Velvet Ant’s Strategic Targeting: A Long-Term Cyber Espionage Campaign Against F5 BIG-IP Systems
In the constantly evolving landscape of cybersecurity, the Velvet Ant Advanced Persistent Threat (APT) group, allegedly supported by the Chinese government, has emerged as a significant adversary.
The Velvet Ant APT group has been engaging in a prolonged cyber espionage campaign, specifically targeting F5 BIG-IP devices across various sectors worldwide. Their sophisticated attack techniques and persistent nature make them a formidable threat to global cybersecurity.

An AI illustration of Velvet Ant’s campaign
Why Do Attackers Target F5 BIG-IP Systems?
F5 BIG-IP systems are critical networking devices, including Application Delivery Controllers (ADCs), that optimize and secure network traffic for large enterprises and service providers. These systems manage extensive data loads and facilitate global internet traffic, making them prime targets for cyber attackers.
Vulnerabilities within these systems can be exploited, allowing unauthorized access or service disruptions. Attackers leverage these vulnerabilities to infiltrate networks, often aiming to exfiltrate data or deploy ransomware.
To counter these threats, regular system updates, monitoring network traffic, and adhering to cybersecurity best practices are essential.
Attack Techniques of Velvet Ant APT
Velvet Ant’s techniques are mapped to the MITRE ATT&CK framework, showcasing their methodical and layered approach to cyber espionage:
- Initial Access:
- T1133 – External Remote Services: By exploiting vulnerabilities in remote services, Velvet Ant gains initial access. To mitigate this risk, organizations should enforce robust Multi-Factor Authentication (MFA) and conduct regular audits of access policies.
- Execution:
- T1047 – Windows Management Instrumentation: Monitoring WMI activity and restricting access to necessary accounts can thwart unauthorized executions.
- T1059.008 – Command and Scripting Interpreter: Network Device CLI: Limiting access to command line interfaces and logging all executed commands is crucial for early detection.
- Persistence:
- T1037.004 – Boot or Logon Initialization Scripts: Vigilant monitoring and restriction of changes to initialization scripts can prevent persistent threats from taking root.
- T1078.002/003 – Valid Accounts: Enforcing MFA and strong password policies for domain and local accounts helps maintain integrity.
- Privilege Escalation:
- T1078.002 – Valid Accounts: Domain Accounts: Implementing robust account security measures is critical to prevent unauthorized privilege escalation.
- Defense Evasion:
- T1574.001 – Hijack Execution Flow: DLL Search Order Hijacking: Application whitelisting can prevent unauthorized DLL execution.
- T1562.004 – Impair Defenses: Disable or Modify System Firewall: Restricting administrative access to firewall configurations and logging changes can counter defense evasion attempts.
- Credential Access:
- T1003.001 – OS Credential Dumping: LSASS Memory: Advanced endpoint protection solutions are necessary to detect and block credential dumping activities.
- Discovery:
- T1087.002 – Account Discovery: Domain Account: Logging and monitoring account enumeration activities, and applying rate limiting can detect reconnaissance efforts.
- T1083 – File and Directory Discovery: Restricting access to sensitive files and directories is essential.
- Lateral Movement:
- T1021.001 – Remote Services: SMB/Windows Admin Shares: Implementing SMB signing and encryption can limit lateral movement.
- Collection:
- T1039 – Data from Network Shared Drive: Monitoring and restricting access to sensitive data on network shared drives is crucial.
- Command and Control:
- T1572 – Protocol Tunneling: Network intrusion detection systems can identify and block unauthorized tunneling activities.
- Exfiltration:
- T1048 – Exfiltration Over Alternative Protocol:Data loss prevention (DLP) solutions can help detect and prevent unauthorized data exfiltration.
Impact and Further Observations
Velvet Ant has demonstrated a significant ability to maintain persistent access to high-value targets, often exploiting overlooked vulnerabilities in legacy systems like F5 BIG-IP devices.
Their agility in adapting to remediation efforts highlights their advanced operational capabilities. The use of sophisticated tools such as PlugX – a Remote Access Trojan (RAT) – further illustrates their technical prowess and persistence.
Visit the Campaigns page on the SOCRadar XTI platform for the latest campaigns and extensive details.
Conclusion
The Velvet Ant cyber espionage campaign exemplifies the sophisticated threats posed by state-sponsored APT groups. Combating such threats requires a blend of proactive and reactive measures.
By integrating advanced security solutions, continuous monitoring, and stringent access controls, organizations can bolster their defenses against these persistent adversaries. Ongoing vigilance and adaptability, coupled with a deep understanding of the threat landscape, are essential for maintaining a robust cybersecurity posture amidst evolving cyber threats.
