
Dark Web Profile: Hunters International
Originating in the latter part of 2023, this Ransomware-as-a-Service (RaaS) operation has drawn attention due to its technical lineage and operational tactics resembling those of the notorious Hive ransomware group. With law enforcement agencies previously disrupting Hive, Hunters International’s rise just after the operation underscores the persistent and adaptive nature of cybercriminal networks.

Hunters International’s logo
Who is Hunters International?
Hunters International emerged in the cyber landscape around the time of the disruption of the Hive ransomware group by law enforcement agencies. This new group, detected in Q3 of 2023, exhibited significant technical overlap with Hive, suggesting an evolution or offshoot of the dismantled operation. The transition highlights the adaptive strategies of cybercriminal networks, which evolve to sustain their malicious activities despite law enforcement efforts. Hunters International’s initiation and operational blueprint reflect a continued threat in the realm of cyber extortion and data theft.
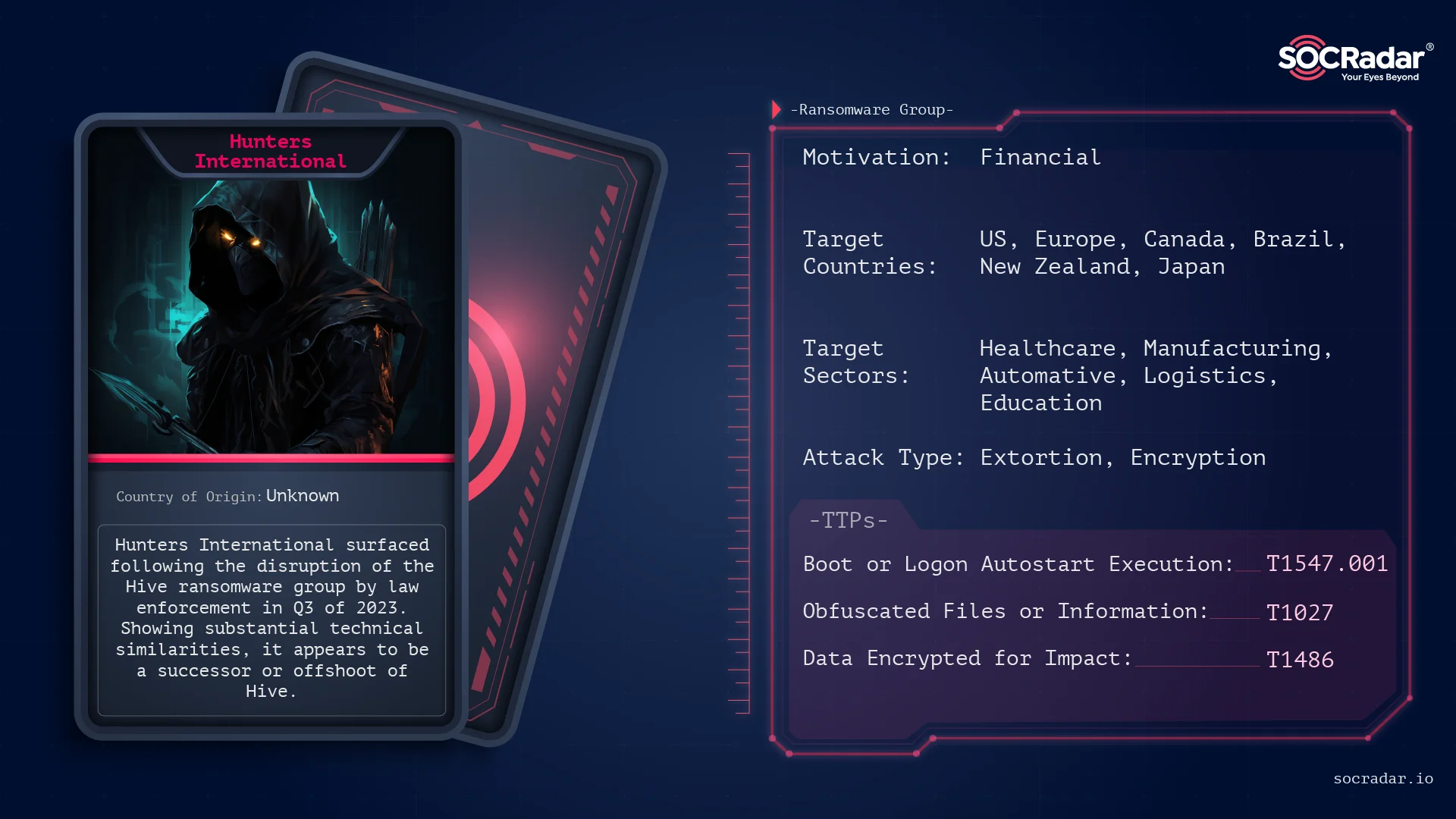
Threat Actor Card for Hunters International
Hive Resurrected
Once again, their techniques and ransomware strain reveals a significant overlap with the Hive ransomware, indicating a shared lineage or possible transfer of technology. This connection suggests that Hunters International have inherited or adapted Hive’s encryption techniques and operational strategies.

