Dark Web Profile: Scattered Spider
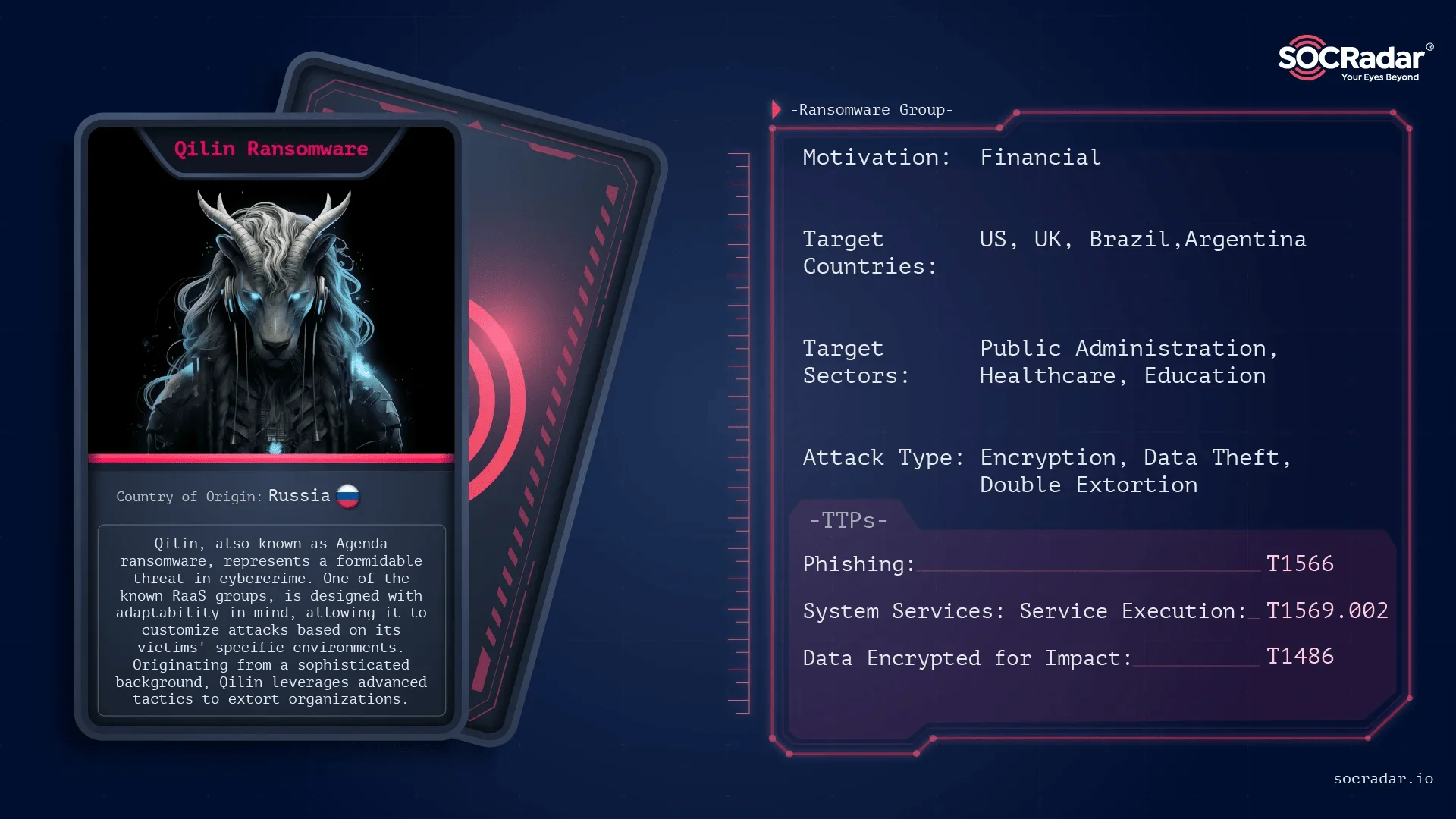
[Update] July 17, 2024: “Collaboration with Qilin Ransomware”
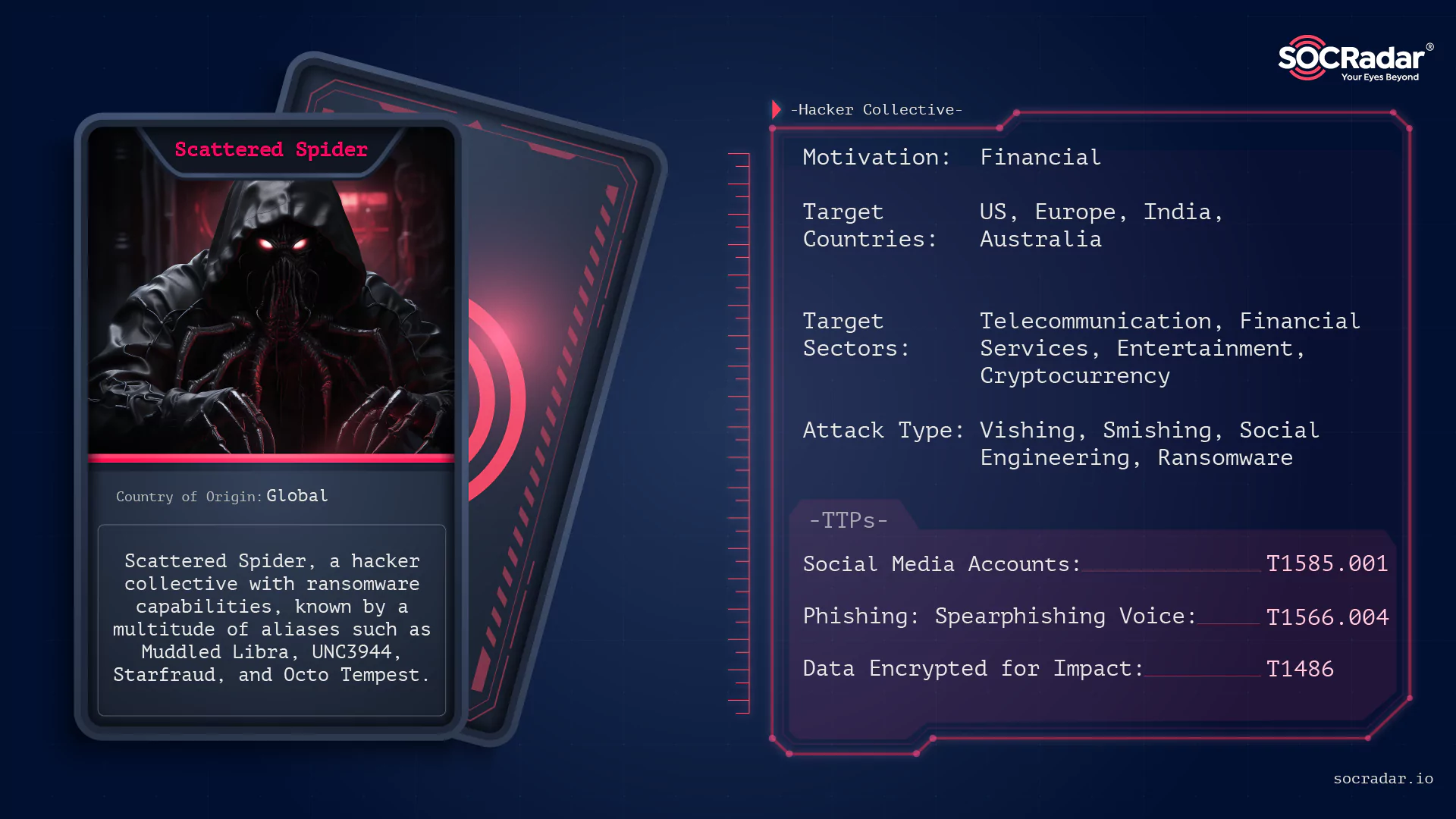
One hacker collective continues to confound federal law enforcement and cybersecurity experts — the Scattered Spider. Known by a multitude of aliases such as Muddled Libra, UNC3944, Starfraud, and Octo Tempest, this hacking group has not only infiltrated major corporate networks like MGM Resorts and Caesars Entertainment but has done so with a bold audacity that leaves many wondering.
Threat actor card of Scattered Spider
Despite claims that the FBI and other agencies have known the identities of the Scattered Spider cybercriminals for over six months, the group remains elusive to the public. The challenge lies in law enforcement’s struggle to adapt to the chaotic and loosely structured nature of modern cyber threats, according to Bugcrowd founder Casey Ellis. This difficulty is highlighted by the FBI’s inability to disrupt groups like Scattered Spider, as emphasized by Callie Guenther, senior manager at Critical Start. The case underscores the broader challenges faced by law enforcement in the digital age, indicative of a new era of cyber threats that demand a robust and innovative response from both law enforcement and cybersecurity experts.
This article delves into the intricacies surrounding Scattered Spider, exploring the disconnect between federal knowledge and operational disruptions. As we navigate through the twists and turns of this cyber saga, we’ll unravel the tactics employed by the group, their evolution from leveraging phishing kits to becoming affiliates of Ransomware-as-a-Service (RaaS) providers, and the alarming escalation into threats of physical violence to coerce victims into compliance.
