Top 10 Stealer Logs
This article has been updated as of July 2025 to reflect recent stealer log activity and trends.
Stealer logs represent a growing cybersecurity threat, capturing sensitive data like passwords, credit card numbers, and cryptocurrency wallets from infected devices. These logs are typically generated by infostealer malware and then traded or sold on dark web forums, often fueling large-scale breaches, fraud, and ransomware operations.
Recent threat intelligence highlights just how impactful these logs have become. Verizon’s 2025 DBIR revealed that over half of ransomware victims had domains listed in stealer logs prior to being attacked. (Curious about the mechanics behind credential theft? Here’s SOCRadar’s full guide on stealer logs.)
Moreover, in 2024, the most advertised stealer tools on the dark web included Lumma, RisePro, Vidar, Stealc, and RedLine – names now linked to billions of compromised records.
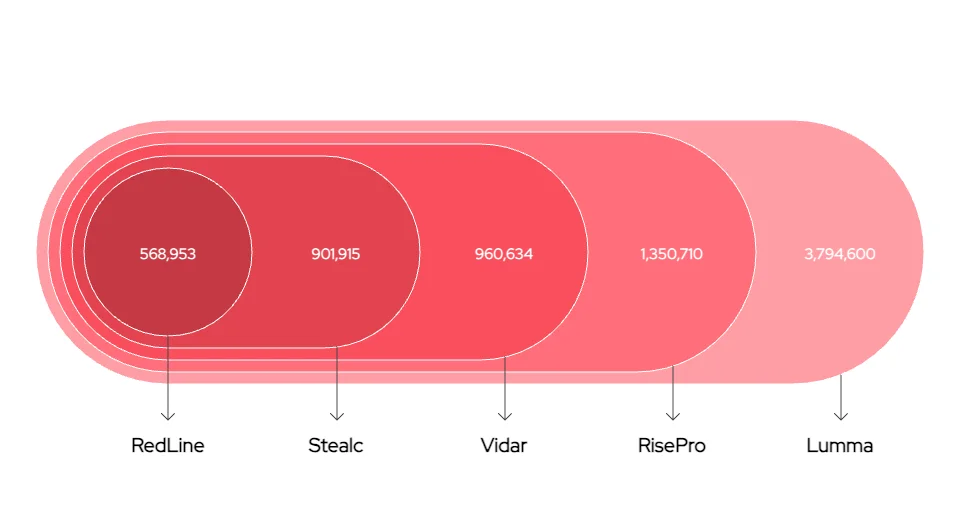
Top five infostealers seen on dark web forums in 2024, by incidence (Statistics by IBM X-Force)
To better understand this threat landscape, SOCRadar continuously analyzes millions of stealer log entries, helping organizations uncover risks, monitor exposure, and trace potential breaches with thorough threat hunting.
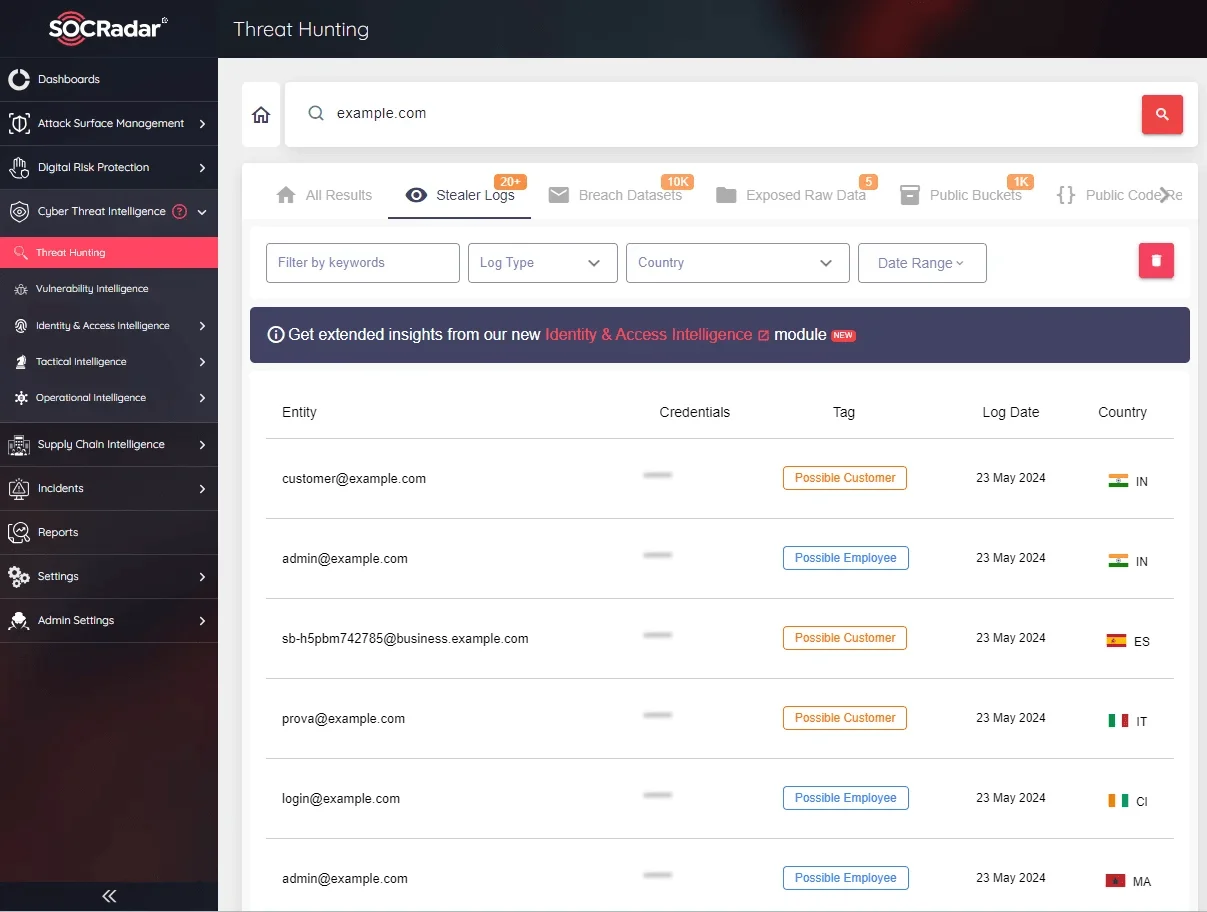
SOCRadar’s Threat Hunting allows you to search within stealer logs
This article presents the top stealer logs based on our analysis, offering insights into the most active and damaging tools of the year.
