
Top 10 TLDs Threat Actors Use for Phishing
[Update] May 18, 2023: Google has released eight new top-level domains (TLDs). Added the subheading: “Google’s New TLDs: Commercial Opportunities and Security Risks”
A TLD is the last character of a domain name, such as .com, .net, .org, etc. Domains play a crucial role in phishing attacks. A threat actor can use free domains to create a distribution of phishing. In addition, if they are willing to pay the price, known TLDs such as .com and .org can be used and are likely to bring more success in phishing attacks.
Generic Top-Level Domains (gTLDs) and country-code Top-Level Domains (ccTLDs) are the two primary categories of TLDs.
The term “generic” (gTLDs) implies that they are not tied to any particular region or nation. On the internet, anyone can register them from anywhere in the world. The well-known gTLDs are “.com,” “.net,” “.business,” “.info,” and “.org”.
Country code Top-Level Domains (ccTLDs) are two-letter TLDs that are given to nations primarily based on their country codes. For instance, “.sg” stands for Singapore, “.vn” for Vietnam, and “.in” for India. A country and geographic designation are included in a ccTLD, which is exclusively intended for one country or region. Due to their exclusive management by their respective governments, several ccTLDs are closed and restricted.
Top Used Phishing TLDs in 2022
According to research done by the Cybercrime Information Center, the top 10 TLDs are:
- .com
- .cn
- .tk
- .ml
- .xyz
- .buzz
- .shop
- .cf
- .net
- .ga
The non-free TLDs range in price, but the most expensive ones are the best for social engineering attacks. When a user sees a .com domain, they immediately think it is legitimate due to .com being standard in online commerce. The user is more likely to fall for the phishing scam if they are familiar with the TLD.
Four of the top ten-ranked ccTLDs (.tk, .ml, .ga, and .cf) are run by Freenom, a Dutch firm that provides free domain registrations in these ccTLDs.
For the 2022 period, in place of .top and .gq, two new TLDs, .shop and .buzz, have entered the Top 10.
Statistics of Phishing
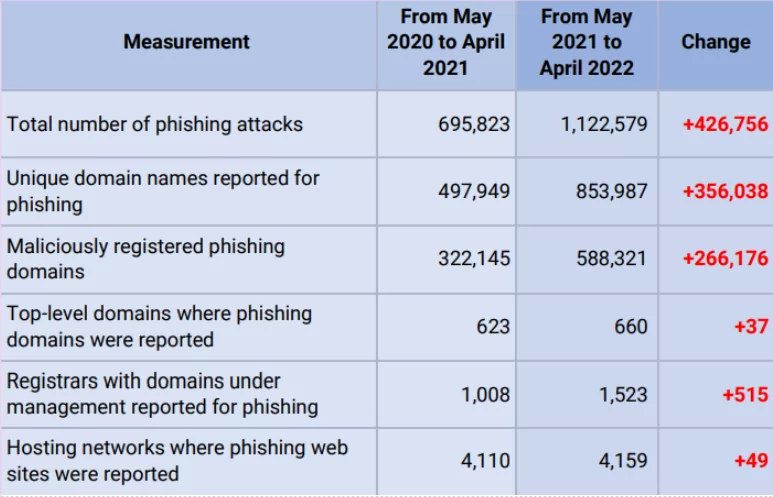
Legacy gTLDs are used in about half of all phishing attacks that target businesses. According to research, the most utilized Legacy gTLD in the group is .com, which is used in nearly 40% of attacks.
In a study by Interisle, they found the number of cryptocurrency-related phishing attempts increased 257% year to year. Crypto wallets were the most often targeted businesses, and over 80% of the generic top-level domains (gTLD) identified for phishing were maliciously registered.
The same study shows that phishers created domains specifically registered for their bitcoin attacks, usually including two or more brands or keywords. The following samples of URLs demonstrate this technique:
Strategies Followed by Phishers
Phishers are always looking for businesses that may have valuable user information, are just starting to gain popularity, or are unprepared to deal with phishing attacks.
Phishers also employ several strategies to attract users to their phishing pages, such as:
- a new product release,
- a problem with a social network account or financial account,
- an upcoming technology or service like cryptocurrency,
- information regarding a criminal investigation or tax violation,
- a necessary software upgrade to obtain.
