What Do You Need To Know About Cybersecurity in Power Grids
Cyberattacks on the electrical power system are becoming as disruptive as natural disasters, and the danger is growing as power grids become more connected and smarter.
Unlike in the past, when a power outage impacted only the energy supplied to homes and businesses, power grids have evolved into critical components of smart cities, infrastructure, and safety-related services. Nothing functions without power, and competent cybercriminal organizations may keep entire areas hostage until they pay vast ransoms or cave into other demands.
Major Attacks to Power Grids
As the profit margin for hacking these systems increases, the number of attacks increases proportionately. In 2020, the European Network of Transmission System Operators for Electricity (ENTSO-E) was hacked.
ENTSO-E is a consortium of 42 European transmission system operators operating in 35 countries. Other successful hacks occurred in 2019 against Russia’s power infrastructure and in 2017 against Saudi Aramco petrochemical facilities.
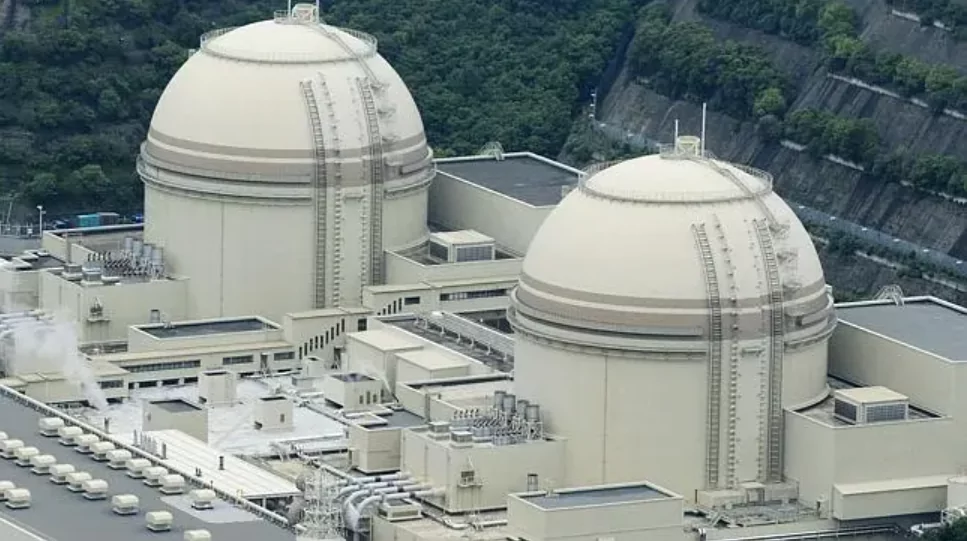
In 2015, a cyberattack on Ukraine’s infrastructure knocked down electricity to 200,000 people. In the following year, a similar attack occurred. And in 2014, cybercriminals who infiltrated Korea Hydro and Nuclear Power, South Korea’s nuclear and hydroelectric corporation, uploaded designs and manuals for two nuclear reactors online, exposing the personal information of 10,000 personnel.
Russia, China, Iran, and North Korea all have hacking capabilities against critical infrastructure, according to the US Intelligence Community’s Annual Threat Assessment Report (page 20). In other words, cyberattacks may occur anywhere and at any time, and no organization is immune at this level of capacity.
Are the Power Grids Getting More Vulnerable to Cyber Attacks?
As utilities diversify their renewable energy sources and add millions of additional components such as smart meters, they quickly increase the number of connections and sensors throughout their networks, increasing the opportunity for intrusions.
Over the last four decades, power plants and substations have shifted from manual to automated controls and enabled remote access to public and private networks for data analysis, exposing them to attack.
The electric grid and most of our infrastructure are really rather well-built in terms of dependability and safety. For decades, industrial engineering has maintained a strong safety culture. Safety and reliability were never considered from a cybersecurity standpoint, but they have resulted in a highly defendable environment.
As an illustration, consider what would happen if a piece of the United States’ electricity grid went down. Typically, we expect such events in the case of hurricanes or winter storms. And we’re adept at removing ourselves from computers and performing manual tasks, simply working the infrastructure to reclaim it. Typically, it’s a matter of hours or days, seldom longer than a week or two.
Numerous cyberattacks are directed targeting computer technology and the interconnected nature of infrastructure. Thus, when they target it in this manner, you’re looking at hours, perhaps a day, and no more than a week of downtime. We’re not talking about prolonged disruptions or jeopardizing safety for acceptable circumstances.
