Major Cyberattacks in Review: April 2023
In April 2023, several cybersecurity incidents were reported across various industries. These included supply chain attacks, data breaches, and cryptocurrency thefts. It’s important to keep up-to-date on the nature of these attacks, their implications, and the steps being taken to minimize their impact.
In this blog post, we will take a look at some of the major cyberattacks that took place in April 2023.
North Korean Hackers Behind 3CX Supply Chain Attack Using TAXHAUL Malware

The effects of the major 3CX supply chain attack are still visible; on April 11, 3CX confirmed that the attack was carried out by a North Korean hacking group. The hacker group UNC4736 used the malware strain TAXHAUL to compromise the 3CX systems. Mandiant’s investigation into the 3CX supply chain exploit scheme revealed that the initial intrusion vector was a malware-infected package from another website. The package was distributed using an altered installer for X_TRADER, a software package available on Trading Technologies’ website. This is the first time a software supply chain attack has been followed by another, according to researchers.
You can read our blog here to learn more about the SmoothOperator Supply Chain Attack.
American Bar Association Hacked, 1.4M Member’s Login Credentials Compromised

The American Bar Association (ABA), the largest association of lawyers and legal professionals globally, suffered a data breach in March 2023.
A hacker gained access to the ABA’s network and obtained older credentials of 1.4 million members, according to a notification email sent to affected members.
The compromised credentials were for a legacy member system that was decommissioned in 2018.
While the ABA claims that the credentials were hashed and salted, making them more secure, there are still concerns that the threat actors could abuse them over time, especially since many passwords may have been default ones assigned by the ABA.
ICICI Bank Leaks Sensitive Data of Millions of Clients Due to Misconfigured Systems

ICICI Bank, an Indian multinational valued at more than $76 billion, recently leaked millions of records containing sensitive information about its clients.
The leaked data included bank account details, bank statements, employees’ and candidates’ CVs, full names, dates of birth, home addresses, phone numbers, emails, personal identification documents, and credit card numbers.
Researchers discovered that the leak was caused by the misconfiguration of the bank’s systems, known as a Digital Ocean bucket. This bucket contained more than 3.6 million files that belonged to ICICI Bank. The bank has since fixed the issue, but the leak could still be used for identity theft and fraud. The financial and insurance industries are some of the most targeted by cybercriminals due to the valuable data they hold.
Philippine Police Database of 1.2 Million Records and 800 GB of Information Breached
A cybersecurity researcher has reported a data breach in the Philippines involving a database containing more than 1.2 million police records and 800 gigabytes of information on people who work or applied for employment in law enforcement.
The breach includes highly sensitive information such as passports, birth and marriage certificates, academic transcripts, security clearance documents, and tax identification numbers of law enforcers. The database was available for public access for at least six weeks.
The breach could have serious consequences, including identity theft, phishing attacks, and other malicious activities.
DeFi Protocol Hundred Finance Hacked, Loses $7M In Assets

Hundred Finance, a multi-chain lending protocol, has suffered a security breach on the Optimism layer-2 scaling network, resulting in the theft of around $7 million worth of assets.
The hacker inflated the exchange rate for hWBTC by donating 200 WBTC, which allowed them to drain Hundred Finance’s lending pools. This was achieved by manipulating the exchange rate between ERC-20 tokens and hTokens, which enabled the exploiter to withdraw more tokens than they had initially deposited.
This is not the first time the protocol has been hacked; it previously lost around $6.5 million worth of ETH in a reentrancy attack. The DeFi space continues to face escalating security threats, with DeFi protocols accounting for 82% of all stolen crypto assets, equivalent to $3.1 billion in losses in 2022.
Bitrue Hot Wallet Exploit Results in $23M Theft

Bitrue, a cryptocurrency exchange, experienced an exploit in one of its hot wallets but was able to address it quickly and prevent the further exploitation of funds.
The attackers were able to withdraw assets worth approximately $23 million USD in ETH, QNT, GALA, SHIB, HOT, and MATIC. The affected hot wallet contained less than 5% of Bitrue’s overall funds, and the rest of the wallets remain secure and have not been compromised.
Bitrue has suspended all withdrawals temporarily to conduct additional security checks.
The exchange will compensate all identified users affected by this incident in full. Bitrue assures its customers that it is committed to maintaining transparency throughout the process and thanks them for their continued support.
Over a Million Invoices Exposed in Unsecured NorthOne Bank Database

A cybersecurity researcher named Jeremiah Fowler discovered a database containing a large number of PDF documents that were not password protected.
The PDFs included invoices from individuals and businesses who used an app to pay for products and services. The invoices contained sensitive information such as names, email addresses, physical addresses, phone numbers, and tax information.
Upon further investigation, it was discovered that the database belonged to NorthOne Bank. It is unclear how long the records were exposed or if anyone else had access to them.
The researcher also estimated that there were over a million files in the database that were marked as “production,” and a random sampling of 1,000 invoices revealed invoice amounts ranging from as low as $60 to over $10,000 for various services.
Hyundai Suffers Data Breach

