Dark Web Profile: Dispossessor Ransomware
[Update] August 13, 2024: “Repossessed: An FBI Operation”
Dispossessor has recently emerged in the ransomware landscape, and it is especially notable for its similarities to the notorious LockBit group. Following an extensive crackdown by global law enforcement agencies, which led to the seizure of LockBit’s primary domains, Dispossessor quickly surfaced, mimicking the structure and content of LockBit.

Dispossessor’s logo
Who is Dispossessor Ransomware
The name “Dispossessor” could be linked to Ursula K. Le Guin’s novel “The Dispossessed,” which explores themes of anarchism, resource scarcity, and socio-political upheaval. The novel presents a dichotomy between a society devoid of personal property and one rich in resources but rife with inequality and competition.
Such references are common among ransomware and extortion groups that engage in million-dollar thefts and extortions but still see themselves on the morally high ground.
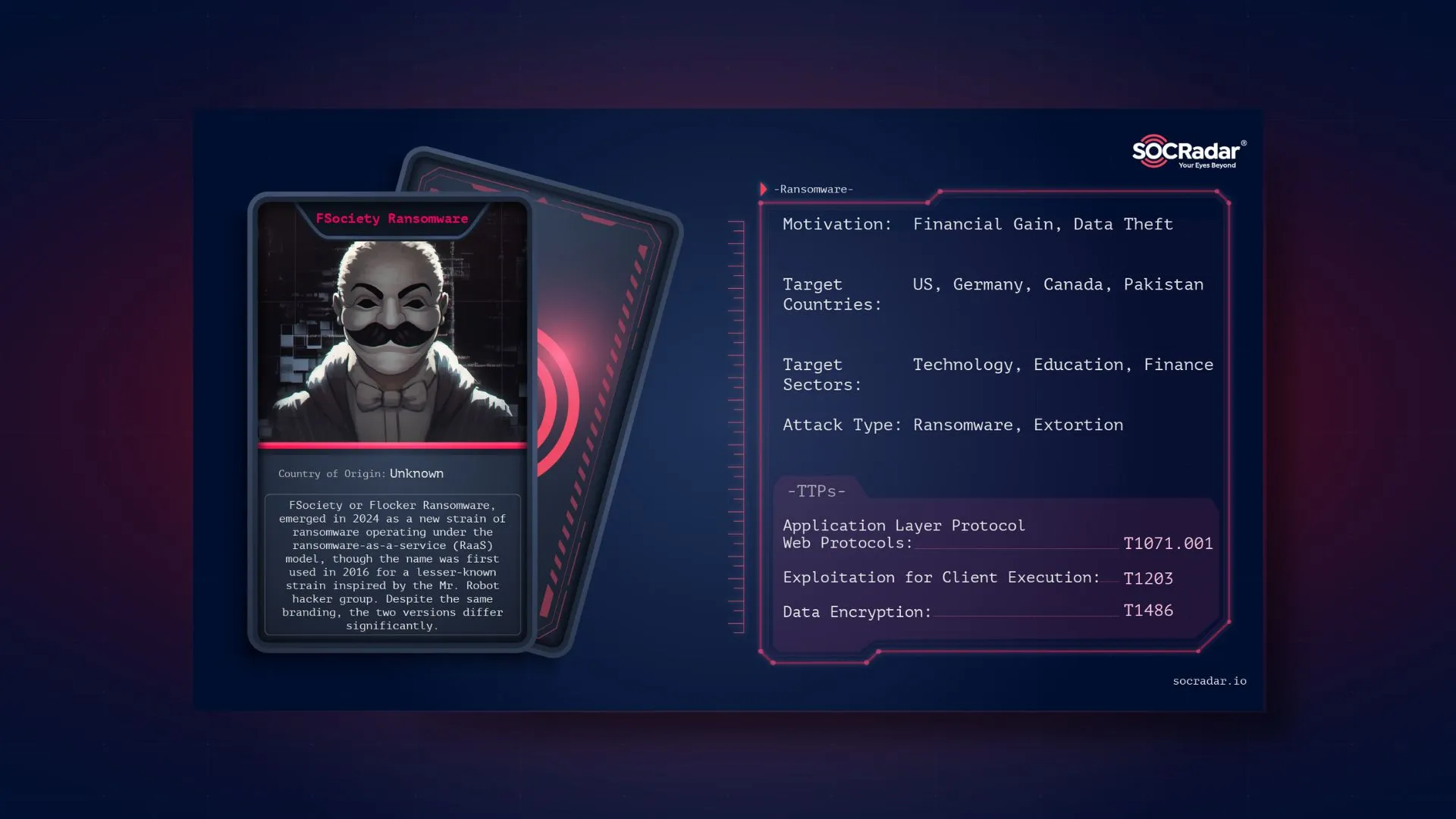
In February 2024, Dispossessor made a bold entrance into the dark web, announcing the availability of previously leaked data for download and potential sale. These announcements appeared across multiple forums and markets, including BreachForums and XSS as stated by SentinelOne.
