Harnessing SIEM Solutions With Threat Intelligence
Organizations strive to implement security measures and remain current to defend against the escalating number of cyber attacks. However, staying ahead of cyber threats is challenging in the constantly evolving threat landscape. Hackers are skilled at exploiting vulnerabilities and launching targeted attacks against organizations. Therefore, organizations require a comprehensive security strategy to counteract complex cyberattacks that surpass structured, rule-based controls.
While Security Information and Event Management (SIEM) systems are pivotal to Security Operations Center (SOC) and ensuring cybersecurity, there are instances where SIEMs alone are insufficient. Given the organized and modern cyber attackers’ increasingly sophisticated and highly targeted techniques, organizations may face security breaches relying solely on SIEM. To effectively detect and thwart cyber attackers, and to augment the capabilities of SIEM security, organizations need an extensive set of tools. These tools assist in understanding the Tactics, Techniques, and Procedures (TTPs) of attackers. This article specifically focuses on enhancing SIEM capabilities for proactive security, leveraging the contextual information provided by cyber threat intelligence.
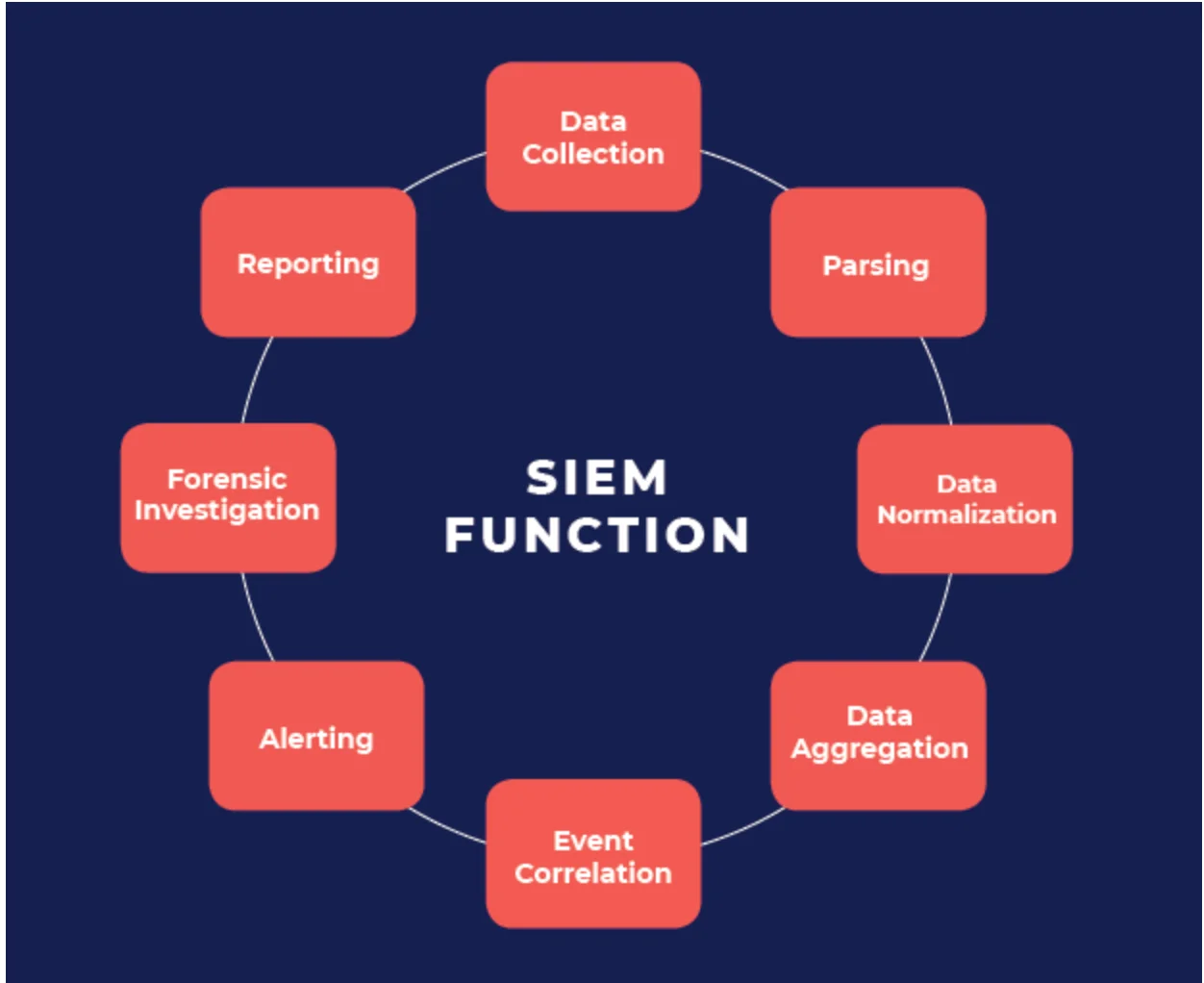
SIEM Functions (Source: RedLegg)
Understanding SIEM and Its Role in SOC Operations and Future Prospects
Security Information and Event Management (SIEM) software and appliances are central to any Security Operations Center (SOC) in enterprise organizations. SIEM provides a crucial capability within the SOC to collect logs and data from multiple sources across the network, enabling the assessment, analysis, and correlation of network events. SIEM analyzes these correlated events to detect known threats, which is invaluable for SOC organizations. However, a key challenge is the constant evolution and change in cyber threats and device vulnerabilities. SOCs must protect their existing environments while also learning and understanding new threats that affect their networks in cyberspace. Enhancing SIEMs to better protect networks, endpoints, and environments to increase threat awareness in global enterprises is a fundamental challenge. Threat intelligence feeds can be a key solution to this challenge.
