
What is The Intelligence Cycle?
The whole activity of leading the intelligence cycle, which is a collection of procedures used to convey decision-useful information (intelligence) to leaders, is referred to as intelligence cycle management. Planning and direction, collecting, processing, exploitation, analysis and creation, and distribution and integration are all part of the cycle.
The use of a process known as The Intelligence Cycle is one of the essential parts of intelligence. It helps intelligence professionals, regardless of their primary area — from counterterrorism to cyber security — develop and execute a strategy for delivering a high-quality intelligence product to clients.
The Intelligence Cycle Steps
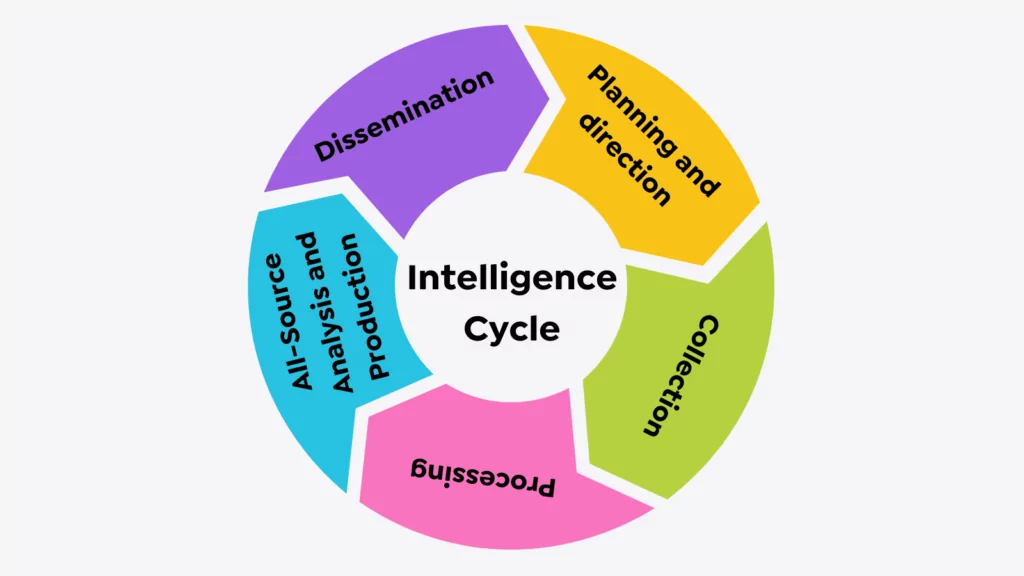
1. Planning and Direction
This is in charge of overseeing the entire process, from determining the need for data to delivering a threat intelligence product to a customer. It is both the beginning and the conclusion of the cycle — the beginning since it entails drafting precise collection needs, and the end because completed intelligence, which aids policymaking, produces new requirements.
The entire process is reliant on public authorities’ supervision. Requests for intelligence are initiated by policymakers, such as the President, his advisors, the National Security Council, and other significant government departments and organizations.
2. Collection

Collecting raw data required to generate final intelligence is a collection. Open sources such as foreign broadcasts, newspapers, magazines, and books are among the various sources of information available. The CIA’s analytical powers rely heavily on open-source reporting. There are additional information sources that are kept hidden. The CIA’s operations officers get this information from foreign agents and defectors who supply intelligence that can’t be obtained any other way.
Finally, technical collection — electronics and satellite photography — is critical in modern intelligence activities such as monitoring arms control agreements and giving direct assistance to armed troops.
3. Processing
Decryption, language translations, arranging content with meta tags, filtering false positives, and data reduction are all used to transform the vast amounts of data collected into a format that analysts can understand. Some of these processes may not always be necessary.
4. All-Source Analysis andProduction
The translation of raw data into polished intelligence is the goal of all Source Analysis and Production. It entails combining, assessing, and analyzing all accessible data — which is sometimes fragmented and even contradictory — and the creation of intelligence products. The information’s trustworthiness, validity, and relevance are evaluated by analysts, who are subject-matter experts. They combine data into a logical whole, contextualize the assessed material, and generate final intelligence that includes event evaluations and judgments about the information’s significance for the United States.
The CIA focuses most of its efforts on supplying policymakers with strategic intelligence. It fulfills this vital role by keeping track of events, alerting decision-makers to dangers to the US, and anticipating trends. Different places, issues, or people may be discussed in diverse contexts — political, geographic, economic, military, scientific, or biographical. The current state of affairs, as well as capabilities and prospective tendencies, are analyzed.
The CIA publishes many written reports, which range in length from one page to several hundred pages. They may include current intelligence that is of urgent value and long-term analyses. In oral briefings, the Agency delivers certain completed intelligence. The CIA also contributes to the writing and production of National Intelligence Estimates, representing the Intelligence Community’s collective assessments.
5. Dissemination
The last phase, which naturally follows the first, is to provide the produced intelligence to the customers, who are the same policymakers who prompted the intelligence requirements in the first place. Every day, completed intelligence is delivered by hand to the President and critical national security advisers.
Policymakers, who are the recipients of completed intelligence, then make judgments based on the information, which may lead to the imposition of further requirements, initiating the Intelligence Cycle.
What is it Good For?
For intelligence analysts, the intelligence cycle is “standard doctrine,” and intelligence organizations adopt it worldwide.
An intelligence cycle is a simple approach to understanding a subject that can be difficult to grasp. Understanding the Intelligence Cycle provides the analyst with clear direction and a method for gathering intelligence.
The Intelligence Cycle has a critical role in generating insightful, actionable intelligence that meets the intelligence needs of the customer.
This method ensures that intelligence specialists stay within the scope of the client’s needs, allowing them to provide finished information to customers ahead of schedule to enhance their risk posture.
Finally, Intelligence Analysts employ the Intelligence Cycle as a framework for gathering information, analyzing and interpreting it, and making evaluations and recommendations in response to Intelligence Requirements.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free

































