Dark Web Profile: RansomHub
[Update] June 6, 2024: “RansomHub Adds ZeroLogon Vulnerability to Its Arsenal”
[Update] April 8, 2024: “From ALPHV to RansomHub: Change Healthcare”
A new threat actor has emerged in the ransomware landscape, distinguishing themselves by making claims and backing them up with data leaks. In February 2024, RansomHub posted its first victim, the Brazilian company YKP. Since then, they have made 17 additional claims, although their leak site currently lists only 14 victims.

RansomHub’s logo on their leak site’s main page
Who is RansomHub
As stated on the group’s About page, RansomHub comprises hackers from various global locations united by a common goal of financial gain. The gang explicitly mentions prohibiting attacks on specific countries and non-profit organizations.
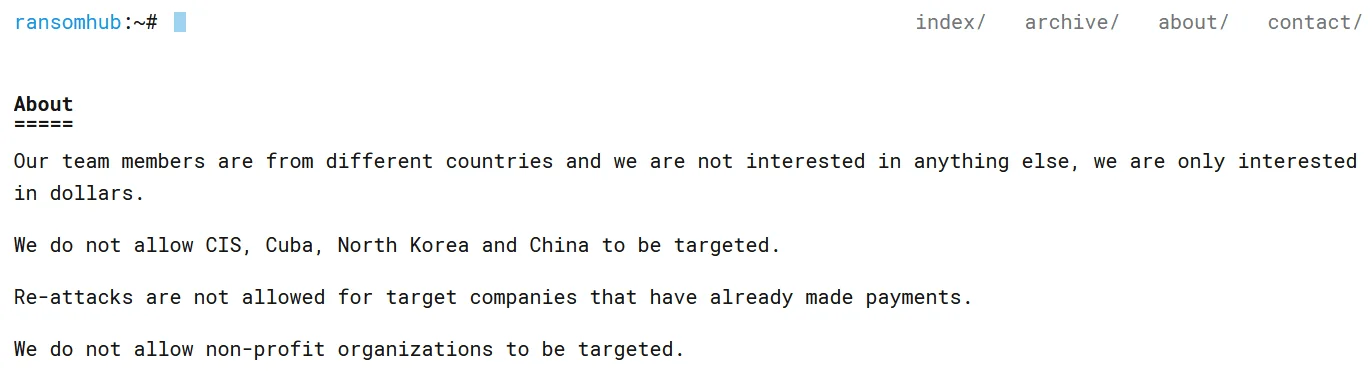
RansomHub’s “About” page
The gang’s website states that they refrain from targeting CIS, Cuba, North Korea, and China. While they suggest a global hacker community, their operations notably resemble a traditional Russian ransomware setup. Their stance on Russian-affiliated nations and the overlap in targeted companies with other Russian ransomware groups are also worth noting.
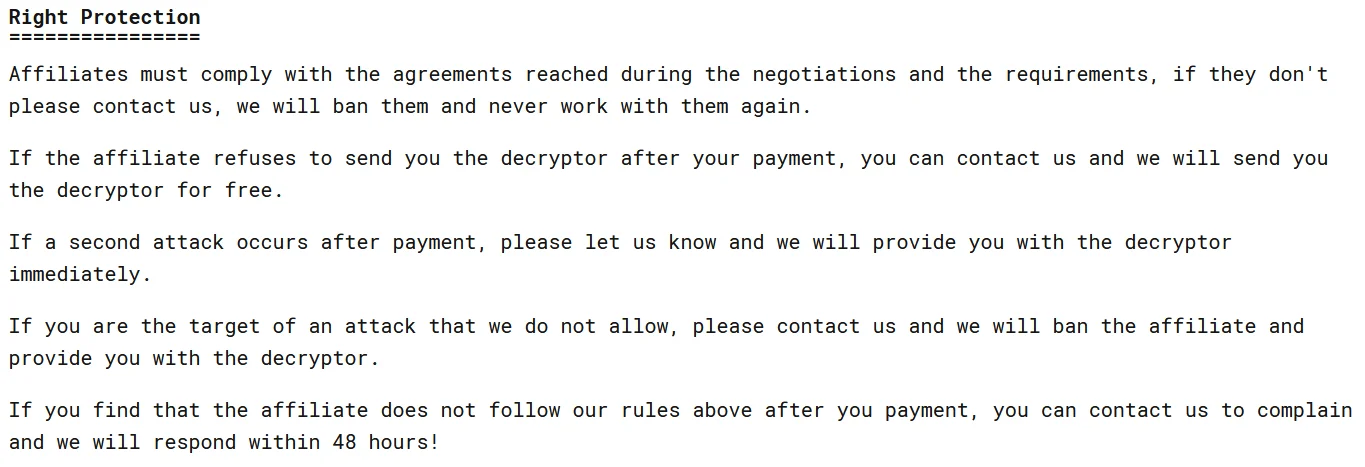
RansomHub’s “About” page-2
The “Right Protection” segment on their About page delineates guidelines for affiliates and underscores the importance of “conscientiousness.” This section also discloses that RansomHub functions as a ransomware group in collaboration with affiliates, thus we can classify it as a Ransomware-as-a-Service (RaaS) group.
