
Top 50 Cloud Statistics in 2024 (Essential Insights on Investments, Br...
Top 50 Cloud Statistics in 2024 (Essential Insights on Investments, Breaches, Misconfigurations, and More) In the fast-changing world of cloud computing, it’s essential for both organizations and prof...

Alleged Leaks: Tencent, FTD Educação, and Yellow Pages Data Exposed
Alleged Leaks: Tencent, FTD Educação, and Yellow Pages Data Exposed The SOCRadar Dark Web Team has identified several significant cyber threats in the past week. These include the sale of 21,000 U.S. ...

SOCRadar APAC Threat Landscape Report: Gain Insights Into Threats &...
SOCRadar APAC Threat Landscape Report: Gain Insights Into Threats & Trends from the APAC Region Understanding localized cybersecurity issues is more important than ever in a time when cyber threat...

Dark Peep #16: Play Ransomware & LockBit's Alliance, BreachForums ...
Dark Peep #16: Play Ransomware & LockBit’s Alliance, BreachForums Leak, and CyberNiggers’ Revival Welcome to Dark Peep #16, where we unravel the freshest and most daring cyber capers. ...
Critical Vulnerabilities in Progress WhatsUp Gold, Jenkins Could Lead ...
Critical Vulnerabilities in Progress WhatsUp Gold, Jenkins Could Lead to RCE Attacks (CVE-2024-4885, CVE-2024-43044) A critical vulnerability in Progress WhatsUp Gold, recently patched, has been activ...

Unlocking the Future of Cybersecurity: SOCRadar’s Advanced AI Training...
Unlocking the Future of Cybersecurity: SOCRadar’s Advanced AI Training Returns The cybersecurity landscape constantly evolves, and staying ahead of emerging threats with complicated risks is more cruc...

5 Supply Chain Intelligence Use Cases with SOCRadar Module
5 Supply Chain Intelligence Use Cases with SOCRadar Module Numerous high-profile incidents have evidenced that cyber threats to the supply chain can have catastrophic consequences. To mitigate these r...

SOCRadar Recognized in Gartner Report on Digital Risk Protection Servi...
SOCRadar Recognized in Gartner Report on Digital Risk Protection Services and External Attack Surface Management Again In a report published by Gartner on its website on July 29, 2024, SOCRadar was hi...

Major Cyber Attacks in Review: July 2024
Major Cyber Attacks in Review: July 2024 July 2024 has been marked by a series of high-impact cyber attacks, affecting millions of individuals and numerous organizations. Amidst numerous threat activi...

SOCRadar's Response to the USDoD’s Claim of Scraping 330 Million Email...
SOCRadar’s Response to the USDoD’s Claim of Scraping 330 Million Emails TL;DR The claim that the threat actor extracted the data from the SOCRadar platform is inaccurate and does not reflect the t...

ADT, Citi Bike, Sun West Mortgage, and Bausch Health Face Alleged Data...
ADT, Citi Bike, Sun West Mortgage, and Bausch Health Face Alleged Data Breaches Several significant data breaches and cyber threats impacting major companies have been detected by the SOCRadar Dark We...

Critical Bitdefender Patch for GravityZone Update Server: CVE-2024-698...
Critical Bitdefender Patch for GravityZone Update Server: CVE-2024-6980 Could Lead to SSRF Attacks Bitdefender, a provider of cybersecurity solutions, has recently patched a critical vulnerability (CV...

Comprehensive Guide to Threat Vectors in Cybersecurity
Comprehensive Guide to Threat Vectors in Cybersecurity In today’s digital landscape, cybersecurity threats are ever-evolving and increasingly sophisticated. Threat vectors are the various methods or p...

NIS2 and DORA: What You Need to Know to Stay Compliant and Secure
NIS2 and DORA: What You Need to Know to Stay Compliant and Secure Navigating regulatory compliance can be challenging, particularly for critical sectors in the EU. The NIS2 (Network and Information Se...

Dark Web Profile: Dark Angels
Dark Web Profile: Dark Angels Dark Angels or Dunghill Leak is a sophisticated and highly disruptive ransomware group that has recently gained notoriety. Known for their aggressive tactics and signific...

The Leidos Leak: What to Know, What Are Its Implications?
The Leidos Leak: What to Know, What Are Its Implications? In July, a post on BreachForums brought to light a significant leak involving Leidos Holdings Inc., claiming the exposure of internal files. L...

Why Brand Protection Matters: 5 Cases Every Business Should Know
Why Brand Protection Matters: 5 Cases Every Business Should Know Businesses need to remain cautious in order to protect their assets from the increasing sophistication of hostile actors and the develo...