1. Lumma / LummaC2
According to IBM X-Force’s 2025 report, Lumma was the most dominant infostealer advertised on dark web forums throughout 2024, leading a list that includes RisePro, Vidar, Stealc, and RedLine. Its sustained presence, technical sophistication, and broad deployment helped solidify its place at the top of recent stealer log activity.
LummaC2 is a commercially distributed stealer that operates under an affiliate model, allowing cybercriminals to license it for their own campaigns. It targets operating systems from Windows 7 to Windows 11, and supports major browsers such as Chrome, Firefox, and Edge.
Once deployed on a victim’s device, it collects detailed system information (including OS version, CPU data, and browser history) while targeting credentials, credit card information, crypto wallets, and other sensitive data. This data theft can lead to severe privacy breaches, financial losses, and identity theft.
Static analysis of LummaC2 reveals its file structure, programming language, and embedded anti-debugging techniques. Once active, the malware communicates with a Command and Control (C2) server, exfiltrating stolen data in a compressed ZIP format. Dynamic analysis further shows how it bypasses debugging environments and transmits the data to its assigned C2 endpoint.
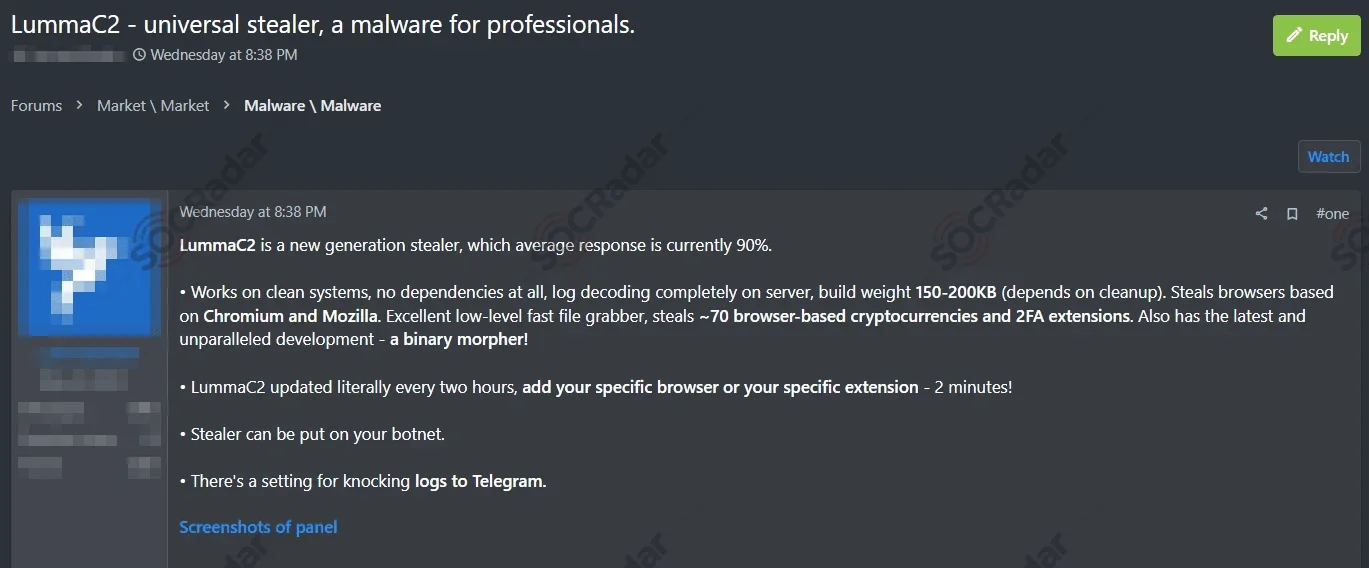
A LummaC2 sale post from 2023, advertising an upgraded version (SOCRadar Dark Web News)
LummaC2’s recent updates include anti-sandboxing (including trigonometry-based checks), Google cookie revival capabilities, and integration with Discord CDN and API for distribution. These advancements make it more evasive and harder to dismantle
LummaC2 Infrastructure Disruption in 2025
In May 2025, the U.S. Department of Justice, in partnership with Microsoft, led a significant disruption operation against LummaC2’s infrastructure. Authorities seized multiple login and administration domains used by Lumma affiliates, aiming to sever the malware’s backend control and disable its service model entirely. Microsoft took down over 2,300 associated public-facing domains, dealing a coordinated blow to the LummaC2 syndicate.
