
New ICT regulation of EU Financial Sector: DORA
by SOCRadar Research
Cyber-attacks are rising worldwide, and the financial industry is among the most targeted ones. Cyber threats and attacks have become one of the sources of systemic risk for the financial industry. The problems that will occur as a result of a cyber-attack on the financial system can trigger a systemic collapse. The European Union has proposed a legal proposal in this regard, known as the Digital Operational Resilience Act (DORA).
What is DORA?
DORA is one of the European Union’s cybersecurity legislative initiatives designed exclusively for the financial industry, and it is one of the most comprehensive cybersecurity legislations prepared. It is intended to strengthen the financial industry’s cybersecurity posture and operational resilience and ease third-party risk management.
What is the Timeline for DORA?
The EU Commission published the first draft of the DORA on September 24, 2020. The document launched the negotiation stage on November 24, 2021, and was accepted as a provisional document on May 10, 2022.
On November 10, 2022, the final version was adopted at the plenary session of the European parliament. It is expected to enter into force before the end of 2022 after it is signed by the Council of the European Union and published in the Official Journal of the EU. After the law goes into effect, companies will have a 24-month compliance period to fulfill the requirements.
Why does the EU Need It?
The financial industry has responded to the digital transformation that has occurred in every field. The rapid transition to remote working, particularly following the Covid-19 pandemic, has accelerated companies’ transfer of operations from the physical to the digital environment. In addition to cyber vulnerabilities caused by increasing digitalization in the financial sector, rising supply chain cyber-attacks globally have forced the European Union to impose broad cyber security regulations for the financial industry, including third-party suppliers.
Furthermore, existing ICT risks urged member states to implement various regulations. However, there has been an increase in national, inconsistent, and non-harmonized regulatory initiatives.
DORA was formed in response to rising financial sector risks and the need for a unified piece of legislation to ensure compliance and strengthen regulatory and operational resilience across the European Union.
What are the Goals?
The DORA’s primary goal is to prevent and minimize cyber threats in the financial industry. DORA develops a regulatory framework to ensure that all businesses are digitally flexible enough to withstand, respond to, and recover from any ICT-related cyber threat. The aim is to ensure business continuity even when an organization’s ICT is disrupted.
DORA also establishes the network and information system security requirements for critical third-party providers of ICT-related services, such as cloud platforms or data analytics services, and organizations in the financial sector. These requirements are consistent across all EU member countries. In this context, the DORA aims;
- To develop a monitoring system for critical technology service providers in the financial industry (such as cloud computing).
- To develop a risk management system within financial institution information technology applications.
- To determine concrete financial industry cybersecurity responsibilities.
- To negotiate contract terms between third-party service providers and financial institutions.
- To determine the roles of financial regulators in cybersecurity.
- To identify requirements for supply chain risk management.
Which Entities Are Covered?
The DORA directly covers financial organizations, including banks and insurance firms. However, depending on their function in the supply chain, institutions that provide technology services to a financial institution may be directly or indirectly covered by the DORA.
Financial entities:
- Banks
- Payments and Credit institutions & Credit rating agencies
- Electronic Money Institutions
- Crypto assets & crowdfund
- Insurance & Reinsurance providers
- Investment companies & Investment funds
- Capital markets entities
- Brokers
- Central Securities Depositories (CSDs)
- Central Clearing Counterparties (CCP)
- Trading venues
- Trade repositories
- Alternative investment funds and management,
- Occupational retirement pensions,
- Statutory auditing and audit firms
Information and Communications Technology (ICT) Service Providers
- Payment solutions providers
- Data storage solutions providers
- Cloud providers / SaaS / Outsourcers
- Software providers
- Collaborative tools providers
- Fraud management providers
- Information management systems/ CRM solutions providers
- Critical ISV and systems integration providers
- Penetration testing providers
- Governance, Risk Management, and Compliance / Risk management providers
How are non-EU organizations relevant to DORA?
The DORA, as an EU regulation, applies directly to EU-based entities. However, if a non-EU financial institution operates within the borders of the EU, has a subsidiary in the EU, or a non-EU technology firm provides services to an EU-based financial institution, the DORA covers both the institution and its supply chain.
