Dark Web Profile: DragonForce Ransomware
DragonForce Ransomware has emerged as an intriguing adversary. Known for its prominent targets and unusual ways of communication, it has quickly gained notoriety among cybersecurity experts and victims alike. This post delves into the origins, operations, and distinctive features of the DragonForce Ransomware, shedding light on the menacing threats in the digital world today.

Depiction of DragonForce Ransomware, Created by Bing AI
Who is DragonForce Ransomware
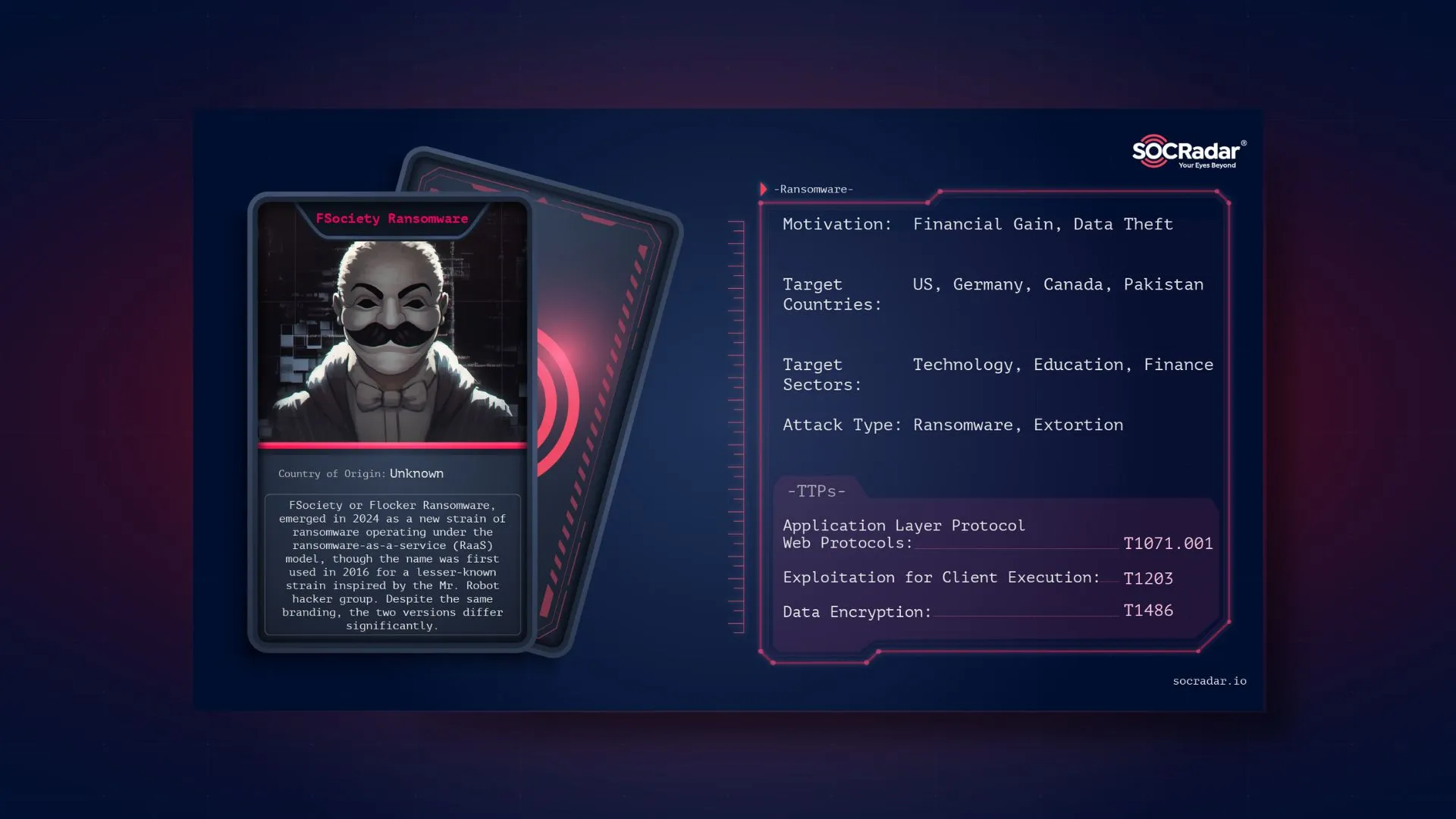
DragonForce Ransomware was first identified in December, 2023 and has since been linked to a series of high-profile attacks. The group behind DragonForce, allegedly connected to the notorious LockBit ransomware gang, has demonstrated capabilities in penetrating networks and encrypting data. Their operations reflect a blend of traditional ransomware tactics and innovative(?) strategies designed to maximize financial gain.

