Dark Web Profile: Brain Cipher
The Brain Cipher ransomware group gained widespread attention after a high-profile attack on Indonesia’s National Data Center (Pusat Data Nasional – PDN), which disrupted essential public services, including immigration. On June 20, the cyberattack targeted one of Indonesia’s national data centers. This attack encrypted government servers, disrupting immigration services, passport control, the issuance of event permits, and other online services.
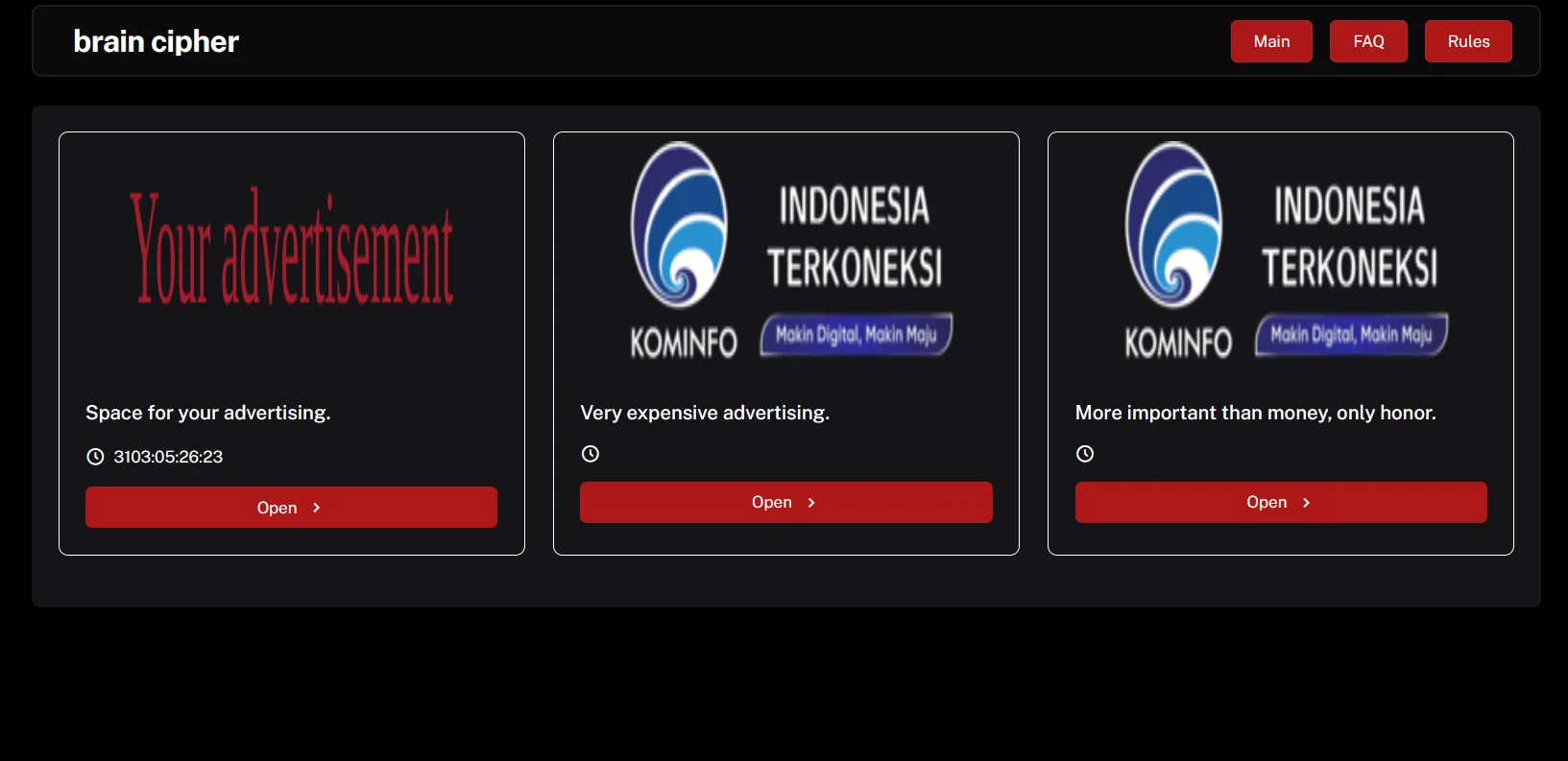
Home page of Brain Cipher’s DLS(Data Leak Site)
Indonesia was developing national data centers to store servers securely used by the government for online services and data hosting. However, the ransomware attack disrupted the ongoing development. The Indonesian government confirmed that Brain Cipher, a new ransomware operation, was responsible for the attack, which affected over 200 government agencies.
