What is the Risk-Based Approach to Cybersecurity?
Cybersecurity is one of the main topics for business managers in today’s world. The approach to cyber risks has changed from “maturity based” to “risk-based” over time. Managerial leaders want to know the cyber threats to their organizations and how to administrate them. Almost everyone, administrators, customers, and the general community, approve of the severity of cybersecurity, and it needs serious attention.
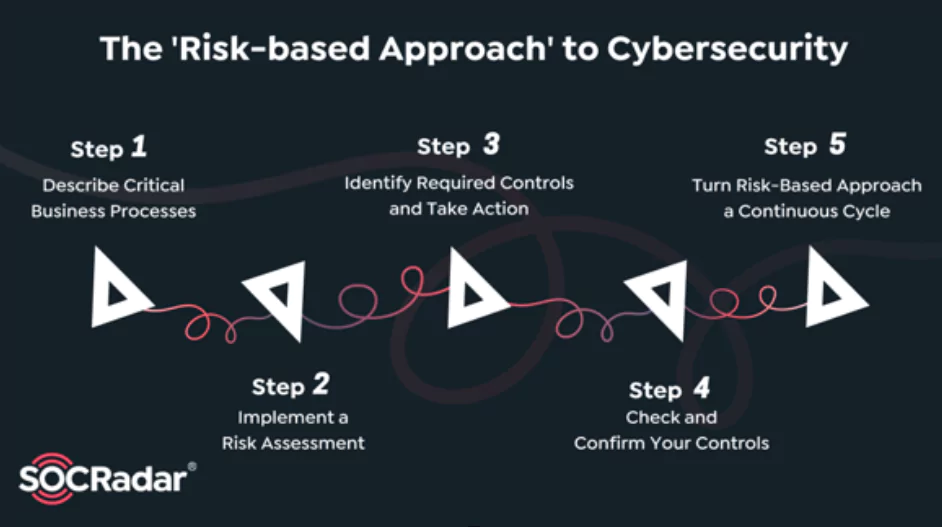
Moreover, analyzing risks is not enough; experts have to focus on how to reduce these risks. So, what is a risk-based approach? The risk-based approach is a cybersecurity technique that describes, assesses cyber threats, and finds priority to defend against them. We can narrate a risk-based approach in five main categories.
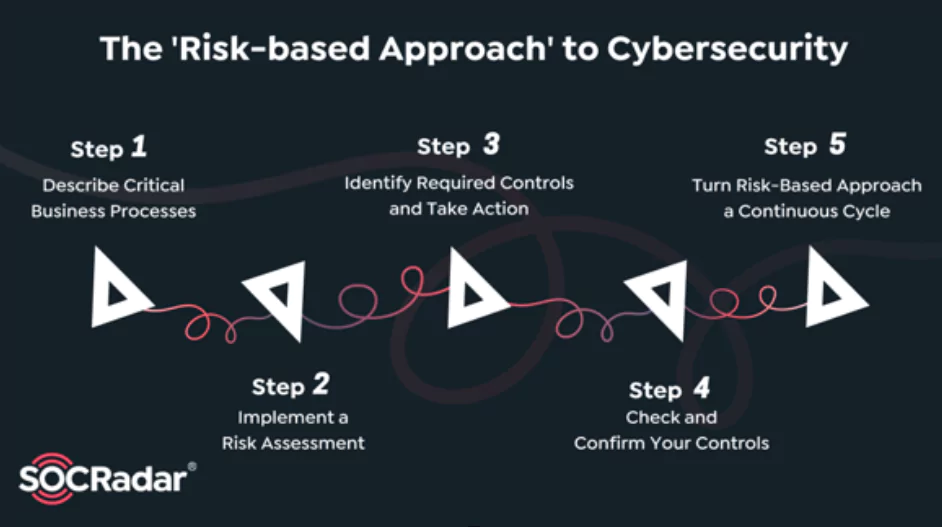
Risk-Based Approach in 5 Steps
1. Describe Critical Business Processes
The first step of risk-based cybersecurity is to notice the potential for losses, such as financial, reputational, productivity-related facilities, and applications in their database. Each element of cyber risk has to be prioritized in order of importance.
So, awareness of losing potential in the digital domain is critical in evaluating possible risks. These potential cyber-attacks may result in the physical domain also. After prioritizing cyber-risks, we have to think about the results of a possible hack.