Security teams have long depended on SIEM technology to collect, correlate, and analyze security event logs from various sources across their network environment. These tools were expected to aid in rapid threat detection and response, streamline compliance reporting, and facilitate post-incident investigations. While these expectations have largely been met, there is speculation in professional circles that SIEM technologies may become obsolete.
However, a recent report by MarketsandMarkets predicts significant growth in the global Managed SIEM Services Market. Estimated to be worth USD 7.5 billion in 2023, it is expected to reach USD 16.0 billion by 2028, growing at a Compound Annual Growth Rate (CAGR) of 16.3% during the forecast period.
As organizations continue to adopt new technologies for digital transformation, the volume of security alerts has increased substantially. This increase is due to both a growing attack surface and rising vulnerabilities related to digital assets. This surge has placed additional burdens and stress on already overworked security professionals. Security Operations Center (SOC) Incident Response (IR) analysts, in particular, suffer from alert fatigue. This section explores some of the challenges they face with SIEM technologies.
Exploring the Challenges with SIEMs
There are several key challenges associated with the deployment and operation of Security Information and Event Management (SIEM) solutions in organizations. Let’s examine these challenges in detail.
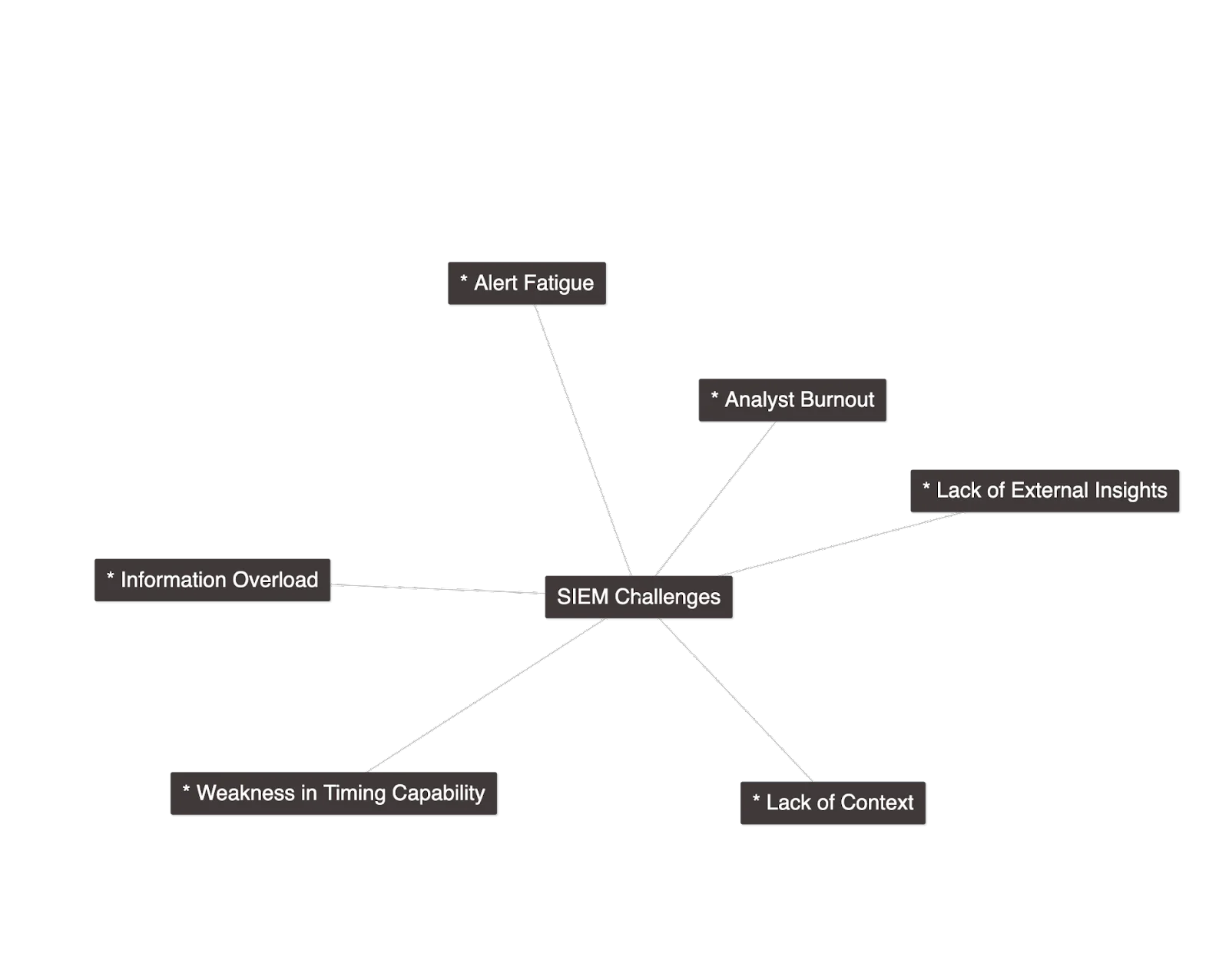
Main Challenges of SIEMs
- Information Overload/Alert Fatigue/Analyst Burnout: SIEMs generate thousands of security alerts daily, creating a labor-intensive process for SOC analysts. They often face the daunting task of manually sifting through an excessive amount of information to prioritize alerts. This deluge of alerts frequently leads to alert fatigue among security analysts. Excessive false positives can cause analysts to become desensitized or overwhelmed, diminishing their ability to recognize and respond to genuine alerts effectively.
