RedAlert Ransomware Targets Windows and Linux VMware ESXi Servers
RedAlert is a new ransomware operation aiming to encrypt Windows and Linux VMWare ESXi servers on corporate networks using the NTRUEncrypt public-key encryption algorithm. The ransomware is named after a string in the ransom text, but the threat actors internally refer to it as N13V, which is the original name.
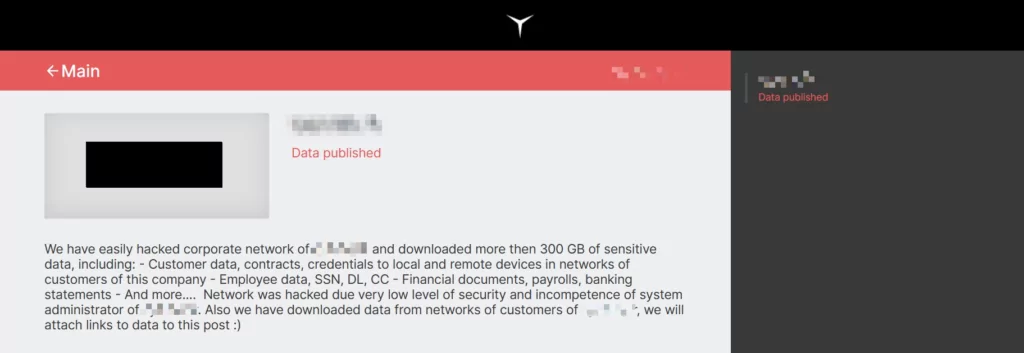
A new victim was listed on RedAlert’s data leak site, which is how MalwareHunterTeam revealed this new operation.
RedAlert Attack Scenario
RedAlert, like other ransomware, can spread via RDP configuration hacking, malicious spam emails, botnets, exploits, malicious ads, web injections, fake updates, and installers. Regardless of the situation, RedAlert can be distributed globally, but for now, its current target seems to be English-speaking users.
Before starting encryption, virtual machines can be shut down using command options in RedAlert’s Linux encryptor. A list of command options is shown below:
- -wStops running VMs by calling an esxcli command:
esxcli –formatter=csv –format-param=fields==”WorldID,DisplayName” vm process list | tail -n +2 | awk -F $’,’ ‘{system(“esxcli vm process kill –type=force –world-id=” $1)}’
- -p Path (Encrypts files in a directory)
- -f File (Encrypts a file)
- -r Recursive (Used with -p)
- -t Show encryption time
- -n Search without file encryption (File info)
- -x Debug Tests (Asymmetric cryptography performance tests)
- -h List of command options
After stealing data and encrypting all files, they demand a ransom in Monero (XMR). For double extortion, RedAlert threatens the victims to publish the stolen data on their leak page that anyone can download, which is named Board of Shame, if they don’t get in contact in 72 hours.