Post about Dispossessor in a hacker forum
The timing was particularly notable, as it followed closely after Operation Cronos, a coordinated effort led by the FBI to shut down LockBit’s operations. This operation saw multiple domains owned by LockBit seized, disabling access to their affiliate panel and other critical infrastructure.
Dispossessor’s website bears a striking resemblance to the original LockBit site. The layout, color scheme, and typefaces are nearly identical, suggesting either a rebranding effort by the same operators or a new group leveraging LockBit’s infrastructure. Content analysis reveals that many posts from the original LockBit site have been mirrored on Dispossessor’s platform on their first days, maintaining the exact publication dates and details.
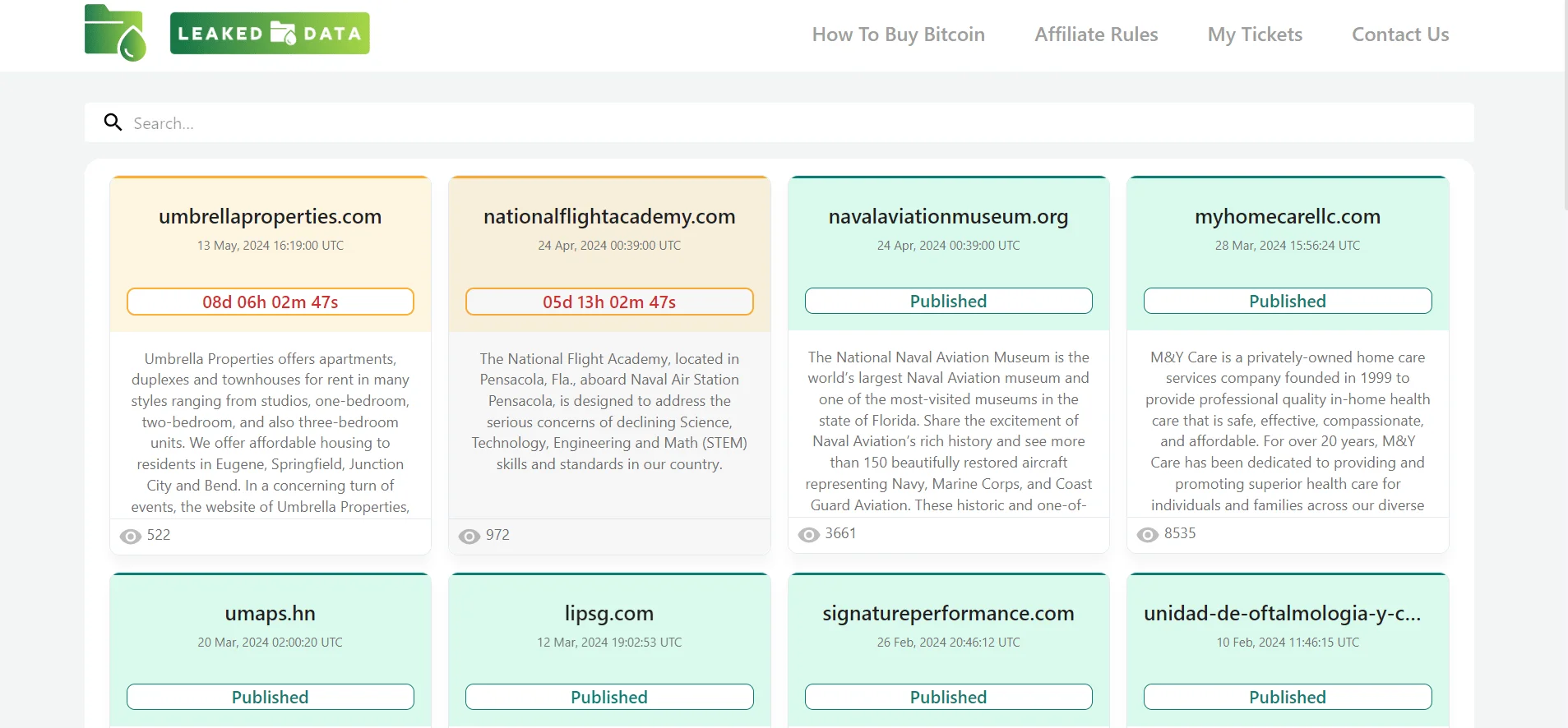
Dashboard of Dispossessor’s surface web leak site
Users on the hacking forums also mentioned a new site named Dispossessor, noting its similarity to the original LockBit site.