Furthermore, under the DORA, non-EU businesses that provide critical ICT services to EU financial institutions will be required to establish a subsidiary in the EU.
What is Included in the DORA?
The DORA is based on five basic pillars:
- ICT Risk Management: DORA establishes requirements for properly managing ICT risks. These requirements include procedures for risk identification and risk minimization.
- ICT Incident Reporting: DORA enforces improved monitoring, detection, and reporting of cyber threats and attacks in the financial sector. As a result, while all reports are collected in a central hub, the reporting process is standardized.
- Digital Operational Resilience Testing: DORA expands security testing requirements and seeks to establish an EU testing standard. Assessments of vulnerabilities and network security, gap analyses, software solution testing, scenario-based testing, penetration testing, and third-party risk surveys are covered by the DORA testing requirements.
- Information and Intelligence Sharing: DORA encourages the exchange of cyber threat intelligence and information between partners and competing businesses.
- ICT Third-Party Risk Management: DORA requires financial institutions to assess and document the risks associated with ICT service providers. Contracts with these companies must comply with DORA.
Are There Any Sanctions?
DORA requires determining if each third-party service provider meets the definition of a Critical ICT Third-Party Provider (CTPP). Furthermore, organizations that provide third-party services must comply with DORA in terms of risk management and operational resilience. According to the DORA proposal, a periodic penalty payment may be imposed on the CTPP to compel compliance with the requirements. The specified amount for the periodic penalty payment is 1% of the average daily global turnover of the CTPP in the previous financial year. Penalties are enforced daily until compliance is met.
How SOCRadar Help to Comply with Digital Operational Resilience Act?
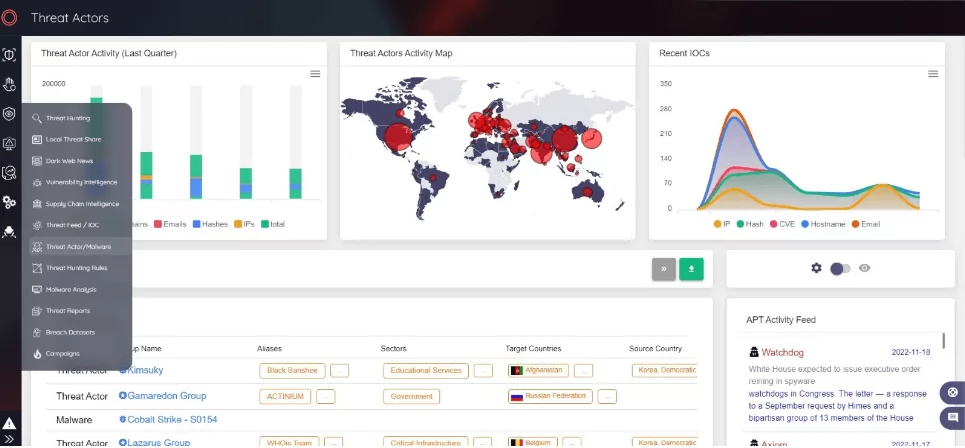
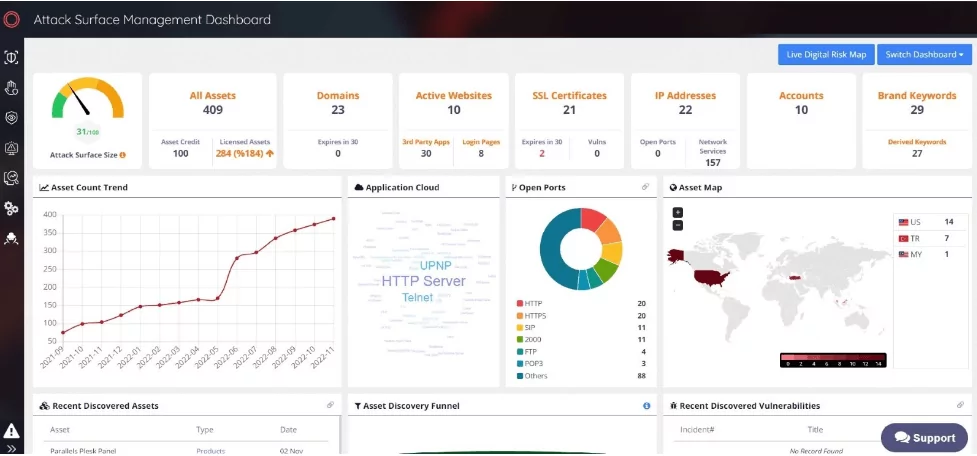
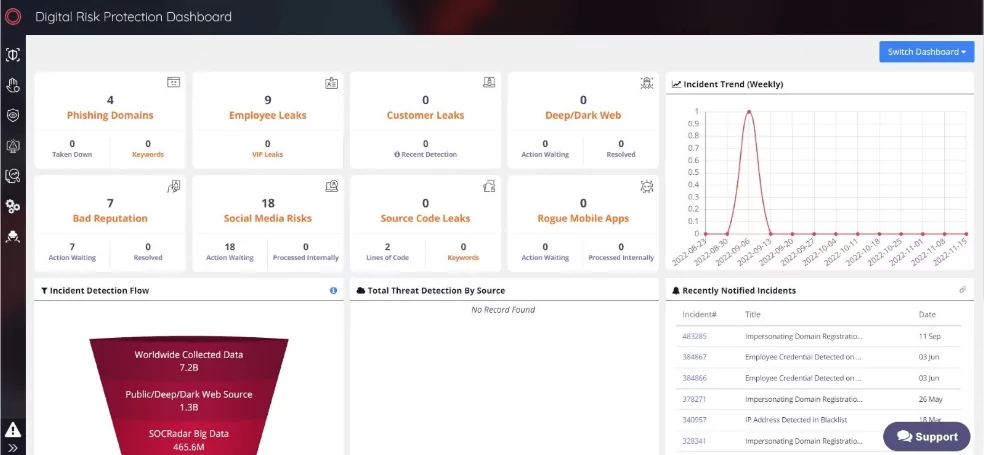
SOCRadar Extended Threat Intelligence concept combines external attack surface management, digital risk protection, and cyber threat intelligence. It can assist organizations in establishing robust risk management with various stages such as identification, protection, prevention, and response in meeting the requirements of the DORA.