FBI’s takedown notice on Hive’s websites.
In January 2023, a coalition involving the US Department of Justice, FBI, Secret Service, Europol, and European agencies targeted the Hive ransomware group. This notorious collective, responsible for extorting over $100 million from more than 1,500 global victims since June 2021, including healthcare, education, and financial sectors, saw two of their extortion and data leak sites seized. These actions displayed international law enforcement’s commitment to dismantling cyber threats and protecting vulnerable sectors from ransomware attacks.
The dismantling of Hive’s network followed a seven-month undercover FBI operation, granting them network access and enabling the provision of decryption keys to over 300 entities, averting about $130 million in potential ransom payments. Additionally, 1,000 more keys were given to previous victims. Despite no arrests, the operation significantly impacted Hive’s operations, highlighting the challenges law enforcement faces with cybercriminals often based in jurisdictions less cooperative with international law enforcement efforts. This raises questions about the future actions of such disrupted groups.
Around these developments, a report from Bitdefender even suggested that Hive’s leaders strategically chose to end their operations, transferred assets to Hunters International.
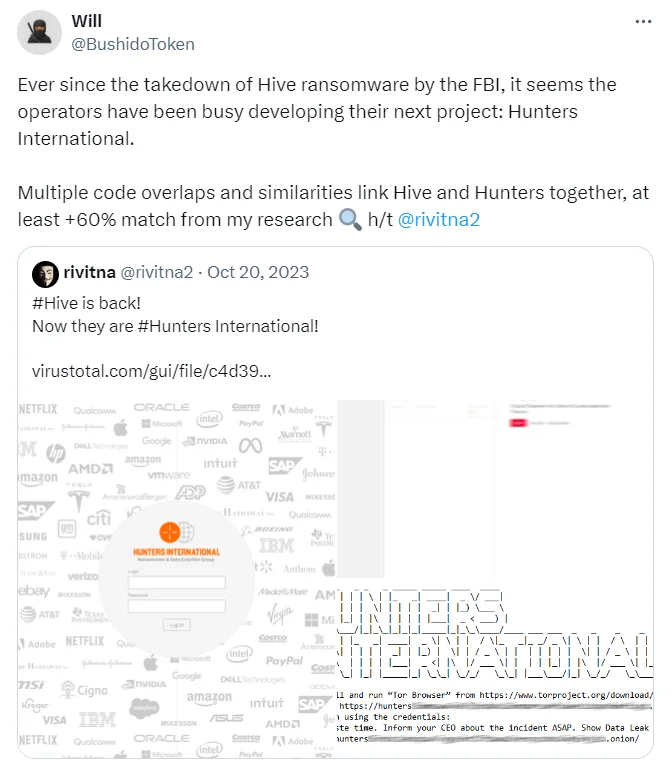
Tweets from researchers, @rivitna2 and @BushidoToken
In fact, security researchers at X (formerly Twitter) stated that Hunters had approximately 60% code similarity when it was first released.