DragonForce Ransomware’s Logo
While LockBit was dethroned as the most dangerous ransomware due to the operation of the security forces, it could be thought that hundreds of affiliates, ransomware strains, and knowledge would flow somewhere. Therefore, a case involving DragonForce also raised the possibility that it might be related to LockBit.
As Graham Cluley reported, in mid-March 2024, the government of Palau experienced a ransomware attack that incapacitated their computers. Unusually, ransom notes from two different hacking groups, LockBit and DragonForce, were discovered.
However, this indicated that they were using the leaked LockBit builder rather than having a connection with LockBit. The double ransom note can be interpreted as an error due to technical inadequacies.
Some members of the cybersecurity community have associated the ransomware with DragonForce Malaysia, a hacking group and forum based in Malaysia. However, these claims were denied on DragonForce Malaysia’s Telegram channel.
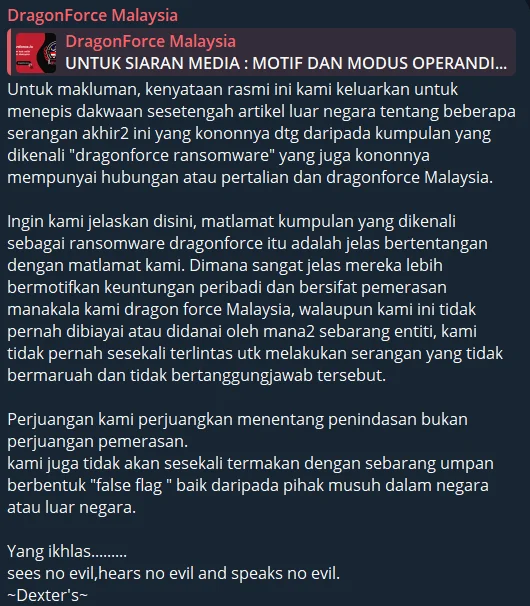
DragonForce Malaysia’s latest Telegram post
In short, They emphasized that their goals are entirely different, as they oppose oppression and do not engage in extortion for personal gain. They also stated that they have never conducted dishonorable or irresponsible attacks and will not fall for any “false flag” tactics from domestic or foreign adversaries.
So, who is DragonForce? We don’t know, maybe we should ask.
DragonForce Ransomware’s DLS, contact form
Modus Operandi of DragonForce Ransomware
As we stated above, DragonForce has been seen utilizing a leaked ransomware builder from the LockBit ransomware group. The Ransomware group aims to extort its victims. The threat actor generally uses a double extortion strategy, where they lock victims out of their infected machines and exfiltrate data before encrypting it. If the victims do not comply with their demands, the threat actor threatens to release the data on the dark web.
LockBit 3.0, also known as LockBit Black, is the third version of a notorious ransomware family. Created by the LockBit group, it was infamously leaked in September 2022 by a disgruntled developer. This leak has allowed various cybercriminal factions, including the newly emerged DragonForce ransomware group, to exploit its capabilities for launching sophisticated attacks.
Of course, the question arises whether the operation of the security forces may negatively affect the success of leaked builds, but the group continues to announce new victims.
