Top 10 Free Vulnerability Intelligence Platforms
Cyber threats emerge every day, and keeping up with vulnerabilities is a constant challenge for security teams. Having reliable vulnerability intelligence is essential for identifying threats, prioritizing mitigation efforts, and strengthening defenses.
Organizations need timely access to CVE data, exploit trends, and risk assessments to proactively mitigate security risks. However, many advanced vulnerability intelligence solutions come with high subscription costs, which may not be feasible for all security teams, especially smaller organizations, independent researchers, and budget-conscious enterprises.
How Can Free Vulnerability Intelligence Tools Improve Your Security Posture?
For defenders seeking cost-effective solutions, a starting point for vulnerability tracking, or an additional resource to complement existing tools, free vulnerability intelligence platforms offer a much-needed alternative. By providing an accessible way to track vulnerabilities and assess risks, these platforms enable security teams to make informed decisions and proactively defend their organization..
This article explores the top 10 free vulnerability intelligence platforms, detailing their key features, benefits, and limitations. Whether you’re looking for real-time CVE tracking, Proof-of-Concept (PoC) exploit databases, or social media-driven risk insights, these tools can help strengthen your security posture without additional cost.
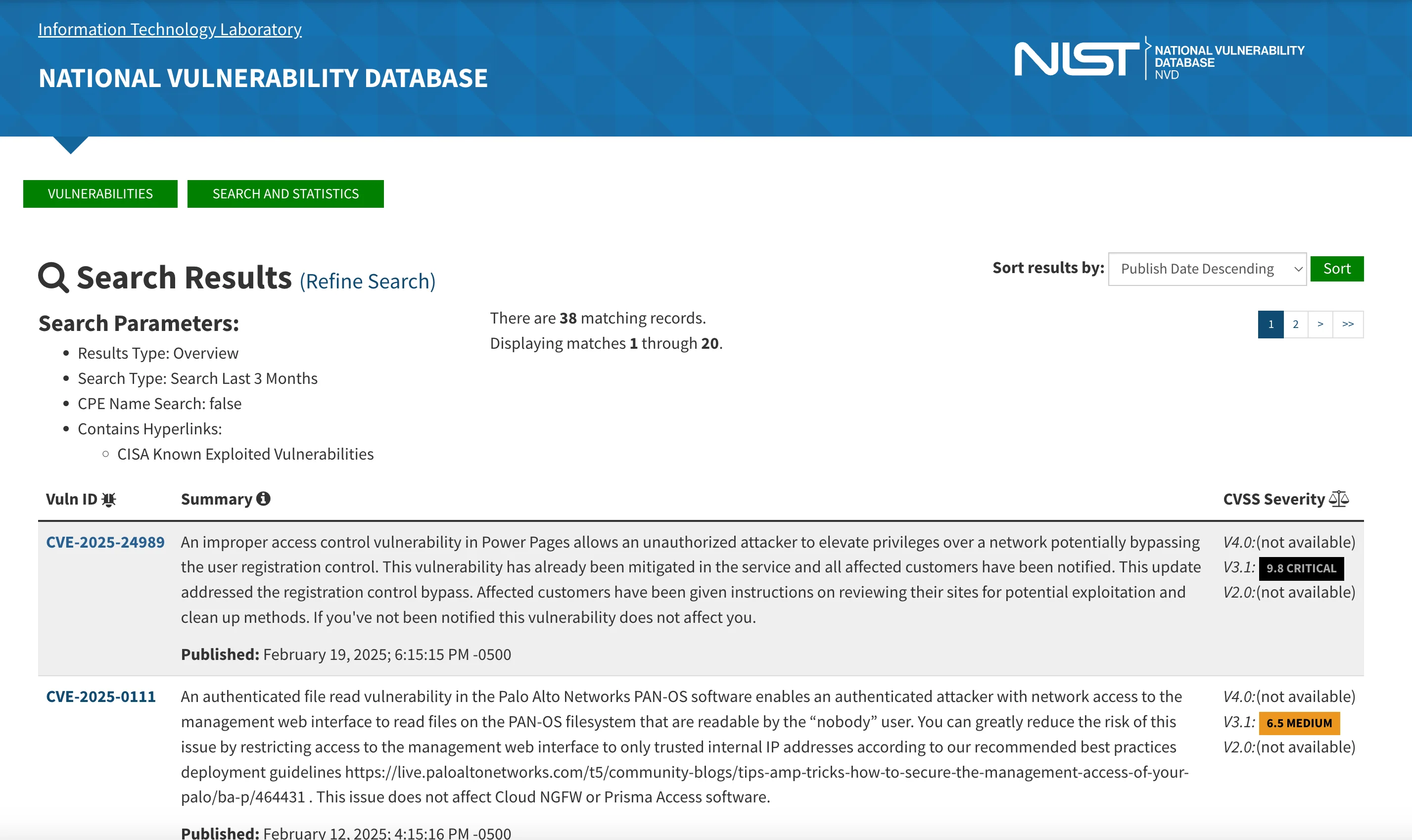
1. NVD (National Vulnerability Database)
The National Vulnerability Database (NVD) is the U.S. government’s central repository for standards-based vulnerability management data. Maintained by the National Institute of Standards and Technology (NIST), it plays a critical role in cybersecurity by offering structured and machine-readable vulnerability data.
Key Features
- SCAP Compliance – Uses the Security Content Automation Protocol (SCAP) to standardize security information, making it easier for automated vulnerability assessments.
- Automation Support – Enables automation in vulnerability management, security measurement, and compliance activities.
- Advanced Search & API Access – Provides powerful search capabilities with filters like CVE ID, CVSS score, vendor, and vulnerability type. Offers data feeds in XML, JSON, and CSV formats for integration with security tools.
Why Use It?
The NVD is a foundational resource for cybersecurity professionals, researchers, and security teams looking to automate and enhance their vulnerability management processes. As one of the most widely used free vulnerability intelligence platforms, its structured, standards-compliant data allows for seamless integration with security tools, making it indispensable for compliance and risk assessment.
Limitations
While the NVD is an extensive database, it primarily relies on public CVE disclosures. It may not always provide real-time exploitability details or insights beyond the structured vulnerability data.
Best For
- Security engineers integrating SCAP-compliant vulnerability automation into enterprise workflows.
- Compliance teams ensuring adherence to government and industry security baselines.
- Developers tracking vulnerabilities affecting widely used software libraries and infrastructure.
2. Feedly’s CVE Dashboard
The Feedly CVE Dashboard is an AI-powered vulnerability intelligence platform that aggregates real-time updates from thousands of Open-Source Intelligence (OSINT) sources. Designed for security professionals, it helps users collect, analyze, and share CVE reports more efficiently.
Key Features
- Continuous Intelligence – Continuously pulls in vulnerability intelligence from diverse sources to ensure up-to-date tracking.
