

Security Breach in Okta Support System Continues Sparking Concerns: Cloudflare and 1Password Share Disclosures
[Update] November 29, 2023: A recent audit uncovered a broader data theft scope in the October breach. Read more under the subheading: “Okta Security Breach Revealed to Impact All Support System Users: Warning for Administrators.”
On October 20, 2023, Okta Security detected malicious activity that exploited a stolen credential, allowing unauthorized access to the company’s support case management system. Several other vendors, also affected by the incident, have since shared their own disclosures. Overall, the incident has ignited substantial concerns over its capacity to trigger a supply chain compromise.
A threat actor successfully gained access to files uploaded by certain customers through recent Okta support cases, according to the company.
Interestingly, Okta has chosen not to disclose critical details such as the extent of the attack, the specific timeline of the incident, or when they first detected the unauthorized access. These details continue to remain undisclosed, leaving the cybersecurity community with critical questions.
What Led to the Breach? Exploring Okta Support’s Use of HAR Files
As part of their standard business procedures, Okta support may request customers to upload HTTP Archive (HAR) files. These files aid in troubleshooting errors by replicating browser activity.
Nevertheless, HAR files may contain sensitive information, including cookies and session tokens. If obtained by threat actors, such data could be leveraged for impersonating legitimate users, underscoring the inherent risks associated with such data exposure.
Upon uncovering the security incident, Okta acted swiftly to notify impacted customers and instituted protective measures to ensure their security, including the revocation of embedded session tokens. Okta recommends all users to enhance security by sanitizing HAR files, removing any credentials, cookies, or session tokens before sharing them.
Have Other Systems Besides Okta Support Case Management Been Affected by the Breach?
It is essential to clarify that Okta’s support case management system operates separately. Consequently, both the Okta service and the Auth0/CIC case management system remain unaffected by this incident.
Disclosures of 1Password, Cloudflare, and BeyondTrust Regarding the Okta Support Breach
1Password disclosed yesterday that they detected suspicious activity on their Okta instance on September 29. The company uses Okta to manage their employee-facing apps and confirms the intrusion is related to the newly disclosed Support System incident.
After a thorough investigation, they concluded that no 1Password user data was accessed, and no sensitive systems were compromised.
1Password worked with Okta since the initial identification of the suspicious activity to determine the initial compromise vector, confirming its relation to the support system breach after Okta’s disclosure.
BeyondTrust notified Okta about the activity on October 2, 2023, as they too were affected. However, the threat actor retained access to Okta’s support systems until at least October 18, 2023. The breach was confirmed on October 19, followed by its disclosure on October 20.
Cloudflare also disclosed that they were affected by the Okta support breach, tracing threat actors leveraging an authentication token compromised at Okta to access Cloudflare’s Okta instance. They responded promptly and contained the risk, with no impact on Cloudflare customer information or systems.
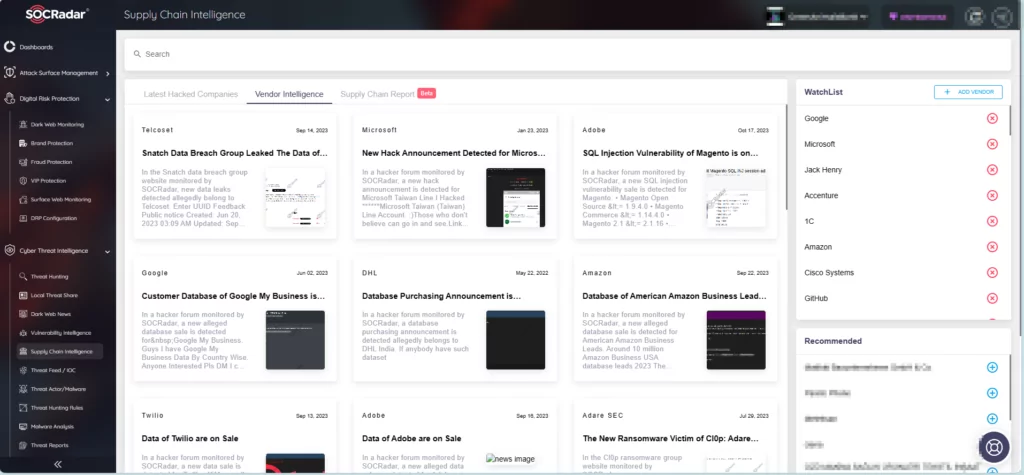
Proactive Supply Chain Monitoring with SOCRadar
The involvement of well-known companies in this breach raises concerns about its potential for a significant supply chain issue had it not been promptly mitigated by these vendors.