Who is Brain Cipher
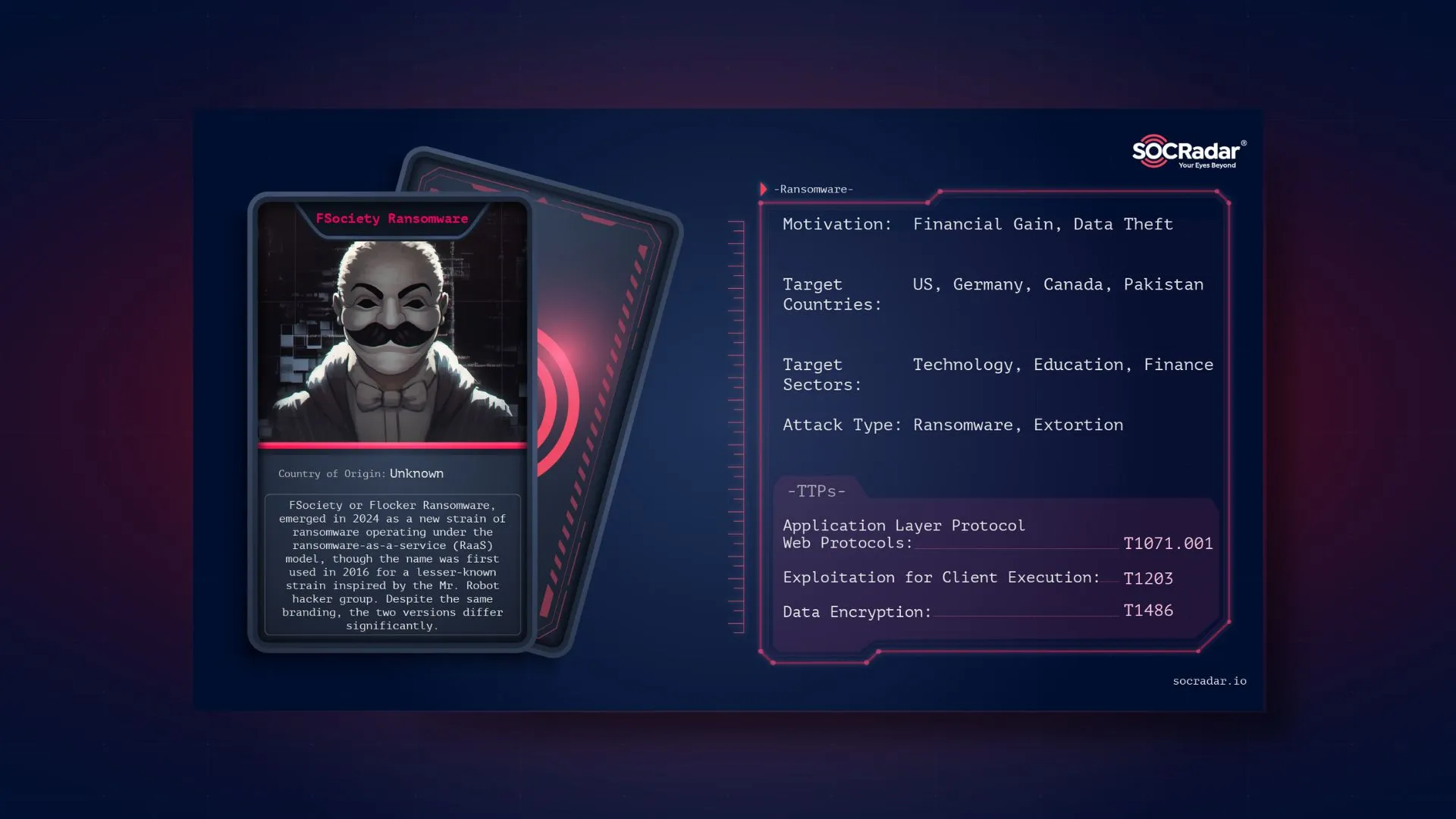
Brain Cipher Ransomware was first mentioned on June 16, 2024, and the earliest tweet we could trace was from June 17. However, the following week, it quickly gained widespread media attention when it was revealed as the perpetrator behind attacks on data centers in Indonesia.
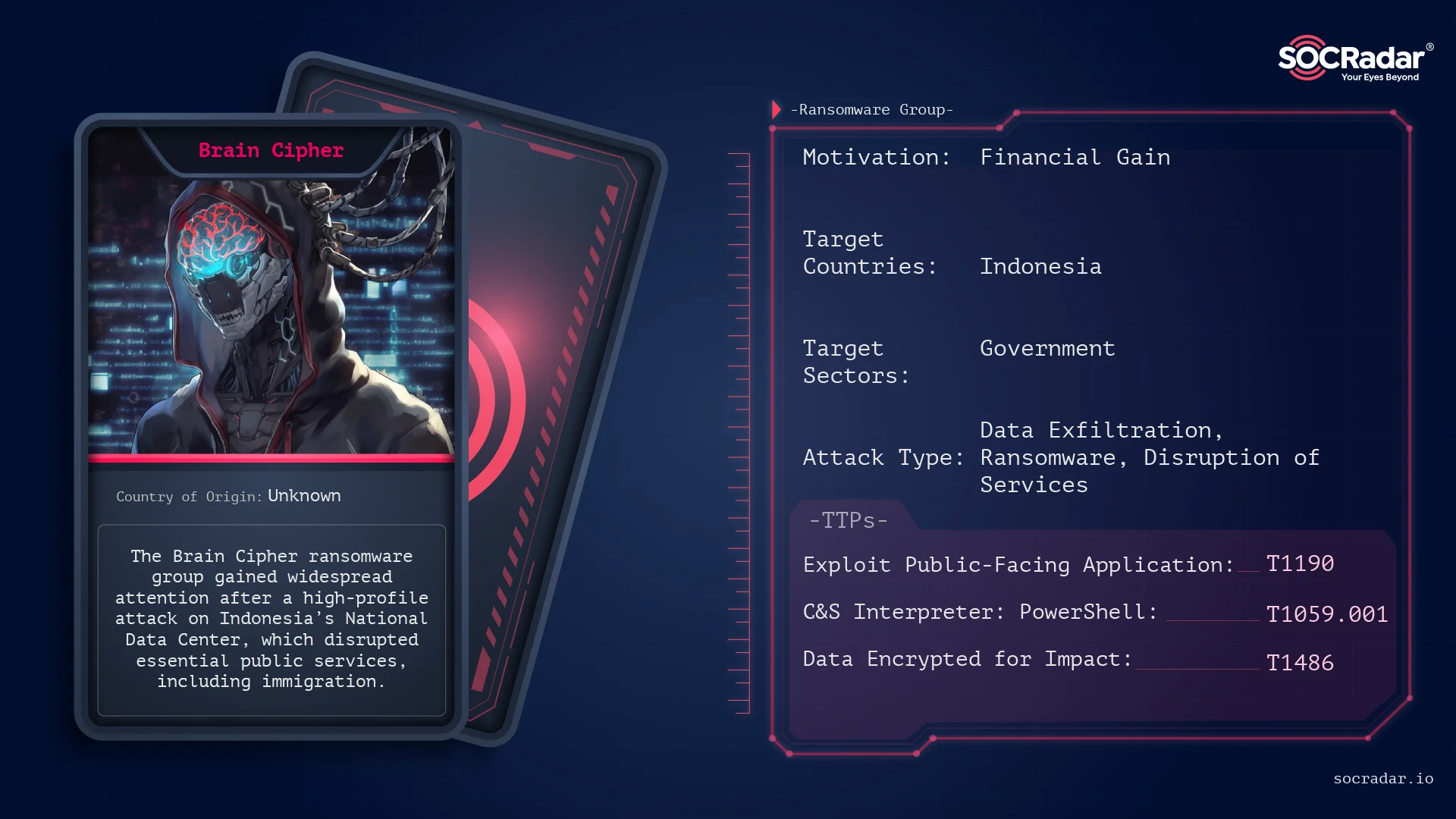
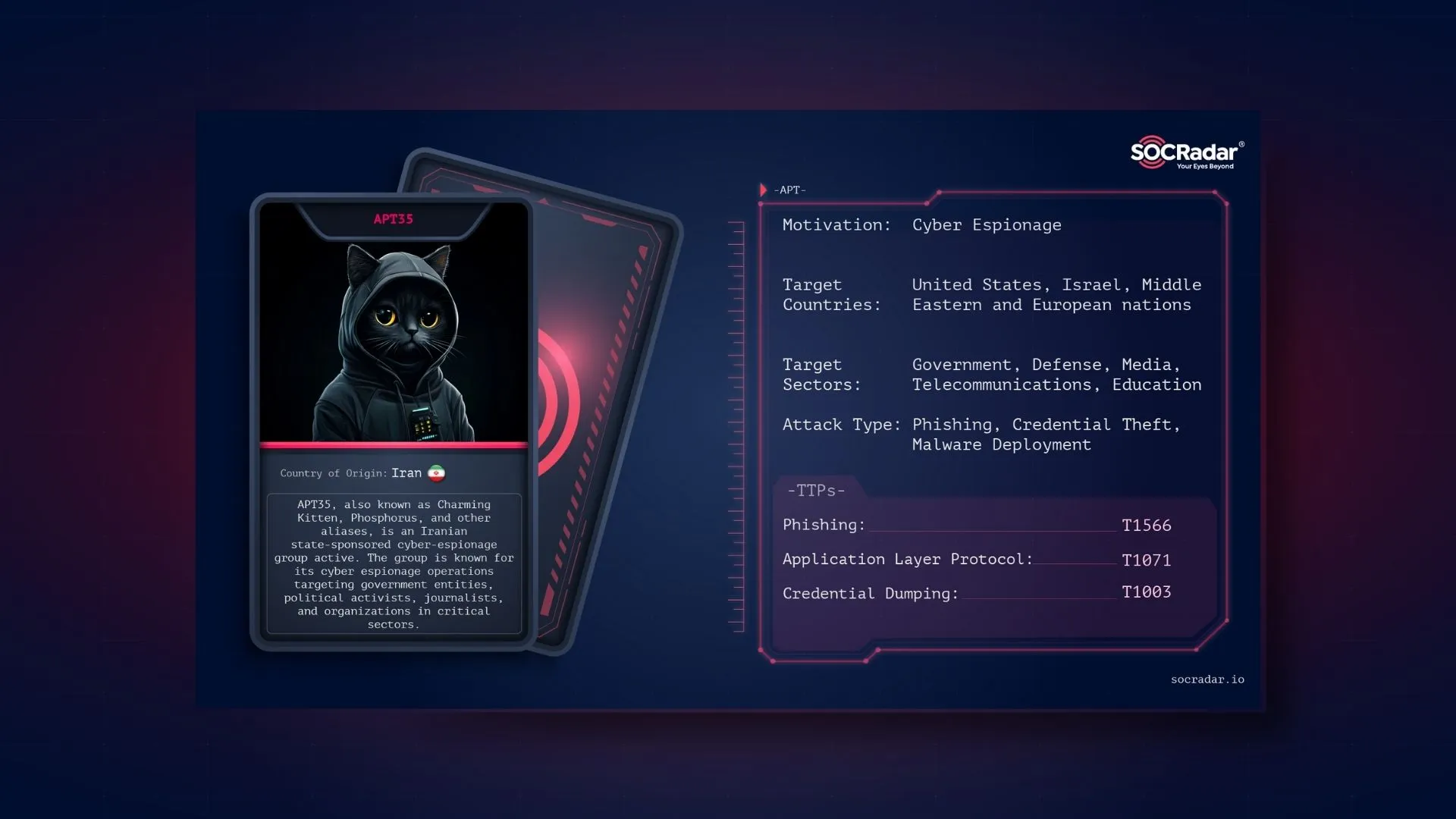
Threat actor card of Brain Cipher
When Indonesian agencies identified Brain Cipher as the perpetrator, the victim was not listed on the Brain Cipher Data Leak Site, initially. Shortly after, the expected victim announcement came.