Operational Tactics
Dispossessor follows the Ransomware-as-a-Service (RaaS) model, similar to LockBit. This approach allows RaaS groups to distribute ransomware through affiliates, who then execute attacks on various targets. The decentralized nature of this model makes it challenging for law enforcement to completely dismantle their operations.
However, Dispossessor does not appear to possess ransomware capabilities; instead, it functions more accurately as a data broker. Since no instances of their ransomware have been observed, it is clear that they are primarily publishing data leaks from other groups, including those that are now defunct or have been shut down. This makes them opportunistic threat actors.
As firstly stated by @ransomfeednews in X, “We have noticed that there is a lot of talk about the alleged new ransomware group #dispossessor; we did some checking and analyzed the situation. In light of everything, from our point of view it is not #ransomware, but a group of scoundrels trying to monetize (on nothing) using the claims of other groups.”
A similar situation was observed with Ransomhub concerning the Change Healthcare data. Dispossessor relies on affiliates from other ransomware groups who have already acquired or stolen data. However, their latest victim portfolio has diversified from those targeted by LockBit or other groups, and they are actively seeking “red teamers” on hacker forums to collaborate with. Therefore, it could be expected that something may change.
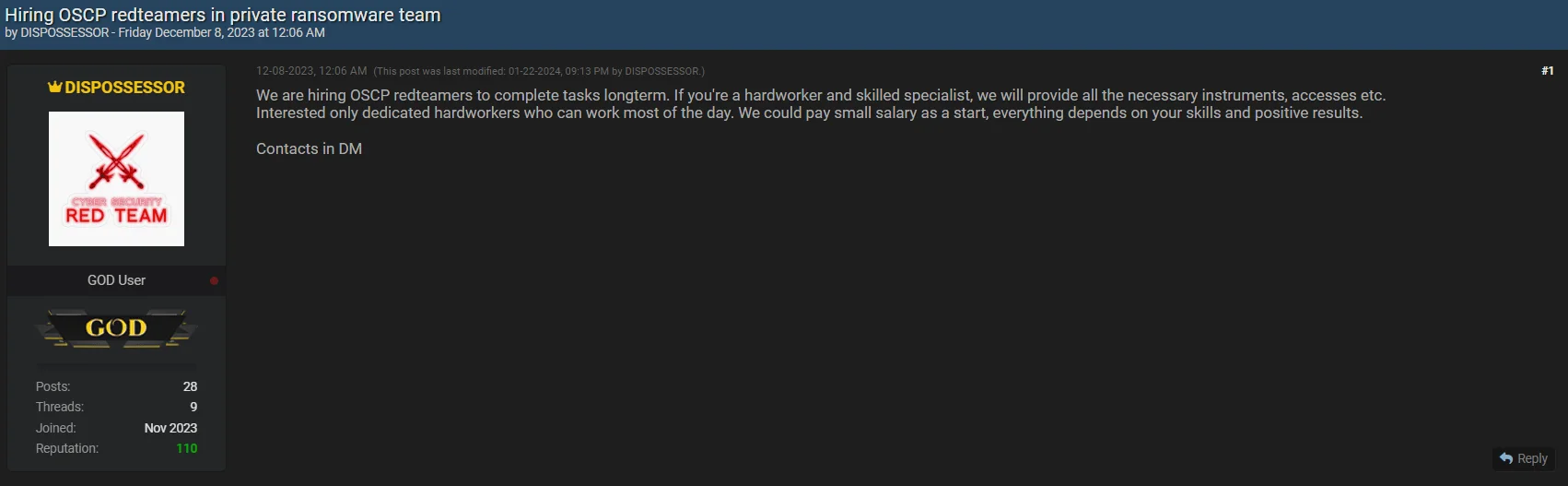
Group was looking for red teamers in late 2023
When we look at the number of victims, we can see that it contains 17 pages and around 300 company names, but the majority of them consist of victims previously listed in groups such as LockBit, Cl0p or Snatch.