The FBI estimates LummaC2 was tied to at least 1.7 million fraud cases, ranging from banking theft to crypto wallet compromises.
2. RisePro
RisePro has quickly climbed the ranks to become one of the most widely observed infostealers of 2024. It was the second most advertised stealer on dark web forums, just behind Lumma, driven by a surge in infections, targeted campaigns, and growing presence in stealer log marketplaces.
First detected in late 2022 and written in C++, RisePro is designed to steal login credentials, credit card data, browser cookies, and cryptocurrency wallets. It also collects system information such as OS details and installed software, making it valuable to threat actors engaged in both fraud and network infiltration.
A RisePro stealer malware advertisement post (SOCRadar Dark Web News)
RisePro is often delivered via PrivateLoader, a pay-per-install service, as well as through phishing campaigns and cracked software disguised as keygens or game mods. Once active, the stealer scans the system, exfiltrates data to command-and-control servers or Telegram channels, and compiles the results into structured logs for resale on platforms like Russian Market.
Notably, RisePro saw a massive spike in infections in 2024, rising from just 1.4% of all infostealer activity in 2023 to nearly 23% the following year. Campaigns increasingly targeted developers and IT professionals, including a GitHub-themed campaign known as “gitgub”, which exfiltrated stolen data through Telegram-linked infrastructure.
With obfuscation improvements like bloated installers and encrypted strings, RisePro has also become harder to detect and analyze. Its widespread use and steady updates make it a persistent and growing threat in today’s stealer log landscape.
3. Vidar Stealer
First seen in 2018, Vidar Stealer continues to fuel large volumes of stealer logs, maintaining a strong foothold in dark web marketplaces.
Vidar is written in C++ and offered as Malware-as-a-Service (MaaS). It can extract a wide range of data: browser credentials, cookies, cryptocurrency wallets, cloud service access, FTP client data, and even session tokens from platforms like Steam, Discord, and Telegram. It also profiles infected systems by collecting OS details, IP addresses, and installed applications.
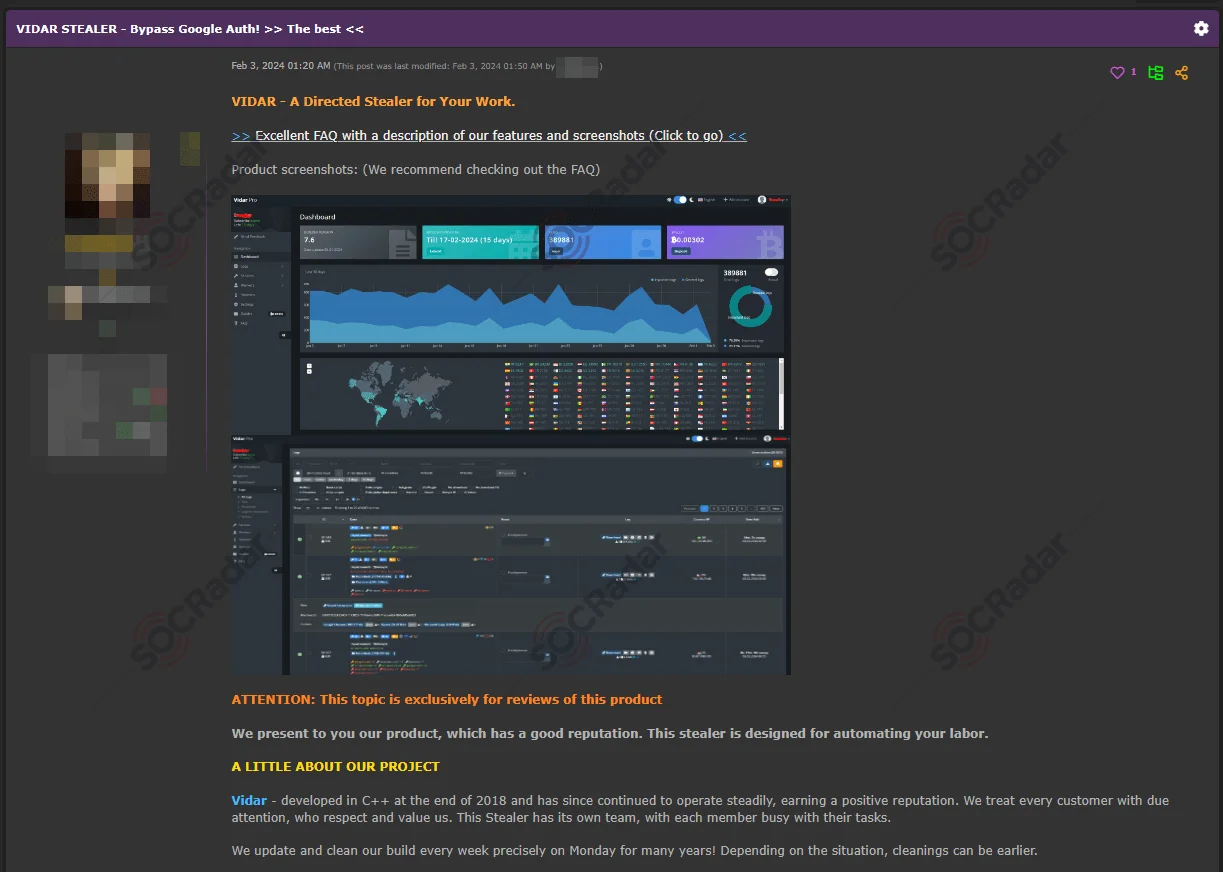
Vidar Stealer advertisement on a Dark Web forum (SOCRadar Dark Web News)
Vidar typically spreads through phishing emails, cracked software, malicious Google Ads, and fake installers. It has even been distributed through Steam games, TikTok ads, and spoofed IT support sites. One 2025 campaign used a fake game called PirateFi to deliver the payload.