RansomHub asserts that affiliates must adhere to the agreements and requirements set during negotiations, warning that failure to do so will result in a ban and termination of collaboration.
Furthermore, they promise to provide victims with a free decryptor if the affiliate fails to do so after receiving payment or if an off-limits organization is targeted. Therefore, the group’s chosen ransomware is evidently capable of encrypting data before exfiltration.
The group tries to recruit its affiliates from the mostly Russian populated RAMP forum, and also states that its strains are ESXi rewritten in Golang.
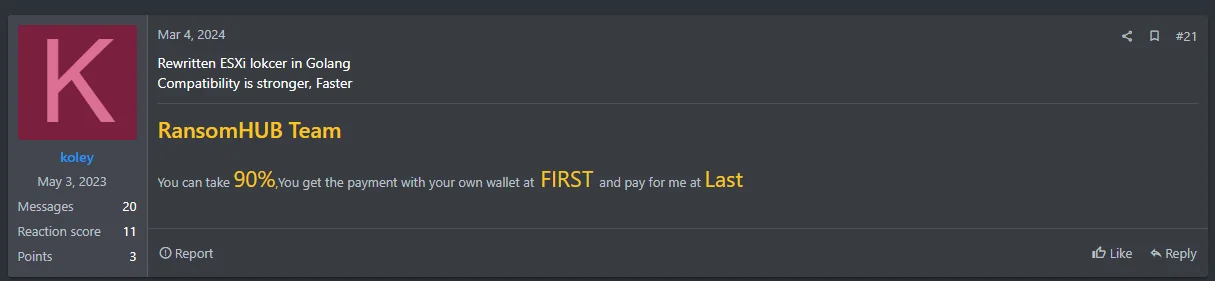
There has been limited activity on the RAMP forum since May 3, indicating that they may have acquired a sufficient number of affiliates for the time being.
Affiliates receive 90% of the money, while the remaining 10% goes to the main group. In contrast to the common practice, the money is initially sent to the affiliate, a feature that is highly regarded in the ransomware community. This approach addresses the distrust caused by ALPHV’s $22 million scam, where affiliates were not compensated, leading to significant mistrust in the Ransomware-as-a-Service (RaaS) environment.
Victimology
As Cyberdaily suggested, on their data leak site, it seems that the affiliates themselves handle the postings. How victims are listed varies, including differences in the presentation of evidence for each hack and the language used. Some posts link to a hosting service for sharing proof-of-hack documents, while others include screenshots directly in the leaked post.