- Lack of External Insights: Operating solely on internal data, SIEMs may fail to alert organizations about potential external threats targeting them. Without external context, SIEMs provide a limited view, leaving organizations potentially vulnerable to unrecognized external attacks.
- Lack of Context: While threat feeds can aid in uncovering new threats, they can also generate unnecessary work. This is due to the varying quality of feeds and a lack of contextual correlation with SIEM data. The prevalence of false positive alerts and noise complicates the already challenging environment. Analysts often need to invest hours to act effectively on these alerts, making manual triage essential in the tiered, layered structure of their workflow.
- Weakness in Timing Capability: The correlation is crucial for discovering new threats. However, given that Indicators of Compromise (IOCs) may only be valid for a certain period, correlating threat stream data with internal logs is necessary. The role that threat intelligence plays in this near real-time process is paramount. Identifying and operationalizing information from threat flow can be challenging with current SIEM capabilities.
As the attack surface expands and organizations are compelled to monitor an increasing number of incidents, they are becoming more aware of the limitations of their SIEM solutions. Faced with a multitude of alerts daily, SOC analysts seek efficient methods to determine which alerts to prioritize. This approach is crucial for optimizing their efforts and ensuring risk minimization.
Key Benefits of Integrating CTI with SIEM Solutions and the Role of SOCRadar
When properly implemented and managed, integrating SIEM with Cyber Threat Intelligence (CTI) can enhance an organization’s defenses, save time, and facilitate better strategic security decisions at the executive level. Let’s explore some of the key benefits.