Who is Scattered Spider?
Scattered Spider, a name that resonates with notoriety in the cybersecurity realm, is a cybercriminal collective known for its sophisticated and multifaceted cyber attacks. This group’s origin is shrouded in ambiguity, but its impact is unmistakable, marked by a series of high-profile infiltrations and data breaches.
Interestingly, this group consists of young English-speaking members, some as young as 16, with different skills. They all hang out on hacker forums. Thus, pinpointing the persons behind Scattered Spider’s actions can be quite a challenge. Some of these Scattered Spider members seem to have ties to ALPHV and the ability to use BlackCat ransomware, making the situation even more confusing to figure out who’s who.

Illustration of Scattered Spider (generated using DALL-E 3)
The Many Faces of Scattered Spider
For Scattered Spider many aliases are appointed, each signifying a different aspect or evolution of their operations in the very short life span of them. Although these names are sometimes thought of as different groups and can sometimes be interpreted as such, we think of them as the same groups due to the similarity of TTPs.
Those stated by CISA to be the same groups are:
Scattered Spider as their most common alias and Scatter Swine in their early days.
Muddled Libra: Under this moniker, Scattered Spider has been linked to a range of deceptive practices, including the use of fake websites and social engineering tactics to manipulate victims.
UNC3944: This name is associated with their more aggressive ransomware attacks and data breaches. UNC3944 operations often involve complex strategies to infiltrate and extract valuable data from their targets.
Starfraud: Reflecting a more financially motivated aspect of their activities, Starfraud operations typically involve credit card fraud and other forms of financial deception.
Names that were not mentioned in the CISA report are:
Octo Tempest: Known for their adaptability and the use of ransomware, Octo Tempest represents the group’s evolution into using more destructive forms of cyberattacks, including ransomware deployment and data destruction.
0ktapus: This alias highlights their targeted phishing campaigns, particularly those aimed at infiltrating corporate networks through credential theft. The 0ktapus operations are characterized by their precision and focus on acquiring access to secure systems.
Also, LUCR-3 and Storm-0875 as their less known assigned names.
Overlap with the Comm: Some of the members are believed to also be part of the “Comm”. Across various Discord servers and Telegram group chats, potentially thousands of individuals engage in what is loosely referred to as “Comm,” an ambiguous network comprising hackers, gamers, and more.
Evolution of Scattered Spider
The webs woven by the Scattered Spider began to be seen in June 2022, from a group of opportunistic hackers to a formidable cybercriminal syndicate is a testament to their adaptability. Initially, their attacks were more rudimentary, focusing on phishing and small-scale data breaches. However, as they gained resources and maybe the expertise, their operations evolved into sophisticated, multi-layered campaigns targeting large corporations and critical infrastructure.
Their evolution is marked by a transition from simple phishing kits to becoming affiliates of Ransomware-as-a-Service (RaaS) providers. According to CISA, Scattered Spider threat actors have traditionally been involved in data theft for extortion purposes. Additionally, they have been observed employing the BlackCat/ALPHV ransomware in conjunction with their standard Tactics, Techniques, and Procedures (TTPs). This shift not only expanded their capabilities but also their reach, affecting a broader spectrum of industries and geographies.
A Global Threat
Scattered Spider’s activities are not confined to any single region; they are a global menace. Their targets have included major corporate networks, financial institutions, and even government agencies, spanning across continents. This global footprint underscores the need for international cooperation in cybersecurity efforts to counter such borderless threats.

Most targeted countries so far by Scattered Spider (Source: SOCRadar)
While the map shows only some countries Scattered Spider targeted many more organizations in various countries and by their breaches nearly all of the countries and their citizens were affected.
Modus Operandi of Scattered Spider
Scattered Spider’s operational tactics are not just diverse; they are insidiously innovative, much like an octopus extending its tentacles into multiple facets of cybercrime. This group has mastered the art of initial access, leveraging a variety of sophisticated methods to infiltrate their targets.
