
Top Cyber Threats Faced by the Aviation Industry
The aviation industry covers a broad spectrum of stakeholders, including airlines, airports, technology providers, etc. It is one of the most important critical infrastructures, with all its network, assets, and systems. It also interacts with various essential infrastructure verticals, including defense and national security, transportation, communication, banking, and energy. As a result, when the operation of the aviation industry is disrupted, negative consequences emerge in establishing social order and delivering public services.
The aviation industry, which operates internationally and hosts many sub-sectors, such as tourism and foreign trade, must benefit from technological solutions to meet the needs of this complex structure. In this context, the sector is gradually becoming digital, with increased use of innovative technology. Within the abovementioned issues, cyber-attacks on the aviation industry have recently increased.
Threat Actors and Motivations
Due to the nature of the aviation industry, threat actors are motivated by access to sensitive data such as passports and high-value credit card information. Major threat actors and their motivations are as listed below:
APT (Advanced Persistent Threat): These organizations conduct state-sponsored attacks to steal intellectual property and intelligence to weaken other countries’ aviation capabilities, improve local aviation capabilities, and develop preventive technologies against other countries’ capabilities.
Cybercrime attackers: They attack to make money. They concentrate on causing the most damage possible and have the necessary knowledge and skills.
Cyber-terrorists: They are triggered by political, religious, ideological, and social factors. They attack to endanger national security, cause mass casualties, harm the economy, disrupt public order and morale, and undermine trust in aviation systems.
Cyber spies: They target the aviation industry, one of the most important critical infrastructures, with the goal of financial, industrial, political, and diplomatic espionage.
Nation-state actors: They can attack for political reasons or as part of a cyber war.
Insiders: Employees, ex-employees, or business partners who are dissatisfied. Their motivation could be monetary gain or a desire for revenge.
Activists: They are not motivated by financial or political considerations. They attack to gain more influence, recognition, and excitement.
Passive observers: They act intending to gather information. They obtain a real-time picture of air traffic and communication from public and private websites and mobile applications that display air traffic by taking advantage of the open nature of air traffic protocols.
Based on SOCRadar analysis, the threat actor ‘pumpedkicks’ shares the most cyber threat-related posts. On the other hand, the LockBit group, one of the most active ransomware groups in many verticals, stands out as the ransomware group that most targets the aviation industry.
Attack Surface and Vulnerabilities
The use of complex and interconnected information technology systems in the aviation industry is increasing daily. From Wi-Fi connections and in-flight entertainment systems for passengers to software used at airports and airlines to manage security controls and reservations, complex information technology solutions are used throughout the industry supply chain. These modern technologies have a significant positive impact on aircraft control systems, improving the quality of aviation operations and increasing flight safety and performance. However, it feeds an ecosystem where data flows between numerous stakeholders and internal/external systems. As a result, it broadens the attack surface.
The basic technologies used in the aviation industry can be categorized under the headings of smart systems, IoT devices, Cloud infrastructures, Bigdata, and Blockchain. Especially remotely targetable smart systems (Biometric Systems, robotic systems, etc.), IoT devices (sensors, actuators, etc.), and cloud systems are the target of attackers. The major systems frequently exposed to cyber threats in the aviation industry are:
- Aircraft IP networks of flights
- Digital Air Traffic Controls (ATCs) and traffic management systems
- Flight-By-Wire systems
- In-flight interface devices
- Flight history servers
- Fleet and route planning systems
- Passenger reservation systems and frequent flyer or loyalty programs
- Ticket booking portals.
- Cargo handling and shipping
- Access, Departures, and Passport Control Systems
- Cabin Crew devices
- Insider threats
Cyber Attacks on Aviation Industry in Recent Years
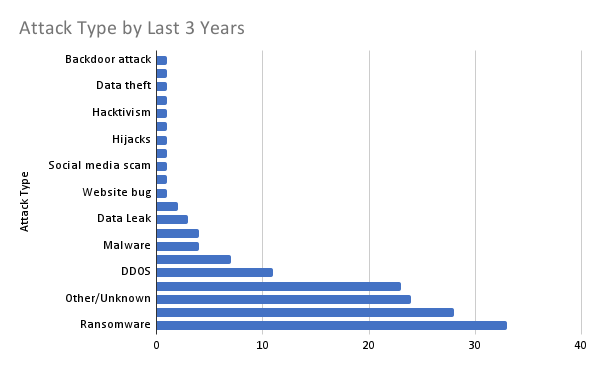
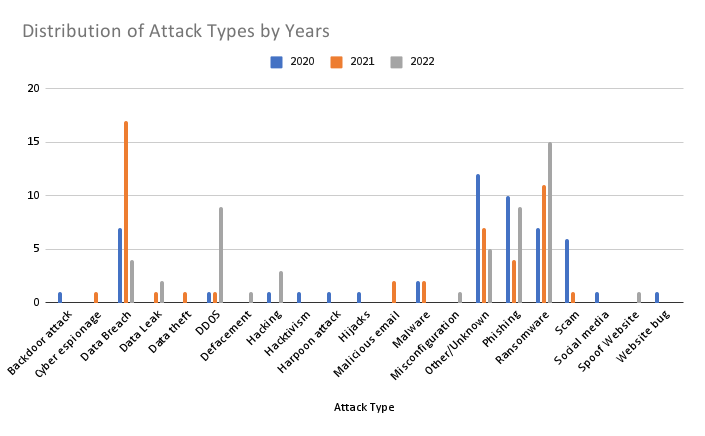
In recent years, cyber incidents in the aviation industry have been reviewed within the context of events monitored by Eurocontrol. Eurocontrol (a pan-European, civil-military organization dedicated to supporting European aviation) publishes the EATM-CERT (European Air Traffic Management Computer Emergency Response Team) Aviation Cyber Event Map. The data in this map has led to the following findings and graphics:
- 52 attacks were reported in 2020, 48 attacks were reported in 2021, and 50 attacks were reported till the end of August 2022. So cyber incidents in 2022 have reached the average of 2020 and 2021 just eight months.