1- Enhanced Threat Detection and Faster Response Capability: CTI provides vital context and insights into potential security threats, enabling organizations to identify suspicious activities that may be overlooked by traditional detection methods. Leveraging CTI from multiple sources (open source, deep/dark web) and consolidating this data into a Threat Intelligence Platform allows for swift detection and investigation of potential threats.
Combining internal intelligence gathered by SIEM with external threat intelligence strengthens real-time threat identification. CTI offers insights into emerging threats enriched with open source and dark web data such as malware, attack techniques, vulnerabilities, and Indicators of Compromise (IoCs). When integrated with a SIEM, this intelligence can correlate logs and events with threat intelligence indicators, enabling proactive detection and response to cyber threats and security incidents.
The volume of threat data emerging daily in the underground world is immense. Curating and aggregating this data from trusted sources and presenting it in a user-friendly manner is crucial for security teams to discern real threats from misleading information. SOCRadar’s Threat Feed and IoC Management module assists cybersecurity teams in investigating and analyzing threats through detailed data supported by user-friendly dashboards. Professionals can customize these streams, access the latest threat information, review current IoCs, and integrate them into security solutions like SIEM via the TAXII protocol.
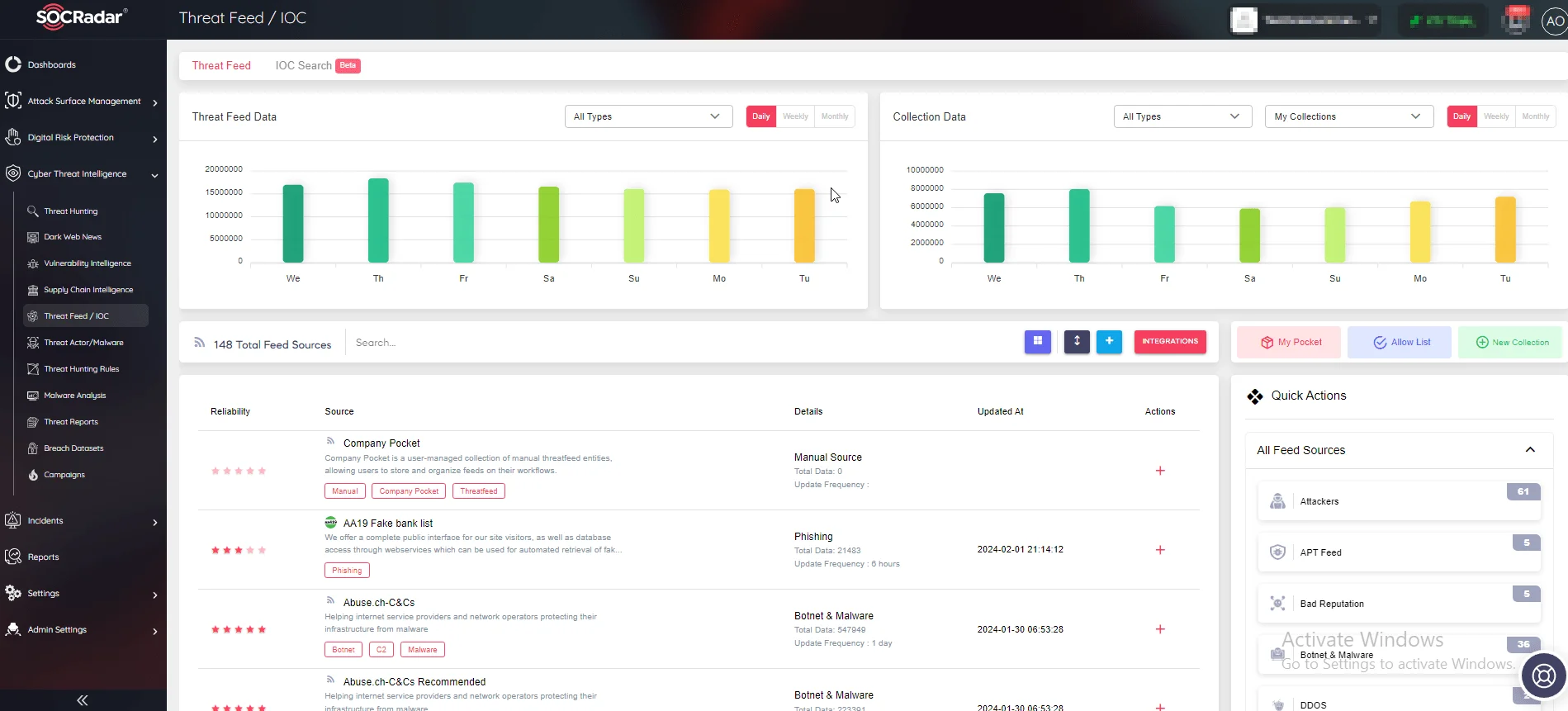
SOCRadar Threat Feed/ IOC Module
2) Improved and More Effective Incident Response: Integrating threat intelligence with built-in rules enables organizations to contextualize data for actionable insights and better understand cyber threats for timely action. By adding context to security events, CTI enables SIEM systems to more effectively analyze and prioritize alerts. With CTI data, SIEM alerts are enriched with information about the threat actor, Tactics, Techniques, and Procedures (TTPs), and the potential impact of an incident. This context aids security teams in making informed decisions about incident response.
