What Do You Need to Know About New SAMA Principles?
The Kingdom of Saudi Arabia (KSA) has launched a digital transformation program focusing on the banking industry. With the growing digitization of financial services, securing the availability of sensitive data, transactions, and services has become a priority for the Kingdom of Saudi Arabia (KSA) financial industry as a crucial aspect of its innovation and security.
The Central Bank of Saudi Arabia, also known as the Saudi Arabian Monetary Agency (SAMA), has established a Cyber Security Framework (CSF) that controls the cybersecurity activities of SAMA’s financial institutions to assist in secure financial services and prevent cyber threats in this sector.
The Framework applies to all SAMA-regulated Member Organizations, such as All Banks; All Insurance and/or Reinsurance Companies; All Financing Companies; All Credit Bureaus; The Financial Market Infrastructure in Saudi Arabia.
The Saudi Monetary Authority based the rule on industry-standard frameworks such as:
- National Institute of Standards and Technology (NIST) Framework for Improving Critical Infrastructure Cybersecurity (NIST CSF)
- Payment Card Industry Data Security Standard (PCI DSS)
- ISO 27001/27002 Information Security Management Standards
- Information Security Forum-Standard of Good Practice for Information Security
- Basel II (Basel III, since 2019) International Convergence of Capital Measurement and Capital Standards
SAMA CTI Principles
In March 2022, SAMA announced the Cyber Threat Intelligence (CTI) Principles as part of the CSF. As a result, cyber threat intelligence has become a requirement for Saudi financial institutions to achieve SAMA Cybersecurity Framework Compliance.
Cyber Threat Intelligence (CTI) allows organizations to gather, evaluate, and exchange data on cyber threats, letting them detect cyber-attacks and protect critical information assets. The Cyber Threat Intelligence (CTI) Principles describe best practices for creating, analyzing, and sharing threat intelligence in order to improve the detection and mitigation of cyber threats relevant to the KSA financial sector.
SAMA has covered all of the principles identified in four categories: Core, Strategic, Operational, and Tactics and Techniques. The Core CTI Principles are a prerequisite for CTI implementation and include the activities required to plan, produce and disseminate CTI. The Strategic CTI Principles contain actions that must be taken to identify threat actors‘ purpose, motivation, and intentions. The Operational CTI Principles include the steps to be taken by threat actors to determine behavior and techniques. The Technical and Tactical CTI Principles contain actions to be taken to identify technical components and indicators of cyber-attacks.
Core Cyber Threat Intelligence Principles
| Principle 1: | Define roles and responsibilities |
| Principle 2: | Define threat intelligence planning and collection requirements |
| Principle 3: | Select and validate relevant sources |
| Principle 4: | Collect data through intelligence sources |
| Principle 5: | Define specific standard operating procedures (SOPs) |
| Principle 6: | Proses and classify information |
| Principle 7: | Analyze information |
| Principle 8: | Share intelligence |
| Principle 9: | Deliver actionable threat intelligence |
| Principle 10: | Continuously improve methods of intelligence |
| Principle 11: | Integrate CTI |
Strategic Cyber Threat Intelligence
| Principle 12: | Identify a cyber threat landscape |
| Principle 13: | Identify strategic cyber-attack scenarios |
| Principle 14: | Elaborate Requests for Information (RFIs) and Tailored Threat Assessments |
Operational Cyber Threat Intelligence
| Principle 15: | Define the attack chain |
| Principle 16: | Identify TTP |
| Principle 17: | Identify malware and tools |
Technical And Tactical Cyber Threat Intelligence
| Principle 18: | Collect IoCs |
| Principle 19: | Monitor and report vulnerabilities |
SAMA Principles and Cyber Threat Intelligence
Cyber threat intelligence aims to assist organizations in understanding the risks related to cyber threats. These threats are reported with the intelligence activities and then reviewed by CTI analysts to give particular protective techniques to aid in the organization’s active defense.
