Misconfigurations in Google Kubernetes Engine (GKE) Lead to a Privileg...
Misconfigurations in Google Kubernetes Engine (GKE) Lead to a Privilege Escalation Exploit Chain A recent Unit 42 investigation revealed a dual privilege escalation chain impacting Google Kubernetes E...

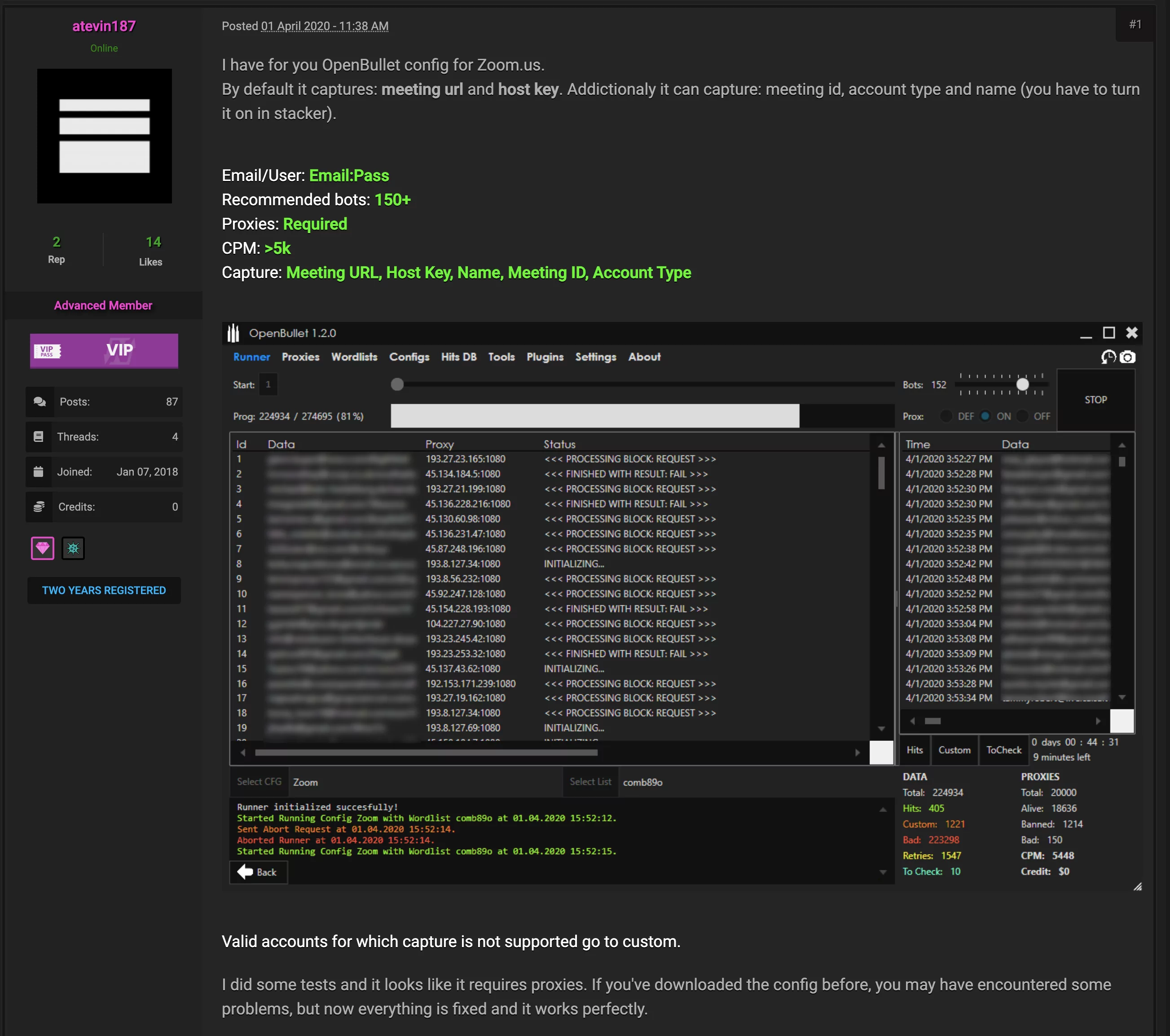
Operation Triangulation: ‘’Most Sophisticated Attack Chain Ever Seen"...
Operation Triangulation: ‘’Most Sophisticated Attack Chain Ever Seen” The cyber security landscape has recently been abuzz with discussions about Operation Triangulation, a sophisticated and mul...