However, the incident took an unexpected turn on July 2, 2024, when the group apologized to Indonesia and promised to release a free decryption tool the following day. Initially demanding a ransom of $8,000,000, the group backed down and, in their announcement, only left a Monero wallet for optional donations.
The announcement post from Brain Cipher in their DLS
It appears that the group followed through on their promise. They shared an onion link with the alleged decryption key and instructions on how to use it. However, there has not been any official statement yet.
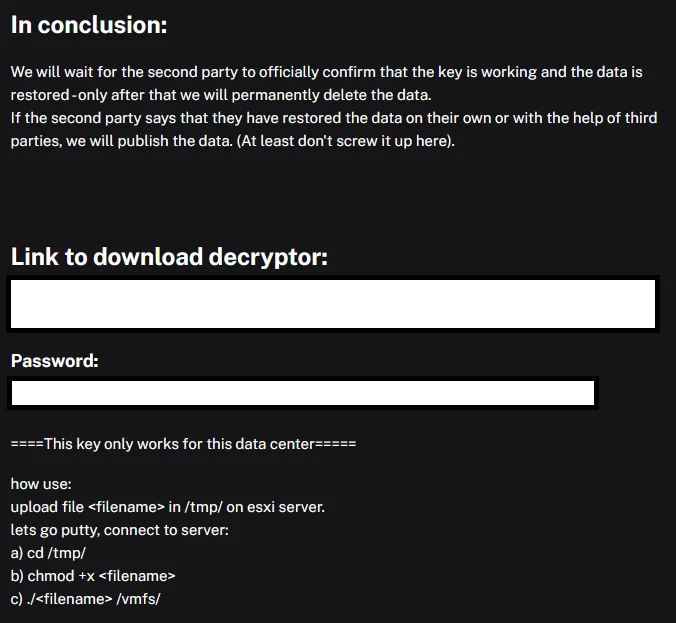
Later post of Brain Cipher, providing an alleged decryptor
So, what will happen to Brain Cipher from now on, how was the group successful in this attack, and what does leaked builder mean? Let’s examine it.