One of the crucial solutions to comply with DORA is cyber threat intelligence (CTI). CTI aims to assist institutions and organizations in understanding the risks associated with cyber-attacks or cyber threats. Companies can use cyber threat intelligence to identify the dynamics and consequences of risks, improve security posture and structures, and reduce potential attacks to minimize damage and defend their network. In this regard, the deployment of CTI helps financial institutions have a strategic advantage against both new and existing threats and fulfills DORA’s regulations.
Another approach to comply with DORA is Attack Surface Management (ASM). The term “attack surface” refers to any asset that is open to the Internet and can be exploited by attackers. ASM keeps track of the ever-changing attack surface and identifies blind spots. It continuously monitors all systems for newly discovered vulnerabilities. This real-time visibility is critical for identifying risk and determining how an organization’s ICT system infrastructure will respond to an attack. The ASM solution, which serves as a platform to provide insight into companies exchanging data in compliance with DORA’s security standards, will be effective for third-party risk management via scanning & analyzing their assets.
Additionally, Digital Risk Protection (DRP) eliminates risks associated with digital transformation to protect company data, brand, and attack surface from unauthorized disclosure. DRP gathers relevant data from large amounts of data, associates it with its user, and presents it to the user as actionable intelligence alerts. Its users can quickly understand how certain risks will develop and what needs to be done to mitigate them and take action. So, DRP is a beneficial solution to meet the requirements of DORA.
Digitalization in the financial sector includes opportunities but also some risks of ICT. Organizations should establish clear rules and expectations to anticipate and mitigate the interruptions caused by potential risks. DORA, which is prepared to strengthen operational resilience capabilities, helps the development of digitalization while mitigating the risks.
Although the DORA, a pioneering regulation in its field, is currently valid for the European Union, it is likely to inspire regulations in other parts of the world. Whether affiliated with the European Union or not, financial institutions and third-party partners will benefit from DORA for aligning their ICT operations.




































