Expectations of SOC Team from CTI
Every company with an online component to its business needs cyber awareness; it also requires a Security Operations Center (SOC) if the online part is big enough. A SOC team requires reliable cyber threat intelligence to function effectively.
What is a SOC?

A SOC is a centralized unit for controlling, identifying, and responding to the ever-changing security issues and incidents that a company may face. A SOC serves as a node that uses the collected information from an entity’s infrastructure, including its networks, equipment, and information centers, to identify and defend against current and potential threats. Therefore, the SOC team ensures the company’s data’s confidentiality, integrity, and availability. The daily operation of the SOC team includes incident detection, identification, analysis, and response.
What is Cyber Threat Intelligence?
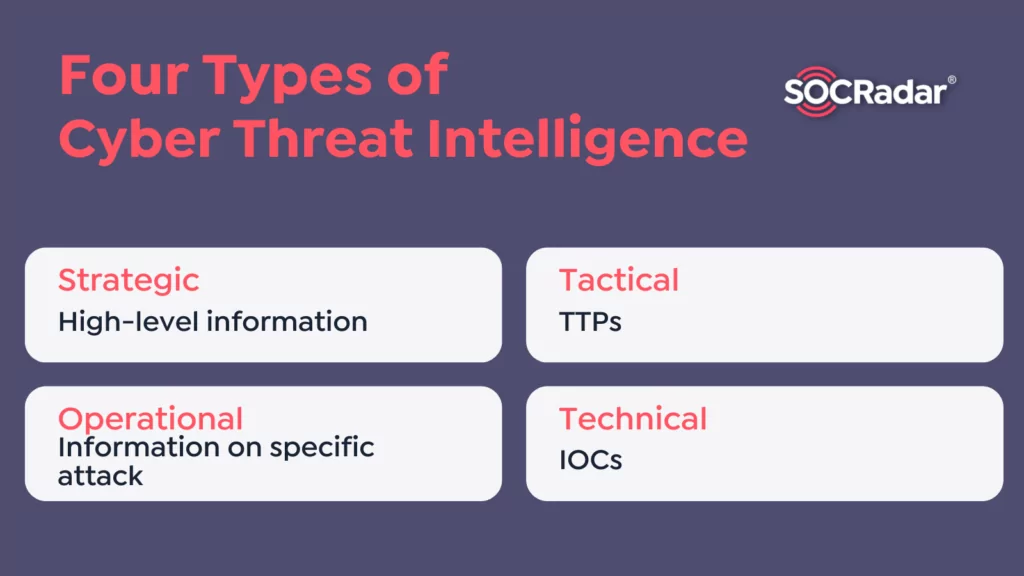
Cyber Threat Intelligence, or threat intelligence, is evaluated and analyzed information collected from various sources with various reliability. This information could be some recent cyber incidents or knowledge about a threat actor’s motives, targets, and attack behaviors.
The involvement of technology like artificial intelligence and machine learning, analysis, and expertise of CTI analysts transforms knowledge into intelligence. Correct threat intelligence fed to a SOC team will reduce uncertainty while aiding the team in identifying current and future threats.
Challenges for SOC Teams
In addition to being the first line of defense against the cyber threat, a SOC team must be ready for potential threats. However, even responding only to cyber incidents could overwhelm the team over time.
Without threat intelligence, a SOC team could waste precious time assessing and sorting similar low-level incidents, warnings, and alerts. One of the dangerous side-effects of such a menial task is that it could create alert fatigue, which could cause SOC analysts not to respond quickly enough or ignore it completely.
Another challenge is the analysis of the collected data. SOCs collect data and logs from many cyber security devices and systems like firewalls, EDRs, virus protection, and email gateways, producing different data types that need to be analyzed differently. Most SOCs neither have time nor means to do that.
How Could CTI Help?
When a SOC team starts to consume tailored CTI for its needs, it will have time to prioritize the actions of detection and prevention to conserve resources and increase the team’s overall efficiency. For example, incident response is one of the time-consuming jobs of a SOC team.
CTI could provide the context of who the threat is, which helps the responders understand the threat actor’s targets, motives, and actions. CTI could also enable the SOC team to reach relevant TTPs (Tactics, Techniques, and Procedures) and IOCs (Indication of Compromise) of the active threat. Therefore, the incident responders of the SOC team could run a more profound investigation in less time.
CTI Outputs for SOC Teams
Cyber Threat Intelligence Reports:
They generally summarize cyber threat activities for a specific enterprise or business sector, ranging from monthly to annual.
Case Management Notes and Reports:
Cyber threat analysts analyze specific threats like known APTs (Advanced Persistent Threats) or ongoing campaigns. Prepared documentation and notes shared with SOC team. These analyses can be done daily to weekly.
Formal Incident Write-ups:
Notable incidents are recorded more formally to be presented to the general information security community and the enterprise in a presentation or report. These presentations could happen monthly or quarterly.
Cyber Threat Tips:
These are short quick communications to warn a cyber threat sharing group within minutes or hours of identifying an activity as a targeted intrusion attempt or ongoing campaign. Tips generally contain simple IOC information and some informal context.
Short-form Malware Report
CTI analysts prepare a brief report on recently observed malware in the SOC environment. The report includes some indicators and information regarding an observed piece of malware.
Long-form Malware Report
The report provides detailed and precise indicators and information about malware used for significant attacks. It includes a reverse-engineering effort that took several days or weeks to accomplish. It comprises technical details like a complete description of the malware sample’s functionality, any encryption used, and its network protocols used for command and control.
Adversary and Campaign Reports and Presentations
Those focus on severe threats like APTs or adversary campaigns. They combined activity from multiple incidents over several months of reporting and contextualized them with ongoing geopolitical and economic developments.
Trends of adversaries, campaigns, or other incidents
Cyber threat analysts follow the bigger picture of adversaries and incidents. Therefore, they conduct trend analysis and pattern recognition and draw associations across activities that a SOC team might miss. These conclusions can be presented in comprehensive annual or quarterly reports.
Indicator Lists and TTPs with Context
Cyber threat analysts collect and correlate various indicators of compromise (suspicious IP addresses, domains, email addresses, etc.) from external and internal. These indicator lists primarily generate signatures and other detection content in the SOC’s tools (Firewalls. SIEM, EDR, etc.).
Sensor and analytics enhancements
CTI analysts could help a SOC team write and enhance detections and analytics via generated technical details.
Custom Tools or Scripts
Cyber threat analysts realize that there are gaps in the capabilities of cyber defense systems that cannot be filled with Free and Open-Source Software (FOSS) or COTS solutions. Custom tools are spun off irregularly, usually developed very quickly, and do not always reach full maturity before they are no longer required.
Conclusion
Most of the time, the production and consumption of CTI relate to the maturity of an organization’s cyber security. A CTI program is a critical part or partner of a SOC team depending on the preference and configuration of the cyber defense of an enterprise and making life easier for the SOC.