- Personalized Dashboards – Users can tailor their dashboard based on their specific tech stack and risk priorities.
- AI-Driven Predictions – Uses AI to predict CVSS scores before they are officially assigned, helping teams stay ahead of potential threats.
- Further Context – Provides detailed timelines, Proof-of-Concept (PoC) availability, active exploit tracking, and links to relevant articles.
- Automation & Integration – Supports REST API access, CSV/PDF exports, and workflow automation for seamless integration into security operations.
Why Use It?
Feedly’s AI-driven approach goes beyond basic CVE tracking by providing predictive insights and real-time intelligence. Security teams benefit from actionable intelligence, allowing them to prioritize vulnerabilities effectively based on emerging threats and potential exploitability.
Limitations
While AI predictions are useful, they are not always 100% accurate. Additionally, Feedly’s most advanced features may require a paid subscription, limiting access to some automation and customization options for free-tier users.
Best For
3. CVE.org
CVE.org is the official website for the Common Vulnerabilities and Exposures (CVE) system, a publicly available list of known cybersecurity vulnerabilities and exposures. It provides a standardized method for identifying and sharing vulnerability information.
Key Features
- CVE List – A publicly accessible catalog of over 240,000 disclosed vulnerabilities, each assigned a unique CVE ID.
- Standardization – Facilitates consistency across security tools and databases using standardized identifiers.
- Governance – Maintained by MITRE Corporation and overseen by the CVE Board, which includes representatives from government agencies and major IT companies.
- Relationship with NVD – Integrated with the National Vulnerability Database (NVD), which provides additional vulnerability details like CVSS scores.
Why Use It?
CVE.org serves as a foundational resource for organizations and security teams, ensuring that vulnerabilities are consistently tracked across multiple platforms. It helps in improving cybersecurity defenses by offering an easy-to-reference system for known security issues.
Limitations
CVE.org does not provide detailed risk assessments or real-time exploitability tracking beyond its standardized vulnerability entries.
Best For
- Security vendors aligning their tools with official CVE identifiers for accurate vulnerability mapping.
- Enterprises with multi-platform environments needing standardized vulnerability tracking.