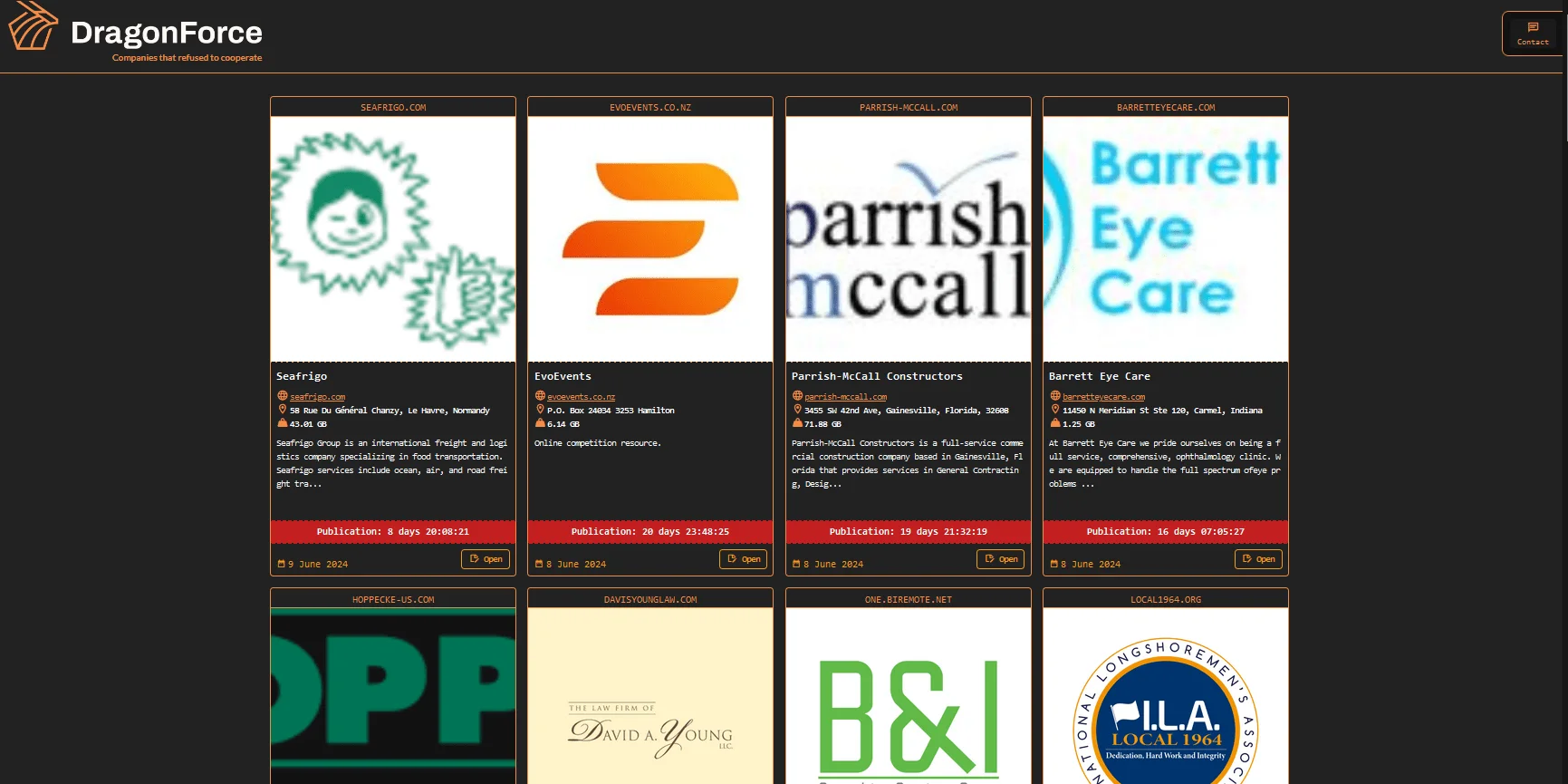
Main page of DragonForce Ransomware’s data leak site, latest victim listed on June 9, 2024
Therefore, these types of ransomware enable threat actors to effortlessly create customized ransomware, making it increasingly difficult to stop every related malicious activity with one single operation.
The initial infection vector often involves phishing emails or exploiting vulnerabilities in Remote Desktop Protocols (RDP) and Virtual Private Network (VPN) solutions. Once inside the network, DragonForce may rapidly spread, leveraging encryption algorithms to lock down critical systems and data.
Extortion with a Phone Call
An incident involving the ransomware gang highlights the sometimes comedic side of cyber extortion.