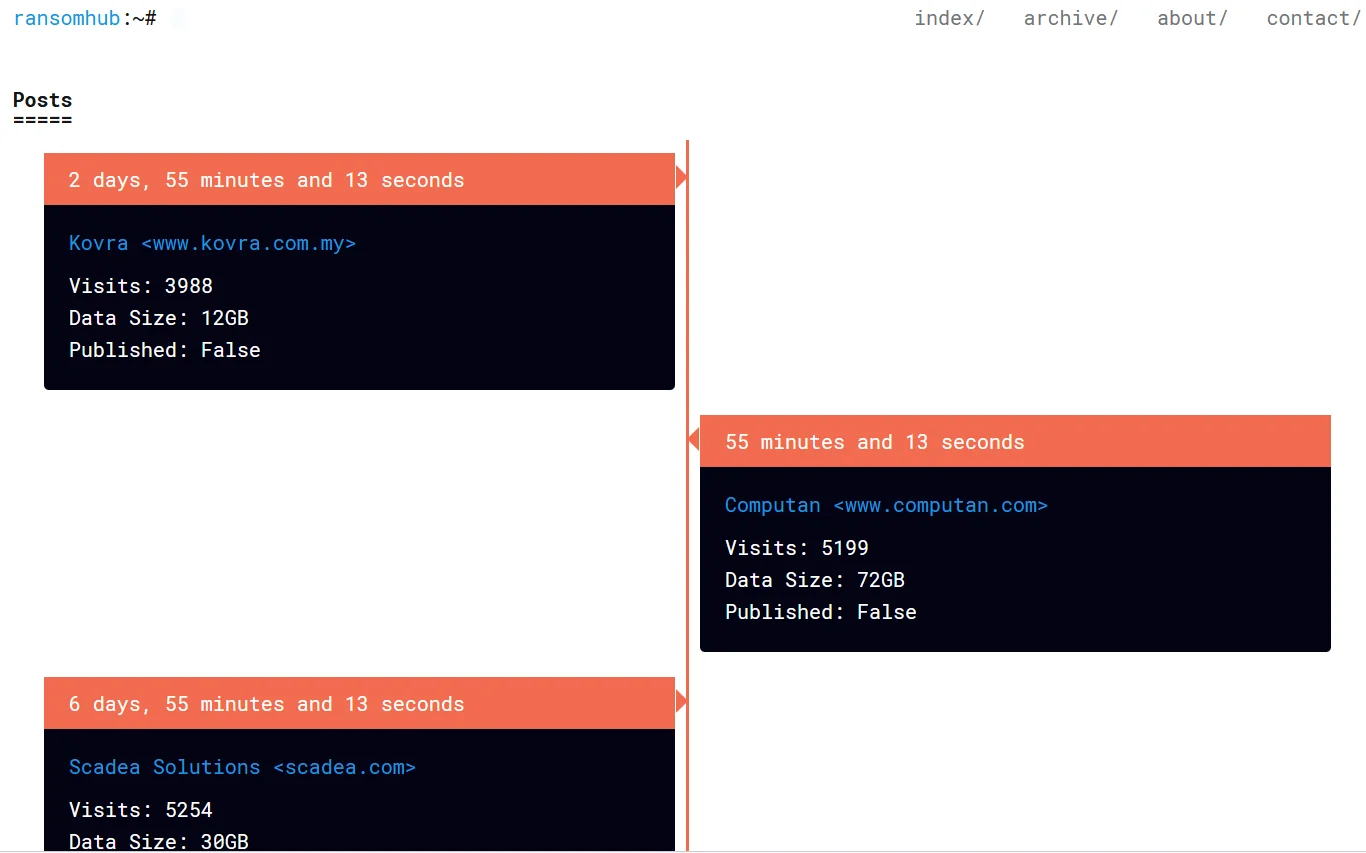
RansomHub’s victim listings
Threat actors are listing victims from various countries without following a specific pattern, targeting a diverse range of nations such as the US, Brazil, Indonesia, and Vietnam. While notably large companies have not appeared on the list so far, healthcare-related institutions, which are considered critical sectors, are among the listed victims.