- IT asset managers cross-referencing CVE data with internal vulnerability databases.
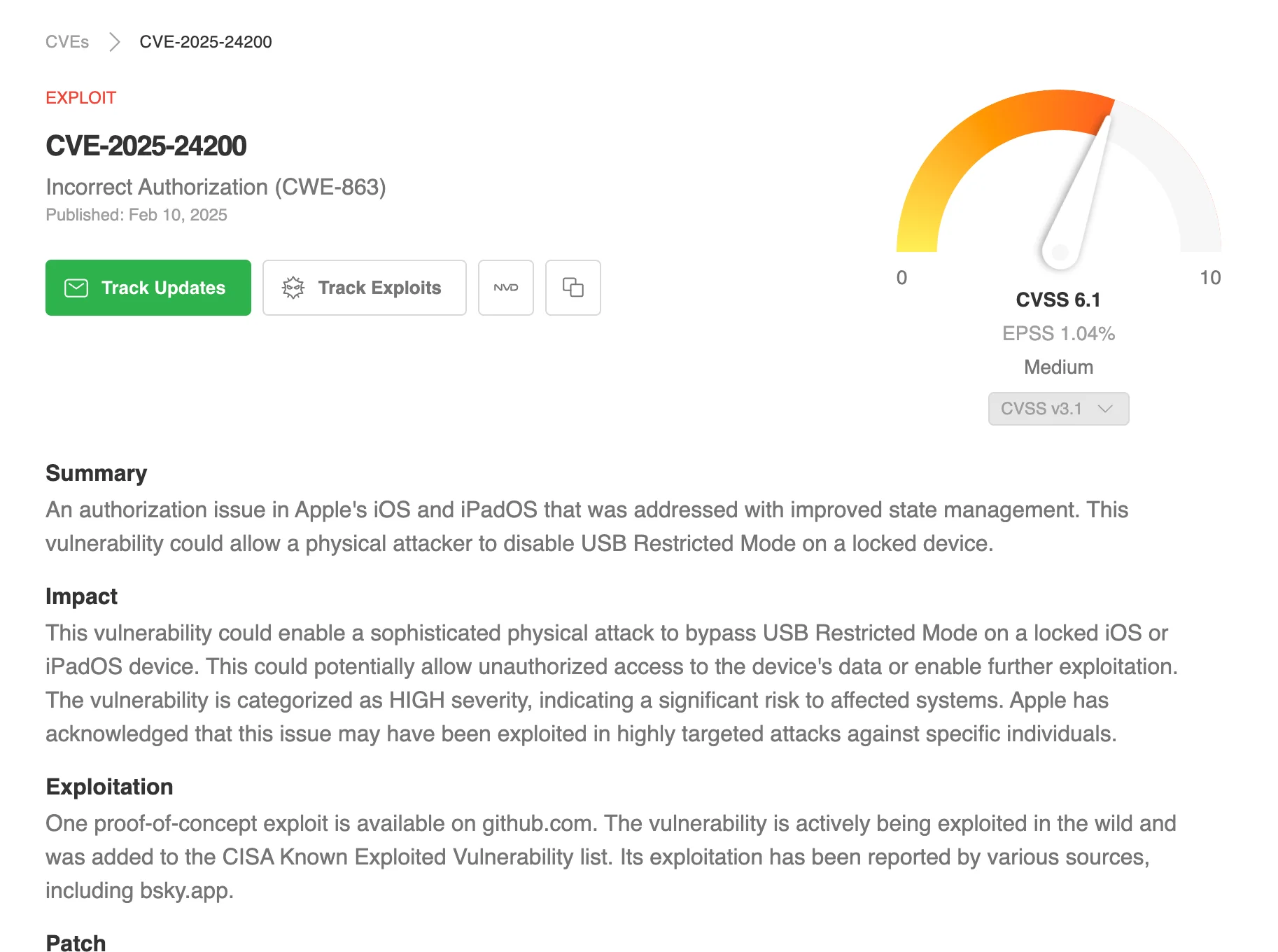
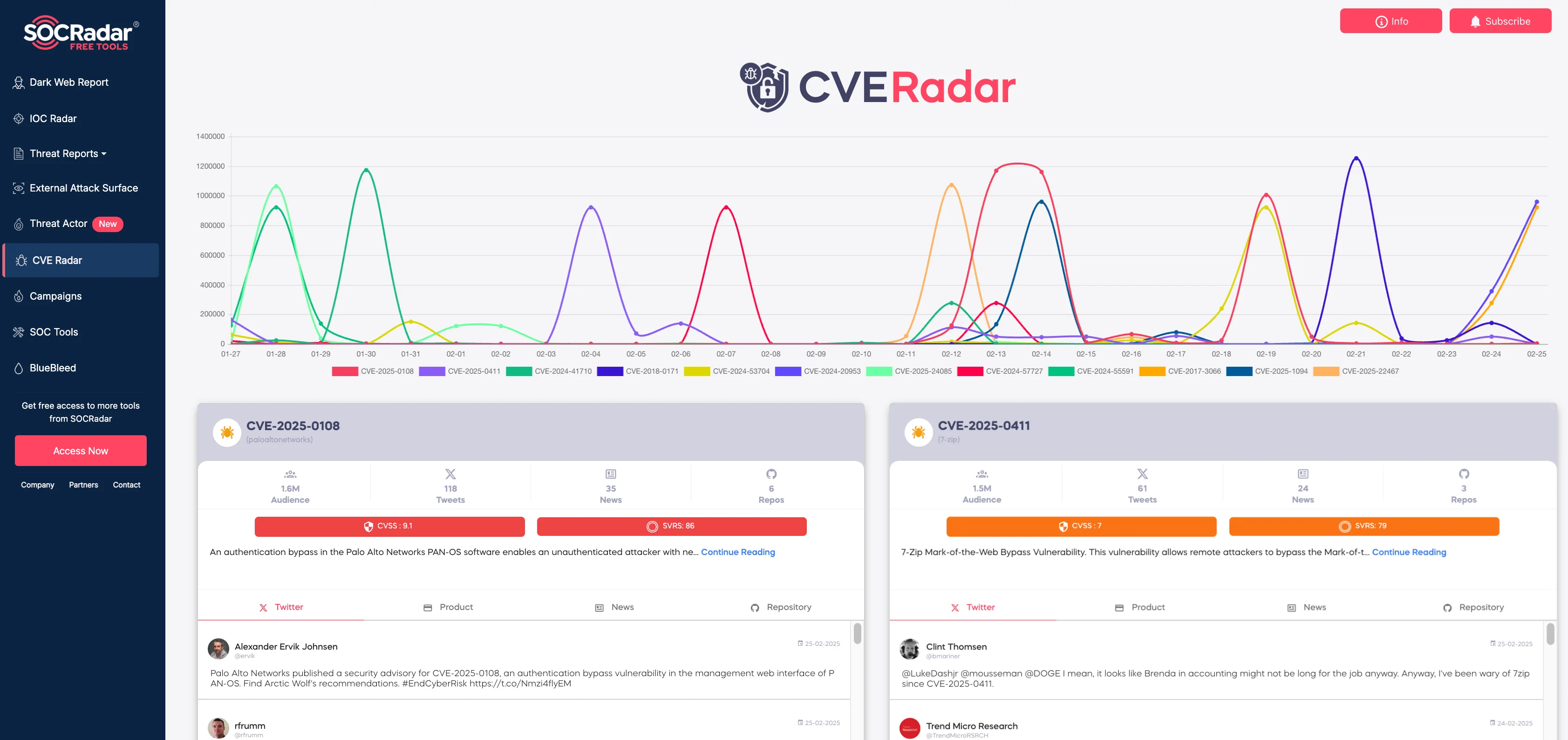
4. SOCRadar LABS Free Tools: CVE Radar
CVE Radar, part of SOCRadar LABS‘ free tools, is a free vulnerability monitoring solution designed to track emerging threats and assess risk trends. It provides insights based on open-source intelligence and dark web monitoring.
Key Features
- SOCRadar Vulnerability Risk Score – Assesses vulnerabilities based on data from dark web sources, social media, and security feeds.
- Trend Tracking – Monitors vulnerability discussions across Twitter, GitHub, news sources, and forums.
- Actionable Intelligence – Helps organizations identify high-risk vulnerabilities early based on real-world threat discussions.
Why Use It?
CVE Radar provides a dynamic approach to vulnerability intelligence, offering risk-based insights beyond traditional CVE databases. It helps security teams stay ahead of potential exploitations by monitoring real-time discussions.
Limitations
While CVE Radar provides valuable insights for free, it does not include the full capabilities of the Vulnerability Intelligence feature, available on the SOCRadar XTI platform. Users looking for deeper risk assessments, exploit tracking, and integration with additional security tools may try out the full version with SOCRadar Freemium.
Best For
- Threat hunters tracking vulnerabilities discussed on dark web forums and social media.
- Teams looking for early warning signals before vulnerabilities gain mainstream attention.
- Security analysts assessing the real-world risk of vulnerabilities beyond static CVSS scores.
Gain Deeper Insights with SOCRadar’s Vulnerability Intelligence
Beyond CVE Radar, SOCRadar’s Vulnerability Intelligence expands security capabilities by offering in-depth risk assessments and actionable intelligence. This feature, offered under the Cyber Threat Intelligence module, allows organizations to prioritize patching and mitigation efforts more effectively.
The platform assigns risk scores based on exploitation likelihood and business impact, ensuring security teams focus on the most pressing threats. It also identifies whether a vulnerability is actively exploited by threat actors, providing critical context for informed decision-making. Integrating with SOCRadar’s Attack Surface Management and Digital Risk Protection solutions, it offers a thorough security approach.