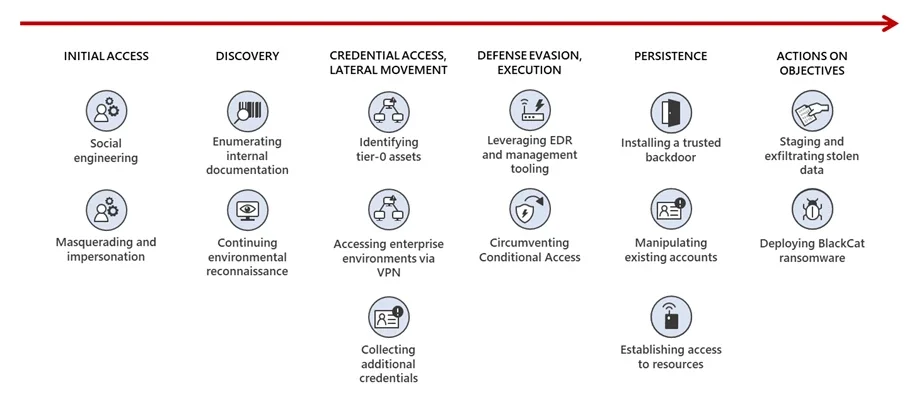
Attack flow of Scattered Spider (Microsoft)
At the core of their initial access strategy lies their expertise in phishing. They craft convincing emails and messages, often impersonating trusted entities, to deceive victims into revealing sensitive information or downloading malicious software. Scattered Spider initiates their campaigns by sending carefully crafted phishing emails, targeting individuals within organizations. Through these deceptive tactics, they aim to gather credentials, including usernames, passwords, and personally identifiable information (PII).
Once armed with this initial set of information, Scattered Spider proceeds to escalate their info set. In some instances, they leverage social engineering techniques, posing as trusted entities such as help desk personnel. This allows them to guide unsuspecting employees to install commercial remote access tools, providing a gateway into the victim’s network.
Scattered Spider also explores other avenues for phishing, such as mobile phishing (smishing) and voice-based spear phishing, showcasing their versatility in exploiting different communication channels. By convincing IT help desk personnel to reset passwords and Multi-Factor Authentication (MFA) tokens, they gain further control over the compromised accounts.
They even create domains and establish fake social media accounts. These serve as tools in their arsenal for phishing and smishing attempts against targeted organizations. The threat actors precisely craft their online presence to backstop newly created user accounts, contributing to a web of deception.
Once access is gained, it begins to follow the next steps of the Cyber Kill Chain., Scattered Spider demonstrates persistence in maintaining access to the compromised network. They create new user identities within the targeted organization and may modify MFA tokens to adapt to changing security measures. The abuse and control of valid accounts become a cornerstone of their approach, ensuring continued network access even when passwords are altered.
CVE’s used by Scattered Spider (Source: SOCRadar)
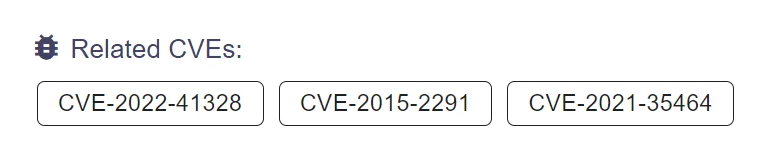
Scattered Spider observed exploited known vulnerabilities. These vulnerabilities can be listed as:
- CVE-2015-2291: This vulnerability affects the Intel Ethernet diagnostics driver for Windows (specifically IQVW32.sys before 1.3.1.0 and IQVW64.sys before 1.3.1.0). It allows local users to cause a Denial of Service or possibly execute arbitrary code with kernel privileges through a crafted IOCTL call.
- CVE-2021-35464: This is a Java deserialization vulnerability in the ForgeRock AM server before version 7.0. It occurs in the jato.pageSession parameter on multiple pages. The vulnerability can be exploited without authentication and allows for remote code execution by sending a crafted /ccversion/* request to the server.
- CVE-2022-41328: This vulnerability is a path traversal issue found in Fortinet FortiOS versions 7.2.0 through 7.2.3, 7.0.0 through 7.0.9, and before 6.4.11. It is due to an improper limitation of a pathname to a restricted directory (‘path traversal’). A privileged attacker can exploit this vulnerability to read and write files on the underlying Linux system via crafted CLI commands.
Moving forward, Scattered Spider strategically focuses on privilege escalation, aiming to gain higher-level account privileges within the targeted organization’s network. Domain policy modifications, including adjustments to domain trust, become part of their arsenal, enhancing their control and maneuverability.
To evade security solutions, the threat actors display a nuanced understanding of cloud compute infrastructure. They modify and create instances in cloud environments for lateral movement and data collection, evading typical security measures. Additionally, their impersonation tactics involve posing as IT and helpdesk staff, creating an added layer of complexity in their attempts to gain access.
They deploy tools like Raccoon Stealer to obtain login credentials and forge web credentials, showcasing a multi-faceted approach to credential access. Multi-Factor Authentication (MFA) request generation becomes another tool in their arsenal, manipulating user prompts to gain access.