SOCRadar is uniquely positioned to assist organizations in this regard. Through its comprehensive threat intelligence capabilities, SOCRadar provides real-time monitoring, advanced threat detection, and actionable insights to preemptively identify and mitigate potential threats like those posed by Velvet Ant.
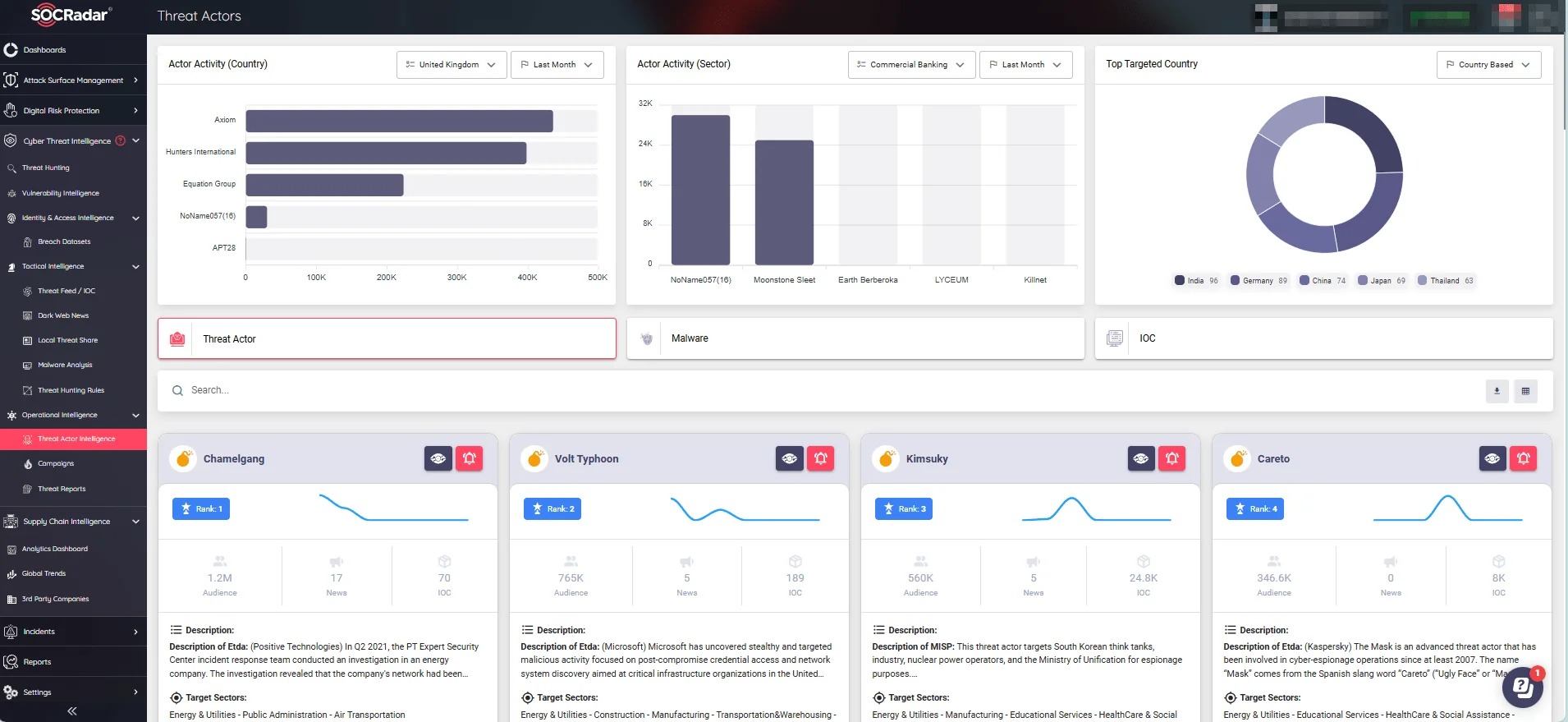
Threat Actor Intelligence page (SOCRadar XTI)
Furthermore, the SOCRadar LABS Campaigns page offers detailed analysis and updates on various cyber campaigns, helping organizations stay informed and prepared against emerging threats.
By leveraging SOCRadar’s extensive resources and tools, organizations can enhance their resilience against the complex and persistent tactics employed by the Velvet Ant group, safeguard their critical assets, and maintain operational integrity in the face of sophisticated cyber espionage activities.




