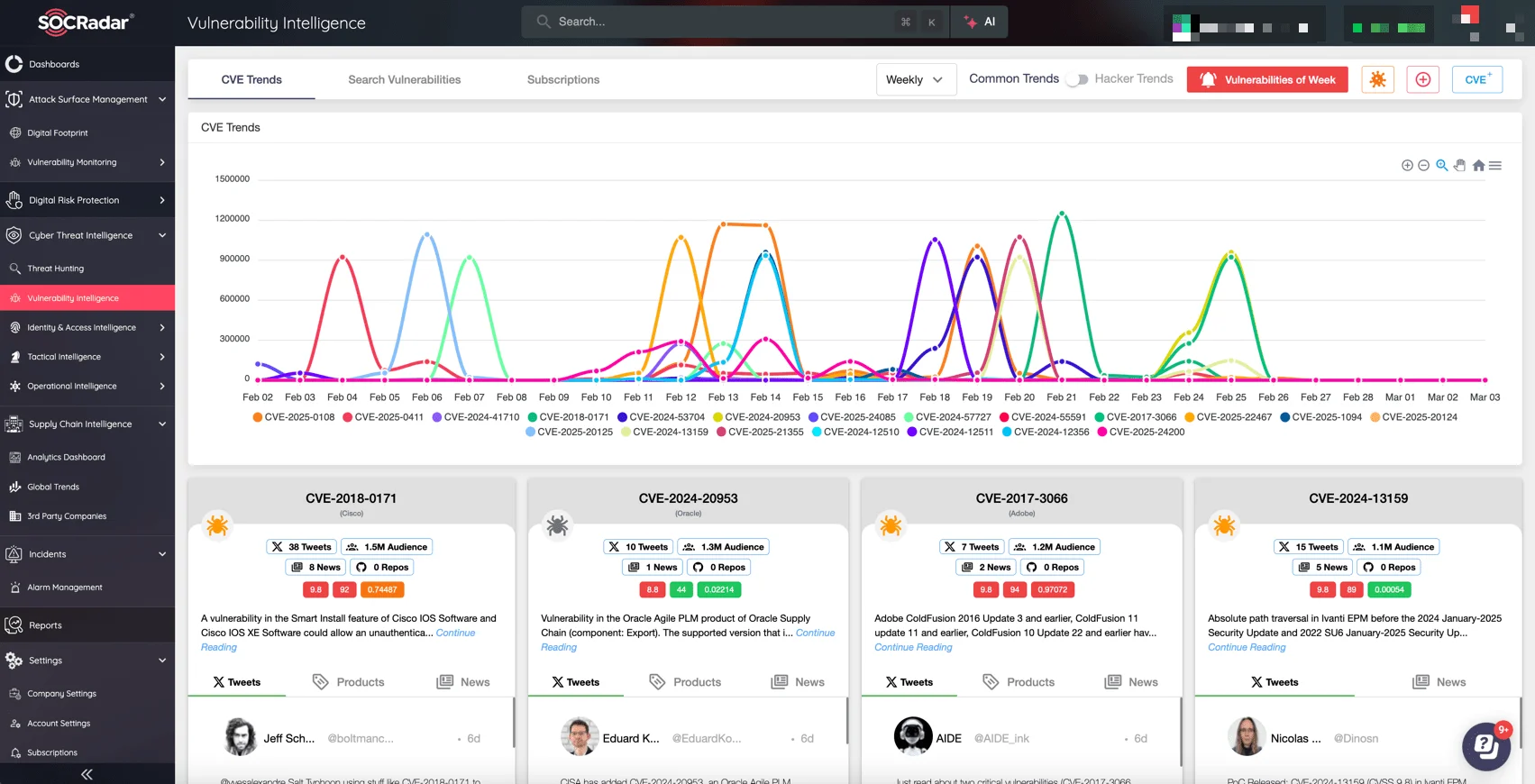
Vulnerability Intelligence page on the SOCRadar XTI platform
Ideal for organizations needing automated risk scoring and prioritization, SOCRadar’s Vulnerability Intelligence streamlines security workflows. Security analysts gain exploit intelligence, while businesses benefit from a unified approach to attack surface management.
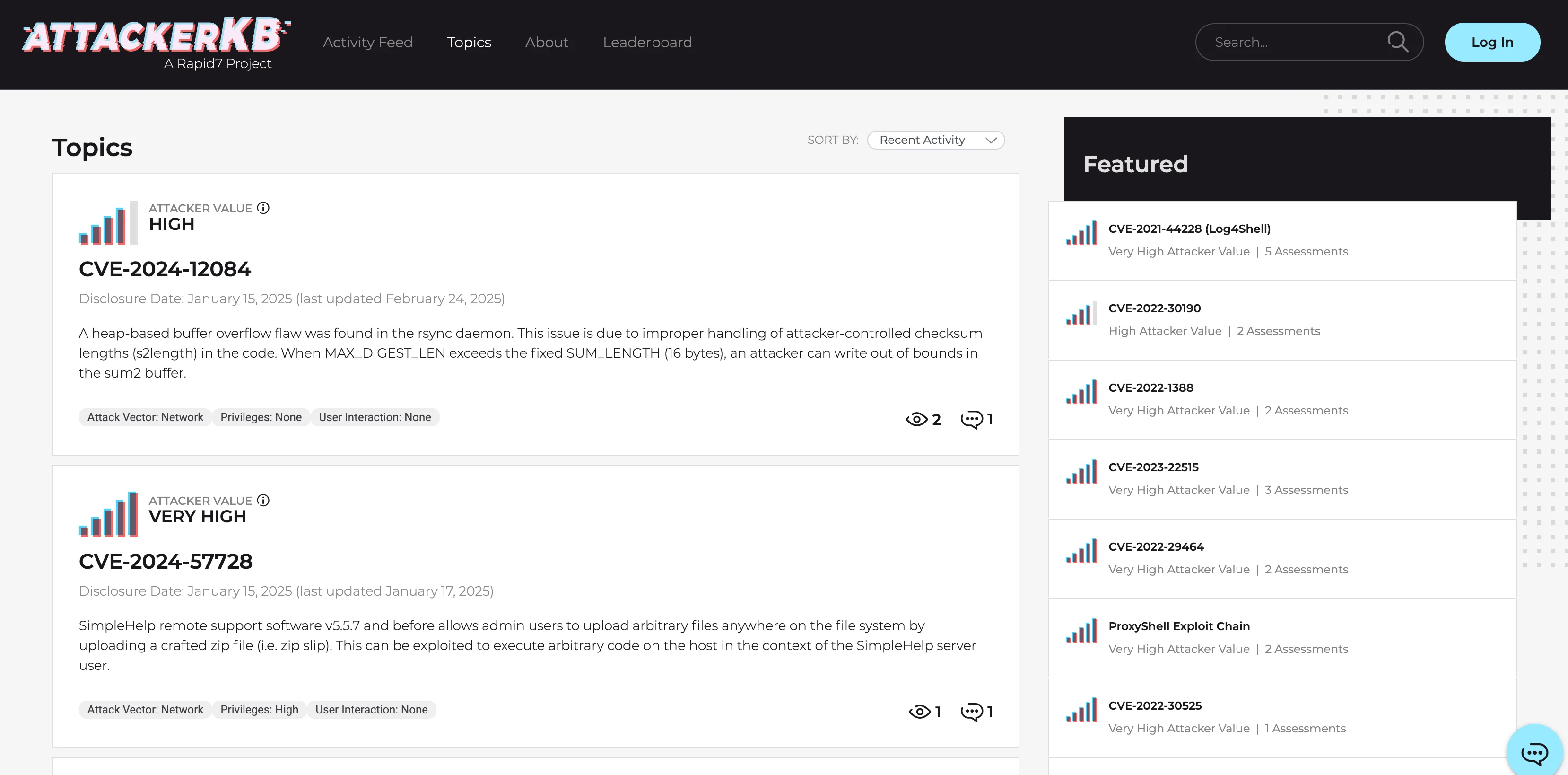
5. AttackerKB
AttackerKB is a free vulnerability intelligence platform designed for analysis, offering detailed insights into the exploitability and impact of cybersecurity vulnerabilities. It provides a running feed of new vulnerability assessments and technical breakdowns.
Key Features
- Exploitability Assessment – Rates vulnerabilities based on their ease of exploitation.
- Attacker Value Assessment – Assigns a value score indicating how useful a vulnerability is to attackers.
- Impact Analysis – Evaluates potential consequences, including data exposure and privilege escalation.