How Brain Cipher Works
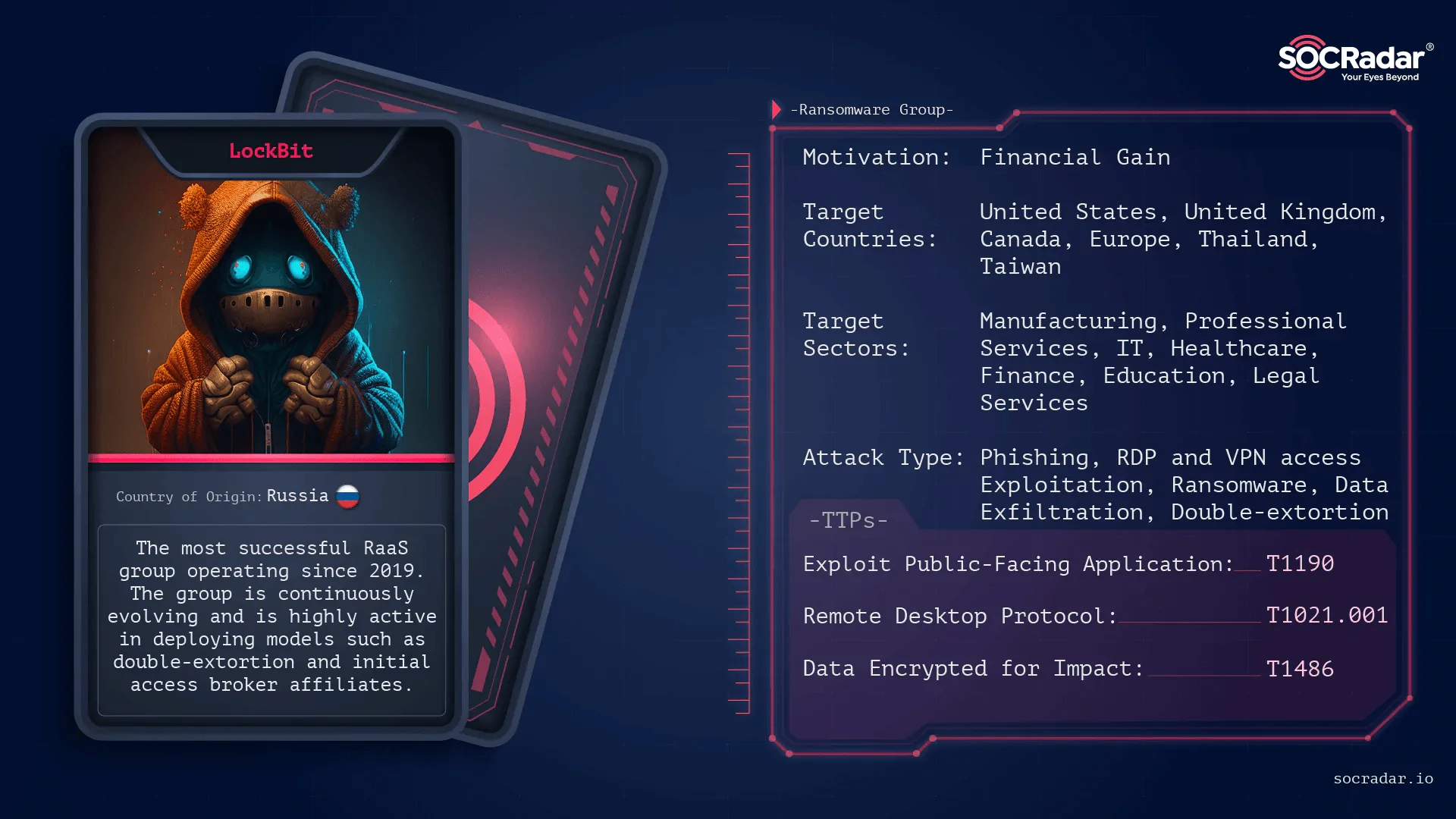
This group used LockBit’s leaked builder and shared characteristics with many newly emerged groups. Furthermore, Brain Cipher has only made some minor changes to the encryptor. So, let’s first look at what this leaked builder is.
LockBit released its version called LockBit 3.0, or Black, in June 2022, and has continued to use similar variations up to the present day. At its launch, LockBit even introduced its own bug bounty program.
During these developments, a significant event occurred that would reshape the ransomware landscape. vx-underground reported that they were contacted by a user named protonleaks, who forwarded them a copy of the builder. Subsequently, a hacker forum user known as LockBitSupp, or their representative, stated that the leak happened due to a disgruntled developer.
The leaked LockBit 3.0 builder allowed anyone to easily create the necessary executables for their own ransomware operations, including an encryptor, decryptor, and specialized tools for launching the decryptor in specific ways.
The builder consisted of four files: an encryption key generator, a builder, a modifiable configuration file, and a batch file to compile everything.
The included ‘config.json’ file could be customized to modify the encryptor, change configuration options, terminate specific processes and services, and specify the command and control server. By adjusting this configuration file, any threat actor could tailor it to their needs and alter the ransom note to link to their own infrastructure. Thus, a new generation of ransomware groups arose.
Now, let’s examine both the group and the builder through Brain Cipher’s most known sample.
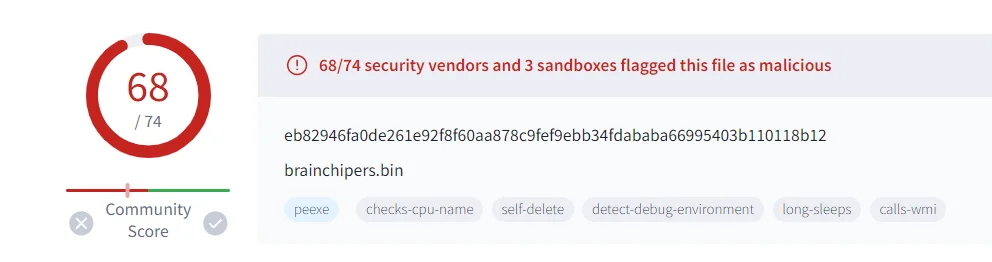
eb82946fa0de261e92f8f60aa878c9fef9ebb34fdababa66995403b110118b12 hashed sample of Brain Cipher
Modus Operandi
Brain Cipher is a variant of the LockBit ransomware family. It is designed to encrypt files on compromised systems, append a distinctive file extension, and demand a ransom payment for decryption.
Although few sources have stated the initial access vector as phishing, we cannot verify this claim. However, especially when we look at the latest statements of the group and network connections, it can be concluded that the attacker knows his victim and where they are attacking. In this context, we can talk about more specific initial access vectors, such as vulnerability exploitation or a spear-phishing operation.