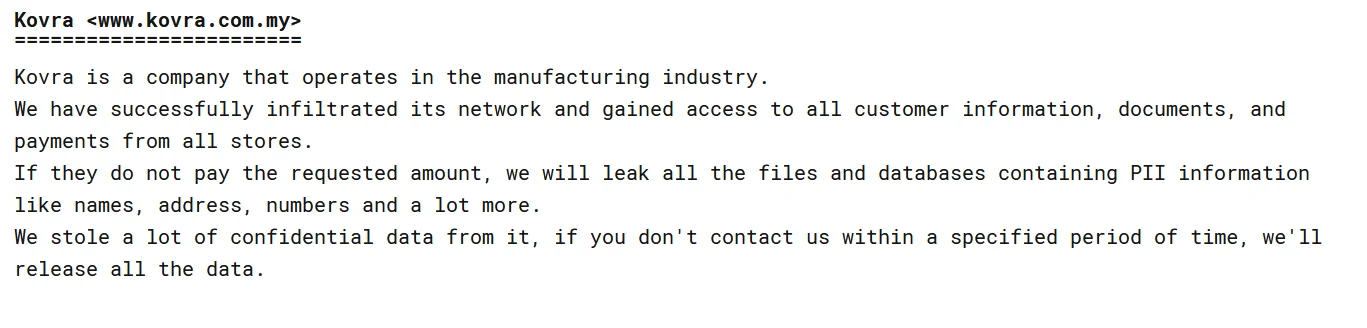
Latest recorded victim is manufacturing company Kovra
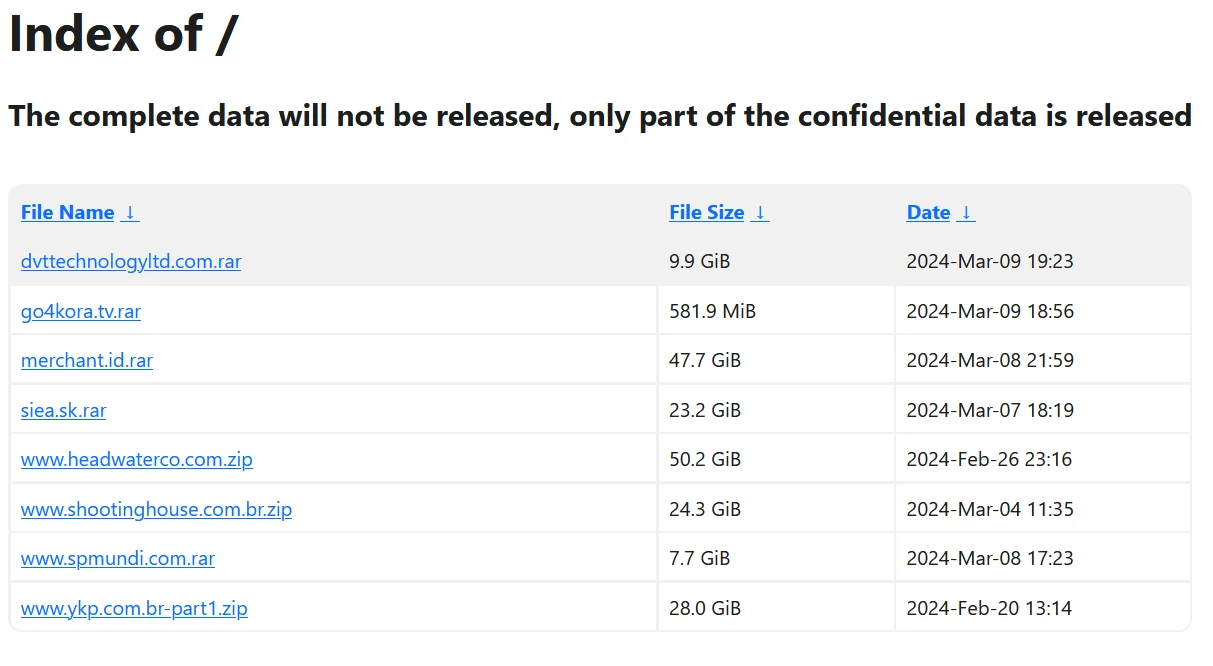
The RansomHub group also hosts sample data from victims from whom it could not receive payment, available for download on its website.
What is to Come?
The RansomHub group seems to be a recently emerged ransomware group, likely with roots in Russia. Due to the benefits it offers its affiliates and the strict controls it enforces, they could be vying for the leadership position amidst pressure from security forces to major players like LockBit and ALPHV. However, their ransomware strains appear to be just a revised version of an old sample for now.
An interesting part is that this strain is also written in Golang language; GhostSec and GhostLocker ransomware, which recently attracted attention, also wrote their new versions in Golang language. Again, it may be a step that will shed light on future trends.