But upon these allegations Hunters International stated that they are not simply a new version of Hive but an independent entity that took over Hive’s source code and infrastructure. Their main operational focus is on stealing data rather than encrypting it, distinguishing their approach from Hive’s.
Their explanation seems acceptable. As analyzed by Bitdefender, the group’s focus significantly leans towards stealing data, as evidenced by all known victims experiencing data exfiltration, whereas not every victim’s data was encrypted. Hunters International seems to have customized Hive’s ransomware to enhance simplicity and efficiency.
By reducing command-line options and optimizing encryption key management, they’ve made their malware less verbose and easier to use for operatives. The switch to Rust, mirroring trends in sophisticated ransomware development, aids in evading detection and facilitates faster encryption. Their unique approach embeds encryption keys within the encrypted files, a method aimed at streamlining the decryption process for victims who pay the ransom while also complicating security professionals’ efforts to counteract the malware.
Target Scheme
Hunters International has targeted a diverse array of industries worldwide, demonstrating a global reach with a strategic focus on maximizing impact and ransom potential. Their victims span across healthcare, automotive, manufacturing, logistics, financial, educational, and food sectors, indicating a non-discriminatory approach aimed at exploiting any vulnerable entity.
Group has been very busy, attacking a lot of different organizations all over the world. Most of their targets are in the United States, but they didn’t stop there; they went after companies and organizations in Europe, Canada, Brazil, and even as far as New Zealand and Japan. It’s like they’re casting a wide net to see what they can catch, without really caring who the victim is.
They’re not picky about who they attack either. Whether it’s an energy company, a hospital, a school, or even a zoo, they’re all fair game to this group. It seems like they’re just looking for any opportunity to make money, going after those who might not have strong protection against cyber attacks or who would really feel the pressure to pay up if their data were taken or locked up.
This wide-ranging victimology underscores the group’s opportunistic nature and its capacity to adapt and penetrate various sectors, posing a significant threat to organizations of all sizes and functions globally. Because financial income is a priority, this wide target audience is normal, especially in groups working with the RaaS model.
Behind the Operation