Hyundai experienced a data breach that affected French and Italian car owners and customers who had booked a test drive. Cyber attackers gained unauthorized access to their email addresses, physical addresses, telephone numbers, and vehicle chassis numbers, but not financial data.
It is unclear how many people were affected, but those who were have been advised to be careful of any contact attempts from Hyundai Italia or other entities of the Hyundai Group. To address the issue, the company has taken impacted systems offline, hired external cybersecurity experts, and informed privacy watchdogs.
Cybercriminals Breached Kodi, Exposing Data of 400,000 Users
Kodi, a well-known provider of open-source home theater software, experienced a data breach that was discovered last week. In February 2023, a malicious actor advertised a dump of Kodi’s user forum, MyBB, on cybercrime forums, and posted the data of 400,000 Kodi users on various hacker forums.
The attackers gained access to the web-based MyBB admin console twice by exploiting an inactive administrator account. They created database backups and downloaded available nightly full backups, including all public and staff forum posts, user messages, and user data, such as usernames, email addresses, and encrypted passwords.
Anonymous Sudan Targets Top Hospitals in Hyderabad, India
The pro-Islamic hacktivist group “Anonymous Sudan” has targeted several top hospitals and healthcare institutes in Hyderabad and other cities in India. This group is known for politically motivated distributed denial-of-service (DDoS) attacks. They have previously targeted Indian seaports and airports, and in March 2023, they attacked France’s hospitals, universities, and airports. According to experts, the attacks are not hacking, but rather multiple users accessing the website simultaneously, leading to a denial of service. Falcon Feeds, a cyber threat intelligence platform, condemned the group’s actions, stating that they are targeting India’s prestigious medical institutes and largest public sector banks.
Yum! Brands Reports Data Breach Following Ransomware Attack

Yum! Brands, the parent company of KFC, Pizza Hut, and Taco Bell, is sending breach notification letters to an undisclosed number of individuals whose personal information was stolen in a ransomware attack that occurred on January 13.
Although Yum! Brands initially claimed that no customer information was stolen, it now acknowledges that the attackers stole some personal information of individuals, including names, driver’s license numbers, and ID card numbers.
The company has found no evidence that the data was used for identity theft or fraud. The ransomware attack forced Yum! Brands temporarily shut down around 300 restaurants in the UK, but the company stated that the attack did not have a material adverse impact on its business or financial results.
Samsung Employees Leak Sensitive Data Via ChatGPT

Samsung employees have inadvertently leaked confidential information to OpenAI’s chatbot service, ChatGPT.
The employees have shared internal documents such as meeting notes and source code with the chatbot, which uses the data to train and improve its experience. This has resulted in three data leaks caused by Samsung employees, according to Techradar.
One employee converted meeting notes into a presentation using ChatGPT, which contained information Samsung did not want to share externally. Samsung has now started developing its own AI for internal use, warning employees of the risks associated with using third-party chatbots, which cannot prevent data leaks. It is unclear if Samsung has requested the deletion of the data shared with OpenAI.
Online Marketplace Z2U Suffers Data Leak Exposing 600K Sensitive Records

Chinese online marketplace Z2U, which sells discounted accounts, license keys and malware, suffered a data leak exposing hundreds of thousands of sensitive records.
Security researcher Jeremiah Fowler discovered the non-password protected database and found 600,000 “customer support attachments” with images of individuals holding credit cards, passports and other ID documents.
The database also included payment transactions, user account logins, emails and passwords, order confirmations and other sensitive information. The website claims to be a digital marketplace trading platform for gamers, but Fowler discovered a range of dubious trading activity outside the gaming world.
Uber and Western Digital Suffer Data Breaches
Two popular companies, Uber and Western Digital, experienced security incidents that resulted in data breaches. Uber had a data breach when a third-party law firm, Genova Burns, was hacked, resulting in unauthorized access to drivers’ personal information such as names, social security numbers, and tax identification numbers. Meanwhile, Western Digital also suffered a data breach on March 26 when an unauthorized third party disrupted its operations and accessed some of its information.
Canadian Directory Publisher Yellow Pages Group Hit by Ransomware Attack

The Yellow Pages Group (YP), a Canadian directory publisher, was targeted in a cyber attack that resulted in the exposure of confidential documents and data on a leak site.
The Black Basta ransomware and extortion gang claimed responsibility for the attack, which occurred in March 2023, according to information published by the group. YP reported that employee data and some limited information from business customers may have been compromised, and the leaked documents contain sensitive information such as tax documents, purchase agreements, and budget forecasts.
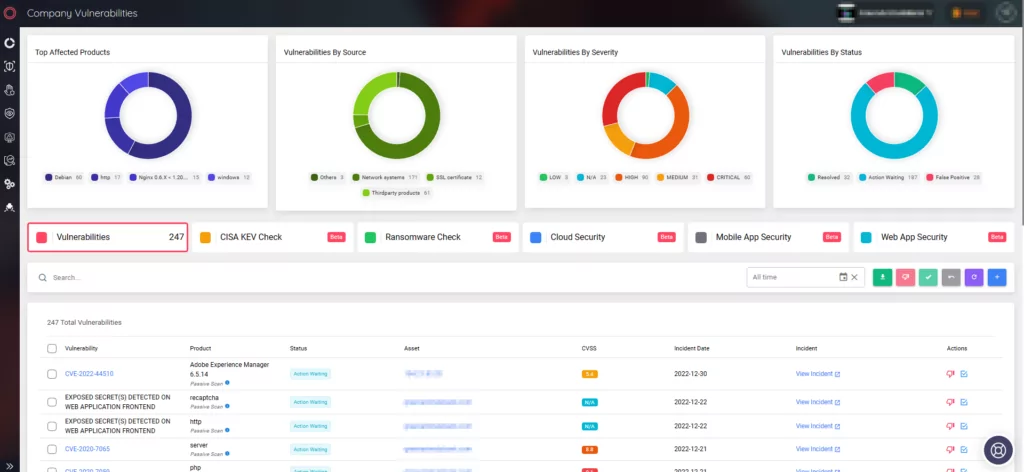
By utilizing SOCRadar’s platform, organizations can comprehensively understand the threat landscape, proactively address potential risks, and improve their overall cybersecurity posture.





































