Excel’s Blind Spot: The Strategic Deployment of Agent Tesla Malware by Cyberattackers
In the ever-evolving landscape of cyber threats, a notable trend has emerged: the exploitation of a longstanding Microsoft Office vulnerability to disseminate a particularly insidious strain of malware, Agent Tesla. This malware, a combination of a Remote Access Trojan (RAT) and an information stealer, capitalizes on an old vulnerability in Microsoft Excel, CVE-2017-11882, to infiltrate systems globally.

The Persistent CVE-2017-11882 Vulnerability
Often referred as the “Microsoft Office Memory Corruption Vulnerability,” CVE-2017-11882 allows attackers to execute arbitrary code on a victim’s machine due to improper handling of objects in memory.
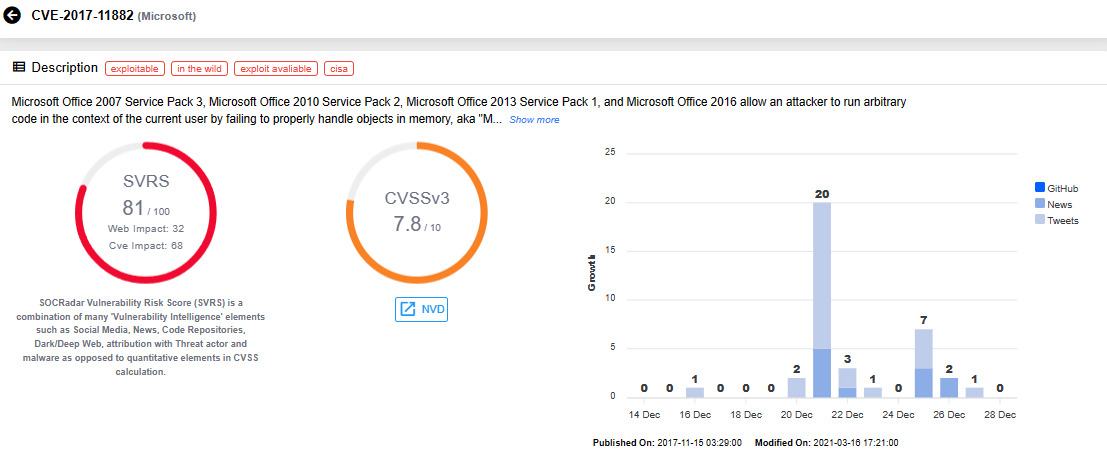
Despite being patched in 2017, CVE-2017-11882 remains a favorite among cybercriminals due to its effectiveness and the prevalence of unpatched systems. Attackers use decoy Excel documents in invoice-themed emails to lure users into activating the malware.
Agent Tesla: A Sophisticated Malware
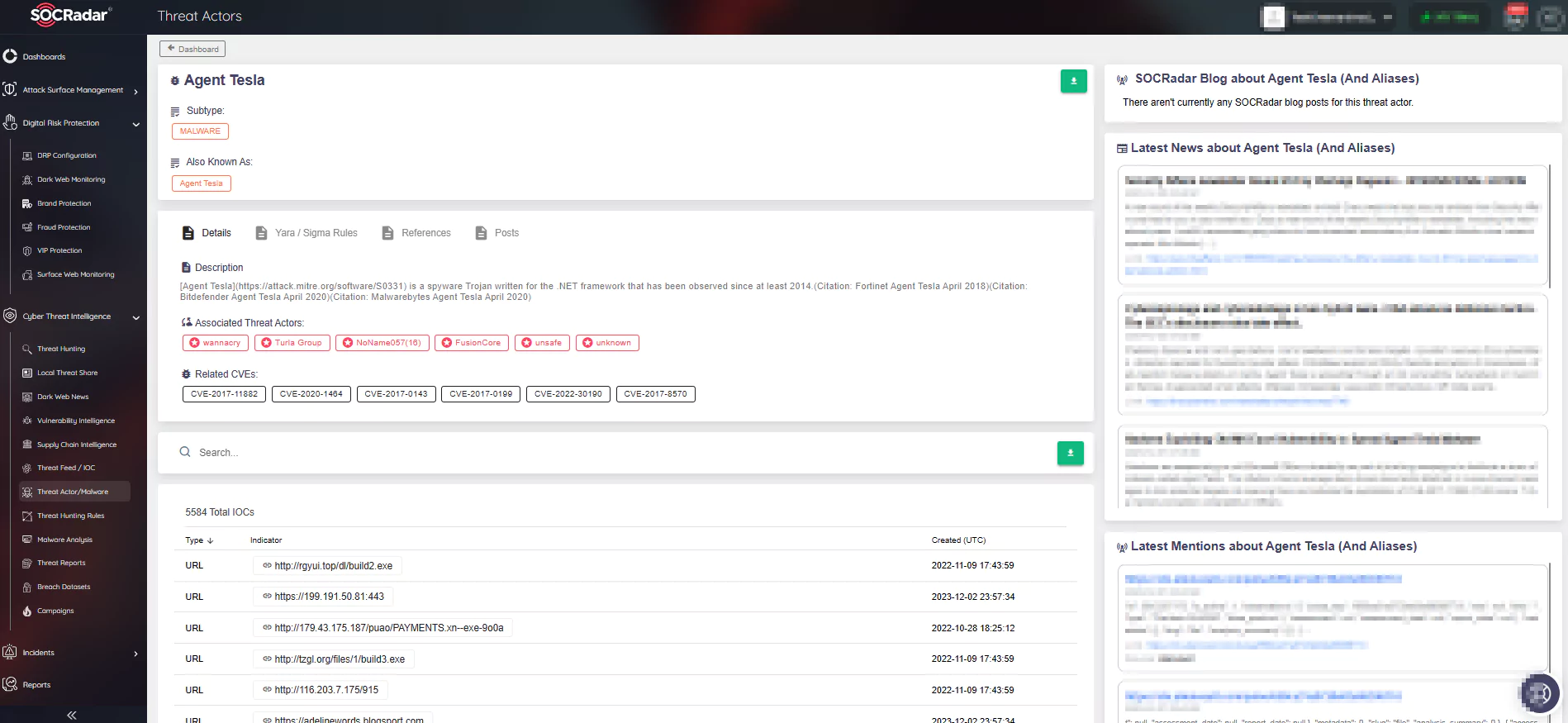
First observed in 2014, Agent Tesla is built on the .NET framework. Its capabilities include account information theft, data encryption for exfiltration, browser session hijacking, keylogging, and capturing screenshots and video.
Additionally, its use of various communication protocols like HTTP and SMTP for Command and Control (C2) communications makes Agent Tesla particularly dangerous.
The campaigns using Agent Tesla have been indiscriminate, affecting various sectors and countries worldwide, posing significant risks to individual privacy and organizational cybersecurity.
Mitigating the Agent Tesla Threat
Several strategies have been proposed to counter Agent Tesla:
- Email Filtering and Employee Training
- Regular Software Updates and Patch Management
- Advanced Threat Detection
- Comprehensive Antivirus and Anti-Malware Solutions
- Network Segmentation and Access Control
- Data Backup and Effective Recovery Plans
- Multi-Factor Authentication (MFA)
- Regular Monitoring of Access Logs
- Updating Corporate Security Policies
- Business Continuity Planning
Remediation Strategies
Upon detecting an Agent Tesla infection, crucial steps include isolating infected systems, malware removal and system recovery, password resets and system updates, forensic analysis, reinforcing security policies and training, continuous network monitoring, and incident reporting and collaboration.