How is the business continuity affected if these functions are hindered somehow? Evaluating this possibility is one of the main steps to analyzing the risk. Examining all the options, knowing the priorities, and describing critical business processes help you realize your environment and what is most important before taking any steps to protect it.
2. Implement a Risk Assessment
The risk assessment is a process that brings to light all vulnerabilities and describes all possible threats. It is used for identifying risks and then scaling and prioritizing them. The result is one of the most significant advantages of this approach, assembling personalized data centered on your organization.
Ready-made protection tools are generalized for all the possible cyber-risks; there is no personalized protection. Therefore, this generalized protection may not apply to your digital threats. This situation makes risk-based protection tools more effective in today’s world.
After detecting the possible risks, all data should be collected in one place, called the risk register. The risk register supplies a significant starting point for protection procedures. The risk register provides strategic resources to relieve risks. These possible threats analyzed by “risk-based” functions are used as a map by cybersecurity experts.
3. Identify Required Controls and Take Action
In this phase, you identify, adapt, implement, and take responsibility for measures that would reduce the inherent risk. A controller is an activity-based statement that describes how to reduce or eliminate security threats. NIST 800-53, CIS, HITRUST CSF, ISO 27001/27002, COBIT, and PCI DSS are examples of cyber security control frameworks. Those are pre-packaged security controls that can be adjusted to your individual’s particular threats.
Personalized risks make it much easier for an organization to adjust control options to specific vulnerabilities and threats. Because the entire decision-making system is documented, it also allows the company to implement compensatory controls. The documentation shows that the organization recognizes the problem that the control is developed to fix and that alternative compensating controls have been adequately implemented depending on a cost-risk analysis.
Identifying and implementing the appropriate or required controls gives a framework and an opportunity to update or develop policies and procedures that cement and explain the organization’s cybersecurity vision and priorities. Similarly, it allows for conversation with specific individuals who “own” the process, including support from critical mid-level management. The risk-based approach offers leadership and management a compelling rationale to adapt and adopt and the potential repercussions of doing nothing.
4. Check and Confirm Your Controls
Your security controls must always be checked and confirmed after they have been implemented. Testing techniques, additional risk assessments, vulnerability management tests, business continuity exercises, internal audits, and compliance control assessments are examples of different testing forms.
Testing and validating your controls ensure that they work and provide the necessary security and allow you to incorporate newly established security controls when they are reviewed regularly. You can now acquire a risk value score termed residual risk, which is logged and added to your risk register for future analysis and prioritization. Your risk rating could fall due to the investment in new control, suggesting a healthier risk profile overall. It is essential to keep track of and report on your testing and validation efforts.
Executive leadership will be able to see your progress, and regulatory authorities will see your compliance if you have a sound reporting system in place. Effective reporting also sets the groundwork for gap remediation and escalation processes, immortalized in the final phase.
5. Turn Risk-Based Approach into a Continuous Cycle
Your goal in this final phase is to turn Stages 1-4 into a repeatable business process. At least yearly, risk assessments should be undertaken, and remediation efforts should be implemented, monitored, and recorded in the risk register. Internal workers should also be able to identify and disclose potential risks to the organization through reporting systems. Managers and other staff frequently have vital insights into vulnerabilities or compliance issues that the risk team may be unaware of.
As an organization commits to its cycle, process gaps will inevitably emerge due to poorly implemented controls or oversights in the risk identification process. You can analyze and reevaluate such gaps by using the risk methodology in Stage 2. Exceptions and exception management take a similar approach. If process owners cannot follow the policy, a risk assessment evaluating the potential consequences of non-compliance can be undertaken. This method will result in a more consistent and high-quality exception management procedure.
Following a cycle can help ensure any new vulnerabilities or threats are discovered and treated consistently and timely, reducing the risk of severe concerns going unnoticed. Employees can raise concerns, inform the organization, and evaluate and assess the damage in the event of exploitation at this phase. Over the lifecycle of the Risk-Based Approach, continuous governance will encourage accountability for control implementation and assessment.
It offers escalation routes for difficult or non-compliant stakeholders and guarantees control adaption uniformity. Finally, the cycle allows you to update or create relevant policies or procedural documents and regularly convey changes to the group.
Taking a risk-based approach to cybersecurity, rather than a compliance-first or checklist approach, will result in a personalized risk score, prioritized gaps, tailored controls, and a more robust cycle for addressing new risks and vulnerabilities.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Get free access.



