In line with SAMA principles, financial institutions can use CTI to increase their visibility in the threat landscape and monitor threat actors, tools, tactics, and procedures (TTP) to protect themselves and their clients. Using CTI helps organizations understand how attackers operate, how they function, and what strategies they employ to design a security strategy against them. Using CTI also allows identifying risk dynamics and consequences, improving security plans and structures, and reducing attack potential to limit damage and protect the network. By using CTI, security breaches can be prevented from disclosing confidential information. In addition, CTI helps to detect Forgotten Assets, and Monitor Attack Surface in Real-time; and determine the blind spots by following the changing attack surface all the time.
Financial institutions can use CTI tools and platforms to achieve SAMA CTI principles to save time and personnel resources. SOCradar offers a practical solution as an extended threat intelligence platform in this context.
Execute SAMA Principles with SOCRadar XTI
SOCRadar combines attack surface management, digital risk protection, and threat intelligence capabilities to support SOC teams. SOCRadar’s ThreatFusion provides actionable insights into future cybersecurity threats with a big data-powered threat investigation module to assist in searching for deeper context, real-time threat investigation, and analysis.
SOCRadar’s RiskPrime combines technologies like as instant phishing domain identification, internet-wide scanning, and compromised credential detection.
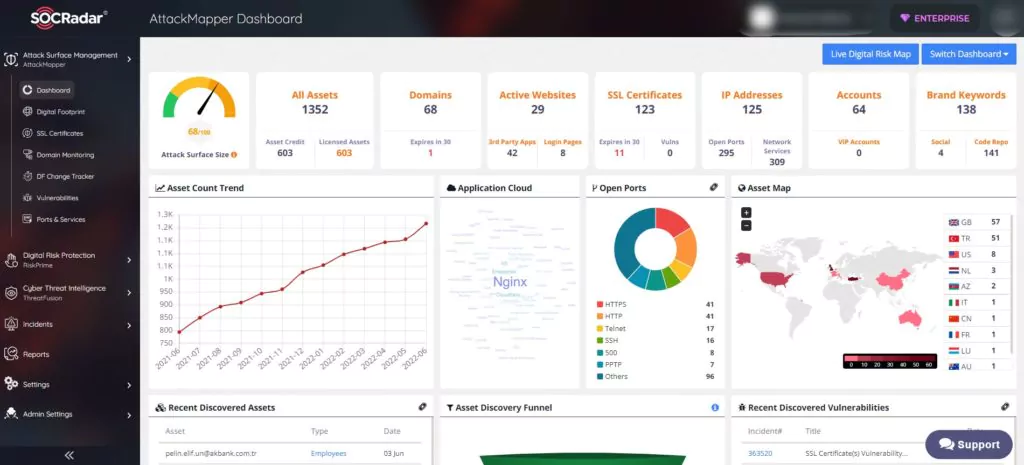
SOCRadar continually identifies the public-facing digital assets to remove blind spots and shadow IT threats and then informs SOC teams with timely and targeted intelligence. SOCRadar’s AttackMapper offers direct visibility into all internet-facing technical assets in use, as well as assets linked to IP, DNS, Domain, and cryptographic infrastructure by advanced internet-wide monitoring algorithms.
Unlike traditional CTI products, SOCRadar’s Unified structure and Extended Threat Intelligence (XTI) structure is an effective solution for fraud prevention and brand protection.
The role-based structure creates in alarms allows forwarding the fraud email structure to the security teams without connecting to the platform. In addition, fraud systems can be fed with relevant alarms with the filtering structure.
Organizations’ security Teams can monitor and control the relevant alarms and dashboards on the platform. In this way, security Teams can take action regarding alarms instantly and turn off alarms.