- Technical Analysis & Mitigation – Offers deep technical breakdowns and defensive guidance.
Why Use It?
AttackerKB is valuable for security researchers and professionals looking to understand real-world exploitability and assess the risks posed by new vulnerabilities.
Limitations
While AttackerKB provides in-depth vulnerability analysis, it relies on community contributions, which means coverage and detail levels may vary. Additionally, it does not offer automated vulnerability scanning or exploit tracking, requiring security teams to supplement it with other threat intelligence sources.
Best For
- Penetration testers evaluating exploitability and attacker interest in specific CVEs.
- Security researchers seeking detailed technical analyses and attack chains.
- Red and blue teams analyzing offensive security perspectives to improve defenses.
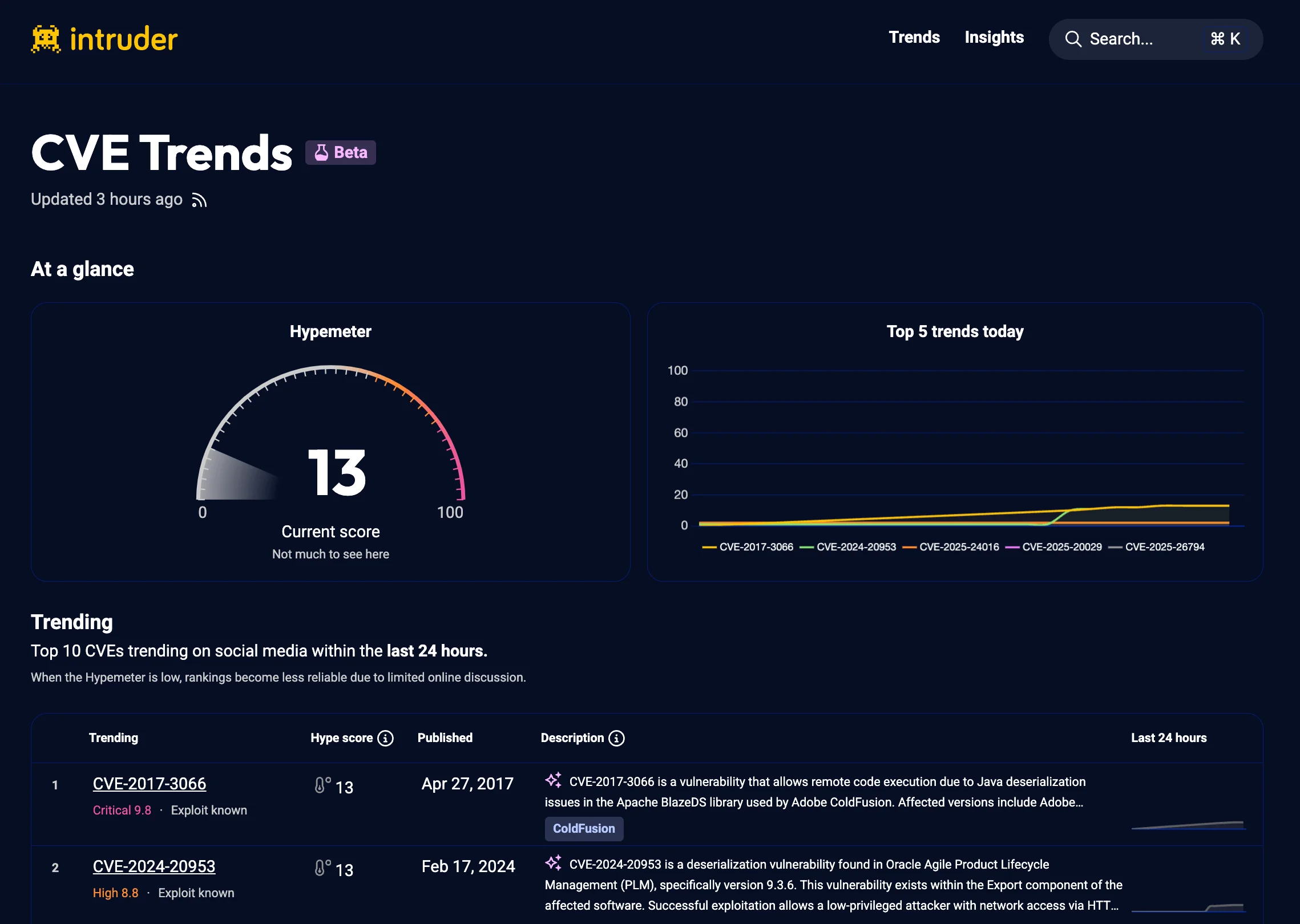
6. Intruder CVE Trends
Intruder CVE Trends is a tool that identifies and ranks the top 10 CVEs trending on social media within the last 24 hours. It helps security professionals stay informed about the most talked-about and potentially actively exploited vulnerabilities.
Key Features
- Trend Analysis – Monitors social media for emerging CVE discussions.
- Hype Score Ranking – Ranks trending CVEs based on discussion volume.
- Detailed CVE Insights – Provides CVE ID, severity, CVSS score, exploit status, and mitigation recommendations.
Why Use It?
Intruder CVE Trends helps security teams focus on vulnerabilities with high exposure, allowing them to prioritize remediation efforts efficiently.
Limitations
While Intruder CVE Trends offers valuable and timely insights, it primarily focuses on social media mentions and may not always correlate directly with real-world exploitation. It also lacks deep technical analysis and exploitability assessments, requiring security teams to use additional sources for verification.
Best For
- Incident response teams monitoring social media traction of newly disclosed CVEs.
- Security operations teams prioritizing vulnerabilities based on hype-driven exploitation risk.
- Organizations using threat intelligence feeds to assess trending vulnerabilities.