The later investigations into Hunters International led to the exposure of its data leak site’s identity, revealing potential ties to Nigeria through domain registrations and email addresses associated with the group. On January 22, 2024, Hunters International unveiled a non-dark web version of their leak site under the same name.
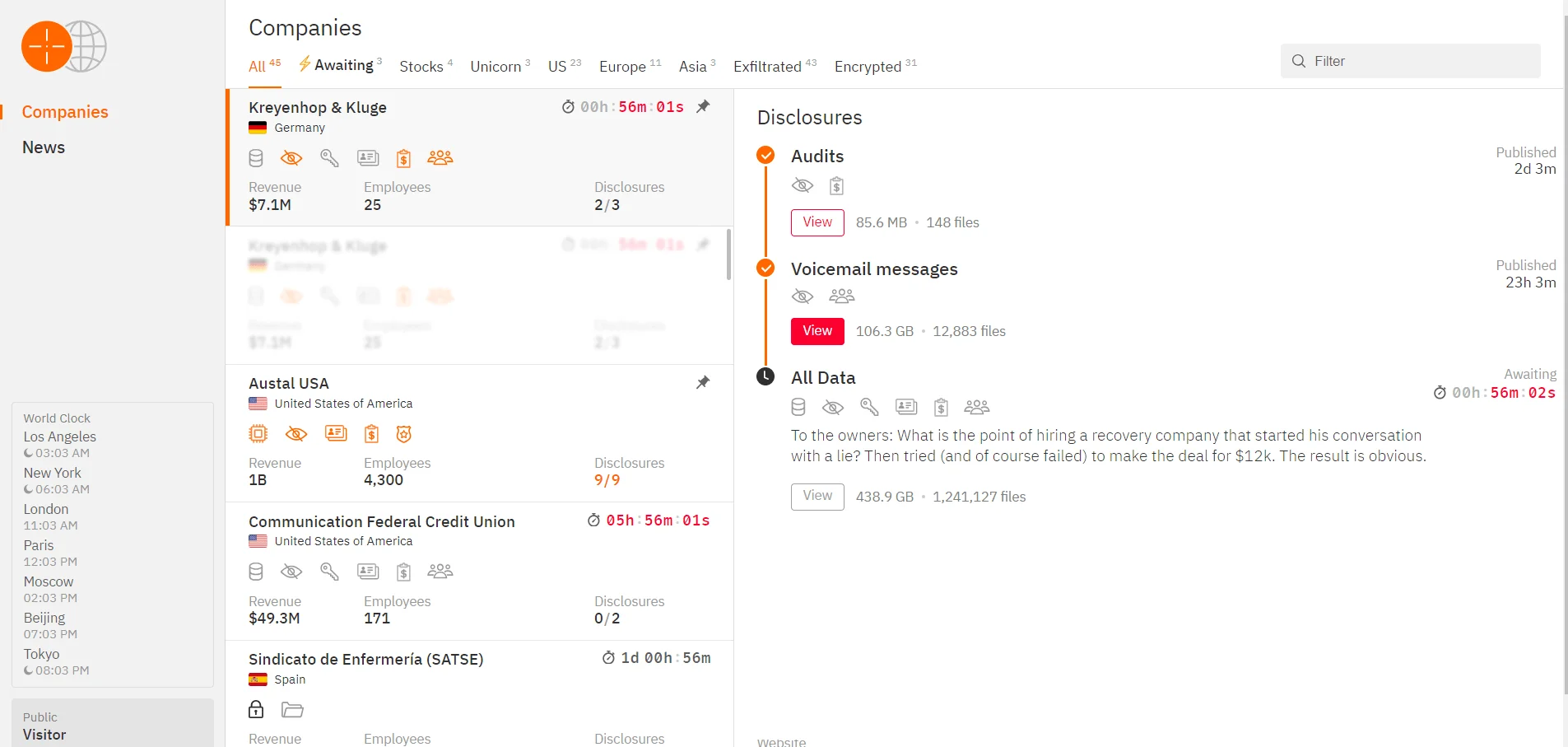
Hunters International’s surface web data leak site
As researcher Krishnan states, they brought back a website that hadn’t been used since 2021, using a fake name to hide who they really are and make it harder to find them. When digging into it, they found email addresses that might connect the group to Nigeria. But, it’s possible these emails are just tricks meant to lead people on the wrong path. This mix of real and fake identities shows how hard it is to figure out who is behind cybercrimes. It shows how clever and complex groups like Hunters International are. They’re very careful to keep their identities secret and use tricky methods that show they operate all over the world.
Conclusion
The impact of Hunters International’s ransomware attacks is multifaceted like many ransomware incidents, causing significant data breaches, financial losses, and reputational damage to affected organizations. In response, cybersecurity experts recommend a proactive and comprehensive approach to defense, including regular data backups, employee training on phishing detection, and the implementation of robust cybersecurity frameworks to mitigate risks. Organizations are also advised to engage in threat intelligence sharing and collaborate with law enforcement to enhance their resilience against such evolving cyber threats.
The emergence and activities of Hunters International exemplify the persistent and evolving nature of cyber threats in the digital age. Despite significant efforts to dismantle ransomware operations, groups like Hunters International continue to pose substantial risks to global cybersecurity. Their sophisticated tactics, global reach, and ability to adapt underscore the importance of sustained vigilance, proactive defense strategies, and international cooperation among cybersecurity communities to mitigate these threats effectively.
How Can SOCRadar Help?
The SOCRadar Cyber Threat Intelligence suite provides tools to help detect and prevent ransomware with its Threat Hunting feature, allowing users to search billions of records for Indicators of Compromise (IoCs) and gather important data. This data can be integrated into SOAR systems via a Restful API, enabling the creation of custom feeds for SIEM systems, Firewalls, and EDR platforms to improve defense against ransomware. SOCRadar also includes a Ransomware Check in its Attack Surface Management, allowing easy integration of these feeds into security setups to protect against threats from new malicious URLs.