Discovery unfolds as a pivotal chapter, where Scattered Spider scours the compromised network for valuable information. They target SharePoint sites, seek credential storage documentation, and enumerate Active Directory to identify key assets and support future operations. Browser information, cloud service dashboards, and file and directory discovery contribute to their comprehensive reconnaissance efforts.
Lateral movement becomes a strategic maneuver for Scattered Spider as they navigate the target network, utilizing pre-existing cloud instances and remote services for data collection. Their movements are calculated and methodical, demonstrating a deep understanding of the network’s structure.
With data in their possession, the threat actors transition to the later phase. They search code repositories, SharePoint, and cloud storage for information, staging data from various sources before exfiltration. Email collection becomes a crucial element, allowing them to determine if the intrusion has been detected and if security responses have been initiated.
Exfiltration marks the final act of their operation. Scattered Spider exfiltrates sensitive data from the target network, often utilizing various web services and data centers for storage. Their methods extend to data encryption with BlackCat ransomware, demanding ransoms for decryption, and even encrypting VMware ESXi servers.
Toolkit
- Raccoon Stealer
- VIDAR Stealer
- BlackCat Ransomware
- Fleetdeck.io
- Level.io
- Mimikatz
- Ngrok
- Pulseway
- Screenconnect
- Splashtop
- Tactical.RMM
- Tailscale
- Teamviewer
- AveMaria
Notable Attacks and Campaigns of Scattered Spider
Scattered Spider has orchestrated several high-profile attacks and campaigns, targeting a range of companies, industries and countries. Their operations have not only caused significant disruptions but also highlighted their capability to infiltrate and compromise well-protected networks.
Major Corporate Infiltrations
Some of their recent headlines have primarily revolved around casino hacks. Scattered Spider gained access to Caesars’ and MGM’s internal systems through social engineering in 2023. The group bypassed multi-factor authentication technologies by attaining login credentials and one-time passwords. The group claims that it targeted MGM due to them catching the group attempting to rig slot machines in their favor.
MGM Resorts Cyber Attack: One of the most notable attacks attributed to Scattered Spider was the cyber attack on MGM Resorts. This attack resulted in a significant data breach, compromising the personal information of millions of guests.

MGM Resorts International’s announcement about the cyber incident (Source: APMdigest)
Caesars Entertainment Breach: Another major attack was against Caesars Entertainment. This breach demonstrated Scattered Spider’s ability to penetrate the defenses of large-scale hospitality companies. Schubert Jonkheer & Kolbe LLP, which is investigating this incident, warned the Caesars’ Customers about the risk of a data breach, underlining that there are more than 65 million rewards program members’ PII in the allegedly stolen databases.
Telecom and BPO Companies: Since June 2022, Scattered Spider has targeted telecom and Business Process Outsourcing (BPO) companies. The group has been establishing persistence mechanisms and, notably, undoing implemented mitigations to regain entry to the compromised networks. These attacks were primarily focused on data exfiltration and espionage.
Blackmailing the Riot Games: Scattered Spider has compromised Riot Games via a social engineering attack and gathered the source code of Riot’s games League of Legends and Teamfight Tactics. The group has demanded $10 million, but Riot Games has refused to pay that and announced it on a Tweet thread.
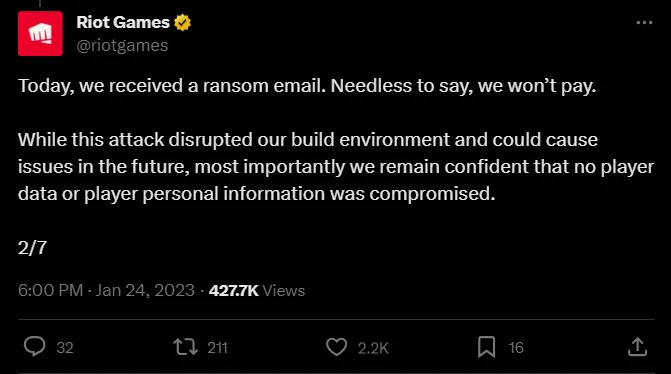
Riot Games’ Tweet about responding Scattered Spider’s blackmail (Source: X)
Furthermore, MailChimp, Twilio and DoorDash can be listed as their other major targets.
Collaboration with Qilin Ransomware
In recent news, Microsoft has linked the notorious Scattered Spider group to Qilin ransomware attacks. Scattered Spider, also known as UNC3944, has been under scrutiny for its sophisticated social engineering tactics and advanced intrusion techniques. The connection to Qilin ransomware marks a significant escalation in its operations, indicating its evolving capabilities and increasing threat to various sectors.