From ALPHV to RansomHub: Change Healthcare
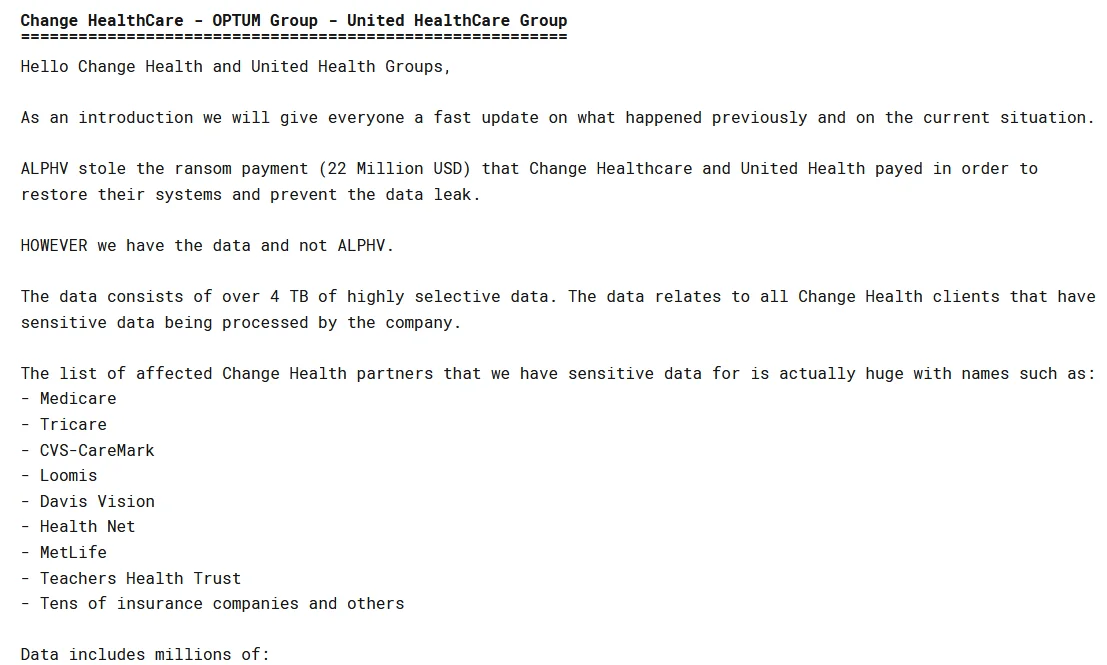
The RansomHub gang targeted two healthcare organizations, but the twist is that Change Healthcare, a company that had dealt with the ALPHV group before, is listed here again.
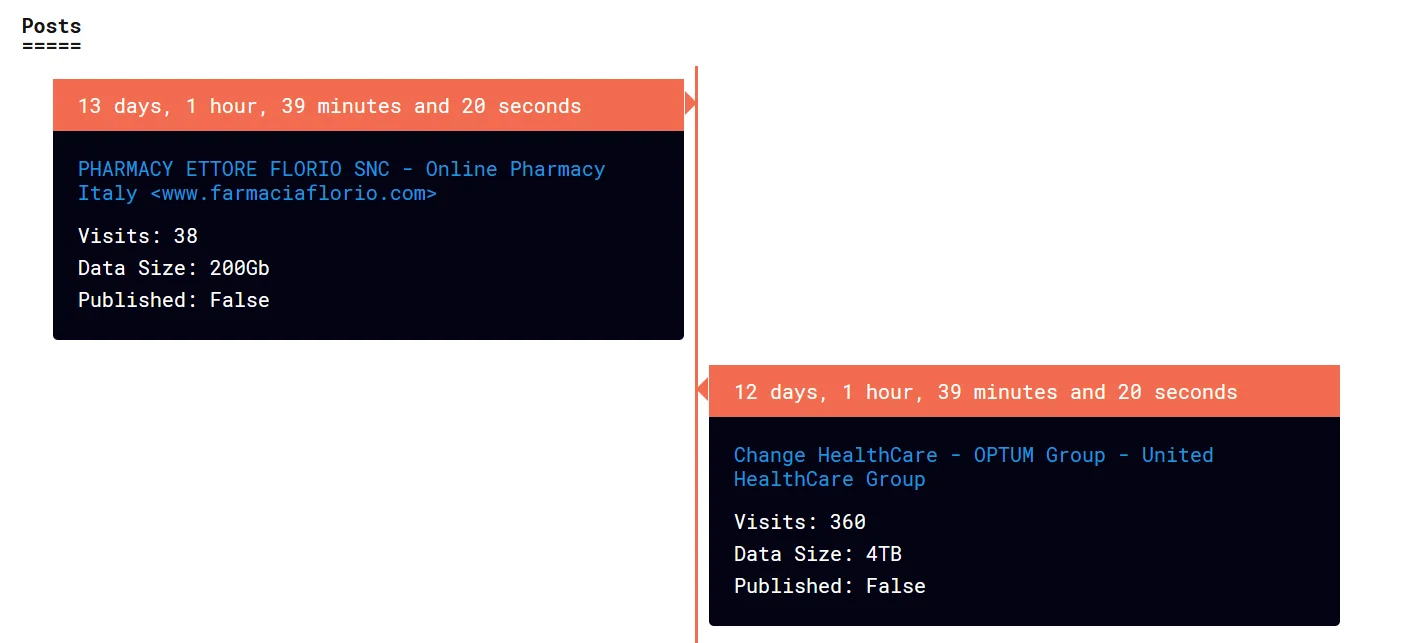
RansomHub’s latest victim listings
Change Healthcare got hit with ransomware before, allegedly by ALPHV. They say they didn’t pay, but the information found by researchers proved otherwise. It seems they shelled out around $22 million to get their data back. Later, when ALPHV got the money, they vanished without giving their partner the 80% cut they usually get. Practically, they made an exit scam.
About United HealthCare
About United HealthCare – 2
Now, RansomHub is in the picture. They’ve listed Change Healthcare on their site and claim to have their data, hinting at another extortion attempt.
Some claims were made even as RansomHub is just a new name for ALPHV or they’re playing a trick to scare Change Healthcare into paying up again.