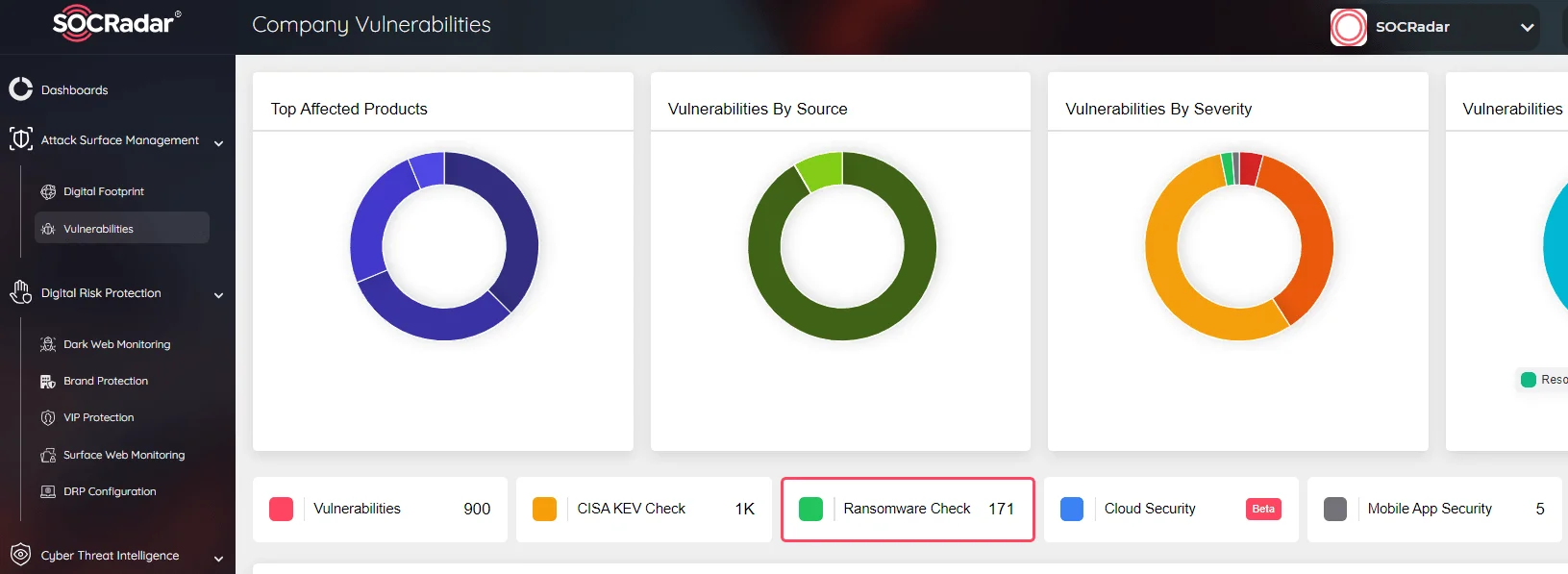
SOCRadar Attack Surface Management, Ransomware Check
SOCRadar continuously enhances its platform to address your security needs and protect against the evolving tactics of cybercriminals. We encourage you to explore our platform, available at no cost, and share your feedback to strengthen your digital security.
Tactics, Techniques, and Procedures
| Tactic | Technique |
| Execution | Native API (T1106), Shared Modules (T1129) |
| Persistence | Boot or Logon Autostart Execution (T1547.001) |
| Defense Evasion | Obfuscated Files or Information (T1027), Impair Defenses (T1562.001) |
| Discovery | Process Discovery (T1057), System Information Discovery (T1082), File and Directory Discovery (T1083) |
| Command and Control | Application Layer Protocol (T1071), Specifically Web Protocols (T1071.001) |
| Impact | Data Encrypted for Impact (T1486) |




