Once deployed, Vidar compiles stolen data into structured logs categorized by platform and credential type, making it easier for buyers to carry out credential stuffing, financial fraud, and account takeovers.
Vidar has received notable updates over time, adopting techniques like RC4 encryption and removing self-deletion routines to maintain persistence. These enhancements have made the stealer more resilient and harder to analyze, contributing to its continued presence in active campaigns.
In June 2025, international law enforcement operations reportedly disrupted parts of Vidar’s infrastructure, though the malware remains active. Its logs continue to be widely sold on dark web markets and are tied to a broad spectrum of cybercrime, from personal account theft to corporate credential breaches.
4. StealC
StealC has gained significant traction among cybercriminals for its stealth, flexibility, and modular design. First identified in late 2022, it has since evolved into a full-featured Malware-as-a-Service (MaaS) offering, actively distributed via phishing campaigns, cracked software, and loader malware like Amadey and MintsLoader.

StealC is also disseminated in hacker forums
Written in C, StealC is designed to extract a wide variety of data, including browser credentials, session cookies, crypto wallets, system metadata, and even files from user directories. It supports major browsers like Chrome, Edge, Firefox, and Opera, and can also target messengers, VPNs, email clients, and gaming platforms.
The malware dynamically resolves API calls and uses advanced evasion techniques including heavy obfuscation, RC4 string encryption, and geofencing to avoid CIS countries. It also leverages commercial packers like Themida and typically self-deletes after execution to reduce its footprint.
In March 2025, a major upgrade – StealC v2 – introduced a new JSON-based C2 protocol, a redesigned control panel for payload customization, and support for new delivery methods such as MSI and PowerShell. Features like multi-monitor screenshot capture, file grabbers, and server-side credential brute-forcing have made the stealer even more dangerous.
Once data is exfiltrated, it is compiled into stealer logs that are resold or traded on underground forums. These logs fuel credential stuffing, account takeovers, and a surge in financial fraud.
With rapid updates and a growing market presence, StealC continues to be a leading contributor to stealer log activity in 2025.
5. RedLine
RedLine remains one of the most widely deployed and commercially successful infostealers on the market. First observed in 2020 and written in .NET, it is offered as Malware-as-a-Service (MaaS) at low prices, making it accessible to a wide range of cybercriminals. Additionally, it supports customizable plugins that allow attackers to add new functionalities. Redline is often employed in targeted attacks aimed at specific victims.
The stealer targets a broad spectrum of data via methods like keylogging and form grabbing: login credentials, credit card information, cryptocurrency wallets (including over 40 browser wallet extensions), and session cookies. It also collects detailed system information such as OS version, IP address, installed software, user-agent, and antivirus status.
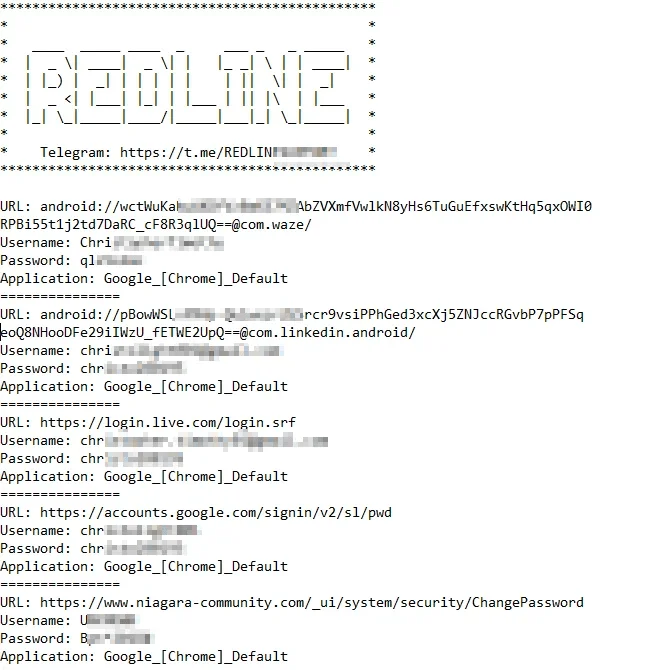
Compromised accounts of a machine through RedLine
RedLine variants have been observed targeting VPN clients (e.g., NordVPN, OpenVPN, ProtonVPN), FTP tools (FileZilla), messengers, email clients, Steam, and Discord. Some builds include remote access features, enabling file transfer and command execution.