However, it is tough to say that RansomHub is a rebranding. First of all, the leak sites appeared before ALPHV’s scamming incident, and the group also claims to have its own strain and partners.
Of course, it is not surprising that ransomware operators originating from the Russian cybercrime landscape have relationships with each other so a connection is always possible. Thus, a higher possibility is that RansomHub may have acquired the former ALPHV affiliate as its own partner.
As we mentioned in our previous headings, they offered much better opportunities for affiliates than other groups, and we also said that it was possible for ALPHV and LockBit affiliates to move under the umbrella of this group.
RansomHub Adds ZeroLogon Vulnerability to Its Arsenal
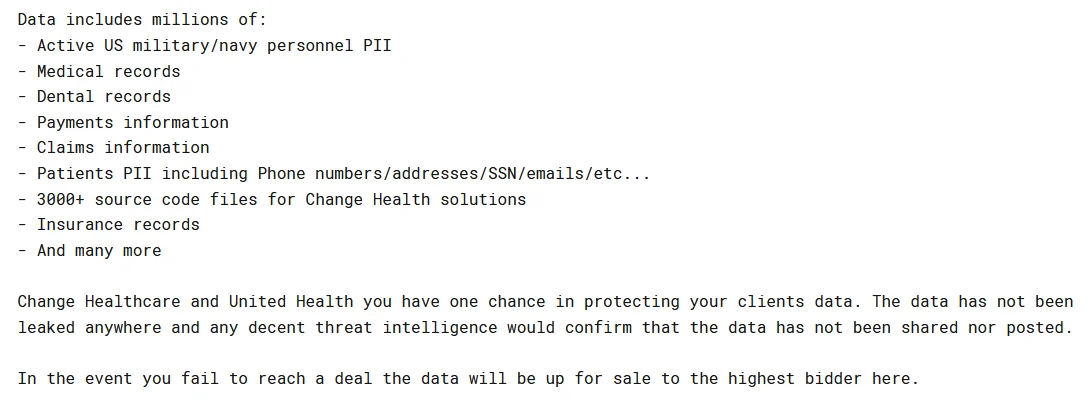
Recent ransomware attacks by the RansomHub group have leveraged the old but critical ZeroLogon vulnerability: CVE-2020-1472 (CVSS: 10).
