
IBM X-Force: Now Threat Actors are Faster and Hard to Detect
Over the last two years, our world has undergone a transformation that we never expected. New business models and ways of working have changed irreversibly. Digitalization, which almost every industry has to adapt to, brought many developments in cyber security. Threat actors quickly got into the process, evolved, and emerged with new cyber attack trends.
IBM has released the 2022 X-Force Threat Intelligence Index, which shares broad cyber threat insights for cybersecurity researchers, policymakers, media, and industry professionals. We provide a summary of the report, which includes detailed data on common attack types, supply chain vulnerabilities, and top threat actors.
What are the Top Attack Types and Infection Vectors in X-Force Report?
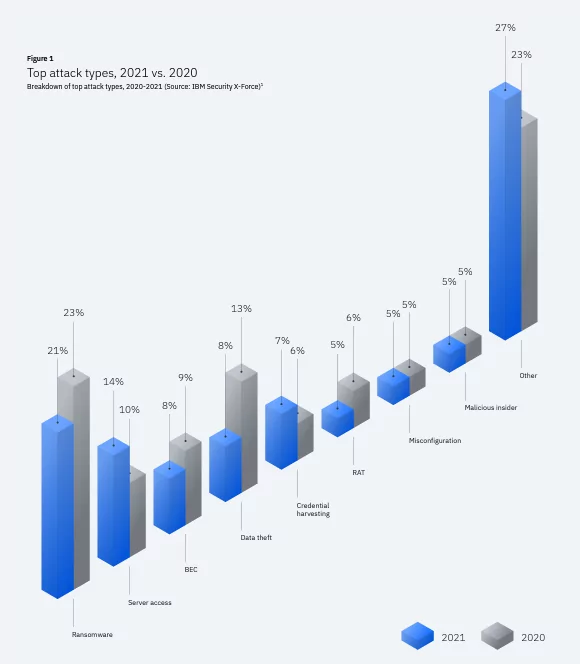
According to X-Force’s findings, 2021 was a year in which ransomware was at the top, just like the last three years. Threat actors still attack the most with ransomware, although the data is down by 2% according to 2020.
Ransomware attacks are followed by server access with a rate of 14%, while BEC (business email compromise) and data theft share the third place with a rate of 8%.
According to X-Force’s observations, the frequency of ransomware attacks was highest in May and June. Attacks dwindle in late summer and fall, driven by operations against DarkSide and Babuk in May, Avaddon in June, and REvil in October.
REvil was involved in 37% of ransomware incidents in 2021. Ryuk follows with 13%. These two names stand out with their longest-running ransomware campaign since 2018.
The most commonly used attack vectors by threat actors are phishing and vulnerability exploitation. In 2021, 78% of attacks appeared to have been carried out through these vectors. Many ransomware groups are known to use phishing emails.
What were the Top Threat Actors of 2021?
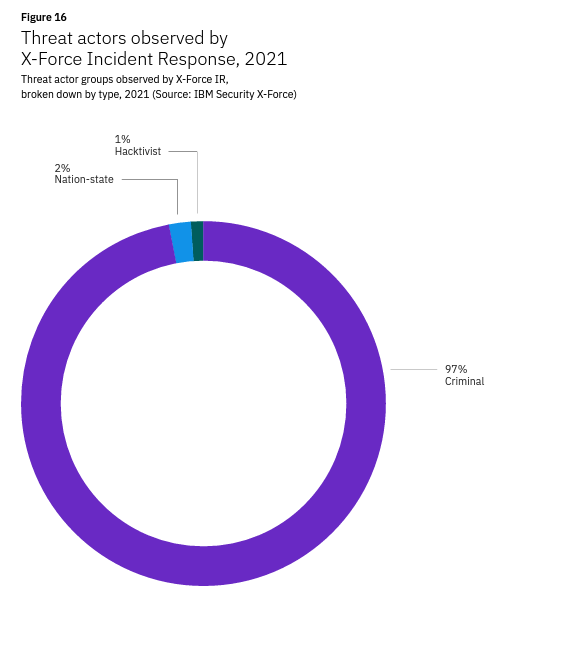
Threat actors may have different motivations. Some are cyber-espionage and state-sponsored groups, while others are purely for-profit. A tiny part of the threat actors carries out attacks to point out social issues and to have their say on current politics.