In 2025, RedLine was responsible for 44% of all stealer logs found on major dark web and Telegram channels – a clear indication of its scale and market share. These logs are well-organized, highly searchable, and commonly used for credential stuffing, account takeovers, and financial fraud.
Recent variants have introduced Lua bytecode for string obfuscation, improving evasion. RedLine also continues to spread through phishing, cracked software, malicious loaders, and fake ads, often disguised as popular tools like ChatGPT. Campaigns have recently targeted gamers via YouTube and GitHub, as well as impersonated oil and gas companies in Southeast Asia.
RedLine’s blend of low cost, high functionality, and constant updates has kept it a dominant force in the infostealer ecosystem, and a consistent driver behind credential theft and follow-on attacks like ransomware and business email compromise.
6. Raccoon Stealer
Raccoon Stealer has remained a mainstay in the infostealer landscape since its emergence in 2019. Sold as a Malware-as-a-Service (MaaS) offering and written in C++, it’s known for its wide target range, active development, and low entry barrier for cybercriminals. Despite law enforcement takedowns, including the arrest of a key operator in 2022 and a sentencing in late 2024, the malware continues to operate, proving the resilience of its affiliate model.
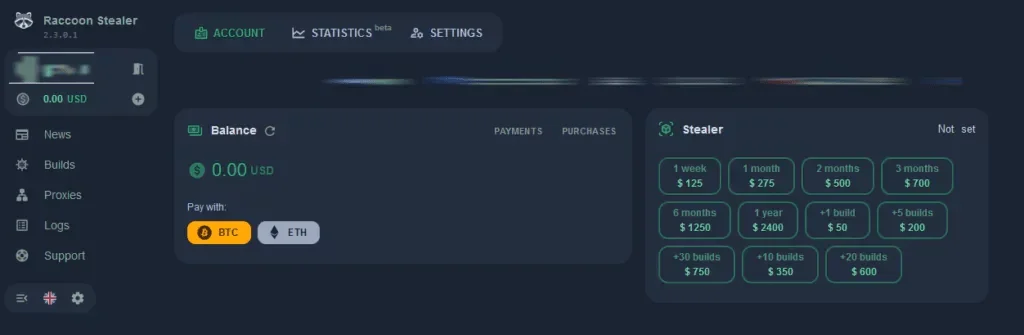
Raccoon Stealer website in 2024
Raccoon targets a wide range of data: credentials, cookies, credit card numbers, crypto wallets (e.g., Exodus, Jaxx, Atomic), and system metadata. It also steals files, screenshots, and app data from password managers (like Bitwarden and 1Password), email clients, and messengers such as Telegram, Signal, and Discord. Some variants include loader capabilities, allowing it to drop and execute secondary payloads such as CryptBot.
Following its infrastructure disruption in 2022, the malware re-emerged as Raccoon Stealer v2, with updated modules for broader application targeting, stronger obfuscation, and new evasion techniques. Current builds employ API hammering, XOR encryption, and configurable components for tailored attacks. One of its hallmarks remains the ability to deliver stolen data in organized ZIP archives (often named log.zip), which are then sold or shared on dark web forums and Telegram channels.
By late 2024, Raccoon Stealer was linked to over 52 million stolen credentials, with logs regularly appearing on marketplaces like Russian Market. Infection vectors include phishing emails, exploit kits, malvertising, and compromised web apps. It often installs itself as a scheduled task or background service to ensure persistence.
Despite international law enforcement efforts, Raccoon’s strong market demand, low pricing, and consistent updates make it a persistent threat. Its logs continue to fuel large-scale credential theft, financial fraud, and secondary infections across industries ranging from software and finance to manufacturing.
7. MetaStealer
MetaStealer (a.k.a. META) is a cross-platform infostealer that has steadily grown in popularity since its emergence in early 2022. Sold as a Malware-as-a-Service (MaaS) offering, it targets both Windows and macOS systems, making it one of the few stealers that consistently goes after Apple users, especially business professionals.
