SIM Swappers Collaborate with Ransomware Gangs
In today’s digital world, the landscape of cyber threats is changing rapidly. One of the latest developments in this arena is the alliance between SIM swappers — individuals known for manipulating telecommunications to hijack phone numbers — and sophisticated ransomware gangs.
This partnership marks a concerning evolution in cyber threats that organizations need to understand and prepare for. This disclosure initially brought to light by Joseph Cox, a hacking and crime journalist from 404 Media, has shaken industries across the spectrum.
A Convergence of Skills
In a new turn within the cybercrime underworld, sources have revealed that English-speaking members of “the Comm,” a diverse group known for SIM swapping and physical violence, have allied with the Russian ransomware group, ALPHV/BlackCat. This collaboration has expanded the threat to various industries, with ALPHV/BlackCat being linked to the recent hack of MGM casinos.
The researcher points out the similarity between the Comm and Octo Tempest. A prime example of the impact of this dangerous alliance is the recent attack on MGM Resorts. The attackers, identified as Scattered Spider (also known as Octo Tempest) and affiliated with the ransomware group ALPHV, used a combination of impersonation, social engineering, and legitimate remote management tools to breach the company’s systems.
The aftermath was chaotic, with significant portions of MGM’s internal networks shutting down, affecting operations across more than 30 hotels and casinos globally.
For more details regarding the MGM resort case and Scattered Spider, please refer to the article: “MGM Resorts Hacked by BlackCat Affiliate, ‘Scattered Spider”
Who is the Comm?
According to Joseph Cox, the Comm refers to a loosely organized network of individuals involved in various forms of cybercrime and underground activities. It’s not a formal organization or group with a clear hierarchy but rather a term used to describe a community or network of people who engage in illegal online activities.
Members of the Comm can include hackers, SIM swappers, gamers, and others who are involved in cybercrime. They often communicate and collaborate on platforms like Telegram channels and Discord servers, where they may share information, tools, and techniques related to their illicit activities.

The Comm is known for its diversity, with participants from different backgrounds and skill sets. While some members may focus on cyberattacks, others might engage in physical violence or other criminal activities. The Comm is not a single entity but rather a loose collection of individuals and groups who share a common interest in illicit online activities.
SOCRadar: Strengthening Cybersecurity Defenses Against Social Engineering Threats
In the face of increasing SIM swapping attacks, it is crucial to prioritize security measures that go beyond SMS-based two-factor authentication (2FA). SIM swapping vulnerabilities underscore the necessity of adopting alternative 2FA methods. These methods, such as authenticator apps, hardware tokens, and biometric authentication, offer a robust defense against the growing threat of SIM swapping, enhancing the overall security of accounts and sensitive information.
SOCRadar is a comprehensive cybersecurity solution that can help organizations protect themselves against various cyber threats, including social engineering attacks. Here’s how SOCRadar can assist in defending against these threats:
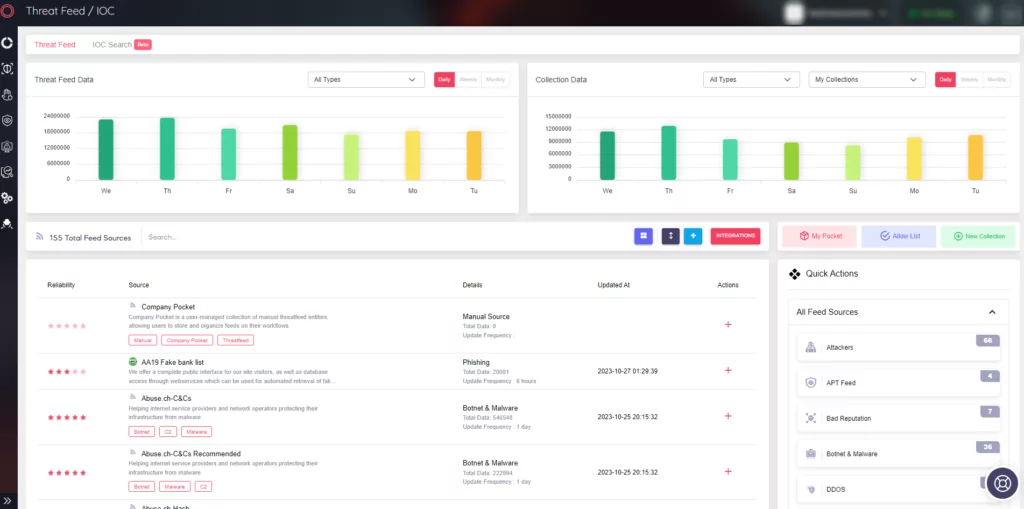
Comprehensive Threat Intelligence: SOCRadar’s Cyber Threat Intelligence module provides access to an extensive network of threat intelligence sources. This allows organizations to obtain up-to-date and comprehensive information about social engineering attacks and understand the context of these threats. By staying informed about the latest attack trends, threat actors, and attack vectors, organizations can strengthen their defense strategies and mitigate risks effectively.
