
Top Open Source Solutions for Building Security Operations Center II
Top Open Source Solutions for Building Security Operations Center II A Security Operations Center (SOC) is a centralized function inside an organization that employs people, procedures, and technology...

Malicious Chrome Extensions Could Affect More Than 1.4 Million Users
Malicious Chrome Extensions Could Affect More Than 1.4 Million Users McAfee researchers discovered several malicious Google Chrome extensions. The total download count for the extensions is over 1.4 m...

10 Free Security Testing Tools to Test Your Website
10 Free Security Testing Tools to Test Your Website Security testing for an application is a crucial element in the lifecycle of software testing. It restricts unwanted intrusions at multiple applic...

The Week in Dark Web - 29 August 2022 - Access Sales and Data Leaks
The Week in Dark Web – 29 August 2022 – Access Sales and Data Leaks Powered by DarkMirror™ This week’s edition covers the latest dark web news from the past week. This week’s headlin...

All You Need to Know About Endpoint Security
All You Need to Know About Endpoint Security Endpoint Security products are responsible for a market size of approximately 14 million in 2021. Regarding this market’s compound annual growth rate...

Critical RCE Vulnerability in the Atlassian Bitbucket Server and Data ...
Critical RCE Vulnerability in the Atlassian Bitbucket Server and Data Center Atlassian recently issued a security advisory to notify Bitbucket Server and Data Center users about a critical v...
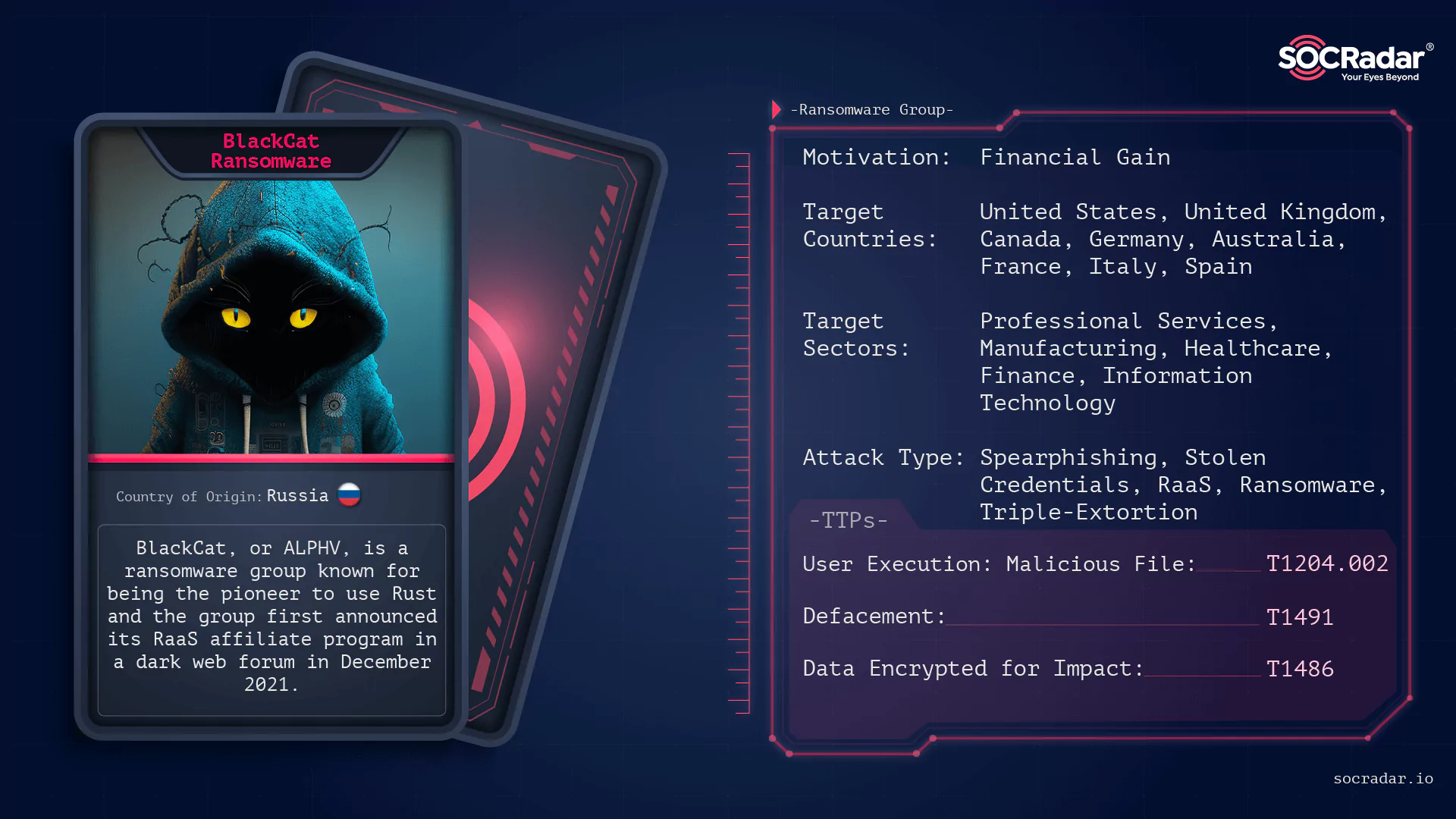
Dark Web Profile: BlackCat (ALPHV)
Dark Web Profile: BlackCat (ALPHV) [Update] December 19, 2023: As we speculated recently, law enforcement agencies have successfully taken control of the official site of the ALPHV.** Read more under ...