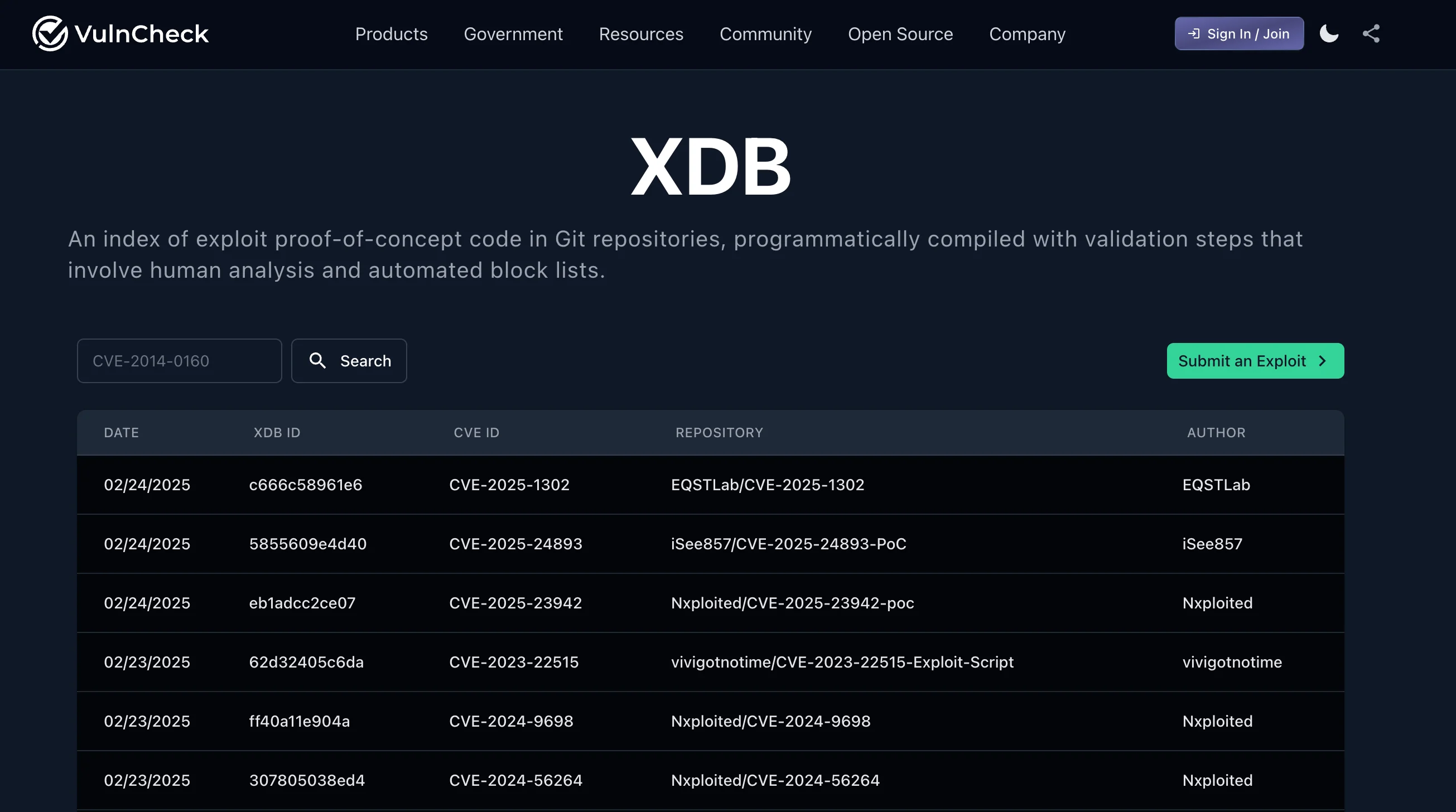
7. VulnCheck XDB
VulnCheck XDB is an indexed collection of Proof-of-Concept (PoC) exploit code gathered from Git repositories. Unlike simple lists, it is programmatically compiled, ensuring more structured and up-to-date exploit information.
Key Features
- Curated PoC Index – Provides a validated and structured repository of exploit PoC code.
- Human & Automated Validation – Uses a combination of human review and automated block lists to filter out malicious or irrelevant entries.
- Seamless Integration – Designed to work in conjunction with VulnCheck’s Cyber Threat Intelligence platform for enhanced exploit intelligence.
Why Use It?
Security professionals can leverage XDB to quickly locate reliable PoC exploit code, enabling better security assessments and proactive defense strategies.
Limitations
While VulnCheck XDB provides a valuable index of exploit PoC code, its reliance on Git repositories means it may not capture all exploits, particularly those shared privately or within closed communities. Additionally, while it includes validation mechanisms, automated filtering may still miss misleading or non-functional PoC code, requiring users to manually verify exploit reliability.
Best For
- Reverse engineers verifying PoC exploit functionality before deploying security patches.
- Red teams searching for reliable exploit code to test internal defenses.
- Cybersecurity educators using real-world PoC datasets for training and research.
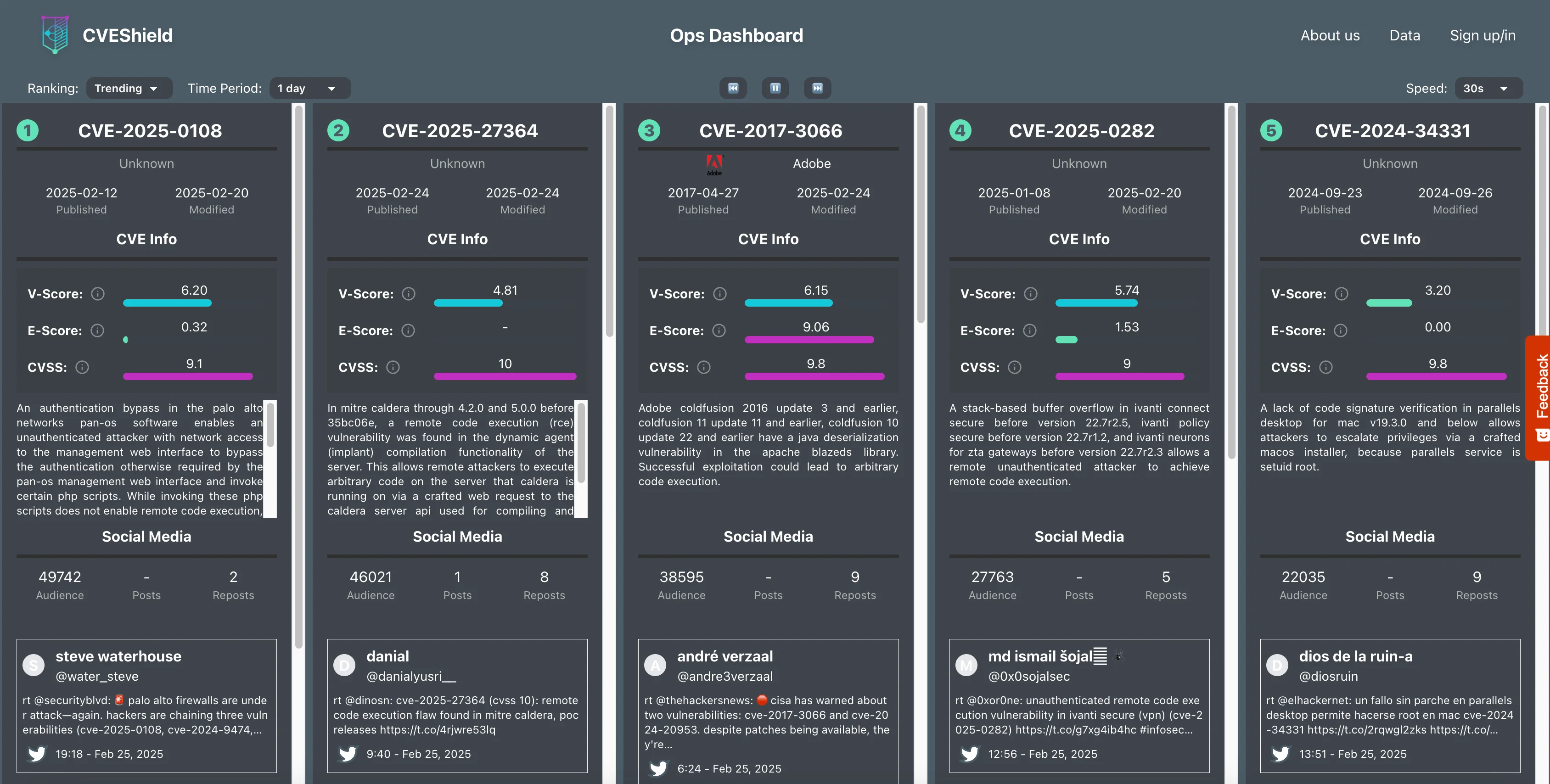
8. CVEShield
CVEShield provides a data-driven vulnerability assessment platform that aggregates threat intelligence signals from multiple sources. It builds upon the approach pioneered by Simon J. Bell’s CVE Trends, incorporating predictive scoring and live vulnerability tracking.