Given that threat actors often select their victims strategically and can be sector-specific, obtaining contextual information from dark web intelligence on the changing TTPs and malware campaigns of cyber attackers becomes crucial for proactive measures.
With the SOCRadar Threat Actor/Malware module, users can obtain intelligence enriched with data from the MITRE ATT&CK database on current TTPs, which can be more crucial than modifiable IoCs for dynamically understanding and tracking cyber adversaries. Through automated data collection, classification, and AI-powered analysis of hundreds of sources across the surface, deep, and dark web, SOCRadar can alert you to the activities of Advanced Persistent Threat (APT) groups and aid in setting up scenarios to effectively detect and prevent malicious attempts.
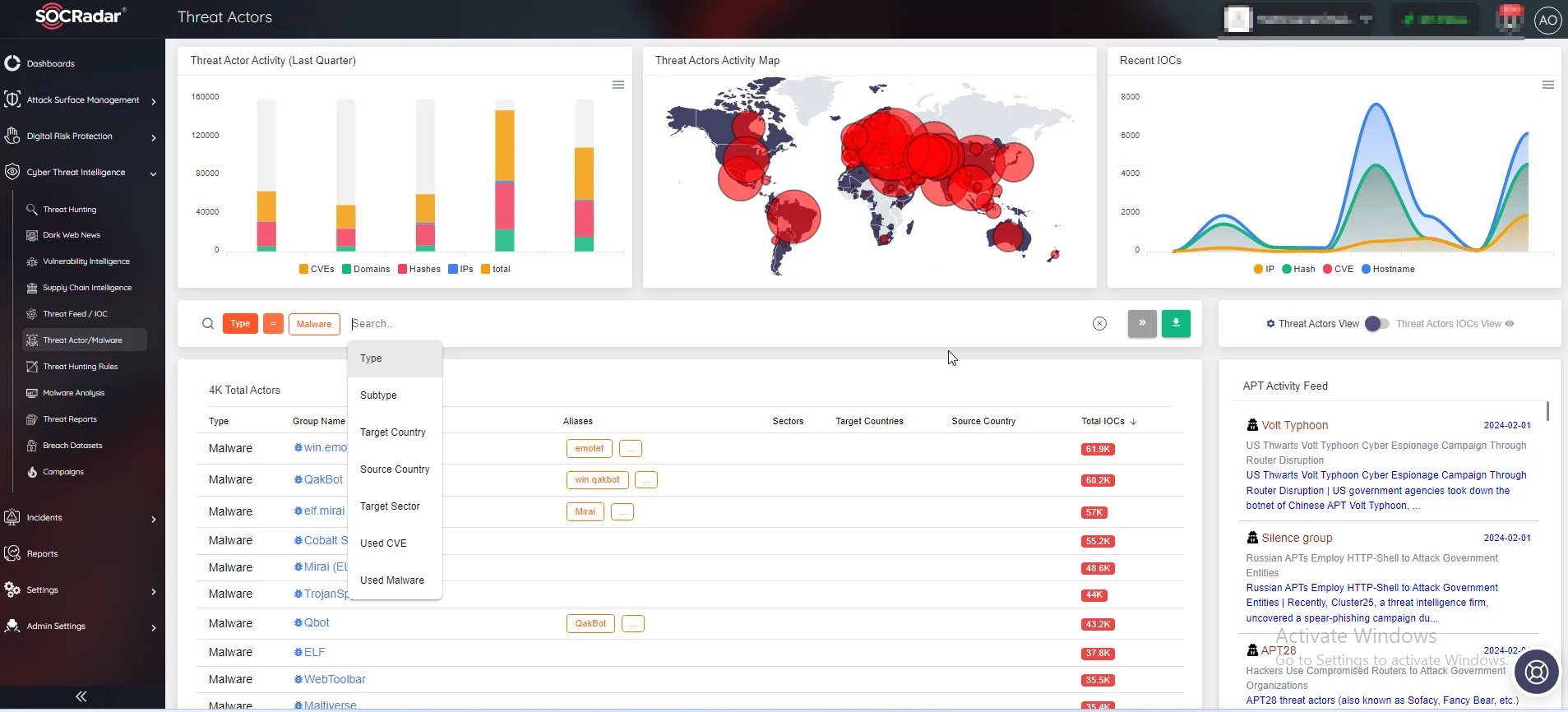
SOCRadar Threat Actors/Malware Module
3) Reducing False Positives: Integrating a Threat Intelligence Platform with SIEM solutions can significantly reduce false positives. By utilizing a user-driven scoring approach and contextual information about potential threats, organizations can enable security analysts to focus on more critical incidents, effectively eliminating less relevant threats.
Thanks to the threat intelligence flows provided by SOCRadar, it is possible to get rid of the traditional workflows you use for security research and remove false positives from your team’s queue before they turn into alerts.
4) Advanced Threat Hunting: A Threat Intelligence Platform can harness all collected intelligence information to identify patterns and trends in threat activity. This enables security teams to proactively hunt for potential threats. By developing more effective threat-hunting strategies, organizations can detect and mitigate potential threats before they cause serious, irreversible damage.