According to their data leak site, Dispossessor’s affiliate program is notably inclusive, welcoming participants regardless of their location, language, age, or religion. The program prioritizes cohesive and experienced teams of “pen testers” and access providers -initial access brokers-offering a transparent process where affiliates can control communication with victims.
Affiliates using Dispossessor’s platform have access to a comprehensive toolkit designed to maximize the impact of their attacks. Key features include an admin panel on the Tor network, secure communication channels, automatic decryption tools, and StealBit stealer, which enables the theft of valuable data. The platform also supports various operating systems and architectures, including Windows, ESXi, and multiple Linux distributions.
Dispossessor’s Affiliate Program Rules
Dispossessor’s rules on their data leak site outline a structured affiliate program. Affiliates are expected to actively work with the software package provided by Dispossessor and adhere to strict guidelines to maintain operational security. Key rules include:
- Affiliates must not share access to the panel with others.
- Agreements made in chats before payment must be fulfilled.
- Valuable information must be downloaded from every attacked company.
- It is prohibited to attack certain critical infrastructure, such as nuclear power plants and medical institutions where data loss could lead to death.
Dispossessor’s emphasis on operational security extends to a deposit requirement for new affiliates. Prospective members must deposit 1 Bitcoin, which serves as an advance payment for future ransom shares. This requirement is intended to weed out insecure novices, law enforcement agents, journalists, and competitors.
Repossessed: An FBI Operation
The FBI recently scored a big win against the Dispossessor ransomware group by disrupting their operations and seizing several of their servers. This group had been on the FBI’s radar for months, and this latest move is part of a larger effort to take down their network and bring those involved to justice.
The FBI explained that this disruption came after a long investigation focused on the servers Dispossessor used to launch their attacks. By taking control of these servers, law enforcement has seriously weakened the group’s ability to lock up and steal data from their victims. For now, this should put a dent in Dispossessor’s operations.

Seizure announcement on the Dispossessor’s leak site
This action is just one piece of a broader strategy to fight ransomware, involving teamwork between international partners and private companies. The takedown sends a clear message to cybercriminals and shows the power of working together to combat these threats.
That said, this might not be the end of Dispossessor. Ransomware groups are known for bouncing back, often with new tricks up their sleeves. So, it’s important for organizations to stay alert and keep strengthening their defenses against potential attacks.
Conclusion and Mitigation Strategies
Dispossessor’s emergence as a significant player in the cyber threat landscape, closely following the crackdown on LockBit, highlights the dynamic and adaptive nature of cybercriminal activities. Their operational tactics, mimicking the Ransomware-as-a-Service model while primarily functioning as data brokers, present a unique challenge for cybersecurity experts and law enforcement agencies.
Therefore, focusing on general ransomware defense strategies with data protection in mind is crucial for robust cybersecurity resilience.
- Regular Data Backup: Implement a robust backup strategy to regularly back up critical data. This ensures data availability for recovery in the event of a ransomware attack.
- Security Awareness Training: Educate employees about ransomware threats and cybersecurity best practices to reduce the risk of falling victim to malicious attacks.
- Patch and Update Management: Keep systems updated with the latest security patches to address vulnerabilities exploited by ransomware.
- Network Segmentation: Segment networks to separate critical systems and data from less secure areas, limiting the impact of ransomware infections.
- Access Control: Restrict user privileges to minimize the attack surface and prevent the spread of ransomware within the network.