According to Microsoft’s latest findings, Scattered Spider has adopted Qilin ransomware to target high-profile organizations, leveraging its advanced encryption methods to cause extensive disruptions. For more information check out our blog post about Qilin Ransomware.
Conclusion
In summarizing the threat Scattered Spider poses, we recognize a cybercriminal group that is versatile in its aliases and methods and formidable in its impact. This group has demonstrated a sophisticated range of cyber activities, from intricate phishing schemes to advanced ransomware attacks. Their ability to target high-profile organizations across different industries and countries highlights their global reach and the serious threat they pose.
The insights provided by cybersecurity experts and agencies like CISA have been invaluable in understanding Scattered Spider’s modus operandi. However, the group’s elusive nature and advanced evasion techniques still present significant challenges in accurately attributing their activities.
As we face such dynamic and dangerous adversaries, the importance of proactive and adaptive security measures becomes clear. Organizations must prioritize regular updates to security protocols, educate employees on emerging cyber threats, and develop robust incident response strategies. In doing so, we can better prepare for and respond to the volatile and sophisticated dangers that groups like Scattered Spider pose.
Security Recommendations: Guarding Against Scattered Spider
Organizations must implement security measures in response to the specific threats posed by the Scattered Spider group. Drawing from the insights provided in the article above, here are specific recommendations to enhance defenses against Scattered Spider’s tactics:
Strengthen Multi-Factor Authentication (MFA): Scattered Spider has been known to exploit weaknesses in MFA implementations. Organizations should ensure that their MFA setup is robust, using the most secure methods available, such as virtual MFA devices, hardware tokens or biometric verification, which are less susceptible to interception or duplication like SIM Swapping.
Enhance Employee Awareness and Training: Given Scattered Spider’s reliance on phishing tactics, regular training for employees on recognizing and responding to phishing attempts is vital. This includes being cautious of unsolicited communications, verifying the authenticity of messages, and understanding the protocols for reporting suspicious activities.
Implement Advanced Phishing Protection: Utilize advanced email filtering solutions that can detect and block phishing attempts. These solutions should be capable of analyzing the authenticity of the sender, the content of the message, and any embedded links or attachments for potential threats.
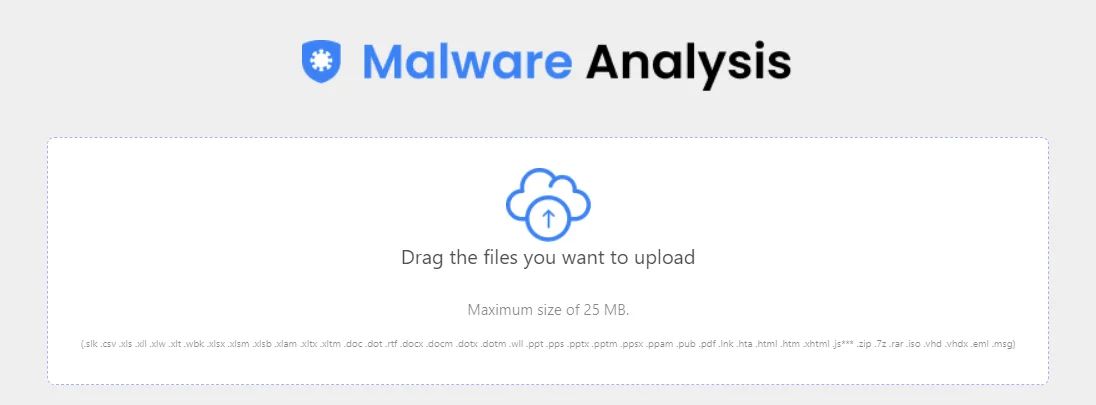
SOCRadar Malware Analysis may also investigate EML files for malicious attachments and URLs.
Regularly Update and Patch Systems: Scattered Spider, like many cybercriminal groups, often exploits known vulnerabilities in software. Keeping all systems updated with the latest patches is a critical defense strategy to close any security gaps that could be exploited.