Hackers Use SSL Certificates to Gain Trust
Examining URLs carefully and avoiding sites that don’t have an SSL certificate have been two of the main recommendations for avoiding phishing sites for many years. When people see that tiny padlock sign in the browser, it gives confidence that they will be secure and no one will steal their money.
A site with an SSL certificate and the HTTPS encryption protocol is identified by the URL prefix “HTTPS” (rather than “HTTP”).
However, using this method to identify suspicious websites is no longer effective. According to the APWG, 83% of the phishing sites reviewed in the first quarter of 2021 had SSL encryption enabled.
Top Targeted Brands
Researchers found that, between 1 May 2021 and 30 April 2022, phishers attacked over 2,000 firms or organizations, including banks, social media platforms, webmail, games, national tax services, universities, and cryptocurrency exchanges. The most targeted brands are listed below:
Google’s New TLDs: Commercial Opportunities and Security Risks
Google has released eight new top-level domains (TLDs). These TLDs have various purposes, including potential commercial value for law firms, usefulness for academics, and a potential security concern due to two TLDs being based on file extensions.
The eight new TLDs are:
- .dad
- .phd
- .prof
- .esq
- .foo
- .zip
- .mov
- .nexus
The cost of these new TLDs varies depending on the registration date. The earlier someone registers a domain, the more expensive it will be. Therefore, the most valuable domains will initially have a higher cost.
The .esq TLD is specifically designed for use by lawyers in the United States. It is an abbreviation for “esquire,” a title used for attorneys who have passed the bar exam in their state. The .esq TLD offers commercial potential for lawyers looking for appropriate domain names related to their profession. For more information about the registration, you can check here.
While exact match keyword domains are not necessary for ranking well on Google, they can help websites stand out in search engine results. The value of such domains lies in their ability to match users’ search queries and potentially improve conversion rates.
Potential Security Risks of .zip and .mov TLDs: Malware Delivery and Phishing
Among the new TLDs, the .zip and .mov domains, which are based on file extensions, may pose security concerns. These file extensions are often used to deliver trojans and malware, making their inclusion as TLDs a curious choice.
There is a concern that when someone mentions a .zip file in an email or on social media, some programs automatically turn it into a clickable link. This can be exploited by attackers who upload malicious files disguised as .zip files. The same issue applies to .mov files used for videos.
Using common file extensions as top-level domains (TLDs) can make phishing attempts easier and deceive unsuspecting users. For example, can you identify the malicious one among the following links?
- https://github[.]com/microsoft/vcpkg/archive/refs/tags/2023.04.15[.]zip
- https://github[.]com/microsoft/vcpkg/archive/refs/tags/@2023.04.15[.]zip
Although these two links may seem similar at first glance, the second one is actually the malicious link. When accessed, it will redirect you to the domain 15[.]zip, treating both “2023” and “04” as subdomains rather than part of the path. It is important to note that anything preceding the “@” (credential part) symbol will be ignored by browsers or any HTTP library. It is crucial not to underestimate the complexity of URI parsing.
While some programs convert .zip TLDs into clickable URLs, not all TLDs are treated this way, and users may have to manually add “https://” for non-standard TLDs to be clickable. Due to security concerns, some websites and programs are cautious about including such TLDs in their automatic linking features.
Despite potential security issues, these new TLDs provide a unique opportunity to register domain names that can be valuable for business, professional use, or even as gifts, such as the .dad TLD.
How to Defend Against Phishing Attacks
It is essential to understand that phishing can occur from any source, regardless of how secure a website may seem. Monitoring network activity and managing your digital assets to keep the attack surface as small as possible are the only ways to ensure that phishing won’t seriously impact your company. The AI-enabled SOCRadar Digital Risk Protection platform examines millions of domains from most of the top domain registrars to find malicious domains targeting your brand and your whole company network. While keeping your online presence secure, real-time alerts will help you to be informed before your domains and SSL certificates expire. Also, the following recommendations can help you protect yourself from phishing attacks:
- Using security software to protect your computer.
- Enabling auto-updates for software to protect your smartphone.
- Utilizing multi-factor authentication to secure your accounts.
- Making a backup of your data to protect it.
- Informing employees about phishing.
There’s a tool available to protect yourself against phishing scams. Check here whether the emails you receive every day come from a secure source.




