- Email and Web Security: Deploy advanced filtering solutions to detect and block malicious attachments, links, and phishing attempts delivering ransomware payloads.
- Endpoint Protection: Use antivirus software, IDS, and EDR tools to detect and mitigate ransomware threats on endpoints.
- Incident Response Plan: Develop and test a response plan specifically for ransomware attacks, including procedures for identifying, containing, and recovering from incidents.
- Regular Security Audits: Conduct audits and vulnerability assessments to identify and remediate security gaps that ransomware attackers could exploit.
- Backup Testing: Regularly test backup data integrity and store backups securely to prevent unauthorized access.
SOCRadar for Data Protection
SOCRadar provides proactive threat monitoring and intelligence solutions to strengthen your organization’s security posture against ransomware attacks. With our platform, you can proactively search for threat actors, gain insights into their tactics and vulnerabilities, and take preemptive measures to protect your assets.
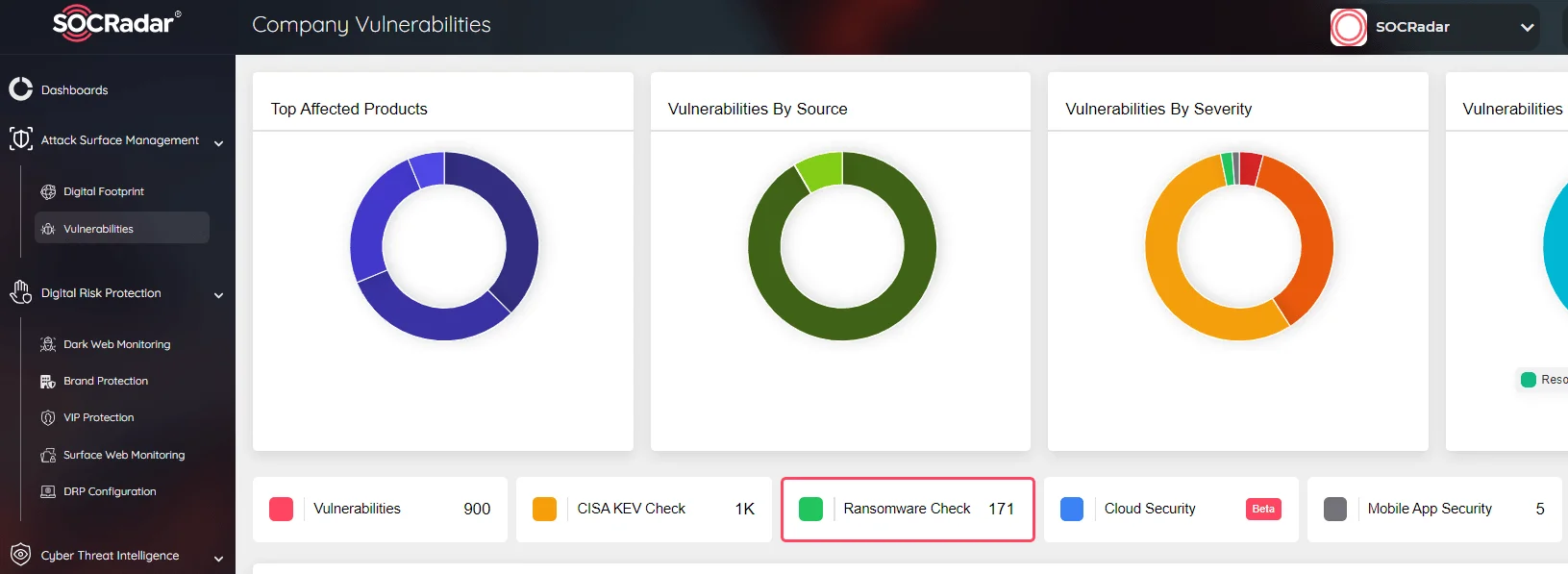
SOCRadar Attack Surface Management, Ransomware Check
Our Attack Surface Management module offers continuous monitoring of potential attack vectors, ensuring timely alerts about suspicious activity. This proactive approach enables swift responses to threats, enhancing overall cybersecurity defenses. Integrating SOCRadar into your cybersecurity framework adds an extra layer of protection against ransomware and other threats.