
SOCRadar Azerbaijan Threat Landscape Report: A Significant Target for Threat Actors
Companies in Azerbaijan are developing their technological infrastructure. This makes them ideal targets for threat actors. The SOCRadar Threat Landscape Report provides an in-depth understanding of cyber incidents occurring or likely to occur in the country in 2021.
Download our full Azerbaijan Threat Landscape Report.
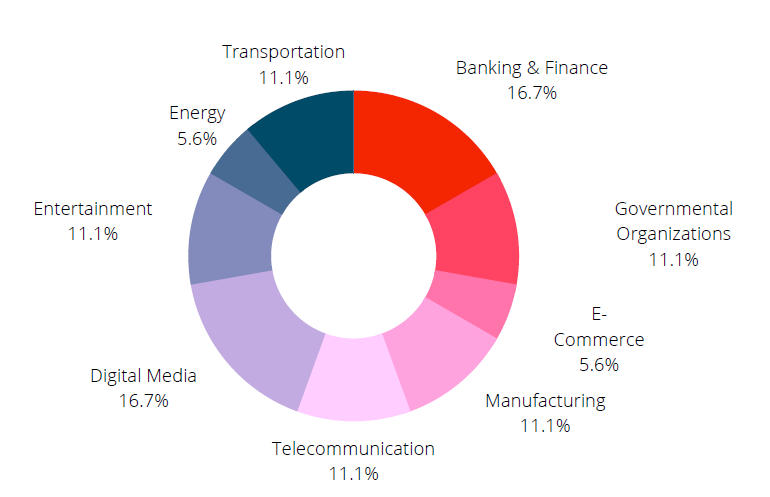
SOCRadar Dark Mirror shows that threat actors mainly targeted Azerbaijan’s banking & finance, digital media, governmental organizations, and manufacturing sectors in 2021. 14 different threat actors targeting valuable assets shared about the sale of database and unauthorized network access.
Ransomware Continues to be a Substantial Threat
It is known that 2021 was a year when ransomware attacks peaked. The top 10 ransomware groups have obtained $5.2 billion worth of bitcoin with their attacks worldwide. The tension between Armenia and Azerbaijan had placed both countries at the target.
Click here to read our Azerbaijan Threat Landscape Report
Ransomware hit the banking, finance, and transportation sectors the most in Azerbaijan. By exploiting known security vulnerabilities, they attacked these crucial verticals.
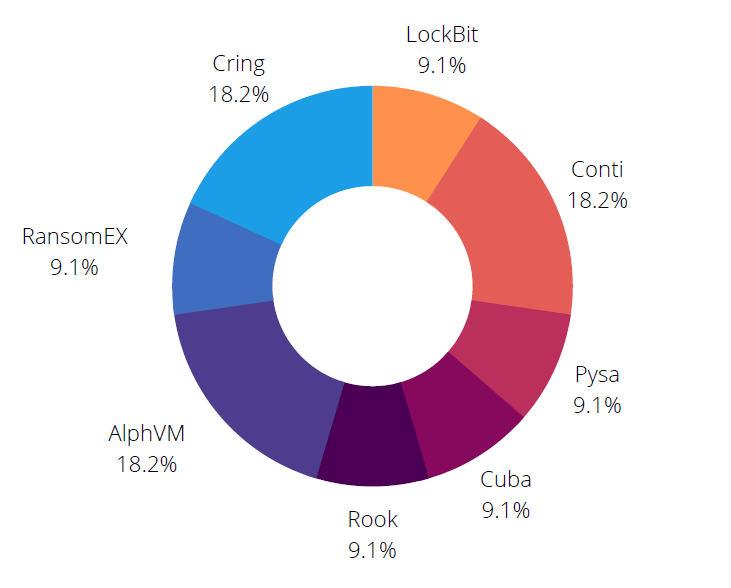
The ransomware gangs that target Azerbaijan the most are:
- Cring
- AlphaVM
- Conti
- LockBit
- Pysa
- Cuba
- RansomEX
- Rook
Who Are the Three Ransomware Gangs Most Targeting Azerbaijan?
Cring
The group, which started its operations in 2019, carries out its attacks using tools such as Mimikatz and uses Cobalt Strike to distribute BAT files.
AlphaVM
AlphVM is also known as BlackCat. It is also considered a rebranding of the BlackMatter / DarkSide group. It is notable for being the first ransomware to use the Rust programming language.
Conti
The gang has been in the headlines for a while, with the Russia – Ukraine war and leaking of their correspondence. Operating as a ransomware-as-a-service (RaaS), the group has carried out many high-profile attacks in Azerbaijan.
Other Threats and Key Findings
- Organizations in Azerbaijan continued to be targeted by advanced persistent threat actors. In particular, APT groups in China and Iran have targeted military, government, technology, and finance verticals.
- The most important vector of ransomware attacks has been phishing emails. The most common tactic was to transmit the malware through the Office document.
- The most exploited vulnerabilities were CVE-2021-26855, CVE-2019-0708, and CVE-2021-13379, with a CVSS score of 9.8.
This report has been prepared with Prosol, SOCRadar’s valuable solution partner in Azerbaijan.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Try for free



