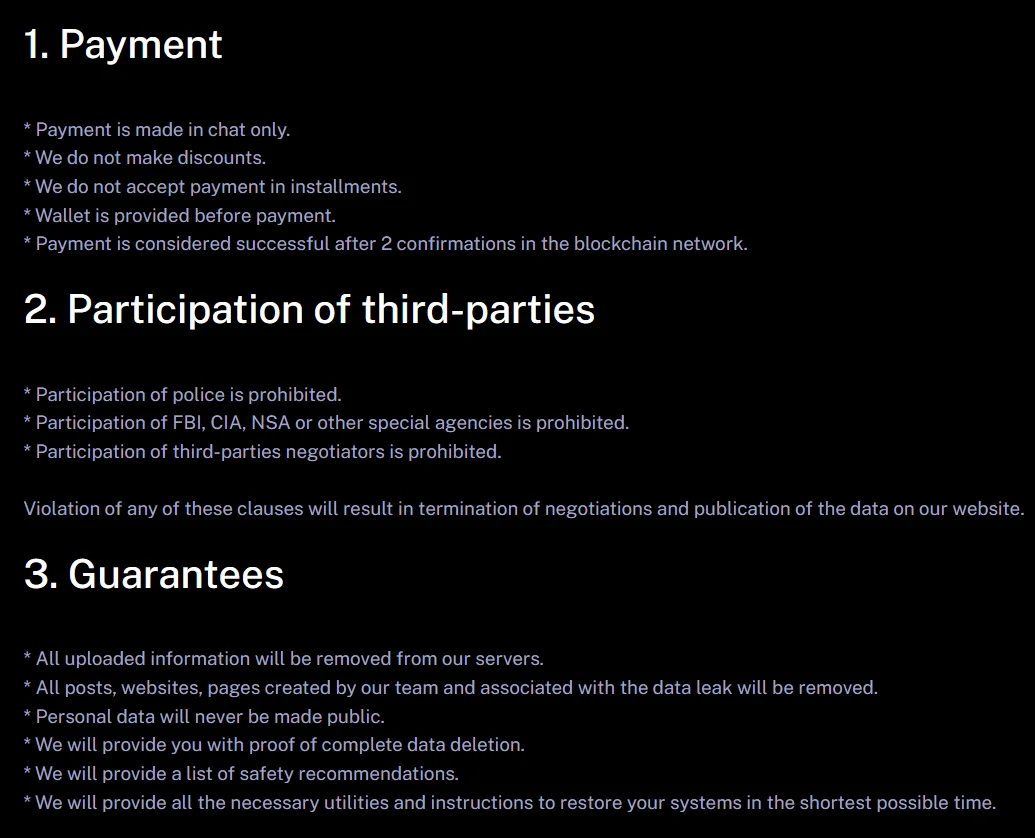
Terms of service in Brain Cipher’s DLS
The Brain Cipher sample, 9gGB296kd4.exe, is associated with the LockBit ransomware. The specific sample has the following identifiers:
MD5: 448f1796fe8de02194b21c0715e0a5f6
SHA1: 935c0b398373f8c5e8ef03c92d606c72c44f49b8
SHA256: eb82946fa0de273dbaaaef320e8925d9a8cc5b7e839e97e2982a1d18ba43c1a4
Brain Cipher is detected with a high confidence level of 100%, indicating its apparent association with ransomware activities. Detection mechanisms include multiple Yara rules and AI-based detection signatures, identifying its malicious nature. Despite this, the ransomware employs evasion techniques, making it a challenging adversary for traditional security measures.
Upon execution, Brain Cipher immediately deletes itself to hinder forensic analysis and detection. It then modifies user documents and overwrites browser settings, explicitly targeting Mozilla Firefox on the sandbox analysis. The ransomware writes numerous high-entropy files, indicating its encryption activities.
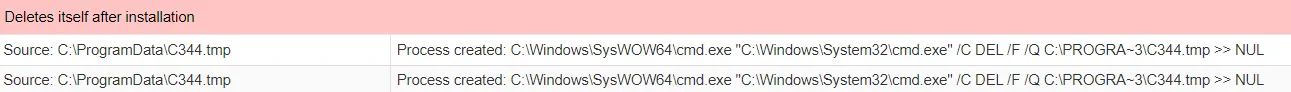
Delete command run through cmd (JoeSandbox)
Brain Cipher is equipped with several persistence and evasion techniques. It hides threads from debuggers and executes in a suspended mode to avoid detection. Additionally, it enables debug and security privileges, potentially allowing it to bypass security measures. The use of code obfuscation further complicates detection and analysis efforts.
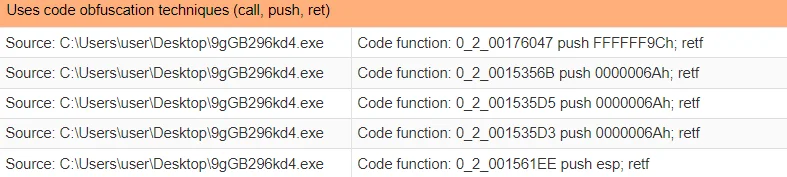
Simple obfuscation techniques that are common for many ransomware (JoeSandbox)
The obfuscation technique used in Brain Cipher involves the instruction sequence push FFFFFF9Ch; retf. This sequence pushes the hexadecimal value FFFFFF9C onto the stack and then performs a far return (retf), which uses the value on the stack to alter the instruction pointer and code segment registers. This method complicates the control flow, making it difficult for analysis tools and researchers to trace the malware’s execution path.
