Cyber Threat Intelligence (CTI) Roles for Ransomware Protection
Cyber Threat Intelligence (CTI) Roles for Ransomware Protection Ransomware attacks remain one of the most significant cyber threats against organizations today. Despite numerous countries launching co...

Chain Reactions: Footprints of Major Supply Chain Attacks
Chain Reactions: Footprints of Major Supply Chain Attacks In today’s interconnected digital ecosystem, supply chain attacks have emerged as one of the most potent threats. A supply chain attack occurs...

Navigating the Cyber Threat Landscape with SOCRadar's Vulnerability In...
Navigating the Cyber Threat Landscape with SOCRadar’s Vulnerability Intelligence and CVERadar In the world of cybersecurity, vulnerability intelligence is like a guiding light for experts dealing with...
Navigating Cloud Vulnerabilities: Challenges and Solutions
Navigating Cloud Vulnerabilities: Challenges and Solutions The cloud, in its simplest form, is a system of servers that store data and applications over the internet rather than on a computer’s ...

Exploring the NIST Cybersecurity Framework: Strengthening Digital Resi...
Exploring the NIST Cybersecurity Framework: Strengthening Digital Resilience In today’s rapidly evolving digital landscape, the term “cybersecurity” has become synonymous with safegu...

The Wolf in Sheep's Clothing: How Cybercriminals Abuse Legitimate Soft...
The Wolf in Sheep’s Clothing: How Cybercriminals Abuse Legitimate Software [Update] November 9, 2023: Added FBI’s notice, see under the title: “FBI Warns of Ransomware Threats via Th...

Threat-Informed Defense (TID): A Threat Intelligence Perspective
Threat-Informed Defense (TID): A Threat Intelligence Perspective Cyberattacks are increasing in frequency worldwide, posing significant challenges for organizations as they strive to protect their cyb...
Living Off the Land (LOTL): The Invisible Cyber Threat Lurking in Your...
Living Off the Land (LOTL): The Invisible Cyber Threat Lurking in Your System [Update] January 10, 2024: “Countering Living Off the Land (LOTL) Attack Methods with AI and ML” ...

The Black Box of GitHub Leaks: Analyzing Companies' GitHub Repos
The Black Box of GitHub Leaks: Analyzing Companies’ GitHub Repos This research aimed to investigate the files that companies might have accidentally uploaded to GitHub and identify any sensitive...
A Snapshot of 2023 CWE Top 25 Most Dangerous Software Weaknesses
A Snapshot of 2023 CWE Top 25 Most Dangerous Software Weaknesses Figure 1: Top 25 CWE logo (MITRE) The 2023 CWE Top 25 Most Dangerous Software Weaknesses is a list that ranks the most widespread and c...

From Azure AD to Microsoft Entra ID: Navigating the Name Change and St...
From Azure AD to Microsoft Entra ID: Navigating the Name Change and Strengthening Phishing Defense Azure AD, now known as Microsoft Entra ID, is undergoing a name change announced by Microsoft on 11 J...
The added OWASP Top 10 for LLMs: An Overview of Critical AI Vulnerabil...
The added OWASP Top 10 for LLMs: An Overview of Critical AI Vulnerabilities with SOCRadar Large Language Models (LLMs) are artificial intelligence models that generate human-like text. They have becom...

Ransomware Attacks on Banking Industry
Ransomware Attacks on Banking Industry Due to the escalating illicit pursuits of cybercriminals seeking unlawful financial gains, particular sectors and specific types of cyber attacks tend to gain pr...
Navigating the Assets Discovery Journey with SOCRadar XTI EASM
Navigating the Assets Discovery Journey with SOCRadar XTI EASM The attack surface is the sum of all potential entry points an attacker can use to gain unauthorized access to an organization’s as...