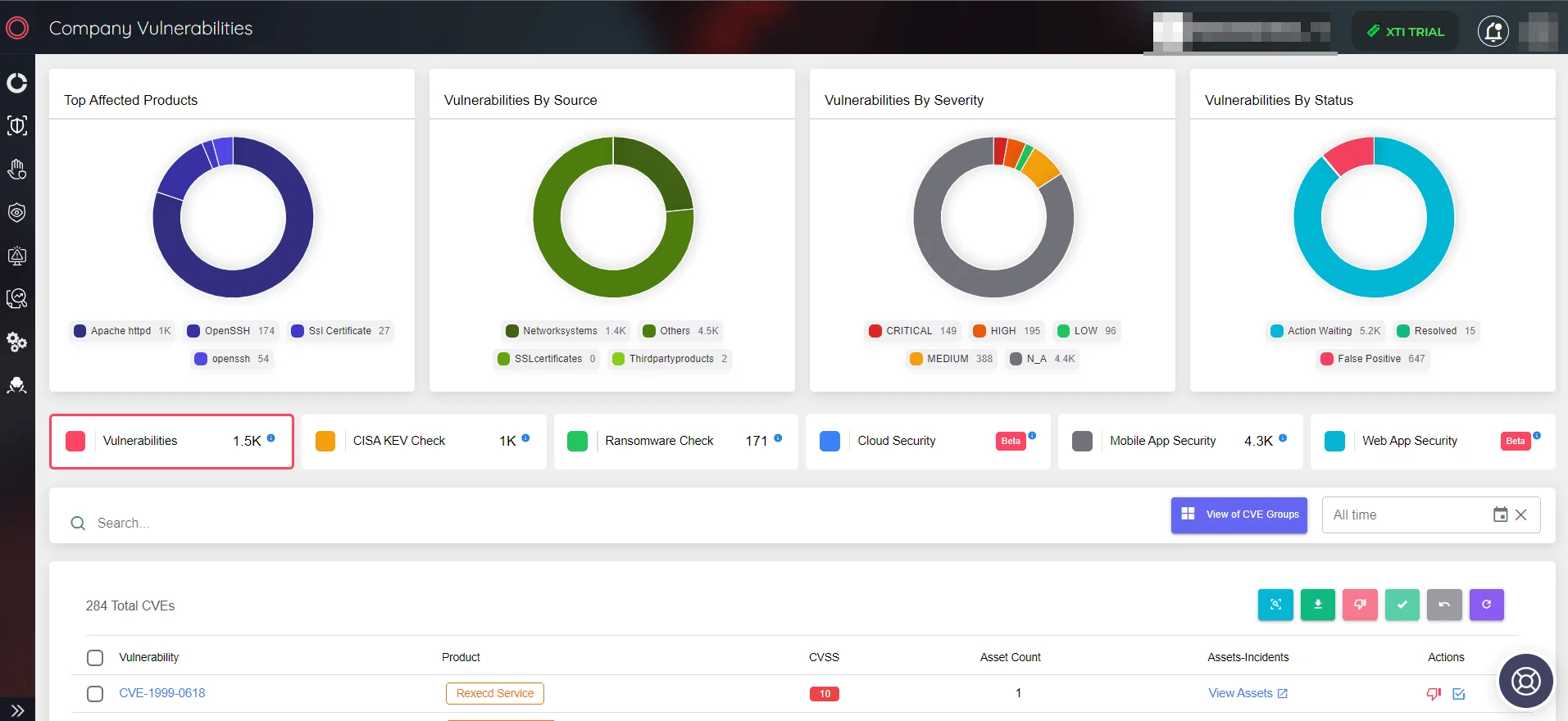
Using SOCRadar XTI’s Company Vulnerability panel, organizations can be informed about their assets’ vulnerabilities and risks.
Monitor for Suspicious Activity: Continuous monitoring of network and system activities can help in early detection of any signs of a breach or attempted intrusion. This includes monitoring login attempts, especially for critical systems, and setting up alerts for any unusual activities.
Develop and Test Incident Response Plans: Having a well-developed incident response plan is crucial. Regular testing and updating of this plan ensure that the organization is prepared to respond effectively in the event of a breach.
By implementing these specific security measures, organizations can significantly enhance their resilience against the sophisticated tactics employed by Scattered Spider. Vigilance and proactive defense are key in mitigating the risks posed by this and other cybercriminal entities.