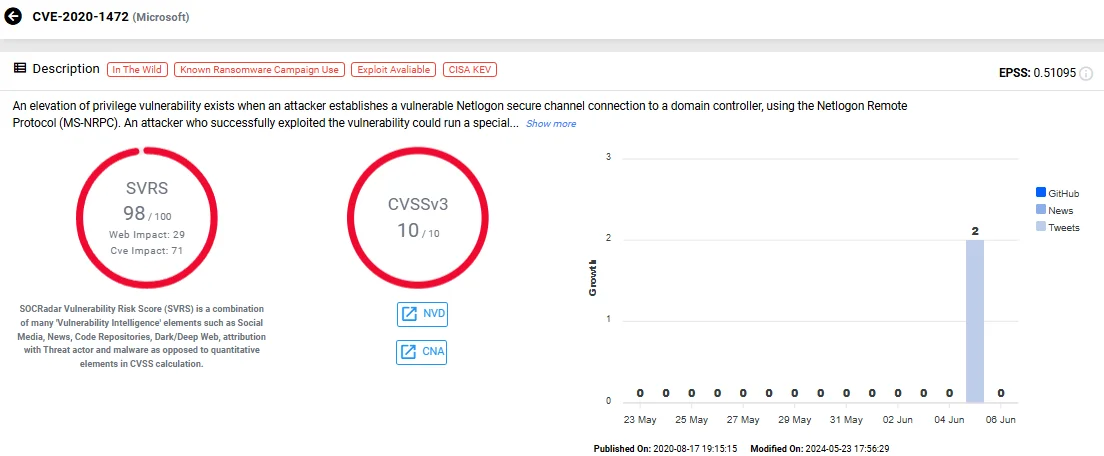
The ZeroLogon vulnerability, CVE-2020-1472 (SOCRadar’s Vulnerability Intelligence)
As one of the top 10 vulnerabilities used by ransomware actors, this flaw allows attackers to take over an organization’s domain controllers by establishing a vulnerable Netlogon secure channel connection. Successful exploitation enables an attacker to run specially crafted applications on network devices, obtaining domain administrator access.
Researchers report that in these attacks, RansomHub operators use tools like Atera and Splashtop for remote access and NetScan for network reconnaissance. Before deploying the ransomware, they use command-line tools such as iisreset[.]exe to stop all Internet Information Services (IIS) services.
Ransomware threat actors constantly evolve their tactics, discovering new ways or exploiting old vulnerabilities to infiltrate organizations. Organizations must patch these vulnerabilities to protect themselves from not only ransomware but all cyber threats.
Mitigation Advices for Ransomware
Although it is valid to establish a defense approach against threat actors through specific TTPs and IoCs, emphasis should be placed on general ransomware defense strategies rather than such an intense focus on dozens or even hundreds of groups that are similar to each other.
Regular Data Backup: Implement a robust backup strategy to regularly back up critical data and ensure its availability for recovery in case of a ransomware attack.
Security Awareness Training: Educate employees about ransomware threats, phishing tactics, and cybersecurity best practices to reduce the risk of falling victim to malicious attacks.
Patch and Update Management: Keep operating systems, software, and applications up to date with the latest security patches and updates to address known vulnerabilities that could be exploited by ransomware.
Network Segmentation: Implement network segmentation to separate critical systems and sensitive data from less secure parts of the network, reducing the potential impact of ransomware infections.
Access Control: Restrict user privileges and access rights based on the principle of least privilege to minimize the attack surface and limit the spread of ransomware within the network.
Email and Web Security: Deploy advanced email filtering and web security solutions to detect and block malicious attachments, links, and phishing attempts that could deliver ransomware payloads.
Endpoint Protection: Use endpoint security solutions such as antivirus software, Intrusion Detection Systems (IDS), and Endpoint Detection and Response (EDR) tools to detect and mitigate ransomware threats on endpoints.
Incident Response Plan: Develop and regularly test an incident response plan specifically tailored to ransomware attacks. This plan should include procedures for identifying, containing, mitigating, and recovering from ransomware incidents.