CVSS v4.0 on the Horizon
CVSS v4.0 on the Horizon [Update] November 2, 2023: See the subheading “FIRST Has Released CVSS v4.0: The Next Generation of Vulnerability Scoring” The Common Vulnerability Scoring System (CVSS) is a...
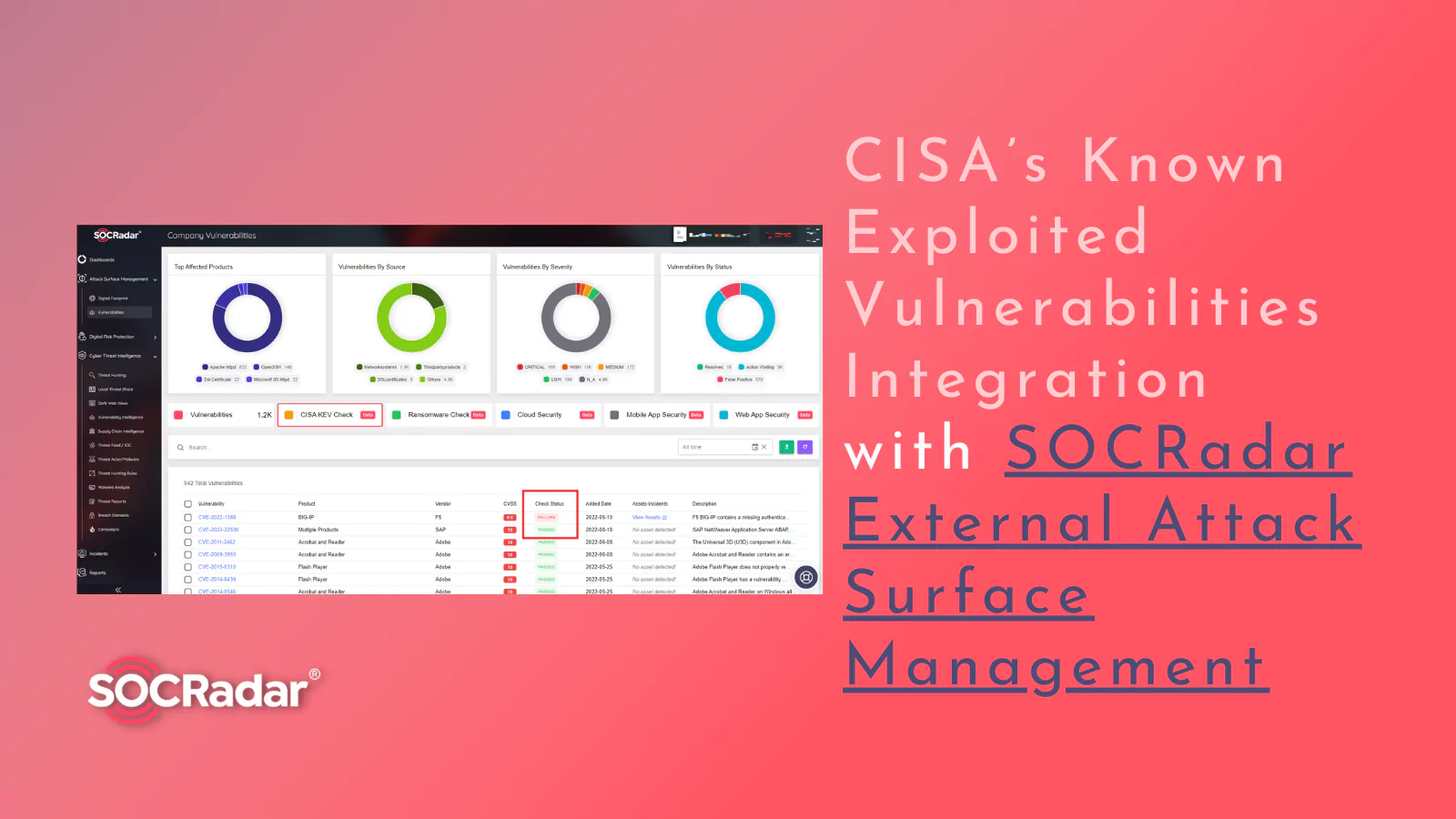
Best of Both Worlds: CISA’s Known Exploited Vulnerabilities Integratio...
Best of Both Worlds: CISA’s Known Exploited Vulnerabilities Integration with SOCRadar External Attack Surface Management In today’s digital landscape, the threat of cyberattacks looms large, with thre...
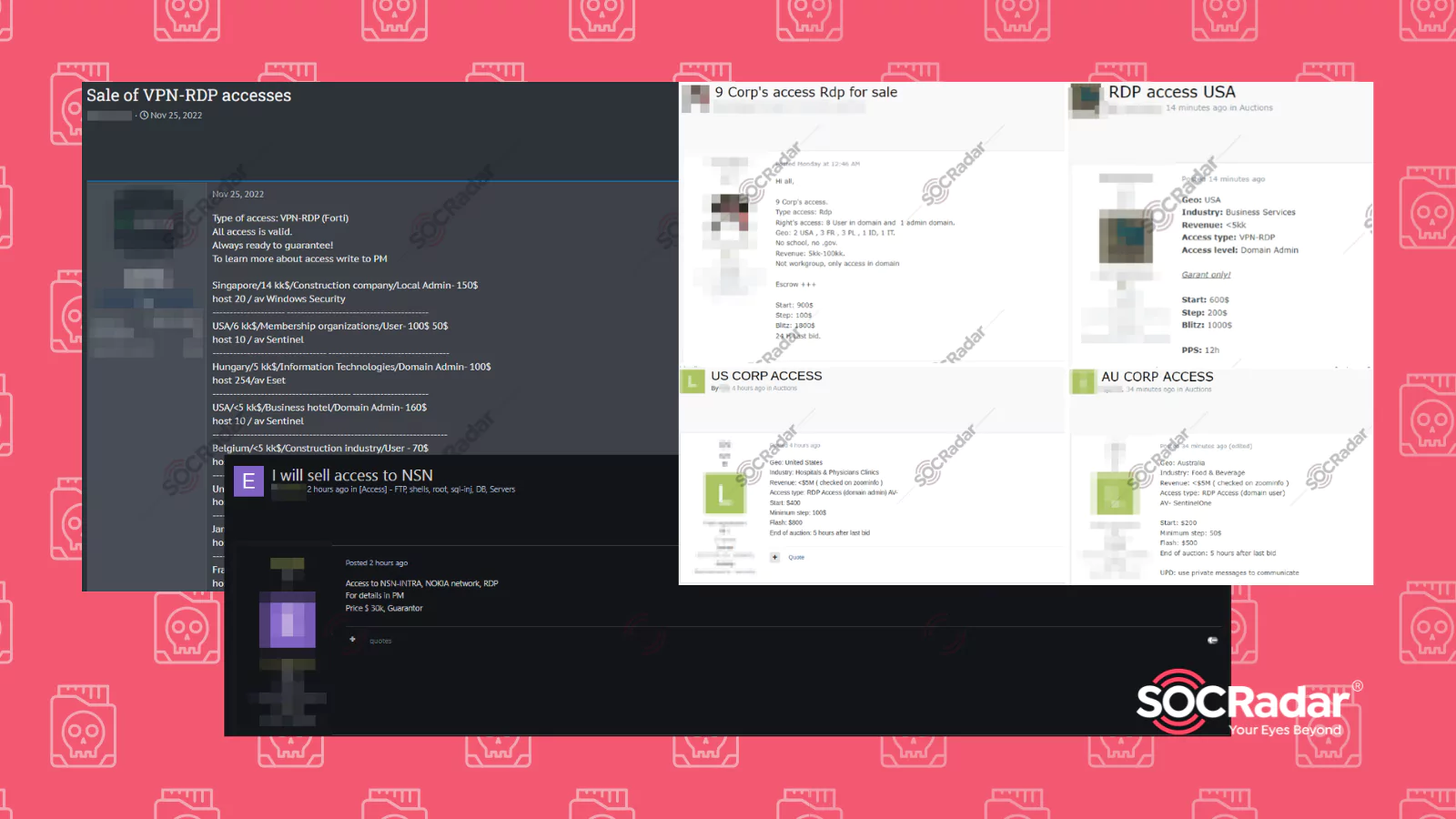
RDP Access Sales on Dark Web Forums Detected by SOCRadar
RDP Access Sales on Dark Web Forums Detected by SOCRadar Remote Desktop Protocol, or RDP, is a protocol developed by Microsoft. It allows the user to control another computer over a network connection...

Using OSINT to Strengthen Organizational Security
Using OSINT to Strengthen Organizational Security Open-source intelligence or “OSINT” is collecting and analyzing data gathered from publicly available open sources (social media, news, dark web, etc....

Exploring the Dark Web Job Market
Exploring the Dark Web Job Market The dark web, notorious for its illicit activities, has evolved into a bustling marketplace for various illegal purposes. It serves as a hub for cybercriminals, offer...

The Surge in Cyber Attacks on Latin American Governments
The Surge in Cyber Attacks on Latin American Governments Latin America, a region bustling with potential and promise, has witnessed a worrying trend of escalating cyber threats directed at government ...