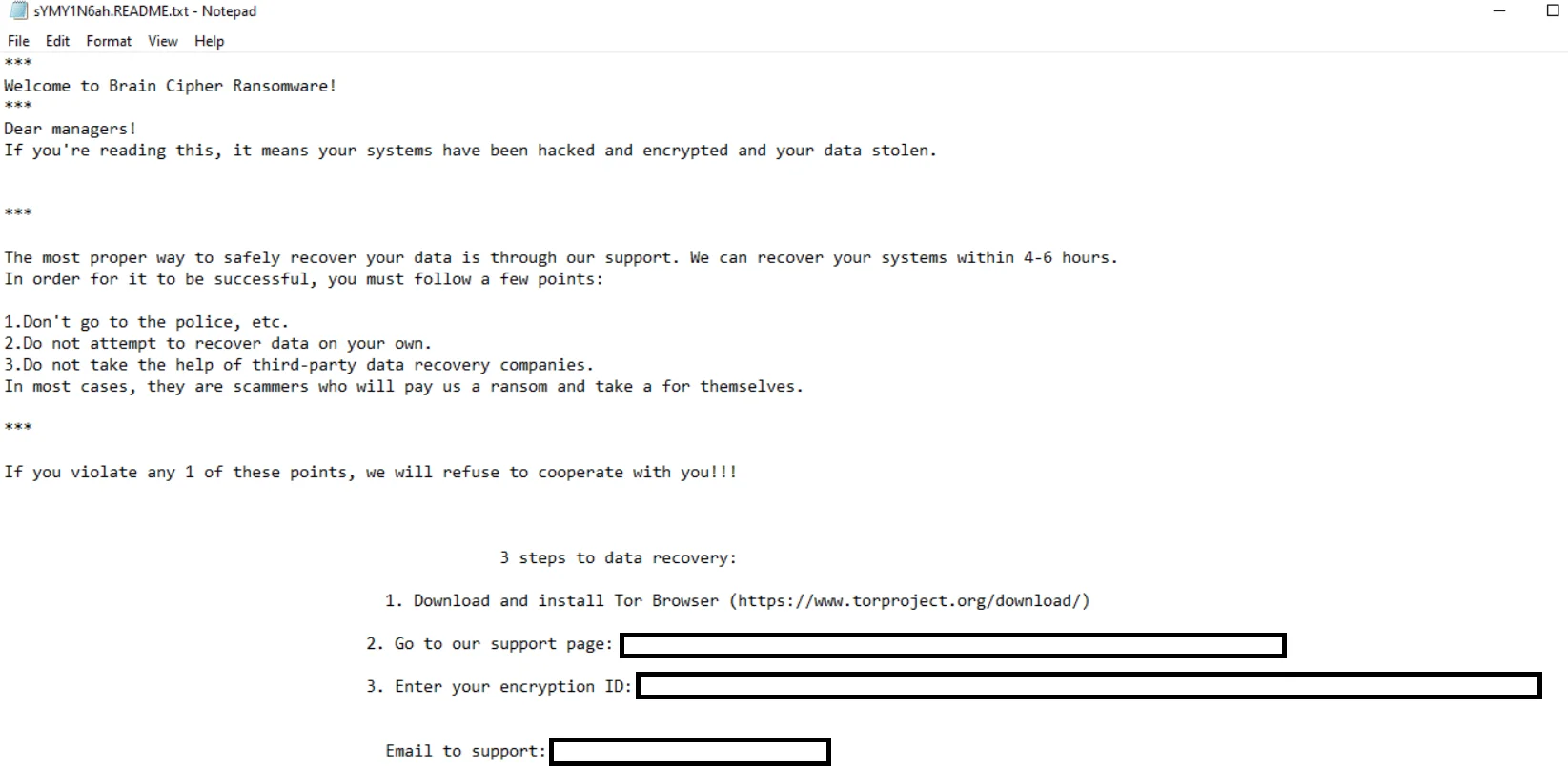
Ransom note
In addition to its encryption capabilities, Brain Cipher attempts to harvest and steal sensitive information from the infected system, including browser information, thereby increasing the potential damage to the victim.
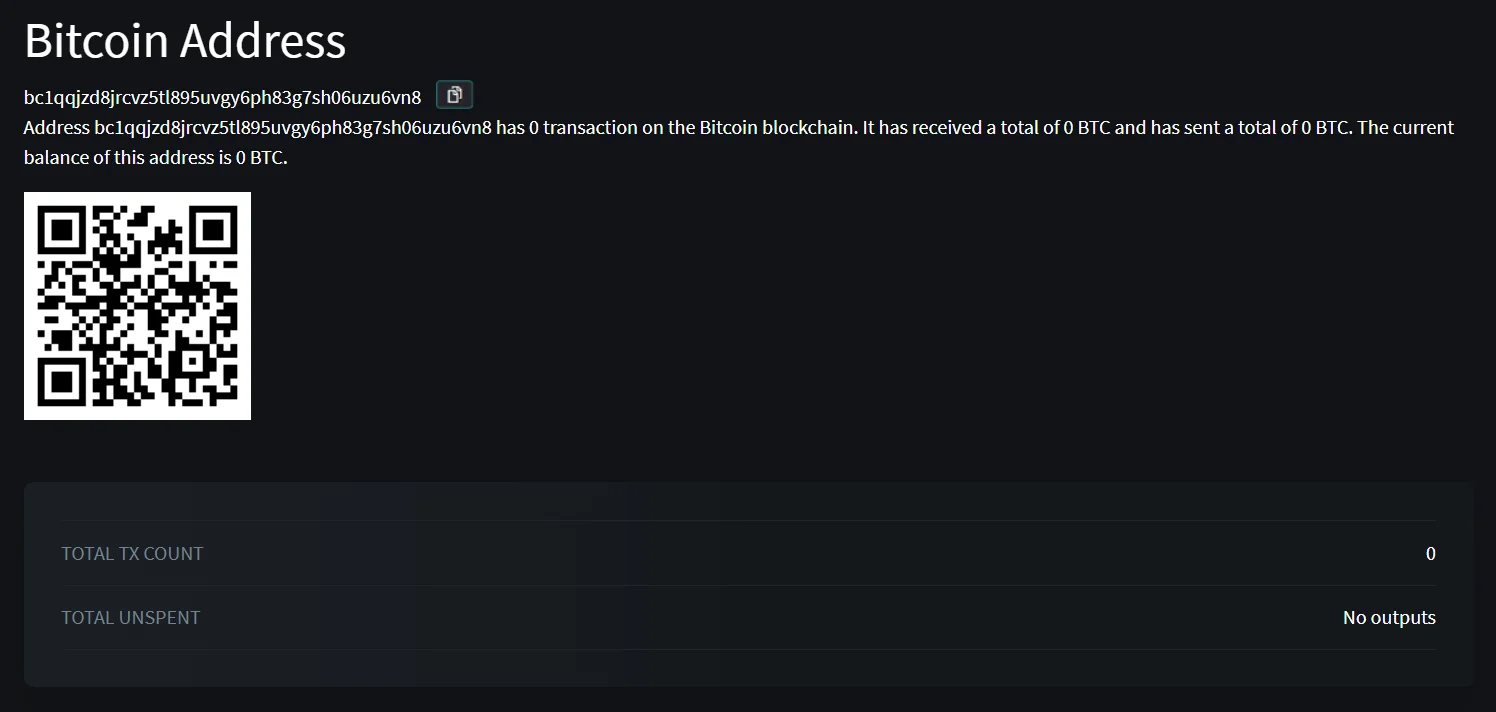
There isn’t any transaction to their Bitcoin wallet (BTCscan). They also have a Monero wallet for donations, but it can’t be traced therefore its not possible for now to say whether they got any donations
Lastly, it is essential to remember that the Brain Cipher and many other ransomware that are derived from LockBit’s leaked builder are detectable by various signatures, including specific YARA rules designed to identify LockBit ransomware and multiple antivirus scanners. Despite this, its evasion techniques often make detection a race against time.