- The most seen attack types in the last three years (2020, 2021, and 2022) are Ransomware (%22), Data Breach (%18.6), Phishing (%15.3), and DDoS (%7.3). Meanwhile, %16 of the attack type was other/unknown.
- In addition to civil aviation attacks, eight military-related incidents were reported. Some of those attacks were aimed at cyber espionage and data theft. Two of these attacks were carried out with ransomware, two with malware, and one with a backdoor, and it is not known how three of them were performed.
Recent Attacks
Seven attacks took place in August 2022. Three were classified as high, while four were classified as medium severity. Those attacks were as follows:
- Threat actors launched a cyberattack against a Portuguese airline (TAP Air Portugal). In a statement, the airline assured that its security mechanisms were promptly activated and unauthorized access was blocked.
- DDoS attacks targeted key Taiwanese websites just before House of Representatives Speaker Nancy Pelosi arrived in Taiwan. At least four websites were targeted, including Taiwan Taoyuan International Airport.
- Some Malaysian and UAE-based airline passenger databases have been marketed on the dark web and underground forums.
- An Indian airline (Akasa Air) suffered a data breach, exposing passengers’ personal information
- A data breach in a Canadian airline (WestJet) app exposed users’ personal information.
- A ransomware group had targeted a major airline technology provider (Accelya).
- An international group of volunteer hackers destroyed the natural gas system at a Russian oil hub and knocked out a power plant and an airport.
- American Airlines Group Inc (AAL.O) reported a data breach on the email accounts of a small number of their team members. Addresses, phone numbers, driver’s license numbers, passport numbers, and/or medical information may have been accessed by an unauthorized threat actor.
- Philippine Airlines confirmed that a cybersecurity breach had affected their third-party IT provider for their frequent flyer program. Members’ names, birth dates, nationality, gender, joining date, tier level, and points balance were among the information compromised. The airline advised members to change their passwords immediately.
- The LockBit ransomware targeted the Agency for Aerial Navigation Safety in Africa and Madagascar (ASECNA). During this high severity incidence, the data of the agency’s 18 member countries have been encrypted, and the agency has threatened to disclose breached data to the dark web unless a $25,000 ransom is paid.
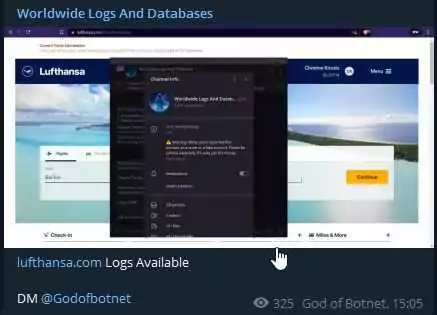
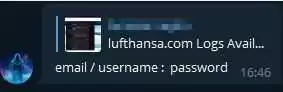
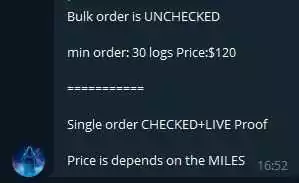
In addition to recent ones, SOCRadar analysts’ most recent dark web monitoring resulted that sensitive data of a well-known airline has been marketed on underground forums. Below are some screenshots of dark web posts.
Conclusions
In the aviation industry, like in many other verticals, Cyber attackers are motivated by financial and political purposes and the desire to obtain sensitive information. In addition to financial and reputational loss risks, successful attacks in the aviation sector may cause air traffic disruptions, accidents, and even loss of life.
The aviation industry, which utilizes numerous technological solutions to provide its clients with the best user experience, must show the same sensitivity in detecting and responding to cyber threats. In this context, some recommendations for the aviation industry to improve its ability to predict, detect, respond to, and mitigate cyber threats are below;
- Employee education in the subject of cyber security, as well as equipping them with the necessary high-capacity tools
- Identify the supply chain risk points
- Keeping data transmission between the ground and the aircraft secure
- Secure access to network devices and systems
- Protecting endpoint devices
- Building a solid Identity and Access Management (IAM) and Customer Identity and Access Management (CIAM) systems
- Encrypt all data transmitted, stored, and processed in environments from beginning to end.
- Assessing all aviation systems for security vulnerabilities, establishing risk assessment and prioritization
- Determine the attack surface and protect all digital assets,
- Activate regulations such as SOC1 and SOC2,
- Using cyber threat intelligence to determine possible threats and respond proactively is critical.




