Now, the frightening aspect of it is [dual]. To begin, our opponents are becoming far more aggressive. They’re gaining valuable knowledge about our industrial systems, not just from a computer technology perspective but also from an industrial engineering one, considering ways to disrupt or even destroy equipment. This is when some very frightening situations begin to emerge.
The second point is that much of that flexibility to revert to manual operation and the harsh nature of our infrastructure is eroding. We’re beginning to witness an increase in computer-based systems due to business reasons and a scarcity of people to man the tasks. We are beginning to witness a convergence of operating systems. And this provides foes with a scale they previously lacked.
Two Types of Attacks
Stage I: Intrusions are made with the intent of obtaining information. These are the types of conventional espionage operations we’ve grown accustomed to hearing about, in which data is taken or wiped.
Stage II: The attack may result in a brief loss of power, physical damage to equipment, or other scenarios that we frequently hear about. It is critical to remember that these are not trivial tasks. To continue a Stage II assault, an attacker must steal knowledge particular to [that] industrial environment during the Stage I intrusion.
The 2013–2014 initiatives listed above were precisely the Stage I activities you’d like to employ to transition into a Stage II activity. As a result, they terrified the living daylights out of us all. However, the latest revelations concerning the nuclear facility and roughly a dozen energy businesses penetrated a high-profile phishing attack did not appear to be geared toward pivoting into Stage II.
Could Attacks Increase in the Future?
Additional renewable energy sources, such as solar, wind, and hydropower, are expected to become a significant component of the contemporary power grids in the future. Digitalization will become a reality in the smart, connected grid, incorporating 5G and LPWAN (Wi-SUN and others). This will speed up the development of smart cities.
The integration of these new technologies with the aging infrastructure remains a challenge. However, one thing stays constant. The electricity industry will face an avalanche of cyberattacks, and it must exercise extreme caution when it comes to cybersecurity. Equipped with $2 billion in federal assistance for cybersecurity and IT equipment improvements, the US business has a fighting chance in the cyber battle.
What Happened When Russian Hackers Come for the Power Grids?
In late 2015, Russian hackers launched the first significant cyberattack on a nation’s energy infrastructure, knocking out a portion of the Ukrainian national grid for six hours. The following year, they launched another attack on Ukraine, entering a transmission substation north of Kyiv and tripping every circuit breaker, momentarily disrupting electricity to a part of the city.

According to Andy Bochman, senior grid strategist at the Idaho National Laboratory and one of the leading US specialists on-grid cyber threats, the intrusion was intended to punish Ukrainians and demonstrate what Russia is capable of doing to other adversaries. “Both of the assaults in Ukraine were protests,” he asserts. “And the entire globe was on the lookout.”
Shortly after that, Russian spyware was detected within at least ten US utilities, including a Kansas nuclear power plant operator. According to three people acquainted with the event, government authorities organized secret meetings with utility executives, leading the power firms to spend months cleaning up their systems.
According to two people familiar with the briefings’ contents, the US Department of Energy kept briefing power industry officials, warning that possible enemies have been found changing grid components during production.
What Techniques Do Threat Actors Use?
To obtain access to power plant computers and internal networks, hackers initially target smaller, less secure businesses, such as those that manufacture generator components or sell software used by power plants.
They accomplished this by sending emails from a hacked account that the recipient trusted and had previously engaged with to convince the recipient to give private information. This practice is referred to as “spearphishing.”
Another technique they employ is called “water holing.” The hackers changed websites often used by energy business members, allowing those websites to capture information such as logins and passwords and feed it back to the hackers.
According to the investigation, some targeted individuals were convinced to “download attractive word documents” concerning control process systems during Russia’s March 15, 2018, US power grid breach. However, those materials proved to be more vicious than tempting. By executing them, the targets enabled hackers to access their machines.
After gaining the login credentials necessary to deceive the computers into granting access, the invaders established local administrator accounts (those with the capacity to perform operations such as program installation). They used them to disseminate further malware across the connections. Additionally, their code included efforts to mask their traces, such as automatically signing out of administrator accounts after eight hours.
Conclusion
The primary issue is that governments worldwide are fast discovering how much critical or even profitable information they can gain through hacking and are continuously devising new ways to evade security barriers they face.
Sanctioning officials responsible for enabling attacks unquestionably punishes those responsibly. However, it’s worth noting that almost a third of those listed in these fresh sanctions have already been sanctioned by the US — which obviously did not deter them from carrying out these new assaults. This implies that penalties alone may not have the deterrent or retaliatory impact sought.
However, because hacks of this nature sit somewhere between network security, espionage, and criminality, it’s difficult to determine how to respond in a way that truly makes a difference. While these intrusions fall short of sabotage or war, that does not mean we have to approve of them.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Get free access.