Conclusion
In recent years, the cybersecurity landscape has been increasingly threatened by ransomware variants derived from leaked builders, such as those associated with the LockBit family. These leaked builders provide cybercriminals with the tools needed to create custom ransomware strains, making it easier for even less sophisticated attackers to launch devastating attacks. To effectively mitigate the risks posed by these threats, a comprehensive and proactive approach is required. Next sections include key strategies and actions to defend against ransomware derived from leaked builders and Brain Cipher.
How to Mitigate: Actions Against Leaked Builders?
- Strengthen Endpoint Security
Implement endpoint security solutions that include advanced threat detection capabilities. These solutions should leverage machine learning, behavioral analysis, and heuristics to detect and block ransomware activities, even if the ransomware is newly created using leaked builders hence the similarity between different strains are very close, it’s possible to detect.
- Regular Patching and Updates
Ensure that all software, including operating systems, applications, and security tools, is regularly updated and patched. Ransomware operators and access brokers often exploit known vulnerabilities in outdated software to gain initial access to systems.
- Network Segmentation
Segment networks to block or limit the spread of ransomware. By dividing the network into isolated segments, you can contain an infection to a small part of the network, preventing it from affecting the entire infrastructure.
- Backup and Recovery Plans
Maintain regular backups of critical data and ensure backups are stored offline or in isolated environments. Test the backups and recovery procedures regularly to ensure that data can be restored quickly in the event of a ransomware attack since the files encrypted by LockBit’s leaked builder are known to be undecryptable without a key.
- User Training and Awareness
Educate employees about the dangers of ransomware and the importance of safe online practices. Training should cover recognizing phishing emails, avoiding suspicious downloads, and reporting potential security incidents promptly.
- Email and Web Filtering
Deploy email and web filtering solutions to block malicious attachments, links, and downloads. These tools can prevent ransomware from reaching users by identifying and quarantining potential threats before they can cause harm. Note that SOCRadar Malware Analysis can also analyze .EML files to check your suspicions about email content and attached files.
- Access Controls and Privilege Management
Implement strict access controls and ensure that users have only the permissions necessary for their roles. Use the principle of least privilege to minimize the potential impact of compromised accounts. Regularly review and update access rights.
- Threat Intelligence and Monitoring
Leverage threat intelligence to stay informed about the latest ransomware Tactics, Techniques, and Procedures (TTPs). Implement continuous monitoring to detect unusual activities and respond to threats in real-time.
- Incident Response Plan
Develop and maintain a detailed incident response plan that includes specific procedures for dealing with ransomware attacks. Conduct regular drills and simulations to ensure that your team is prepared to respond effectively.
How Can SOCRadar Help?
Understanding the tactics and strategies of ransomware variants like Brain Cipher is crucial for organizations looking to bolster their cybersecurity defenses. Implementing robust mitigation measures and staying vigilant are key steps in combating these threats effectively.
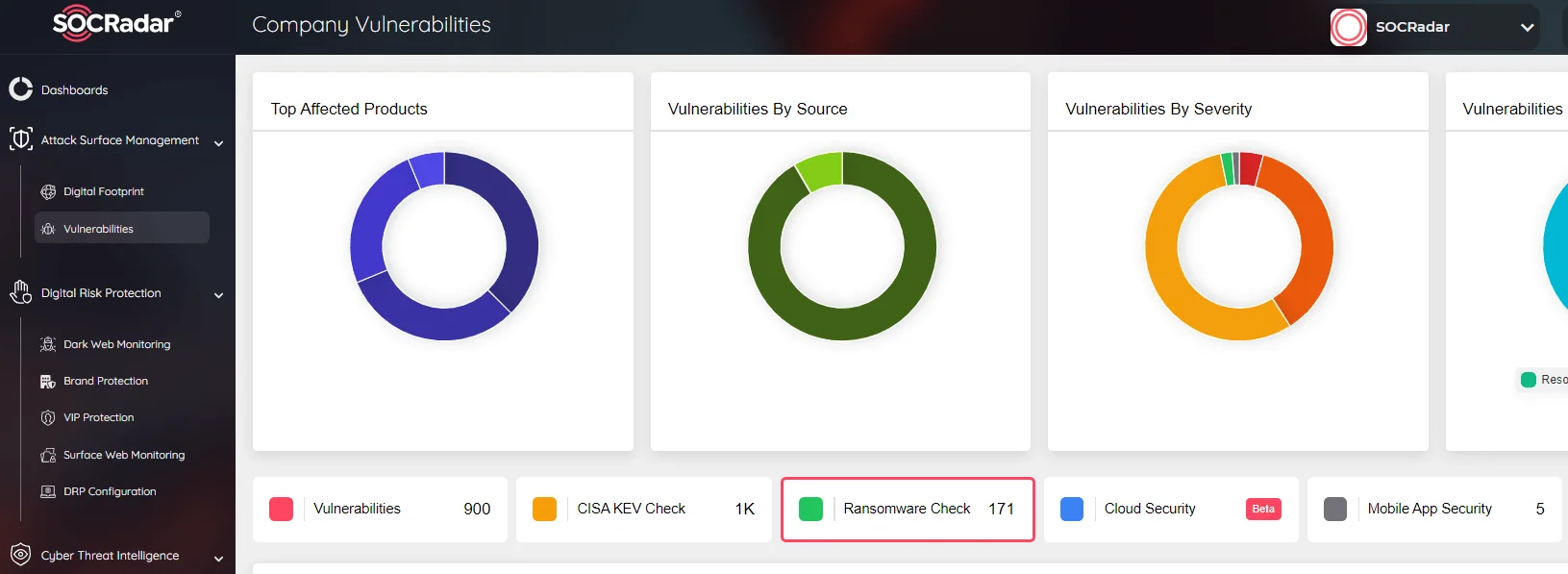
SOCRadar Attack Surface Management, Ransomware Check
SOCRadar’s Attack Surface Management includes a specialized Ransomware Check function designed to help organizations protect against ransomware attacks, including those orchestrated by sophisticated malware like Brain Cipher. Our platform empowers you to proactively monitor potential attack vectors, detect suspicious activities, and take preemptive actions to safeguard your digital assets.
