
5 Things You Should Know About the Genesis Marketplace
[April 5, 2023] Update: Law enforcement has seized the Genesis Market domains.
The FBI has taken down the domains for the major marketplace Genesis as a result of Operation Cookie Monster. Since 2017, the Genesis Marketplace has been a popular source of sensitive information for threat actors.
A seizure banner appears when visiting the Genesis Market domains, explaining that these seizures were made possible through “international law enforcement and private sector coordination.”
According to reports, the takedown of the Genesis Market resulted in many arrests worldwide. Despite this, the authorities have not yet identified the administrators of Genesis, and they seek contact with any individuals who may have information about the marketplace’s operations.
The Genesis Market is an automated online store that sells credentials, fingerprints, web platform vulnerabilities, cookies, and various sensitive data that assist cybercriminal hackers in gaining initial access into the targeted victim network. Security researchers forewarn that with hundreds of thousands of digital identities listed, the Genesis Marketplace has become a go-to shop for threat actors planning to perform various cyber-attack techniques.
Below we have listed five significant facts to know about this underground market.
1- Unknown Risk: Bypassing MFA Mechanisms with Stolen Browser Cookies
It’s not only stolen credentials but also browser cookies for sale that poses a massive account takeover risk.
Multi-factor Authentication (MFA) is a layered method to improve account security on the web, VPN, remote desktop sessions, and almost any virtual environment. By introducing additional control mechanisms into the login procedure like a code delivered through SMS, users can improve their access to online accounts, thus stopping a considerable portion of impersonation attacks.
For most digital businesses, user experience is prioritized. Browser cookies reduce the friction after a user has logged in to the application so that users do not need to reauthenticate often. Thanks to cookies, user sessions are usually valid for a longer time. However, threat actors have workarounds to evade this mechanism through stolen browser cookies. In bypassing attacks, a threat actor can use a stolen session cookie to authenticate web applications, bypassing MFA because the session is already authenticated.
The cookies purchased on the Genesis Blackmarket can then be imported into a control browser. Meaning they can use the online app for as long as the cookie remains active, potentially giving them sufficient time to move around laterally and access confidential data performing other actions as the victim.
2- Current Statistics
More than 430 thousand bots are currently put up for sale on the Genesis Market. These bots are available in almost all countries. The figure below illustrates bot numbers available on the market for different countries.
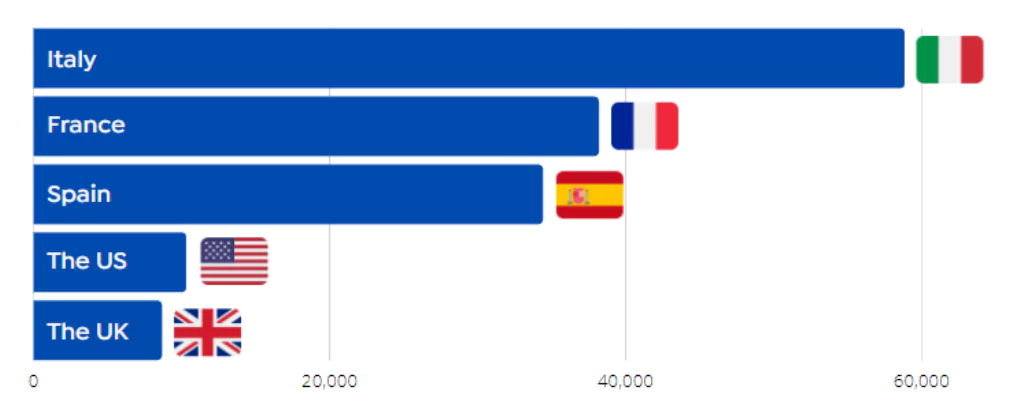
3- Prices Vary by Country
Bots that automatically collect cookies and digital fingerprints are open on Genesis Marketplace for numerous countries, including Italy, the United States, Singapore, France, Australia, and the United Kingdom. Each bot has a multiplicity of accounts related to a compromised host. The Genesis bots’ prices range from $0.60 to the most expensive at $103.2.
4- Stealer Logs for Sale Automation
Cybercriminals use different attack methods such as the rainbow table, brute-force, and credential stuffing to capture passwords. However, more tech-savvy cybercriminals leverage the capabilities of info stealer malware families like Raccoon, AZORult, and RedLine. This malware can be distributed through mail phishing campaigns, malicious mobile applications, or a browser extension. After getting infected, the victim system becomes a part of the botnet. The bot owner has access to logs, files, images, system configuration, IP address, browser history, cookies, and other functionality such as taking random screenshots. The stolen data is automatically uploaded to Genesis Market, available to threat actors.
5- There Are Competitors to the Genesis Marketplace: 2easy and Russian Market
The Genesis Market is not the only place where threat actors can automatically obtain cookies, web fingerprints, and vulnerabilities. Genesis Market has different competitors like 2easy and Russian Market. 2easy is a relatively new and reputable market, where the data sold appears to have been legitimately stolen, and the buyers are assured that data has not been previously sold. The Russian Market is also online market cybercriminals can use to collect attack instruments and sensitive data.
Get Advanced Monitoring on the Genesis Marketplace
SOCRadar’s Extended Threat Intelligence solution has modules to protect your business against data breaches or exposure threats. RiskPrime, which collects contextual data from the surface, deep and dark web, is an early warning system against all kinds of digital risks for your Security Operations and Risk Management teams to work more effectively and support them with in-depth analysis.
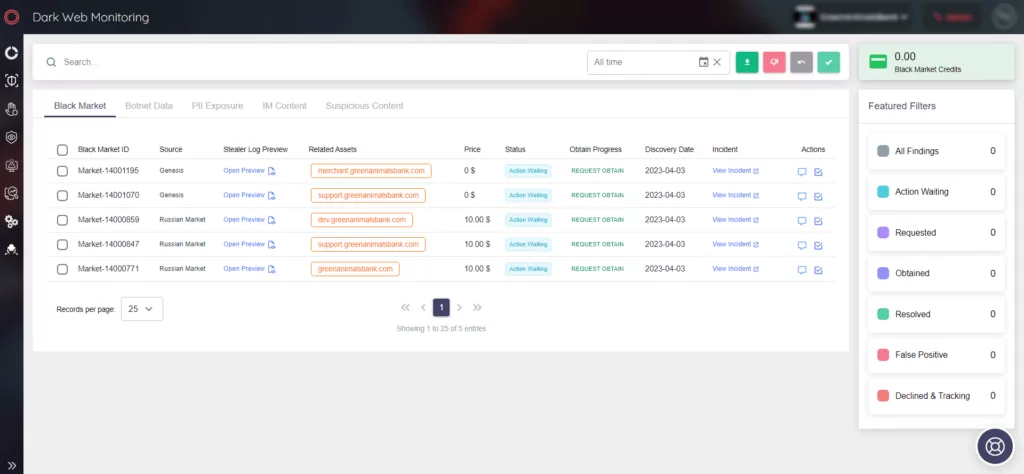
With RiskPrime, you can easily monitor black markets, dark web forums, Telegram channels, social media, GitHub repositories, etc. Click here for detailed information about the RiskPrime system, which works in coordination with AttackMapper and ThreatFusion.





































