
Attackers Exploit Fortinet Zero-Day CVE-2022-42475 with BoldMove Malware
Researchers have discovered a sophisticated new BoldMove malware created specifically to operate on Fortinet’s FortiGate firewalls after collecting data related to a recently disclosed zero-day vulnerability in the company’s FortiOS SSL-VPN technology.
A threat actor created the malware with a base in China that conducts cyberespionage operations against individuals and groups associated with the government.
What is BoldMove Malware?
The malware that Mandiant tracks as BoldMove is connected to the CVE-2022-42475 exploit, per their research. A European government agency and an African service have both been targets since October, and the malware was recognized in December 2022.
The BoldMove malware is a backdoor written in C language. It has Windows and Linux versions that are customized to operate on FortiOS. Researchers have not detected any exploit activity in the wild related to the Windows version.
The BoldMove malware’s Linux variant tries to establish a connection with a hardcoded command-and-control (C2) server upon execution.
BoldMove can start gathering information on the system when a connection is successful. The information is then relayed to the C2, and the C2 server relays instructions to the malware. As a result of events, the threat actor gains full remote control of the compromised FortiOS device.
Other Capabilities of BoldMove Malware
The Linux version of BoldMove has abilities to manipulate specific FortiOS features.
Fortinet also described the malware as a FortiOS-specific variant of a “generic” Linux backdoor. According to the company’s analysis, the malicious file may have masqueraded as a component of Fortinet’s IPS engine on compromised systems.
The malware also has the capability to:
- Manipulate FortiOS logs to prevent detection.
- Look for event logs in FortiOS. The malware can delete a particular string that enables the reconstruction of the logs.
- End all logging processes.
How Does the Fortinet Zero-Day (CVE-2022-42475) Work?
In November, Fortinet patched the vulnerability, which is identified as CVE-2022-42475. Fortinet made the flaw public in December, and the company urged users to update their devices because threat actors were actively using it.
The flaw exists in several versions of Fortinet’s FortiOS and FortiProxy technologies and enables an unauthenticated attacker to run arbitrary code on vulnerable systems. You can read our blog post for more information on the vulnerability.
Which Products and Versions are Affected?
The malware affects all the products and versions vulnerable to the CVE-2022-42475 vulnerability. See them in the list below:
- FortiOS versions 7.2.0 through 7.2.2
- FortiOS versions 7.0.0 through 7.0.8
- FortiOS versions 6.4.0 through 6.4.10
- FortiOS versions 6.2.0 through 6.2.11
- FortiOS-6K7K versions 7.0.0 through 7.0.7
- FortiOS-6K7K versions 6.4.0 through 6.4.9
- FortiOS-6K7K versions 6.2.0 through 6.2.11
- FortiOS-6K7K versions 6.0.0 through 6.0.14
How to Prevent Exploitation?
To send network requests to the entire internal network and spread laterally to other devices, BoldMove can send requests to internal Fortinet services.
Because they provide simple network access without requiring interaction, threat actors will continue to target unpatched internet-facing devices like firewalls and IPS/IDS appliances.
Mandiant claims that native security mechanisms do not effectively protect these devices and that it is difficult for defenders to examine what processes are running on these devices.
So, to address the security flaw, all users should update to the latest versions of affected products. If the patches cannot be applied immediately, users are advised to check logs, disable VPN-SSL, and set up access rules to only permit connections from specific IP addresses.
The original Fortinet security advisory is available here.
Indicators of Compromise Relating to BoldMove (IOCs)
Researchers have identified the following indicators of compromise for the BoldMove malware’s variants:
Basic:
- MD5: 12e28c14bb7f7b9513a02e5857592ad7
- SHA256: 3da407c1a30d810aaff9a04dfc1ef5861062ebdf0e6d0f6823ca682ca08c37da
Extended:
- MD5: 3191cb2e06e9a30792309813793f78b6
- SHA256: 0184e3d3dd8f4778d192d07e2caf44211141a570d45bb47a87894c68ebebeabb
Windows:
- MD5: 54bbea35b095ddfe9740df97b693627b
- SHA256: 61aae0e18c41ec4f610676680d26f6c6e1d4d5aa4e5092e40915fe806b679cd4
Track Vulnerabilities Concerning Your Organization
SOCRadar notifies a company when a vulnerability affecting its assets is exposed on a public network and in one of its applications.
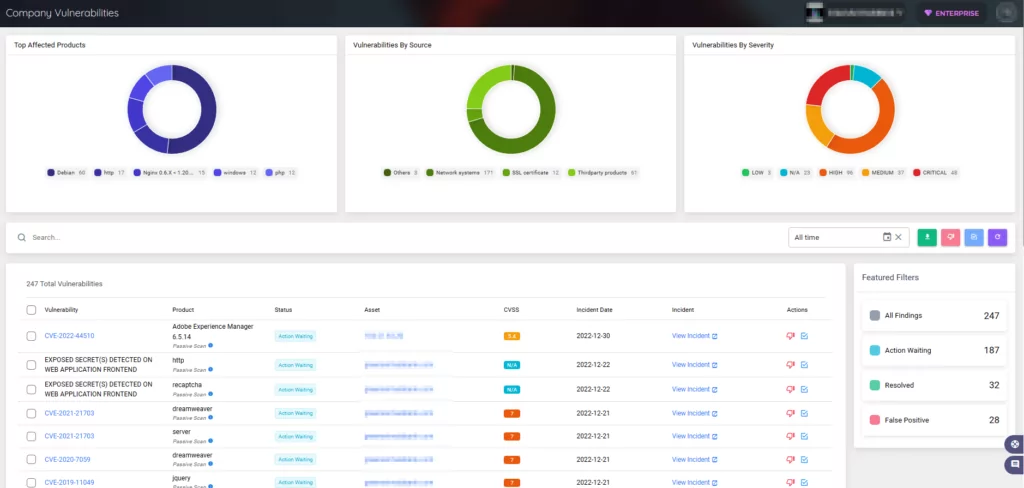
You can see the vulnerabilities threat actors use with the vulnerability intelligence module. Additionally, you can obtain actionable insights and context on potentially vulnerable technologies to speed up the assessment and verification procedures.




