Furthermore, by leveraging SOCRadar’s intelligence-driven solutions, you can gain insights into threat actors’ methods and vulnerabilities, enabling you to fortify your cybersecurity posture.
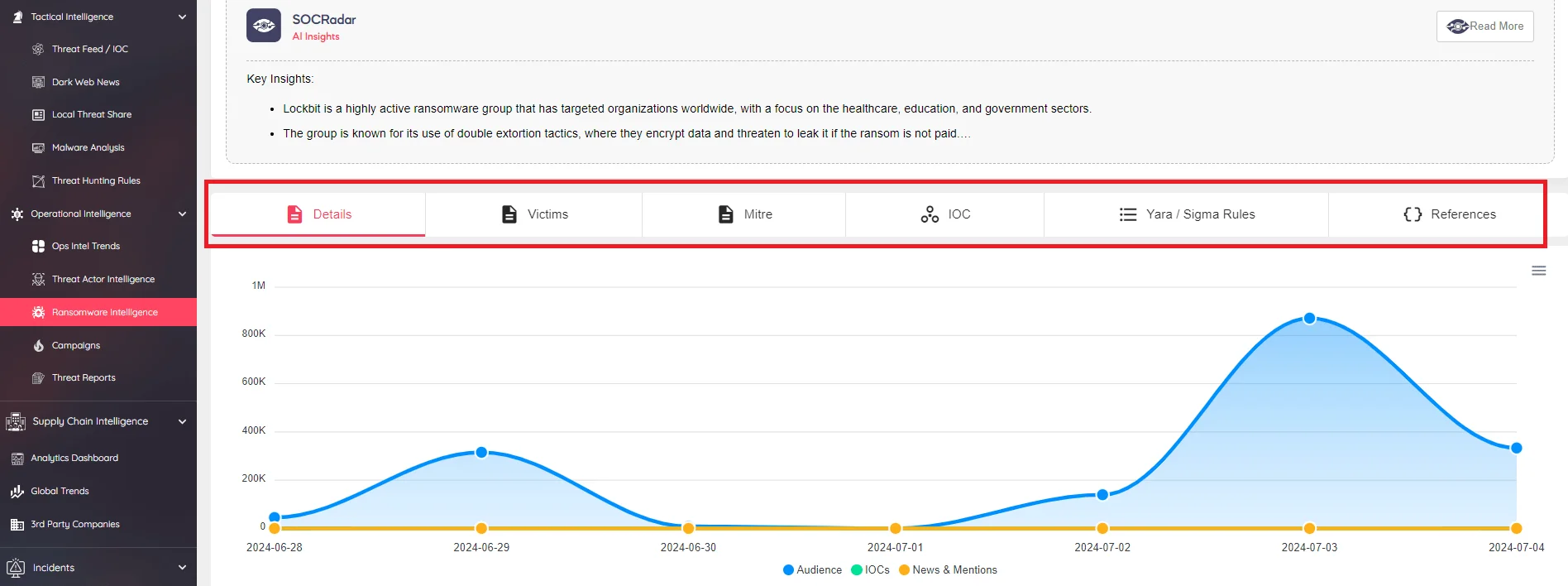
You can access resources such as YARA rules, IoCs, which will allow you to detect LockBit and derived samples, from the SOCRadar Ransomware Intelligence tab.
Our continuous monitoring and timely alerts ensure that you stay ahead of potential threats, allowing for swift responses and enhanced overall defense against ransomware and other cyber threats.
What Are the TTPs and IoCs for Brain Cipher?
In the table below, we have listed the TTPs that we consider important in the specific sample and the TTPs that are possible in possible future attacks.
| Tactic | Technique | Description |
| Initial Access | T1190 – Exploit Public-Facing Application | Brain Cipher may exploit vulnerabilities in public-facing applications to gain initial access. |
| Execution | T1059.001 – Command and Scripting Interpreter: PowerShell | Utilizes PowerShell scripts to execute malicious payloads. |
| Persistence | T1053.005 – Scheduled Task/Job: Scheduled Task | Creates scheduled tasks to maintain persistence on the infected system. |
| Privilege Escalation | T1068 – Exploitation for Privilege Escalation | Exploits vulnerabilities to escalate privileges within the system. |
| Defense Evasion | T1027 – Obfuscated Files or Information | Uses code obfuscation techniques to avoid detection by security tools. |
| T1112 – Modify Registry | Modifies registry keys to evade detection and maintain persistence. | |
| T1070.004 – Indicator Removal on Host: File Deletion | Deletes itself and other malicious files to avoid forensic analysis. | |
| Credential Access | T1555.003 – Credentials from Web Browsers | Attempts to harvest and steal credentials stored in web browsers. |
| Discovery | T1083 – File and Directory Discovery | Enumerates files and directories to identify target data for encryption. |
| Lateral Movement | T1021 – Remote Services | Uses remote services to move laterally within the network. |
| Collection | T1560.001 – Archive Collected Data: Archive via Utility | Collects and archives data before encryption. |
| Command and Control | T1090.003 – Proxy: Multi-hop Proxy | Uses multi-hop proxies, including Tor, for anonymized communication with command and control servers. |
| Exfiltration | T1048.002 – Exfiltration Over Alternative Protocol: Exfiltration Over Unencrypted/Obfuscated Non-C2 Protocol | Possibly, exfiltrated data using alternative protocols to avoid detection. |
| Impact | T1486 – Data Encrypted for Impact | Encrypts files on the system to prevent access and demands a ransom for decryption. |
SHA-256 Hashes for Brain Cipher
- eb82946fa0de261e92f8f60aa878c9fef9ebb34fdababa66995403b110118b12
- 0ed5729655b3f09c29878e1cc10de55e0cbfae7ac344f574d471827c256cf086
- 6e07da23603fbe5b26755df5b8fec19cadf1f7001b1558ea4f12e20271263417
URLs of Brain Cipher
- Communication for victims:
http://mybmtbgd7aprdnw2ekxht5qap5daam2wch25coqerrq2zdioanob34ad[.]onion/ - Data Leak Site:
http://vkvsgl7lhipjirmz6j5ubp3w3bwvxgcdbpi3fsbqngfynetqtw4w5hyd[.]onion/
Communication Channels in Ransom Notes
- E-mail:
[email protected] - Tox:
BEBA1CBBD4C1D6DFCB788024174FDE6AE6137C7835FBF997CB178DB5697AE574FB6055381095 - BTC:
bc1qqjzd8jrcvz5tl895uvgy6ph83g7sh06uzu6vn8