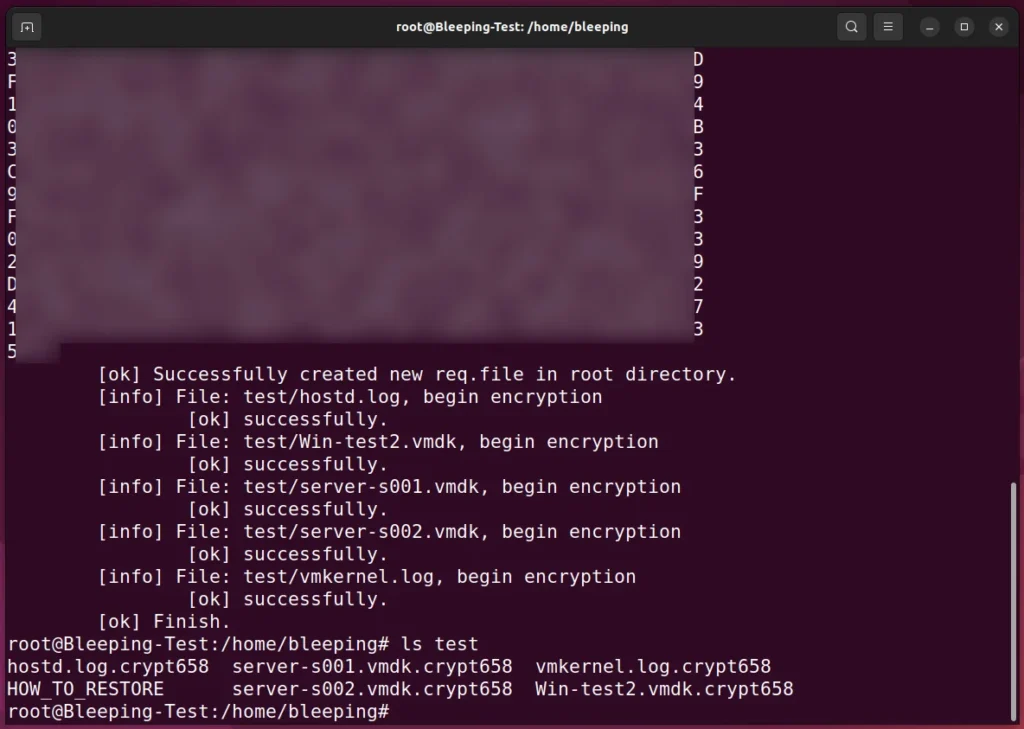
The ransomware will also create a custom ransom note named HOW_TO_RESTORE in each folder, which includes a description of the stolen data as well as a link to a unique TOR ransom payment site for the victim.
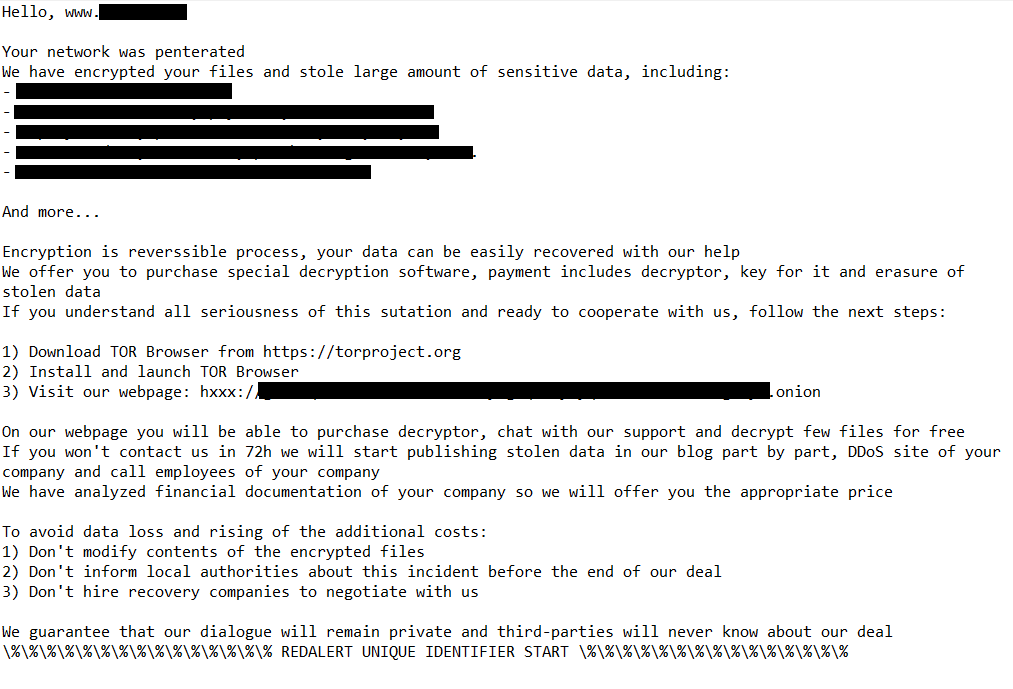
The Tor payment site, like other ransomware operation sites, displays the ransom demand and allows threat actors to negotiate.