As TechCrunch stated, in an attempt to coerce a company into paying a ransom, a hacker called the front desk, only to be transferred multiple times and finally connected to an unperturbed HR representative named Beth. Unfazed by the hacker’s threats, Beth remained calm, asked about the legality of recording calls, and ultimately dismissed the hacker with a polite request for a callback number. The hacker’s frustration was evident as his intimidation tactics fell flat.
DragonForce released the recording on their dark web site, intending to pressure the company, but instead, it turned into a comedic display of a failed extortion attempt. Beth’s calm and collected responses highlighted the ineffectiveness of the hacker’s threats, making the incident a humorous reminder that sometimes, the best defense against cybercriminals is a mix of legal awareness and unshakeable composure.
Victimology
The group’s first known ransomware attack targeted the Ohio Lottery. In this incident, the group claimed to have stolen over 600 GB of data, including three million records with names, email addresses, social security numbers, and other sensitive information.
There are currently 63 victims listed on the group’s Data Leak Site, and the published victims are listed on the home page along with the victims with ransom payment deadlines.
Latest alleged victim of DragonForce Ransomware
There is general information about the victims, the size of the data obtained, and a countdown for publication.
An example of a victim with alleged publicated files
They host the leaked data on their own website and make it available for public download. Furthermore, they seem to act without limits in both the targeted sectors and countries. Of course, the US remains the most targeted country.
A Notable Incident
One of the most significant incidents attributed to DragonForce involved the attack on the Aussizz Group, a leading educational and migration consultancy. The ransomware gang claimed responsibility for exfiltrating and encrypting nearly 300GB of sensitive data, showcasing their ability to target and impact large organizations with significant data stores.
Impact and Response
A large group or not, it uses leaked builders instead of its own strains, but it is still a criminal organization and ransomware groups should always be taken seriously. The impact of DragonForce Ransomware extends beyond financial losses. The operational disruptions and potential data breaches cause significant reputational damage and legal complications for affected organizations. Cybersecurity firms and law enforcement agencies worldwide are actively working to mitigate the threat posed by DragonForce, employing advanced detection and response strategies to protect potential targets.
Defending Against DragonForce Ransomware
As cyber threats continue to evolve, organizations must adopt a multifaceted approach to cybersecurity, especially in defending against ransomware attacks like DragonForce. Leveraging advanced security tools and implementing proactive strategies are imperative in fortifying digital defenses.
Robust Anti-Malware Solutions
Implementing advanced anti-malware software is essential in combating DragonForce ransomware. These tools use signature-based detection, heuristic analysis, and machine learning algorithms to identify and block known and emerging ransomware variants. Coupled with Endpoint Detection and Response (EDR) solutions, organizations can enhance real-time threat detection and response capabilities. SOCRadar Attack Surface Management has a Ransomware Check function.
Regular Security Audits and Vulnerability Management
Conducting routine security audits and vulnerability assessments is critical to identifying and addressing potential security gaps within an organization’s infrastructure. By systematically evaluating network configurations, system settings, and application vulnerabilities, organizations can proactively remediate weaknesses exploited by DragonForce ransomware attackers.
Strong Authentication and Access Controls
Enforcing strong authentication mechanisms like Multi-Factor Authentication (MFA) and implementing stringent access controls significantly enhance user account security and mitigate the risk of unauthorized access. This adds an extra layer of protection against DragonForce ransomware attacks targeting user credentials.
Comprehensive Backup and Disaster Recovery Planning
Developing a robust Backup and Disaster Recovery (BDR) plan is essential in mitigating the impact of DragonForce ransomware attacks and ensuring business continuity. Regular backup schedules for critical data, both onsite and offsite, along with backup testing and data recovery drills, validate the effectiveness of the BDR plan and ensure timely restoration of operations in case of an attack.
Conclusion
Despite their somewhat novice tactics, DragonForce Ransomware still represents a significant threat due to its adaptability and intriguing attack and extortion methods. Organizations must remain vigilant and proactive in their cybersecurity efforts to defend against such advanced threats. By understanding the tactics and techniques employed by DragonForce, organizations can better prepare and protect themselves from this formidable ransomware.