Top 10 Attack Surface Management Tools
Top 10 Attack Surface Management Tools Attack Surface Management (ASM) tools have become critical for organizations in identifying, managing, and mitigating vulnerabilities in digital environments. Th...
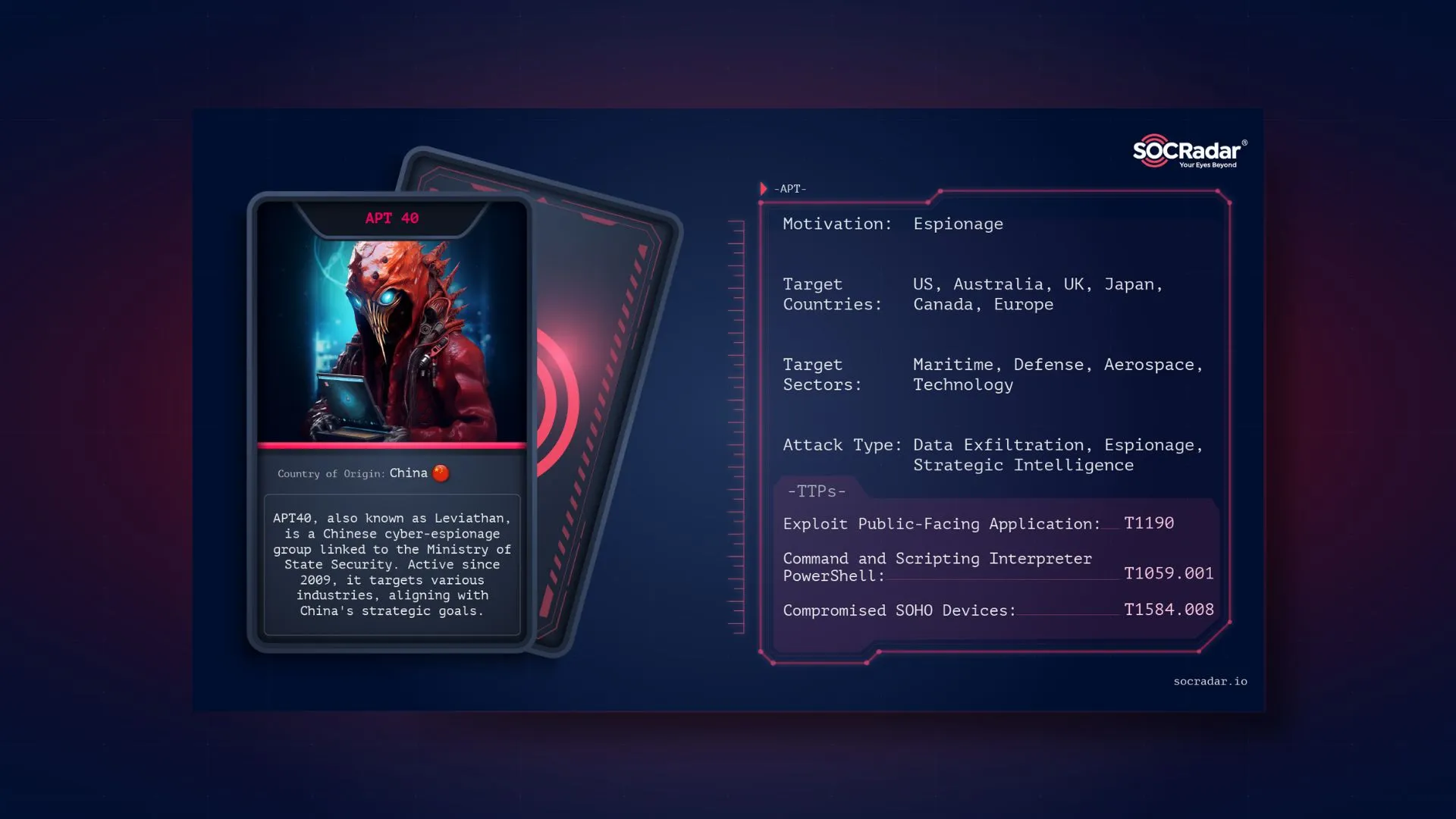
Dark Web Profile: APT40
Dark Web Profile: APT40 APT40, also known as TEMP.Periscope, Leviathan, and many other aliases, is a Chinese cyber-espionage group attributed to the Chinese Ministry of State Security (MSS). Active si...

VMware ESXi Hypervisor Vulnerability (CVE-2024-37085) Exploited by Ran...
VMware ESXi Hypervisor Vulnerability (CVE-2024-37085) Exploited by Ransomware Groups, Microsoft Warns [Update] July 31, 2024: “CISA Adds VMware ESXi Hypervisor Vulnerability (CVE-2024-37085) to ...
































