Ever-Changing Tactics on Social Engineering
In today’s digital age, cyber threats are becoming increasingly common, and one of the most prevalent types of attacks is phishing. Phishing involves tricking people into giving away their personal or confidential information by posing as trustworthy entities, such as banks or email providers. On the other hand, “vishing” is a form of phishing that relies on voice communication, typically over the phone. Vishing attackers may pose as legitimate businesses or organizations attempting to extract sensitive information from unsuspecting victims.
To make matters worse, threat actors constantly evolve their tactics to stay one step ahead of security measures. They may use social engineering techniques to manipulate victims, impersonate trusted sources, or even use AI-generated voices to make their attacks more convincing. One of the rising attack trends of last year, callback phishing, was one of the best examples of this constant change.
New Tactics, Old Vulnerabilities
Cybersecurity researchers continue to observe new phishing tactics every day, and companies with a large attack surface and many users, such as Microsoft, are the most targeted systems.
A new phishing scam has been discovered that tricks users into giving away their Microsoft login information. The phishing campaign starts with an email that appears legitimate, with a vague message and an attachment related to EFT payments. Once the user opens the HTML attachment, they are redirected to a fake Microsoft login page designed to look authentic with official Microsoft logos and design elements. After entering their credentials, the user is then redirected to an unrelated Google Drive voice recording about catering prices, which is intended to create confusion and make the user question the legitimacy of the interaction.
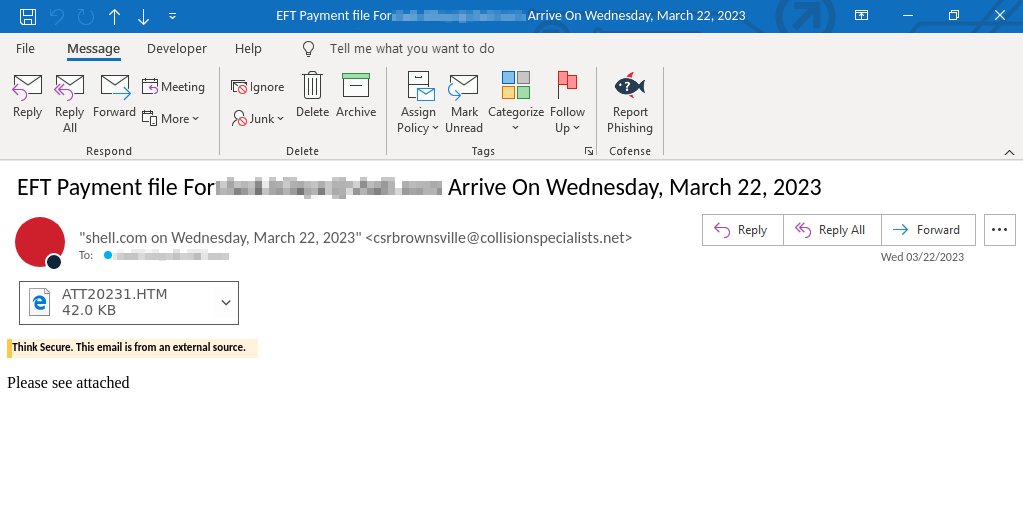
This phishing campaign highlights the importance of remaining vigilant when dealing with emails requesting sensitive information. Users should always verify the authenticity of emails and websites and never provide personal or financial information without knowing the recipient’s legitimacy. By staying informed and practicing good cyber hygiene, such as using strong passwords and MFA solutions, avoiding suspicious links and attachments, and keeping software up to date, we can help protect ourselves and our digital identities from these evolving threats.
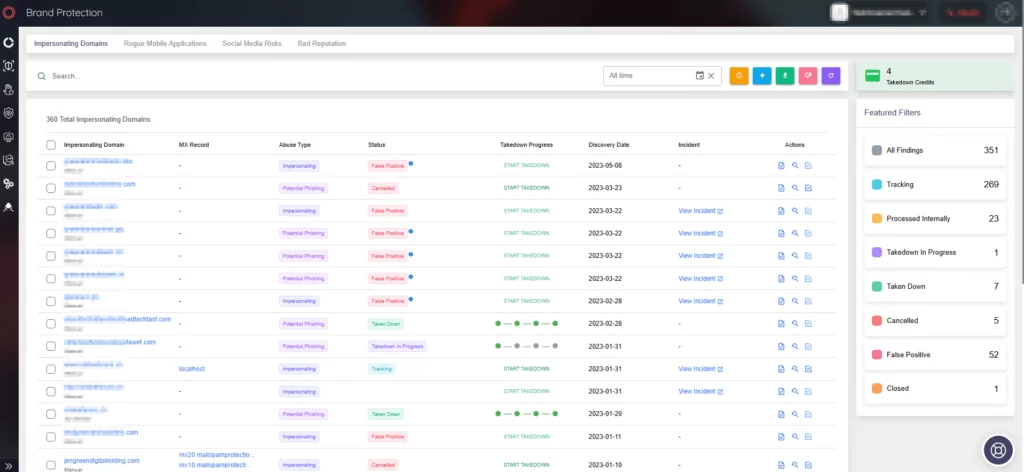
How Can SOCRadar Help?
Our Digital Risk Protection module, which utilizes artificial intelligence, scans millions of domains from various major domain registrars to identify any potentially harmful domains that may be aimed at your brand or entire business network.
When any suspicious changes occur on these domains, alerts are triggered. Through the use of machine learning algorithms, SOCRadar can examine a vast amount of domain data to identify lookalike domains. Additionally, “real-time notifications” will alert you to upcoming expiration dates for your domains and SSL/TLS certificates, helping you maintain a secure digital presence.