How Can SOCRadar Help?
Understanding the tactics and strategies of ransomware groups like DragonForce is crucial for organizations looking to bolster their cybersecurity defenses. Implementing robust mitigation measures and staying vigilant are key steps in combating these threats effectively.
SOCRadar’s Attack Surface Management includes a specialized Ransomware Check function designed to help organizations protect against ransomware attacks, including those orchestrated by groups like DragonForce. Our platform empowers you to proactively monitor potential attack vectors, detect suspicious activities, and take preemptive actions to safeguard your digital assets.
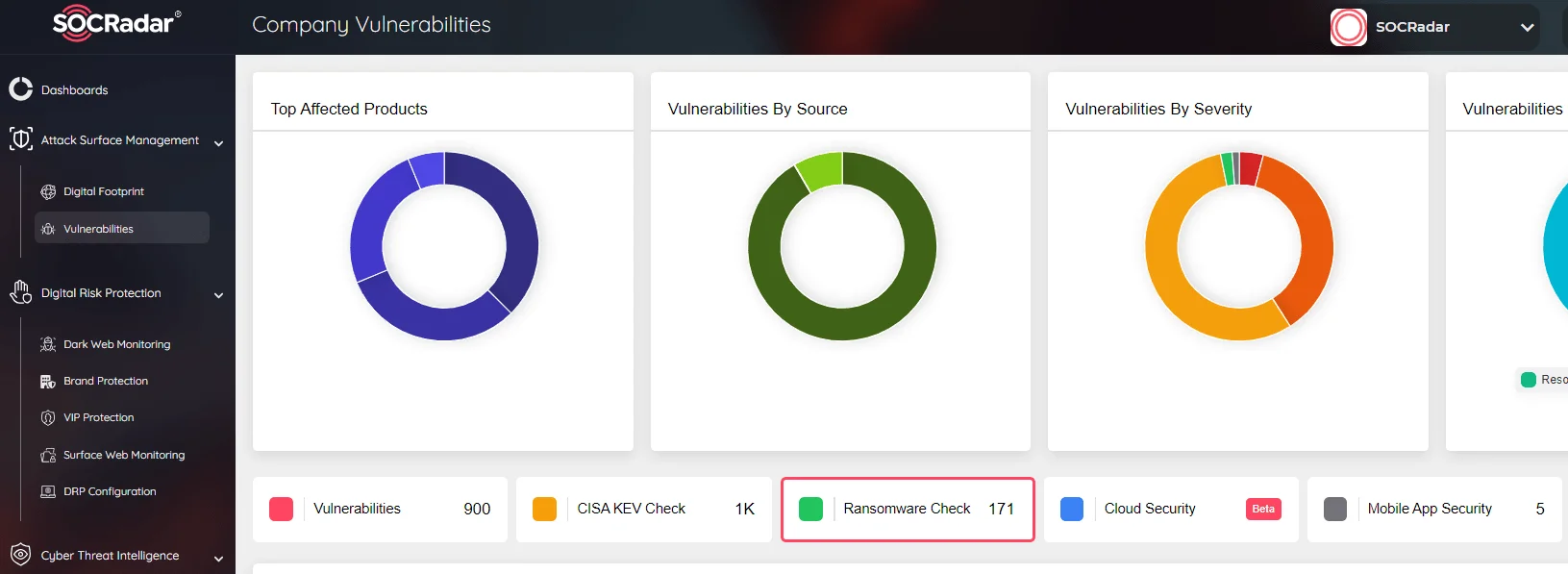
SOCRadar Attack Surface Management has a Ransomware Check function
By leveraging SOCRadar’s intelligence-driven solutions, you can gain insights into threat actors’ methods and vulnerabilities, enabling you to fortify your cybersecurity posture. Our continuous monitoring and timely alerts ensure that you stay ahead of potential threats, allowing for swift responses and enhanced overall defense against ransomware and other cyber threats.
Integrating SOCRadar into your cybersecurity framework adds an additional layer of protection, helping you mitigate the risks posed by ransomware groups like DragonForce and ensuring the resilience of your organization’s security defenses.