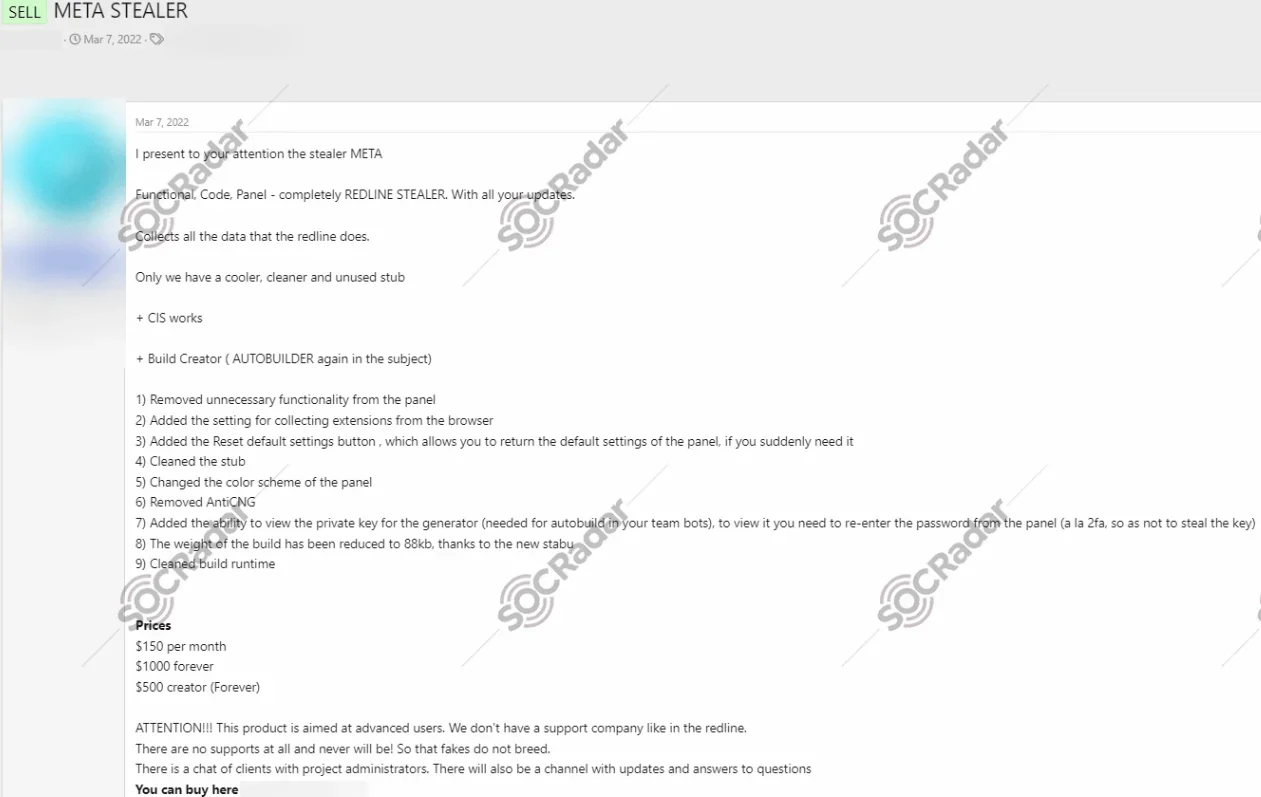
META stealer malware sold in 2022 on a hacker forum
Once installed, MetaStealer extracts credentials, credit card data, browser cookies, system information, cryptocurrency wallet details, and even files from user directories. It supports major browsers like Chrome, Firefox, and Edge, and also targets messaging apps, email clients, and password managers.
Specifically, Meta Stealer targets popular wallet software to steal cryptocurrency and demonstrates adaptability, possibly being customizable for different types of attacks. Recent variants have included persistence mechanisms such as scheduled tasks and evasion techniques that manipulate Windows Defender exclusions or rely on open-source libraries to bypass security tools.
MetaStealer has been actively used in malspam campaigns and against macOS business users, often posing as potential clients to deliver obfuscated Go-based payloads disguised as business documents or app bundles.
Law Enforcement Disruption: Operation Secure
In early 2025, MetaStealer’s infrastructure was among the targets of Operation Secure, a global law enforcement operation spanning 26 countries. The effort led to 32 arrests and the takedown of thousands of malicious servers and domains, disrupting operations tied to MetaStealer, Lumma, and RisePro.
Despite these crackdowns, the malware and their associated logs are still actively traded across underground forums and illicit channels.
8. Mystic Stealer
Mystic Stealer quickly made its mark in the cybercrime ecosystem after surfacing in April 2023. Known for its highly obfuscated code and advanced evasion techniques, Mystic is designed to steal a wide range of sensitive data, from browser credentials and cryptocurrency wallets to Steam and Telegram session tokens.
It supports nearly 40 web browsers and over 70 browser extensions, and has increasingly added support for wallet extensions and desktop applications. Initially communicating with its Command and Control (C2) servers via a custom encrypted binary protocol, newer versions now use HTTP-based C2 communication, improving flexibility and stealth.
Mystic is written in C on the client side and uses Python with Django for its control panel. It employs several anti-analysis methods, including polymorphic string obfuscation, binary expiration, anti-virtualization checks, runtime constant calculation, and hash-based import resolution, all aimed at evading detection and slowing down reverse engineering efforts.