To remain vigilant and protect your organization against supply chain issues, you can utilize SOCRadar’s Supply Chain Intelligence module. It allows you to monitor the latest breaches, add vendors to a WatchList for a specialized incident feed, and stay informed about upcoming incidents for timely mitigation.
Okta Security Breach Revealed to Impact All Support System Users: Warning for Administrators
Contrary to Okta’s initial assessment, a recent audit revealed a more extensive scope of data theft resulting from the security breach in October.
Okta revised its findings, acknowledging that more users, including some Okta employees, were affected. The threat actors had pilfered a customer report with data of all users utilizing the Okta Customer Support System. The stolen customer report included user names, company names, and mobile phone numbers; however, most fields were blank, without credentials or sensitive personal data. For over 99% of the listed customers, the compromised information was limited to full names and email addresses.
The company had initially reported that merely 1% (approximately 184 clients) of its customer base had experienced an impact. However, it has now become apparent that the extent of the impact is considerably larger than initially acknowledged.
The impact of the security breach extends to all Okta Workforce Identity Cloud (WIC) and Customer Identity Solution (CIS) customers, except those in the FedRamp High and DoD IL4 environments. These exempt environments use a different support system that the threat actor could not access. Also, the Auth0/CIC support case management system remained unaffected by the incident.
Although there is no direct evidence of active exploitation of the stolen information, Okta emphasized the heightened risk of phishing and social engineering attacks. To strengthen defenses, Okta strongly advises customers to use robust Multi-Factor Authentication (MFA), recognizing the potential misuse of the downloaded data.
Okta especially highlighted the increased vulnerability of Okta administrators, who represent many of the users in the Okta Customer Support System. The company says it is critical that these users implement MFA, to protect not only the support system but also secure access to Okta admin consoles.
Engaging a digital forensics firm to support the ongoing investigation, Okta committed to sharing the comprehensive report with customers upon its completion. Further information and recommended actions in response to the breach are available on Okta’s official website.
Indicators of Compromise (IoCs)
Okta has provided the Indicators of Compromise (IoCs) to help customers identify potential malicious activity.
The company also advises checking their recommendations on how to search the System Log for any signs of suspicious sessions, users, or IPs.
Ip Addresses:
- 23.105.182.19
- 104.251.211.122
- 202.59.10.100
- 162.210.194.35 (BROWSEC VPN)
- 198.16.66.124 (BROWSEC VPN)
- 198.16.66.156 (BROWSEC VPN)
- 198.16.70.28 (BROWSEC VPN)
- 198.16.74.203 (BROWSEC VPN)
- 198.16.74.204 (BROWSEC VPN)
- 198.16.74.205 (BROWSEC VPN)
- 198.98.49.203 (BROWSEC VPN)
- 2.56.164.52 (NEXUS PROXY)
- 207.244.71.82 (BROWSEC VPN)
- 207.244.71.84 (BROWSEC VPN)
- 207.244.89.161 (BROWSEC VPN)
- 207.244.89.162 (BROWSEC VPN)
- 23.106.249.52 (BROWSEC VPN)
- 23.106.56.11 (BROWSEC VPN)
- 23.106.56.21 (BROWSEC VPN)
- 23.106.56.36 (BROWSEC VPN)
- 23.106.56.37 (BROWSEC VPN)
- 23.106.56.38 (BROWSEC VPN)
- 23.106.56.54 (BROWSEC VPN)
User-Agents:
Okta points out that although the listed user-agents are legitimate, they might be uncommon in your environment, primarily due to the release of Chrome 99 in March 2022.
- Mozilla/5.0 (Windows NT 10.0) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.7113.93 Safari/537.36 (Legitimate, but older user-agent)
- Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/99.0.4844.83 Safari/537.36 (Legitimate, but older user-agent)