SOCRadar’s Role in Combating Agent Tesla
SOCRadar’s XTI (Extended Threat Intelligence) platform provides comprehensive monitoring and alerting services. With modules like Attack Surface Management (ASM) and Cyber Threat Intelligence, the platform can detect signs of malware activity, such as the Agent Tesla malware, including its unique communication patterns and IOCs. SOCRadar enables organizations to proactively identify potential breaches.
Conclusion: The Need for Vigilance and Proactivity
The persistent use of CVE-2017-11882 for spreading Agent Tesla malware underscores the critical need for heightened cybersecurity measures. Organizations must remain vigilant against sophisticated phishing campaigns, consistently update software against the risk of vulnerabilities, and deploy advanced threat detection strategies.
Employing SOCRadar’s comprehensive suite of tools can significantly bolster defense against sophisticated tactics used by Agent Tesla operators. A comprehensive approach, combining technology, awareness, and robust security protocols, is essential to safeguard against these sophisticated and ever-evolving cyber threats.
Analyzing the Agent Tesla Threat
- Exploitation of CVE-2017-11882: The continued use of this vulnerability indicates a gap in software update adoption and emphasizes the need for regular patch management.
- Capabilities of Agent Tesla: Its diverse communication protocols and stealthy operations highlight the advanced nature of modern cyber threats.
- Global Impact: The widespread impact of Agent Tesla campaigns calls for international cooperation in cybersecurity.
- Proactive Mitigation: A holistic approach, including employee training and continuous monitoring, is vital.
- Remediation Strategies: Immediate isolation and removal of threats, followed by system recovery, are crucial in minimizing impact.
- Conclusion: Continuous vigilance and proactivity are essential in cybersecurity, integrating technological solutions with employee education to create a resilient defense. The use of specialized cyber intelligence platforms like SOCRadar XTI can bolster cyber defense.
You can find details about Excel’s Blind Spot: Hackers’ Strategy to Spread Agent Tesla Malware campaign on the SOCRadar Campaigns page.