Regular Security Audits: Conduct regular security audits, vulnerability assessments, and penetration testing to identify and remediate security gaps and weaknesses that could be exploited by ransomware attackers.
Backup Testing and Verification: Regularly test and verify backup data to ensure its integrity and usability for recovery purposes, and store backup copies securely to prevent unauthorized access.
By implementing these mitigation strategies, organizations can enhance their resilience against ransomware attacks and minimize the potential impact on their operations and data.
SOCRadar against Ransomware
SOCRadar offers proactive threat monitoring and intelligence solutions designed to bolster your organization’s security posture. Through our platform, you gain the capability to proactively search for specific threat actors and obtain comprehensive insights into their tactics, targeted vulnerabilities, affiliations with other actors, and indicators of compromise. This empowers you to stay ahead of potential threats and take preemptive measures to protect your assets.
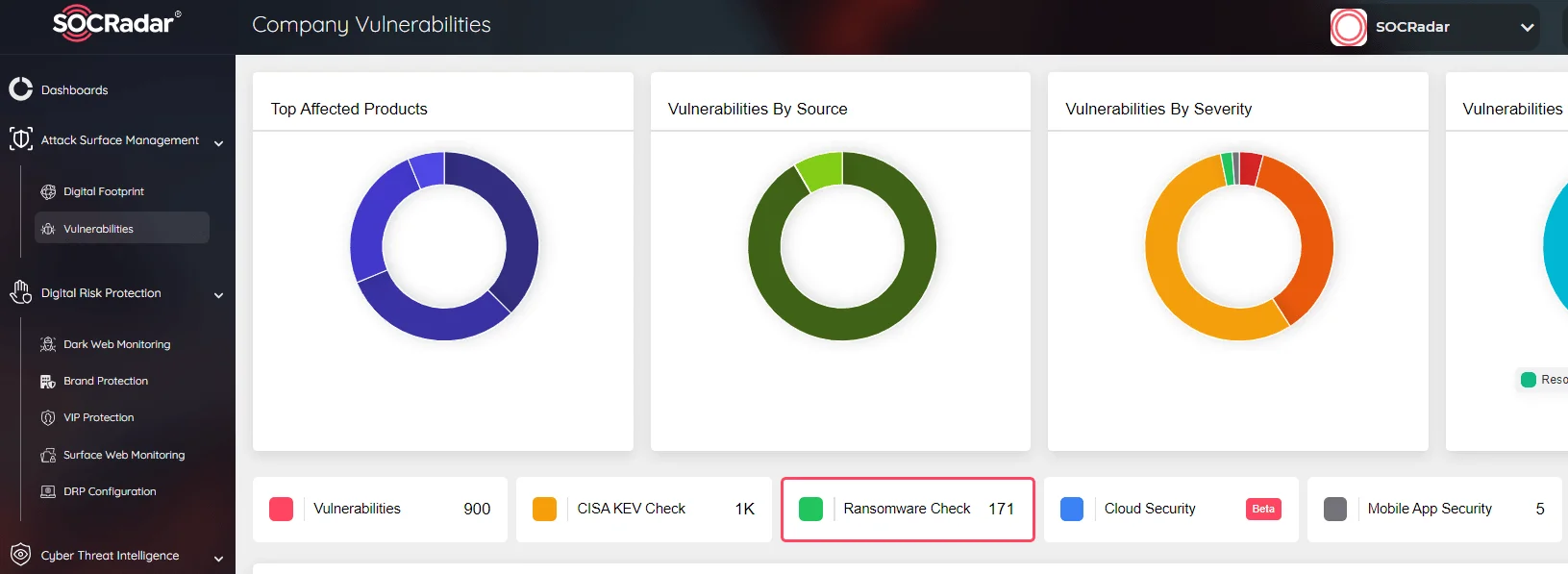
SOCRadar, Attack Surface Management Module with Ransomware Check function
Moreover, our Attack Surface Management module provides continuous monitoring of all potential attack vectors, ensuring that you receive timely alerts about any suspicious activity. This proactive approach enables you to swiftly respond to threats and strengthen your overall cybersecurity defenses.