Twilio and MailChimp Attackers Hit 130 Organizations with Okta Phishin...
Twilio and MailChimp Attackers Hit 130 Organizations with Okta Phishing Campaign A larger phishing campaign that targeted 136 organizations and resulted in the theft of 9,931 account login ...

Threat Actors Stole LastPass Source Code Through a Compromised Develop...
Threat Actors Stole LastPass Source Code Through a Compromised Developer Account On 25th August, LastPass announced a breach and stated that its source code was stolen, along with some technical infor...

Dark Web Stories: Escrow
Dark Web Stories: Escrow Have you ever heard of the term dark web? Besides sheltering various individuals from spies to threat actors in its highly private environment, the dark web also hosts black m...

IBM Fixes Security Bypass Vulnerabilities Discovered in MQ Software
IBM Fixes Security Bypass Vulnerabilities Discovered in MQ Software IBM released security updates for two critical vulnerabilities in its message-oriented middleware IBM MQ. The vulnerabilities, ident...
Patch Available for Important LPE Vulnerability in VMware Tools
Patch Available for Important LPE Vulnerability in VMware Tools A security flaw identified in VMware Tools could lead to local privilege escalation attacks. A remote attacker with initial access can s...

Top 10 TLDs Threat Actors Use for Phishing
Top 10 TLDs Threat Actors Use for Phishing [Update] May 18, 2023: Google has released eight new top-level domains (TLDs). Added the subheading: “Google’s New TLDs: Commercial Opportunities...

Critical RCE Flaw Fixed in New Versions of GitLab
Critical RCE Flaw Fixed in New Versions of GitLab GitLab released patches where they fixed a critical remote code execution vulnerability. It is labeled CVE-2022-2884 with a CVSS score of 9....

Hackers Utilize AWS to Launch Phishing Attacks
Hackers Utilize AWS to Launch Phishing Attacks Phishing attacks are being launched by hackers using a tactic called Static Expressway. The newly-spread tactic lets hackers get their emails past Amazon...

The Week in Dark Web - 23 August 2022 - Access Sales and Data Leaks
The Week in Dark Web – 23 August 2022 – Access Sales and Data Leaks Powered by DarkMirror™ This week’s edition covers the latest dark web news from the past week. This week’s headlin...

Spain Threat Landscape Report: E-Commerce & Finance Industries Under A...
Spain Threat Landscape Report: E-Commerce & Finance Industries Under Attack SOCRadar’s Threat Landscape Report this month aims to provide organizations located in Spain with a region-based ...
Major Cyberattacks in Review: July 2022
Major Cyberattacks in Review: July 2022 Today’s world has many cyberattack targets, including large organizations, small businesses, and individuals. Any action, no matter how small, can put yo...

LockBit Allegedly DDoSed After Leaking Entrust's Data
LockBit Allegedly DDoSed After Leaking Entrust’s Data IT security company Entrust suffered a cyberattack on June 18. Attackers gained unauthorized access to the company’s network to r...

Fixed Flaw in Fishbowl Inventory Could Lead to RCE
Fixed Flaw in Fishbowl Inventory Could Lead to RCE Researchers identified a Java deserialization flaw in a Fishbowl Inventory instance that could result in remote code execution. The vulnerability is ...

