Key Features
- V-Score – A proprietary rating system estimating a vulnerability’s exploitability potential.
- E-Score – Derived from EPSS, evaluates real-world exploitation likelihood.
- Threat Intelligence Metrics – Tracks CVE discussions in threat intelligence reports, Reddit, and X (Twitter).
- Historical Context – Provides analysis of vulnerability trends over time.
Why Use It?
CVEShield helps organizations prioritize vulnerabilities by offering predictive risk scores and discussions from multiple intelligence sources.
Limitations
CVEShield’s heavy reliance on social media and external threat intelligence reports means it may not always reflect real-world exploitability accurately. Users may still need to cross-reference multiple sources for better risk assessment, accurate to their environment.
Best For
- Risk assessment teams balancing proprietary scoring models (V-Score, E-Score) with traditional CVSS ratings.
- Security leaders needing high-level insights into vulnerability discussion trends.
- Organizations evaluating historical threat intelligence to predict future attack patterns.
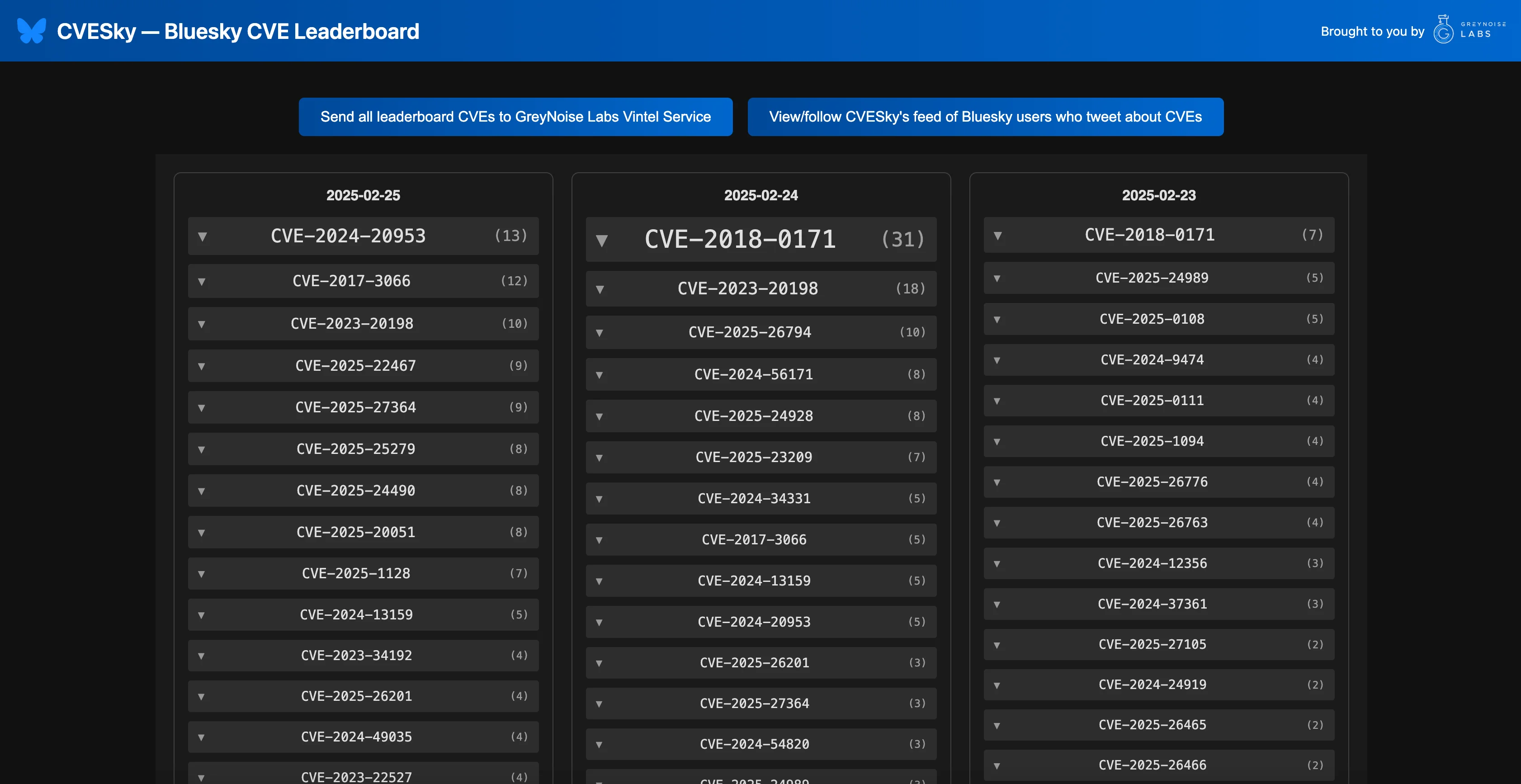
9. CVESky — Bluesky CVE Leaderboard
CVESky is a leaderboard that ranks CVEs (Common Vulnerabilities and Exposures) based on their popularity and discussion volume on the Bluesky social media platform. It is developed by GreyNoise Intelligence Labs.
Key Features
- Trend Monitoring – Identifies vulnerabilities gaining traction in the security community.
- Popularity Ranking – Ranks CVEs based on the volume of mentions and engagement.
- Community Sentiment Analysis – Provides insights into how the security community perceives specific vulnerabilities.
Why Use It?
The free vulnerability intelligence platform CVESky informs defenders about trending vulnerabilities, offering a snapshot of what is actively discussed within the Bluesky community. This can be particularly useful for identifying potentially exploitable vulnerabilities before they become widely targeted.