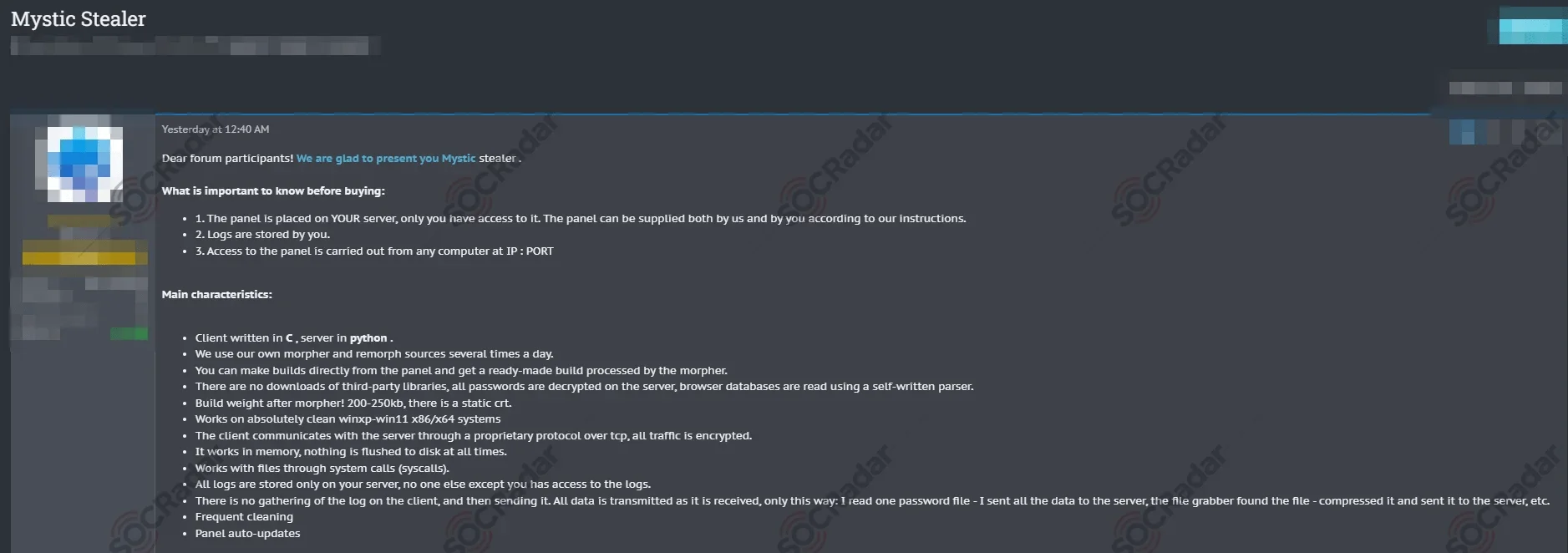
Mystic Stealer was put on a sale in different forums by the same threat actor (SOCRadar Dark Web News)
One of Mystic’s enhancements was the addition of loader functionality, enabling it to deliver and execute secondary payloads post-infection. In older versions, target application lists were hardcoded. Newer builds, however, dynamically retrieve their configurations from the C2 servers, allowing operators to adjust targets on the fly.
Mystic operates across a distributed C2 infrastructure, linked to both legitimate and bulletproof hosting providers. Its operations are supported by a Telegram channel run by the developer, where updates are shared and feature suggestions are crowdsourced from buyers.
9. Hawklog

An advertisement of Hawklog from a Telegram channel
Unlike the other entries on this list, Hawklog is not a stealer malware but a private cloud-based service that distributes data harvested by infostealers. It operates on a subscription model, offering weekly or monthly access to large troves of compromised credentials, browser data, and other sensitive information. But, this data was also distributed by other threat actors.
In January 2024, Hawklog suffered a major breach by the hacker group Mooncloud, resulting in the leak of 1.7 GB of internal data, primarily comprising emails. The breach occurred within Telegram channels.
While Hawklog may not develop its own malware, its role as a central distributor of stealer logs makes it a key enabler in the underground economy.
10. Nexus
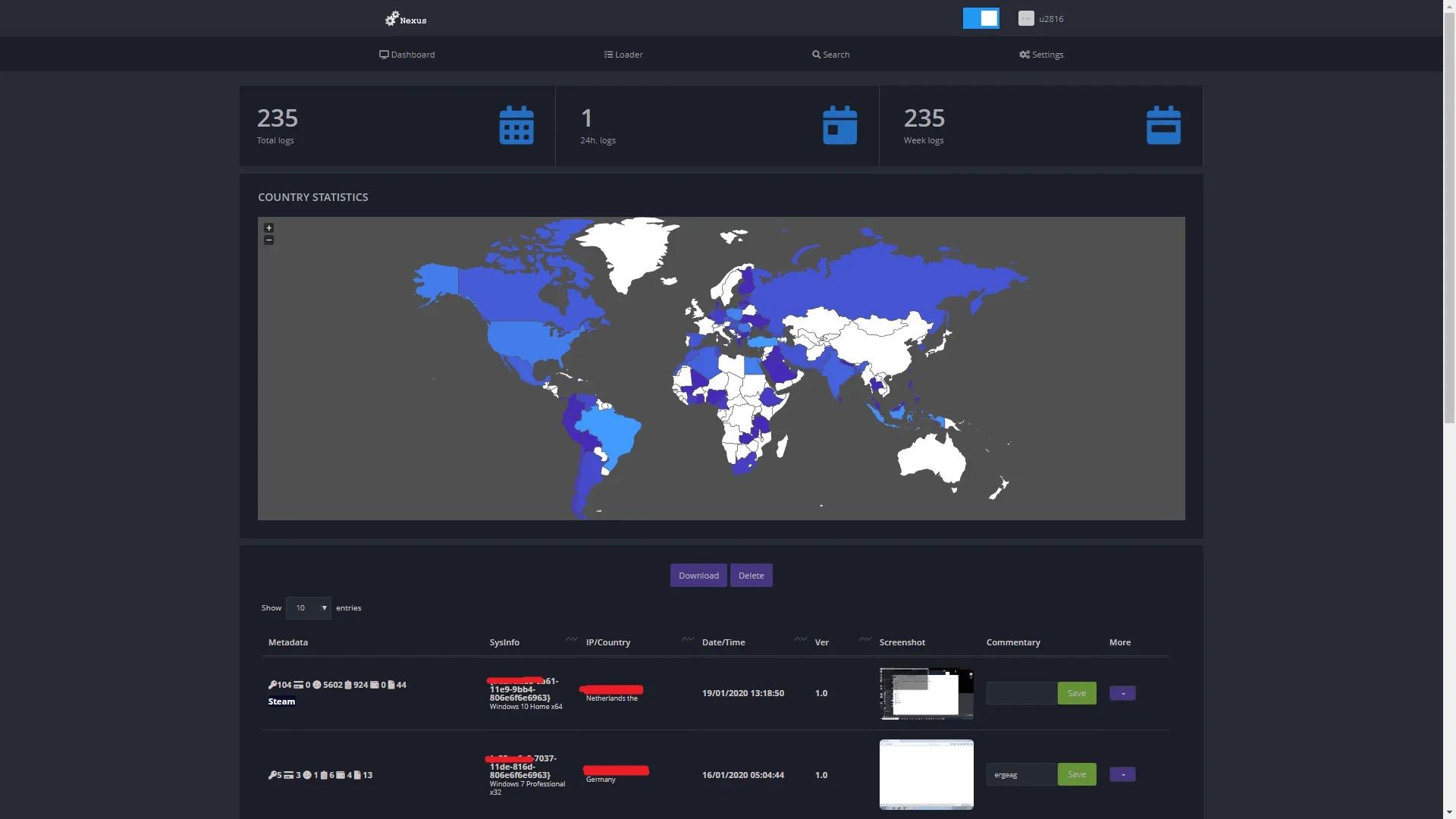
Nexus Stealer Dashboard (fr3d.hk)
Nexus Stealer, first introduced in 2020, has maintained a steady presence in the cybercrime landscape thanks to its broad compatibility and detailed data collection capabilities. Initially introduced on an underground forum, Nexus Stealer garnered attention for its extensive feature set tailored to the data theft objectives of malicious actors.
Nexus targets a wide array of applications and platforms, including Chromium-based browsers, Yandex-Browser, messaging apps like Telegram, Authy, Discord, and Steam, as well as FTP clients (FileZilla, WinSCP), VPNs (NordVPN, ProtonVPN), and software like WindowsSecureVault, Internet Explorer, Edge, Pidgin, PSI, PSI+. Its functionality includes credential theft, cookie extraction, screenshot capture, and detailed system profiling, collecting information such as CPU, GPU, RAM, and installed programs.
The stolen data is transmitted to a centralized web panel, providing operators with organized access for further exploitation. Nexus logs continue to be traded on dark web forums, where they fuel credential stuffing, account takeovers, and targeted intrusions.
