Severe Vulnerabilities in Moby BuildKit and OCI runc: CVE-2024-23651, ...
Severe Vulnerabilities in Moby BuildKit and OCI runc: CVE-2024-23651, CVE-2024-23652, CVE-2024-23653, CVE-2024-21626 The Cybersecurity and Infrastructure Security Agency (CISA) has issued an alert reg...
Harnessing SIEM Solutions With Threat Intelligence
Harnessing SIEM Solutions With Threat Intelligence Organizations strive to implement security measures and remain current to defend against the escalating number of cyber attacks. However, staying ahe...

RE#TURGENCE: A Deep Dive into Turkish Hackers’ Campaign Targeting MSSQ...
RE#TURGENCE: A Deep Dive into Turkish Hackers’ Campaign Targeting MSSQL Servers Financially motivated Turkish threat actors have emerged with a significant development in cyber threats, introducing a ...

Vulnerability in Ivanti Connect Secure, Policy Secure, and Neurons for...
Vulnerability in Ivanti Connect Secure, Policy Secure, and Neurons for ZTA Exploited (CVE-2024-21888, CVE-2024-21893) [Update] March 11, 2024: “Rapid Exploitation of CVE-2024-21888 and CVE-2024-...

GNU C Library Affected by Several Vulnerabilities, Attackers Could Obt...
GNU C Library Affected by Several Vulnerabilities, Attackers Could Obtain Root Access (CVE-2023-6246) Researchers have recently discovered several vulnerabilities in GNU C Library (glibc), impacting v...

Llama Guard: A Potent Ally for Threat Detection in LLM Environments
Llama Guard: A Potent Ally for Threat Detection in LLM Environments In a previous article, we delved into CyberSecEval, a benchmark created by Meta to tackle primary security concerns surrounding Larg...

Dark Web Monitoring: A Vital Tool for MSSPs
Dark Web Monitoring: A Vital Tool for MSSPs In today’s digital age, data breaches, cyber threats, and information security are at the forefront of every organization’s concerns. Managed Security Servi...

Top 10 Custom GPTs for Cybersecurity
Top 10 Custom GPTs for Cybersecurity Custom GPTs in cybersecurity represent a groundbreaking fusion of AI and information security. These specialized GPT models are tailored to address diverse cyberse...

Cybersecurity Predictions: What Trends Will Be Prevalent in 2024?
Cybersecurity Predictions: What Trends Will Be Prevalent in 2024? The evolving digital environment and expanding attack surface demand vigilant adaptation to stay one step ahead of adversaries. Recogn...
A for APT: Criteria for Classifying Cyber Threats
A for APT: Criteria for Classifying Cyber Threats The term “Advanced Persistent Threat” (APT) has emerged as a critical concept, necessitating a nuanced understanding and accurate classification. APTs...
Atlassian’s Confluence Data Center and Server Affected by Critical RCE...
Atlassian’s Confluence Data Center and Server Affected by Critical RCE Vulnerability, CVE-2023-22527: Patch Now [Update] August 29, 2024: “Cryptojacking via CVE-2023-22527” [Update] January 25, 2024: ...
Top 10 RCE Vulnerabilities Exploited in 2023
Top 10 RCE Vulnerabilities Exploited in 2023 Cybersecurity unfolds in a continuous interplay between defenders and threat actors – an ever-evolving quest for software vulnerabilities, with both partie...

EU & US Credit Cards, 750M Indian Mobile Data at Risk; Subway Hit by L...
EU & US Credit Cards, 750M Indian Mobile Data at Risk; Subway Hit by LockBit The SOCRadar Dark Web Team identified critical incidents in the cyber threat landscape over the last week. These includ...