However, RedAlert/N13V exclusively takes Monero cryptocurrency (XMR) as payment, which is uncommon in US cryptocurrency exchanges due to its private nature.
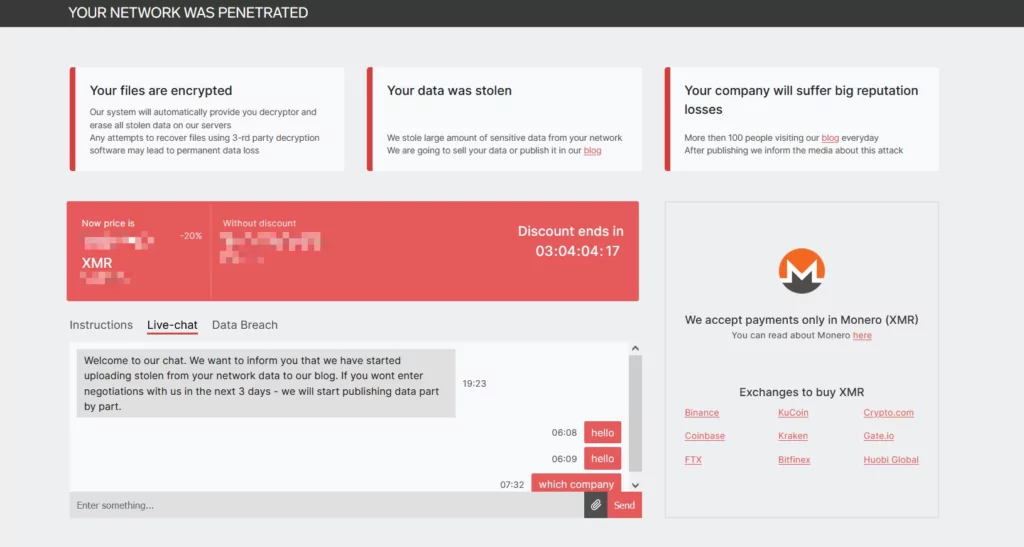
The payment site contains secret components demonstrating the existence of Windows decryptors even though only a Linux encryptor has been discovered.
Encryption Method
The ransomware uses the NTRUEncrypt public-key encryption method to encrypt files. This algorithm supports several “Parameter Sets” that provide various levels of security. Compared to other asymmetric encryption methods like RSA, ElGamal, and elliptic curve cryptography, these processes are rapid because encryption and decryption use only simple polynomial multiplication. However, NTRUEncrypt has not yet undergone a comparable level of cryptographic analysis in deployed form.
The ‘-x’ command-line option of RedAlert/N13V is an intriguing feature because it performs ‘asymmetric cryptography performance testing’ utilizing these various NTRUEncrypt parameter sets. But it’s unknown whether there’s a way to force a specific parameter set during encryption or if the ransomware will choose a more effective one.
FiveHands is the only other known ransomware operation using this encryption method.
The ransomware will only encrypt files associated with VMware ESXi virtual machines, such as log files, swap files, virtual disks, and memory files, as their extensions are listed below.
- .log
- .vmdk
- .vmem
- .vswp
- .vmsn
These file formats would be encrypted by the ransomware in the sample BleepingComputer examined, and the file names of encrypted files would be appended with the.crypt658 extension.
RedAlert IoCs
MD5:
f2fa9a3ce883a7f5b43ba5c9ff7bdf75
SHA-1:
da6a7e9d39f6a9c802bbd1ce60909de2b6e2a2aa
SHA-256: 039e1765de1cdec65ad5e49266ab794f8e5642adb0bdeb78d8c0b77e8b34ae09
Vhash:
e8adfad3b48440fe2975b62ba923fced
SSDEEP:
6144:65LjX/bdHB/q496k3amhqGDbQdnm2ENgJF7v+YT:I/DdHB/ukSokFgSv+YT
TLSH:
T129846B0FFFA1CE5BC49943B188AF87667738D07CA7999723335991346C077E89E06A44