
AvosLocker’s New Linux Variant Targets VMware ESXi Servers
A Linux variant of the AvosLocker gang, which first appeared in the summer of 2021 and conducted its operations in RaaS style, targeting VMware ESXi virtual machines, has emerged.
AvosLocker, which carries out its VMware ESXi virtual machines, was determined to use the Linux variant as the new ransomware in November of 2021. Although there is currently no information about the targeted company or institutions, it is alleged that a ransom of $ 1 million was demanded from the victim.
What Happened?
In November, the AvosLocker gang introduced the latest ransomware variants, Windows Avos2 and AvosLinux.
The gang introduced their new variant with the phrases, “Avos2 / Avoslinux has the best of both worlds: High performance and high amount of encryption compared to its competitors”.
How Does AvosLinux Attack?
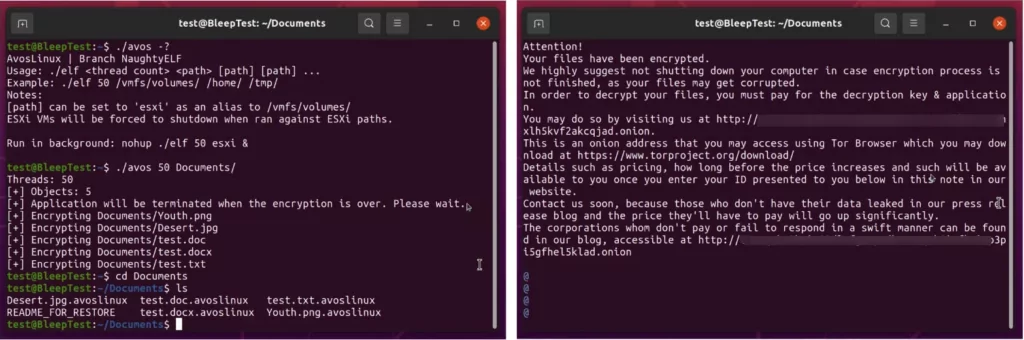
AvosLinux, the new Linux variant of AvosLocker, terminates all ESXimachines on the server using the following command:
esxcli --formatter=csv --format-param=fields=="WorldID,DisplayName" vm process list | tail -n +2 | awk -F $',' '{system("esxcli vm process kill --type=force --world-id=" $1)}'Once running on a compromised system, the ransomware adds the “.avoslinux” extension to all encrypted files.
The gang also leaves ransom notes asking victims not to shut down their computers to avoid file corruption and to visit a TOR site with more details on how the ransom will be paid.
How Does Attack Work?
In recent years, ransomware operators have turned their targets to virtual machines by targeting virtual machines, as they also benefit from more accessible and faster encryption of multiple servers with a single command.
Ransomware gangs such as Revil, Hive, Babuk, RansomExx/Defray, Mespinoza, GoGoogle, DarkSide, and HelloKitty also create their variants of Linux and target virtual machines.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free


