Limitations
CVESky’s reliance on Bluesky discussions means it may miss vulnerabilities that are highly relevant but not actively talked about on the platform. Additionally, trends on social media do not always correlate with real-world exploitability.
Best For
- Security researchers tracking emerging threats in Bluesky’s security community.
- Threat analysts correlating social sentiment with vulnerability prioritization.
- Teams looking for an alternative to X/Twitter-based CVE tracking.
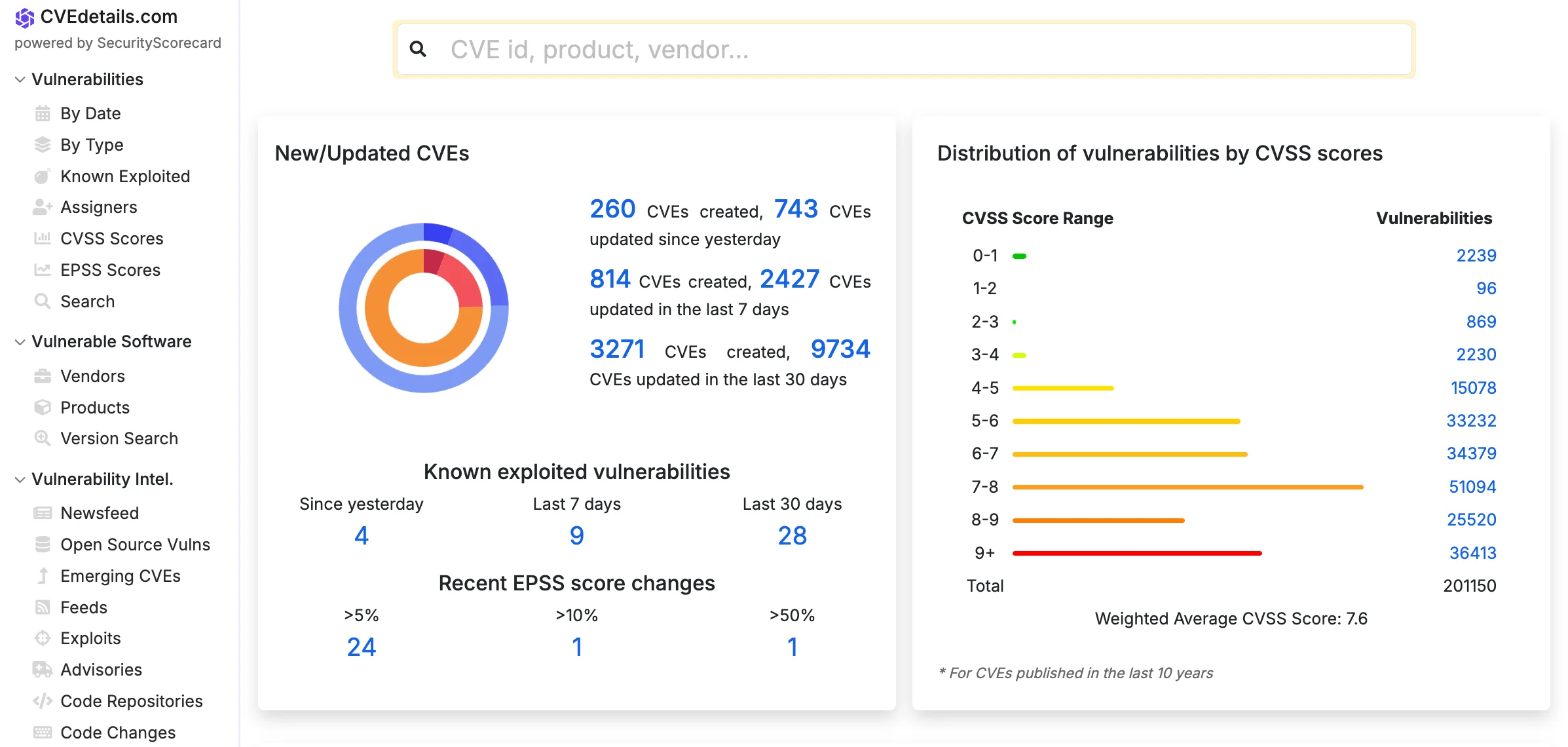
10. CVE Details
CVE Details is a comprehensive vulnerability intelligence platform that enhances publicly available CVE information with additional context, making it easier for security teams to assess and act on threats.
Key Features
- Enhanced CVE Database – Integrates advisories, exploits, tools, and source code changes, providing many filtering options for search.
- CISA KEV Catalog Integration – Lists vulnerabilities known to be actively exploited.
- EPSS Scores – Provides Exploit Prediction Scoring System (EPSS) scores to estimate exploitation likelihood.
- CPE Information – Offers Common Platform Enumeration (CPE) data for CVEs, even when missing from NVD.
- Alerts & Feeds – Allows users to set up email alerts, CVE feeds, and API integrations.
Why Use It?
CVE Details aims to serve as a one-stop-shop for free vulnerability intelligence, helping security professionals efficiently gather relevant information without relying on multiple sources.
Limitations
CVE Details it sees NVD’s reliance on automation and delays in data enrichment as leading to incomplete or inaccurate CPE data. To mitigate this, it combines automated and manual analysis to improve CPE accuracy, particularly for widely used and enterprise software. However, this approach means niche applications, open-source projects with limited adoption, or obscure platforms may not receive as much attention. While this selective focus strengthens its reliability for enterprise security, teams working with niche software should supplement their research with additional sources for a more complete risk assessment.
Best For
- Security teams needing an all-in-one vulnerability reference.
- IT teams mapping CPE data to affected products for more accurate asset management.
- Vulnerability management teams that need deeper filtering options beyond NVD’s standard feeds.
Conclusion
Effective vulnerability management requires timely, accurate, and actionable intelligence. The 10 free vulnerability intelligence platforms covered in this article provide security teams, researchers, and organizations with essential resources to track, analyze, and prioritize vulnerabilities without the financial burden of premium services.
From government-backed databases like NVD and CVE.org to AI-driven insights from Feedly and SOCRadar’s CVE Radar, these platforms offer diverse capabilities for different use cases. Whether you need exploit tracking, social media-driven CVE rankings, or curated PoC exploit repositories, these free tools can enhance your cybersecurity posture.
While free solutions provide immense value, they do have limitations. Some rely heavily on public disclosures, social media trends, or proprietary scoring models that may not always align with real-world exploitability. As such, security teams should combine multiple sources and validate findings to ensure a well-rounded vulnerability management strategy.
Ultimately, leveraging free vulnerability intelligence platforms helps organizations stay ahead of threats, reduce risk exposure, and make data-driven security decisions. By integrating these tools into their workflows, cybersecurity teams can enhance their defenses and improve overall threat awareness – at no cost.