Despite its initial impact and feature-rich design, Nexus Stealer’s novelty gradually waned as it became more familiar to cybersecurity professionals and security solutions. Over time, security measures evolved, and antivirus software became adept at detecting and neutralizing Nexus Stealer and similar malware variants.
Previously Ranked Stealer Logs
In our original 2024 ranking, Taurus and Octopus were also featured. However, given their reduced activity in recent stealer logs, we’ve removed them from the current top 10. Here’s a quick recap of what made them notable:
Taurus
Active since 2020 and attributed to the “Predator the Thief” group, was known for targeting credentials from browsers, crypto wallets, email clients, and more. It leveraged anti-sandbox techniques and obfuscation to evade detection and exfiltrated data using a fileless approach. Taurus was once widely sold in underground markets and later leaked as source code.
Octopus
First observed around 2018, Octopus Scanner stood out for its unusual method of spreading through GitHub repositories. It targeted developers using NetBeans IDE by injecting backdoors into project build files and source code. The malware ensured persistence and made cleanup particularly difficult by infecting both compiled and source components.
Conclusion
The top 10 stealer logs of 2025 highlight how deeply embedded infostealer malware has become in the cybercrime ecosystem. From Lumma’s affiliate-powered campaigns to persistent threats like Vidar, RedLine, and StealC, these tools are no longer the domain of elite actors; they are widely accessible, constantly evolving, and responsible for billions of exposed credentials.
Our analysis shows that stealer logs play a foundational role in enabling ransomware attacks, account takeovers, and financial fraud. They act as an early warning signal, often appearing in dark web markets and Telegram groups weeks before victims even realize their systems have been breached.
Given this threat, organizations need more than just reactive defenses. Platforms like SOCRadar offer proactive threat hunting and stealer log analysis capabilities, allowing enterprises to:
- Monitor for leaked credentials and session data in near real-time
- Detect early signs of compromise linked to stealer malware
- Investigate dark web mentions and actor activity tied to known logs
- Correlate exposed assets with their digital footprint for faster response
By combining Cyber Threat Intelligence, Dark Web Monitoring, and Attack Surface Management, SOCRadar helps reduce the gap between initial compromise and detection.
As stealer logs remain a go-to tool for cybercriminals in 2025 and beyond, staying ahead will require continuous visibility, timely intelligence, and the ability to act before attackers do.