Securing the Chain: How Threat Intelligence Strengthens Third-Party Ri...
Securing the Chain: How Threat Intelligence Strengthens Third-Party Risk Management Businesses increasingly face new cybersecurity incidents that are disruptive, costly, and can significantly damage t...
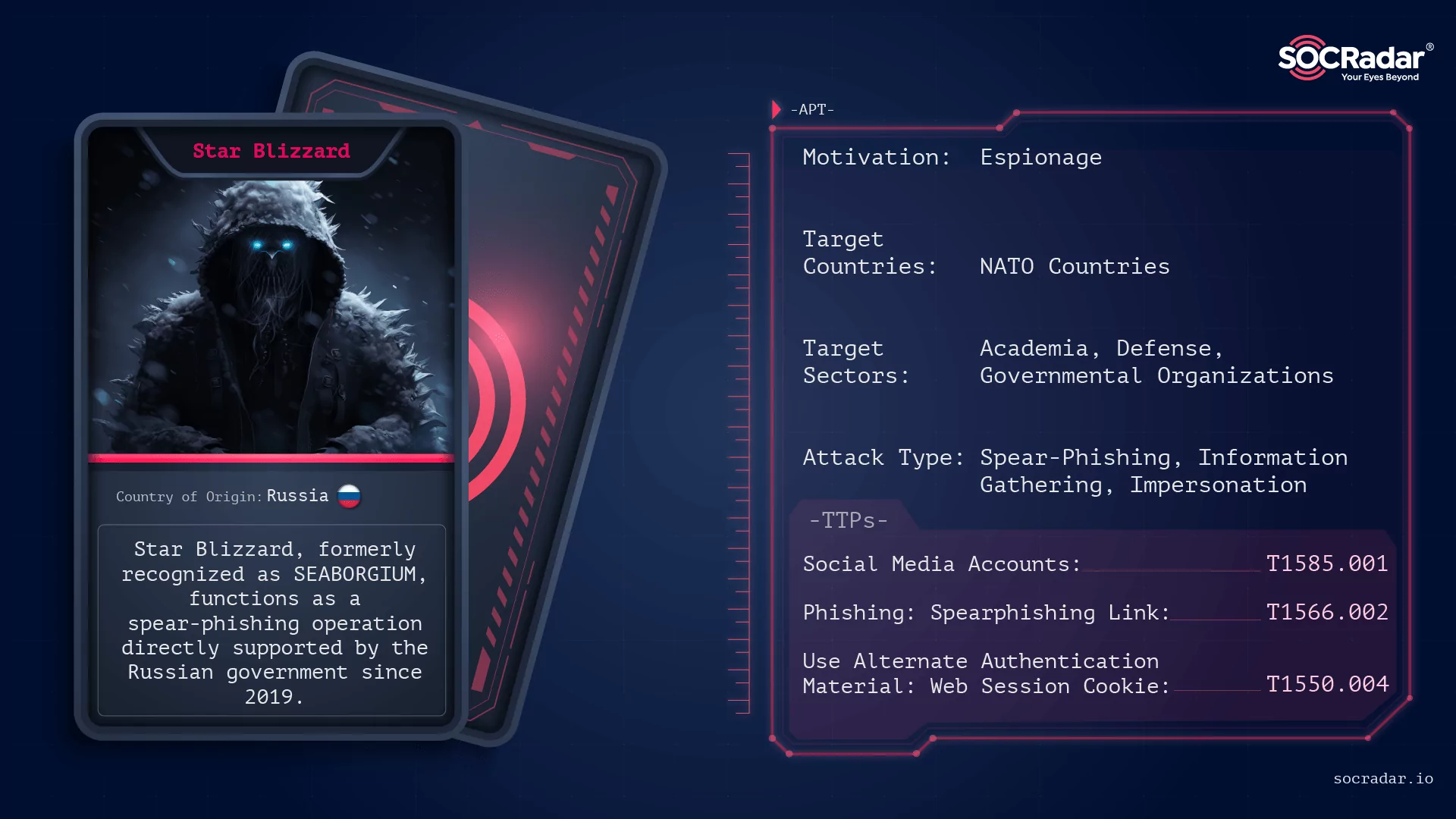
Russian APT Operation: Star Blizzard
Russian APT Operation: Star Blizzard [Update] January 30, 2024: “Official Attributions of Star Blizzard” Within the continuously changing cyber threat landscape, the strategies of Star Blizzard unfold...

Critical RCE Vulnerability in Cisco Unified Communications with Risk o...
Critical RCE Vulnerability in Cisco Unified Communications with Risk of Root Access (CVE-2024-20253) The Cybersecurity and Infrastructure Security Agency (CISA) has issued an alert highlighting Cisco ...
A Review of 2023 – 26,447 CVEs, 44 Days to Exploit, and Ransomware Ons...
A Review of 2023 – 26,447 CVEs, 44 Days to Exploit, and Ransomware Onslaught As we reflect on the cybersecurity journey of 2023, we uncover valuable lessons that shape our understanding of the ever-ch...
Dark Peep #9: The McFlurry Bandit
Dark Peep #9: The McFlurry Bandit Welcome to “Dark Peep #9.” This edition takes you behind the scenes of the digital world, where every byte tells a story. Here, we uncover the ongoing sagas of cyberc...
Stealer Malware 101: Understanding the Different Variants and Families
Stealer Malware 101: Understanding the Different Variants and Families In the realm of cybersecurity, malicious software (malware) continues to evolve, with various types targeting sensitive data for ...
Writing YARA Rules with Custom GPTs and SOCRadar Platform
Writing YARA Rules with Custom GPTs and SOCRadar Platform YARA rules stand out as essential instruments for identifying and classifying malware. These rules are indispensable for cybersecurity profess...

































