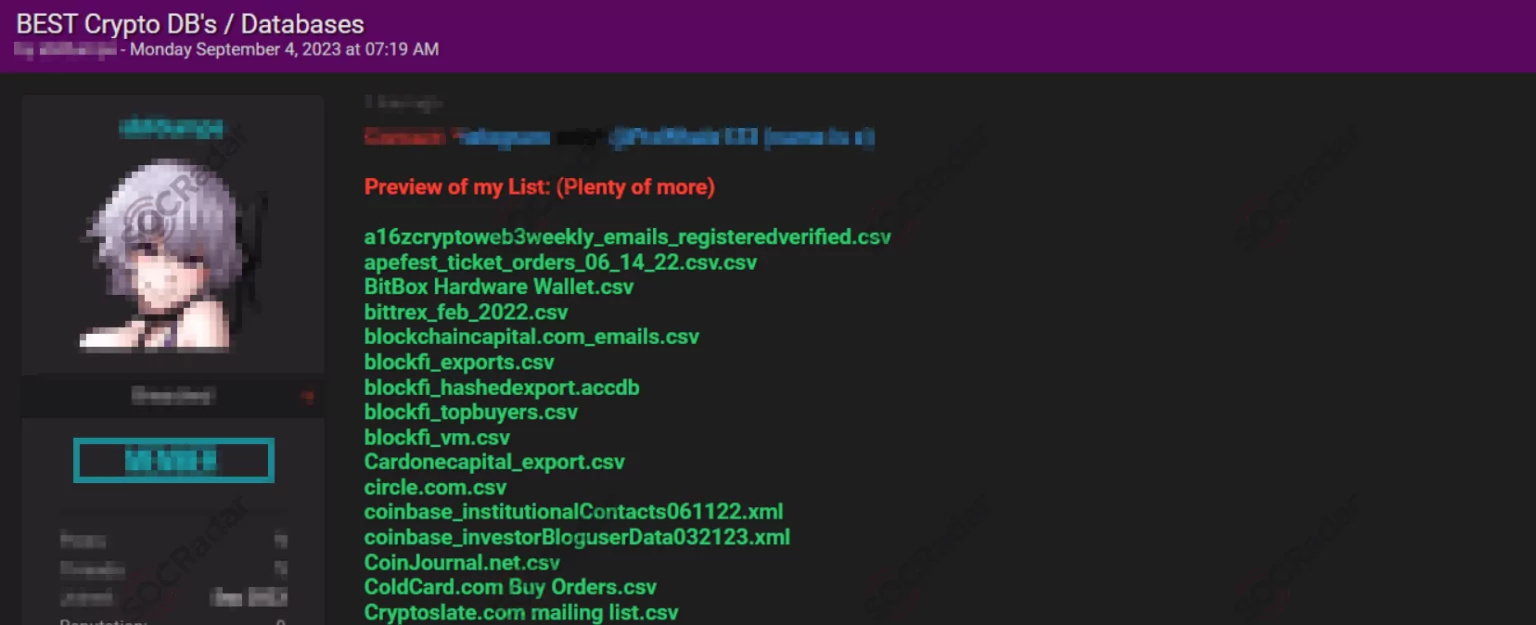
Various cryptocurrency mixer advertisements are also shared on hacker forums.
These services work by mixing the cryptocurrencies of various users, blending potentially identifiable or ‘tainted’ coins with others, thus masking their origins. After undergoing this mixing process, the funds are redistributed to the original owners, now appearing as new, unrelated transactions on the blockchain. This effectively breaks the direct link between the cybercriminal’s initial acquisition of the cryptocurrency and their subsequent use of it. Moreover, money laundering through crypto coins also adds a different dimension to the cryptocurrency-crime relationship.
For example, in August 2023, the U.S. Justice Department filed charges against the founders of Tornado Cash, Roman Storm, and Roman Semenov, accusing them of aiding criminals, including the North Korean Lazarus hacking group, in laundering over $1 billion of stolen cryptocurrency.
Lazarus allegedly utilized the decentralized crypto mixing service provided by Tornado Cash to launder approximately $455 million stolen in a major cryptocurrency heist following the Axie Infinity’s Ronin network bridge hack. Tornado Cash was implicated in additional laundering activities, including over $96 million after the June Harmony Bridge hack (out of a total of $100 million stolen) and at least $7.8 million following the August Nomad Heist (out of roughly $150 million stolen).
Blockchain Technology and Cybersecurity
We mentioned that it has many criminal uses, but the situation is not always that dire. As cybercriminals continue to exploit the very features that make cryptocurrencies attractive, blockchain technology – the foundation upon which these digital currencies are built – may also hold the key to a new era of cybersecurity.
While blockchain is synonymous with cryptocurrencies like Bitcoin and Ethereum, its applications extend far beyond. Its ability to create secure, unalterable records has the potential to enhance cybersecurity across various sectors.
One of blockchain’s most powerful features is its resistance to data modification. Once information is recorded on a blockchain, it becomes nearly impossible to change without detection.
Another benefit is the smart contract, self-executing contracts with the terms of the agreement directly written into code, can automate and enforce security protocols.
However, despite its potential, blockchain technology faces hurdles in adoption for cybersecurity purposes. Scalability, energy consumption, and integration with existing systems pose significant challenges.
Conclusion
It is evident that the digital age has brought with it a complex tapestry of challenges and opportunities. Cryptocurrencies, while a beacon of innovation in financial transactions has also cast a shadow by offering new avenues for cybercriminals to exploit. The anonymity and decentralization that make digital currencies so appealing for privacy and freedom also serve as cloaks for illicit activities, from ransomware to the dark dealings of the Dark Web.
The landscape of cybercrime is ever-changing, with cryptocurrencies both fueling and fighting the battle. The decline in cryptocurrency values has mirrored a reduction in cybercrime-related costs, suggesting a symbiotic relationship between market dynamics and criminal activities. Yet, as we’ve seen, cryptocurrencies are not just tools for crime but also targets themselves, with cryptojacking and platform breaches highlighting the vulnerabilities within the system. It may not be known exactly what will happen in the future for cryptocurrency, especially since the steps taken by states in this regard may cause dramatic changes. Still, for now, these structures seem to continue to be related.
As we stand at this crossroads, the need for proactive measures is critical. Because an efficient security posture cannot be achieved by trying to produce reactive solutions against such constantly changing structures, organizations must also turn to proactive security solutions to keep up with the ever-evolving cyber landscape.