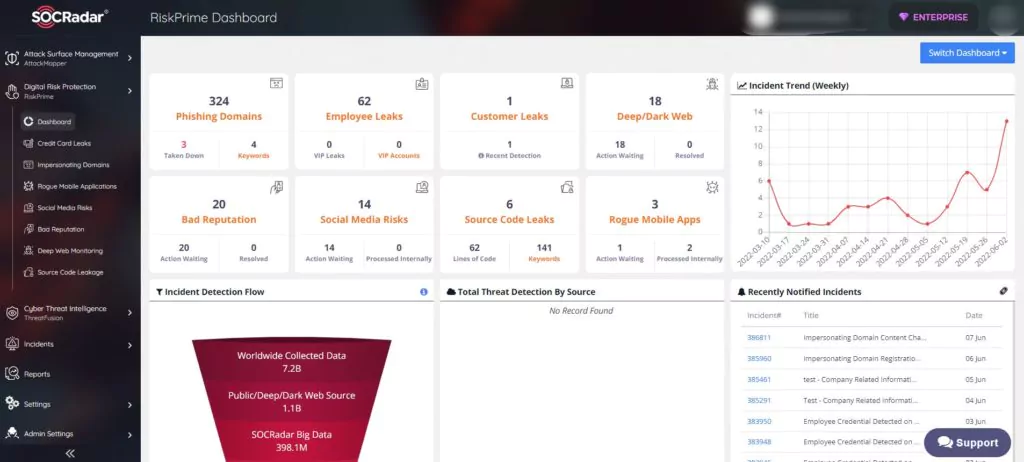
SOCRadar RiskPrime module (Digital Risk Protection); provides the leaked credit card information from the database and follows the fraud activities on the dark & deep web, black markets, IRC channels, Telegram, etc.
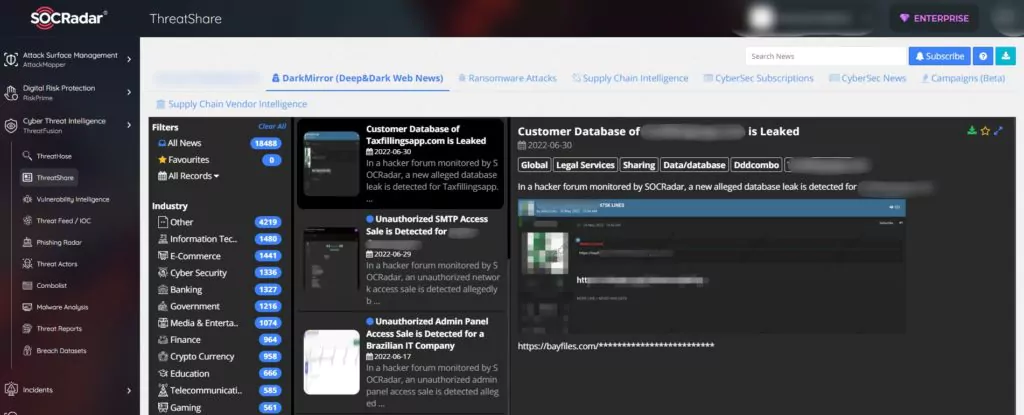
The ThreatShare section on the SOCRadar ThreatFusion module enables access to analyze the fraud field for banks and the news on the dark & deep web.
SAMA CTI principles have made cyber threat intelligence mandatory for KSA financial institutions to reach SAMA Cyber Security Framework Compliance. SAMA member organizations can benefit from extended threat intelligence solutions like SOCRadar to successfully execute the SAMA CTI principles, allowing them to improve their security perceptions.
For our Saudi Arabian customers, rest assured that your data is geographically located within Saudi Arabia, ensuring compliance with local regulations and standards.
REFERENCES:
- https://www.sama.gov.sa/en-US/RulesInstructions/CyberSecurity/Financial%20Sector%20Cyber%20Threat%20Intelligence%20Principles%20V1.0.pdf
- https://www.sama.gov.sa/en-US/Laws/BankingRules/SAMA%20Cyber%20Security%20Framework.pdf
- https://www.arabianbusiness.com/industries/technology/resecuritys-cyber-threat-intelligence-for-sama-compliance-protects-saudis-financial-services-sector
Use SOCRadar® FOR FREE 1 YEAR
With SOCRadar® Free Edition, you’ll be able to:
- Prevent Ransomware attacks with Free External Attack Surface Management
- Get Instant alerts for fraudulent domains against phishing and BEC attacks
- Monitor Deep Web and Dark Net for threat trends
- Get vulnerability intelligence when a critical zero-day is disclosed
- Get IOC search & APT tracking & threat hunting in one place
- Get notified with data breach detection
Free for 12 months for one corporate domain and 100 auto-discovered digital assets.
Get Free Access.