
SOCRadar’s First Year-End Report: What Happened on the Deep Web in 2021?
In 2021, we saw that deep web monitoring and cybersecurity are essential to large corporations, governments, and ordinary people. While the Log4j vulnerability allowed threat actors to attack all java-based web servers, resounding attacks such as the Colonial Pipeline ransomware attack showed that there could be problems with the supply of essential products we need most in daily life, such as gasoline.
Another large-scale attack was the SolarWinds attack. Threat actors in the US and other countries are estimated to have caused around $20 billion in total damage. The attacks that occurred in 2021 allowed 2022 to start with operations. Russia’s Federal Security Service raided 25 sites allegedly associated with threat actors and arrested 14 members of the REvil gang.
Read our full report to find out what you can do to secure all your digital assets and potential vulnerabilities.
13,000 Dark Web Posts Inspected
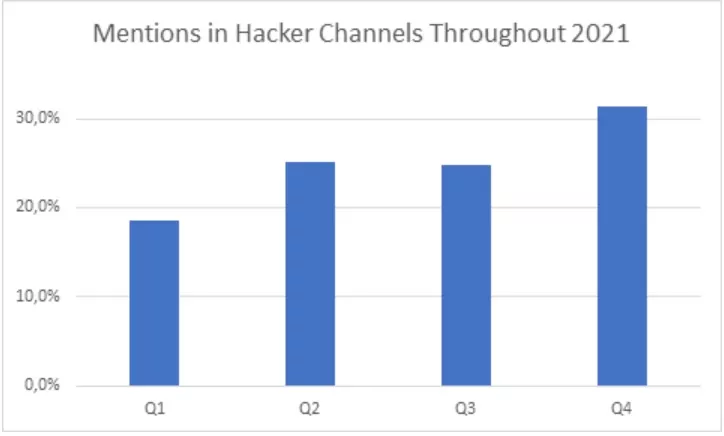
The SOCRadar Research Team analyzed over 13,000 posts on darknet and deep web forums and networks like Discord and Telegram. It found that the activity of threat actors increased excessively in the last quarter of 2021.
As can be seen in the chart below, while 19% of the activities took place in the first quarter, it reached 32% in the last quarter.
While the most targeted sectors on a global basis were Information Technologies, Government, E-commerce, and Banking, the other sectors were:
- Media & Entertainment
- Cyber Security
- Cryptocurrency
- Education
- Healthcare
USA: Most Targeted Country in 2021
Here are the countries most mentioned in dark web posts and hacker channels that revealed in SOCRadar’s deep scans:
- United States
- United Kingdom
- India
- Russian Federation
- France
- Germany
- Canada
- Brazil
- China
- Italy
The forums and channels monitored, showed that threat actors have different trends by region. For example, in North and South America, the threats were predominantly ransomware, while differences were detected in other regions.
While data share, data sale, and ransomware go hand in hand in Europe, data sale and data share constitute half of the total threats in APAC countries. In MEA countries, the data sale trend is higher.
IT and E-commerce Sectors Most Targeted by Phishing Attacks
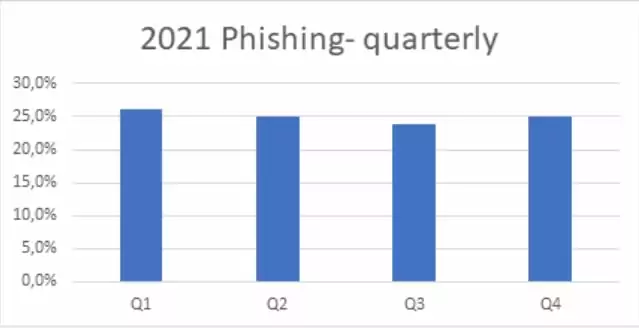
Phishing was also one of the most common methods threat actors used in 2021. SOCRadar has detected around 700,000 phishing attempts worldwide. The trend of these attacks, which aim to infiltrate companies’ networks by stealing people’s identity information, remained the same throughout the year.
Top 10 countries most targeted by phishing attacks:
- United States
- Turkey
- Russia
- Germany
- Canada
- Netherlands
- Singapore
- United Kingdom
- France
- Hong Kong
The threat actors’ most used domains in the attacks had extensions such as .com, .org, .net, and .ru, it was found that threat actors preferred domain names with SSL certificates to be credible.
The sectors most targeted by phishing attacks are also in harmony with the most mentioned sectors on the deep/dark web. IT, e-commerce, banking, and government are taking the lead. Other most targeted sectors are the defense industry, telecommunications, and cryptocurrency.
37% of Businesses and Organizations Attacked by Ransomware
With the prevalence of the ransomware-as-a-service (Raas) business model, it has become easier for even people with no technical knowledge to carry out ransomware attacks. The use of double-extortion tactics by threat actors also increased the victimization of companies. Ransomware gangs, not just encrypting data, are now putting pressure on companies by threatening to release data.
Research shows that in 2021, 37% of all businesses and organizations were attacked by ransomware. While 32% of victims pay the ransom, they only get 65% of their data back. The most important reason for this is that they are deprived of an adequate backup system.
SOCRadar’s Extended Threat Intelligence solution offers the holistic understanding you need to stay one step ahead of global cyberattack threats. SOCRadar prepared a global deep web report for the first time by addressing the issues on the agenda throughout the year with the data compiled from the platform.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free



