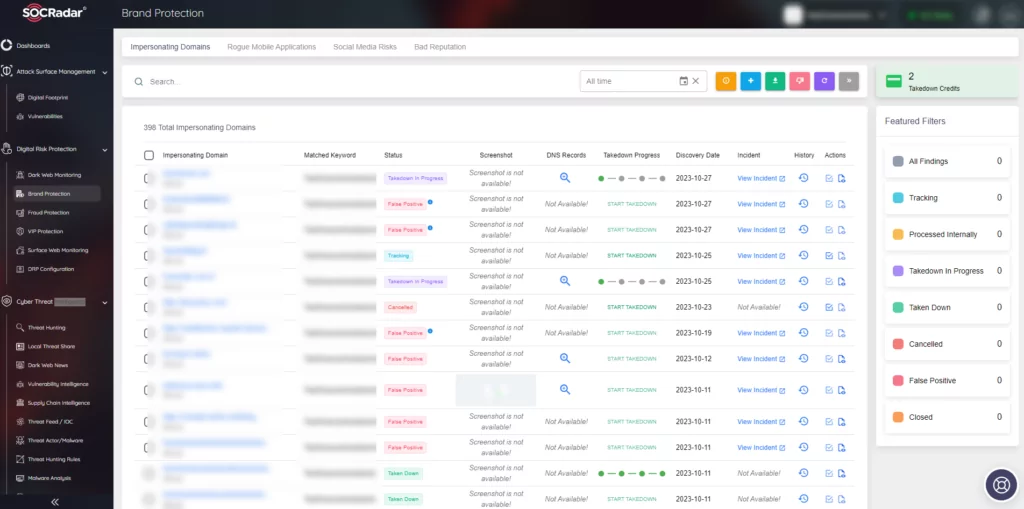
Domain Monitoring and Protection: The Digital Risk Protection module of SOCRadar allows organizations to quickly identify potential malicious domains targeting their brand. This is particularly crucial for defending against phishing attacks, which often use fake domains to impersonate legitimate organizations. SOCRadar enables organizations to monitor changes in domains and take prompt action to take down phishing and brand abuse domains, minimizing harm to their brand reputation.
Real-time Social Media Threat Detection: SOCRadar’s Digital Risk Protection module focuses on detecting and analyzing threats on social media platforms in real-time. This solution helps companies and institutions quickly identify social media threats that could harm their reputation and increase cybersecurity risks. Using machine learning and artificial intelligence technologies, SOCRadar automatically scans social media content, analyzes critical data, and generates alerts and reports about meaningful threats.
Monitoring Company Assets in Dark Web Environments: SOCRadar’s platform also tracks company assets in dark web environments. It generates real-time alerts and provides insights into potential threats and evolving social engineering attack vectors that target sensitive company information. This proactive monitoring allows organizations to identify threats early and take preventative measures.
In summary, SOCRadar provides valuable tools and capabilities to help organizations defend against social engineering attacks. It offers threat intelligence, domain monitoring, real-time social media threat detection, and dark web asset monitoring to enhance an organization’s cybersecurity posture. By leveraging SOCRadar’s capabilities, organizations can stay ahead of cybercriminals and protect their assets and reputation effectively.