MITRE ATT&CK TTPs of Scattered Spider
TTP Table, as shared by CISA:
| Tactic | Technique | Procedure |
| Reconnaissance | Gather Victim Identity Information | Threat actors gather usernames, passwords, and PII for targeted organizations. |
| Phishing for Information | Threat actors use phishing to obtain login credentials, gaining access to a victim’s network. | |
| Resource Development | Acquire Infrastructure: Domains | Threat actors create domains for use in phishing and smishing attempts against targeted organizations. |
| Establish Accounts: Social Media Accounts | Threat actors create fake social media profiles to backstop newly created user accounts in a targeted organization. | |
| Initial Access | Phishing | Threat actors use broad phishing attempts against a target to obtain information used to gain initial access. Threat actors have posed as helpdesk personnel to direct employees to install commercial remote access tools. |
| Phishing (Mobile) | Threat actors send SMS messages, known as smishing, when targeting a victim. | |
| Phishing: Spearphishing Voice | Threat actors use voice communications to convince IT help desk personnel to reset passwords and/or MFA tokens. | |
| Trusted Relationship | Threat actors abuse trusted relationships of contracted IT help desks to gain access to targeted organizations. | |
| Valid Accounts: Domain Accounts | Threat actors obtain access to valid domain accounts to gain initial access to a targeted organization. | |
| Execution | Serverless Execution | Threat actors use ETL tools to collect data in cloud environments. |
| User Execution | Threat actors impersonating helpdesk personnel direct employees to run commercial remote access tools, enabling access to the victim’s network. | |
| Persistence | Persistence | Threat actors seek to maintain persistence on a targeted organization’s network. |
| Create Account | Threat actors create new user identities in the targeted organization. | |
| Modify Authentication Process: Multi-Factor Authentication | Threat actors may modify MFA tokens to gain access to a victim’s network. | |
| Valid Accounts | Threat actors abuse and control valid accounts to maintain network access even when passwords are changed. | |
| Privilege Escalation | Privilege Escalation | Threat actors escalate account privileges when on a targeted organization’s network. |
| Domain Policy Modification: Domain Trust Modification | Threat actors add a federated identity provider to the victim’s SSO tenant and activate automatic account linking. | |
| Defense Evasion | Modify Cloud Compute Infrastructure: Create Cloud Instance | Threat actors will create cloud instances for use during lateral movement and data collection. |
| Impersonation | Threat actors pose as company IT and/or helpdesk staff to gain access to victim’s networks. They also use social engineering to convince IT help desk personnel to reset passwords and/or MFA tokens. | |
| Credential Access | Credential Access | Threat actors use tools, such as Raccoon Stealer, to obtain login credentials. |
| Forge Web Credentials | Threat actors may forge MFA tokens to gain access to a victim’s network. | |
| Multi-Factor Authentication Request Generation | Threat actors send repeated MFA notification prompts to lead employees to accept the prompt and gain access to the target network. | |
| Unsecured Credentials: Credentials in Files | Threat actors search for insecurely stored credentials on victim’s systems. | |
| Unsecured Credentials: Private Keys | Threat actors search for insecurely stored private keys on victim’s systems. | |
| Discovery | Discovery | Upon gaining access to a targeted network, the threat actors seek out SharePoint sites, credential storage documentation, VMware vCenter, infrastructure backups, and enumerate AD to identify useful information to support further operations. |
| Browser Information Discovery | Threat actors use tools (e.g., Raccoon Stealer) to obtain browser histories. | |
| Cloud Service Dashboard | Threat actors leverage AWS Systems Manager Inventory to discover targets for lateral movement. | |
| File and Directory Discovery | Threat actors search a compromised network to discover files and directories for further information or exploitation. | |
| Remote System Discovery | Threat actors search for infrastructure, such as remote systems, to exploit. | |
| Steal Web Session Cookie | Threat actors use tools, such as Raccoon Stealer, to obtain browser cookies. | |
| Lateral Movement | Lateral Movement | Threat actors laterally move across a target network upon gaining access and establishing persistence. |
| Remote Services: Cloud Services | Threat actors use pre-existing cloud instances for lateral movement and data collection. | |
| Collection | Data from Information Repositories: Code Repositories | Threat actors search code repositories for data collection and exfiltration. |
| Data from Information Repositories: SharePoint | Threat actors search SharePoint repositories for information. | |
| Data Staged | Threat actors stage data from multiple data sources into a centralized database before exfiltration. | |
| Email Collection | Threat actors search victim’s emails to determine if the victim has detected the intrusion and initiated any security response. | |
| Data from Cloud Storage | Threat actors search data in cloud storage for collection and exfiltration. | |
| Command and Control | Remote Access Software | Impersonating helpdesk personnel, Threat actors direct employees to run commercial remote access tools, thereby enabling access to and command and control of the victim’s network. They also leverage third-party software to facilitate lateral movement and maintain persistence on a target organization’s network. |
| Exfiltration | Exfiltration | Threat actors exfiltrate data from a target network for data extortion. |
| Impact | Data Encrypted for Impact | Threat actors recently began encrypting data on a target network and demanding a ransom for decryption. They have also been observed encrypting VMware ESXi servers. |
| Exfiltration Over Web Service: Exfiltration to Cloud Storage | Threat actors exfiltrate data to multiple sites, including U.S.-based data centers and MEGA[.]NZ. | |
| Financial Theft | Threat actors monetize access to victim networks in numerous ways, including extortion-enabled ransomware and data theft. |