In 2021, profit-oriented cybercrime seemed to be more common as in previous years. While 97% of the attacks are carried out for criminal purposes, 3% share state-sponsored and hacktivism-oriented attacks.
What are the Trends in Malware Development?
Threat actors continue to develop malware that is difficult to detect and can be more effective on the systems they infiltrate. Here are some of the developments X-Force observed in 2021:
- Ransomware started developing different encryption techniques to evade detection systems. For example, intermittent encryption encrypts individual data blocks instead of the entire system for faster encryption.
- Malware began using more sophisticated code obfuscation techniques to hide its true purpose. Malware developers have tried programming languages like PureBasic and Nim to make reverse engineering more difficult.
- According to X-Force’s analysis, malware infecting cloud environments has shifted from targeting Linux systems to Docker containers.
- In addition to using legitimate scripts to launch fileless malware, threat actors have started using Ezuri, an open-source encryptor written in Golang.
What are Cybersecurity Industry Trends in 2021?
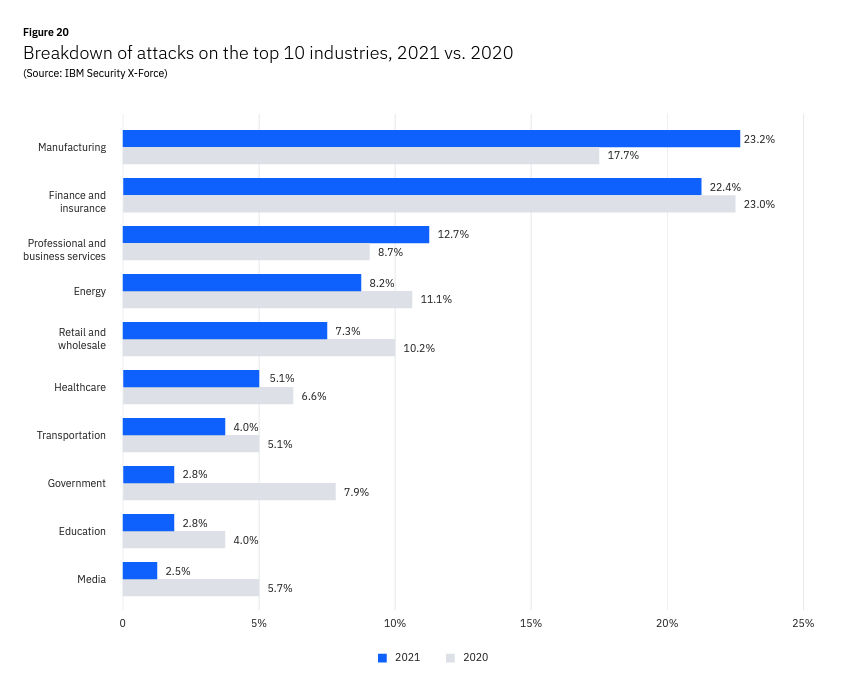
In the X-Force Threat Intelligence Index report, a first in five years, the most targeted sector is the manufacturing sector, not finance and insurance. The report says this may be due to the supply chain pressure created by the COVID-19 pandemic.
According to the report, the most targeted sectors are as follows:
- Manufacturing
- Finance and insurance
- Professional and business services
- Retail and wholesale
- Healthcare
- Transportation
- Government
- Education
- Media
For the full X-Force Threat Intelligence Index 2022 report, click here.
Discover SOCRadar® Free Edition
With SOCRadar® Free Edition, you’ll be able to:
- Discover your unknown hacker-exposed assets
- Check if your IP addresses tagged as malicious
- Monitor your domain name on hacked websites and phishing databases
- Get notified when a critical zero-day vulnerability is disclosed
Free for 12 months for 1 corporate domain and 100 auto-discovered digital assets.
Get free access.


