SIEMs can be programmed with rules designed to automatically monitor and correlate Indicators of Compromise (IoCs) with incoming logs. CTI data provides known malicious threat indicators such as IP addresses, domains, file hashes, or email addresses, which can be compared against incoming data. When a match is found, the SIEM can trigger an alert or an automated response, aiding in the early detection and prevention of threats.
The SOCRadar Threat Hunting module offers a comprehensive repository of Tactics, Techniques, and Procedures (TTPs) and Indicators of Attack (IoAs)/Indicators of Compromise (IoCs) for proactive investigation. It provides threat intelligence information gathered and analyzed from a broad spectrum of open and dark web sources available for threat hunters. This extensive database enables the analysis of retrospective, current, and future potential threats and cyber-attacks, as well as the investigation of suspicious incidents. Investigations may focus on a suspicious domain name, IP address, or TTP-level information about an active threat actor.
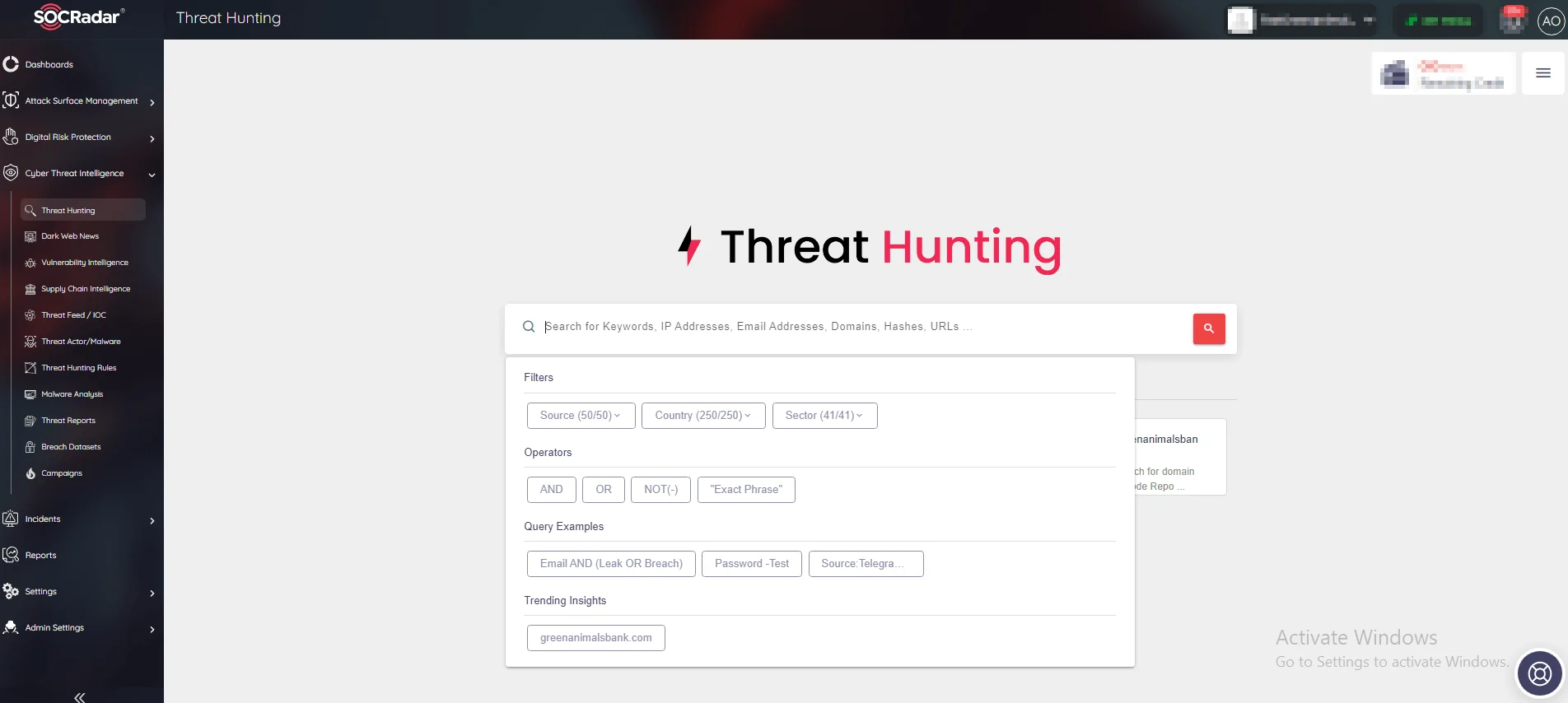
SOCRadar Threat Hunting Module
5) Improved Collaboration and Productivity: Utilizing a Threat Intelligence Platform to investigate potential threats enables teams to collaborate effectively and respond efficiently to threat actors targeting the organization. It helps automate previously manual tasks and enhances the efficiency of security operations. Within the Threat Intelligence Platform, organizations can learn about the Tactics, Techniques, and Procedures (TTPs) of threat actors and use this information to develop effective response strategies.
In summary, integrating Cyber Threat Intelligence with a SIEM system is crucial for enhancing the system’s ability to identify, respond to, and mitigate cyber threats. Providing contextual information, real-time threat data, and customizable detection rules strengthens an organization’s cybersecurity posture and reduces the risk of data breaches and security incidents.
Conclusion
The rapid identification and remediation of security issues are vital for corporate security. It is advisable to evaluate the capabilities of various SIEM systems to select the one that best meets organizational needs. Security Information and Event Management (SIEM) is a technology that supports defensive actions within organizations. This platform aids security teams in identifying threats specific to their organization. A significant advantage of SIEM platforms is that they provide businesses with time to block and combat attacks, minimizing damage defensively. A SIEM platform can also perform automated actions to block suspected malicious traffic, allowing SOC analysts to quickly identify relevant threats and take faster action. However, as mentioned earlier, this technology also presents many challenges and limitations.
A robust threat intelligence strategy is essential for understanding the risks in cyberspace and finding ways to mitigate them. A business unprepared for cyber threats is at risk of failure. Cyber attacks often occur stealthily, frequently bypassing security measures, making them increasingly difficult to block and stop. For example, ransomware attacks can hold businesses hostage until a ransom is paid. Instead of being reactive, it is necessary to develop a proactive strategy to protect systems from threats.
SOCRadar assists organizations in reducing cybersecurity risks with a leading threat intelligence solution powered by artificial intelligence. It provides comprehensive context from threat feeds and real-time updates, seamlessly integrating with SIEM solutions to offer up-to-date intelligence insights.



































