The Week in Dark Web – 18 January 2023 – Partnership Posts, Data Leaks...
The Week in Dark Web – 18 January 2023 – Partnership Posts, Data Leaks, and Requests Powered by DarkMirror™ Threat actors seek to acquire new capabilities by forming partnerships with their peers to e...

What Do You Need to Know About the Critical RCE Vulnerability in Zoho’...
What Do You Need to Know About the Critical RCE Vulnerability in Zoho’s ManageEngine? (CVE-2022-47966) CVE-2022-47966, a critical vulnerability in a number of Zoho’s products, allows remote code execu...

Attackers Infected a CircleCI Employee with Malware to Steal Customer ...
Attackers Infected a CircleCI Employee with Malware to Steal Customer Session Tokens Software provider CircleCI confirmed that a data breach in December resulted in the theft of some of its ...

4 Lessons Learned from Log4Shell
4 Lessons Learned from Log4Shell By SOCRadar Research Log4Shell vulnerability shook the cyber world to its core when it first became public in December 2021. It is a zero-day vulnerability d...

Threat Actors Exploit CVE-2022-44877 RCE Vulnerability in CentOS Web P...
Threat Actors Exploit CVE-2022-44877 RCE Vulnerability in CentOS Web Panel (CWP) Update (16.01.2023): According to data gathered by researchers, the CVE-2022-46169 vulnerability in Cacti saw an increa...
5 Lessons Learned from Ransomware Attacks in 2022
5 Lessons Learned from Ransomware Attacks in 2022 By SOCRadar Research In 2022, SOCRadar researchers detected over 1700 alleged ransomware victims. The total number was approximately 29% hig...
Cacti Patched CVE-2022-46169 Critical RCE Vulnerability
Cacti Patched CVE-2022-46169 Critical RCE Vulnerability Cacti patched a critical security flaw to prevent arbitrary code execution on Cacti-running servers. Cacti is an open-source, we...

SOCRadar Free Dark Web Training: Learn How to Navigate in the Shadows
SOCRadar Free Dark Web Training: Learn How to Navigate in the Shadows The concept of the dark web plays a key role in today’s increasingly complex cybercrime ecosystem. Threat actors share the dataset...

5 Lessons Learned from Data Breaches in 2022
5 Lessons Learned from Data Breaches in 2022 By SOCRadar Research Online products and services are growing daily. Consumers are entrusting more personal information to online databases, and businesses...

Ransomware Gangs Leak Large Amounts of Data in Recent Attacks: Hive an...
Ransomware Gangs Leak Large Amounts of Data in Recent Attacks: Hive and Vice Society Ransomware gangs are known to release stolen data in retaliation if the ransom is not paid after successful encrypt...
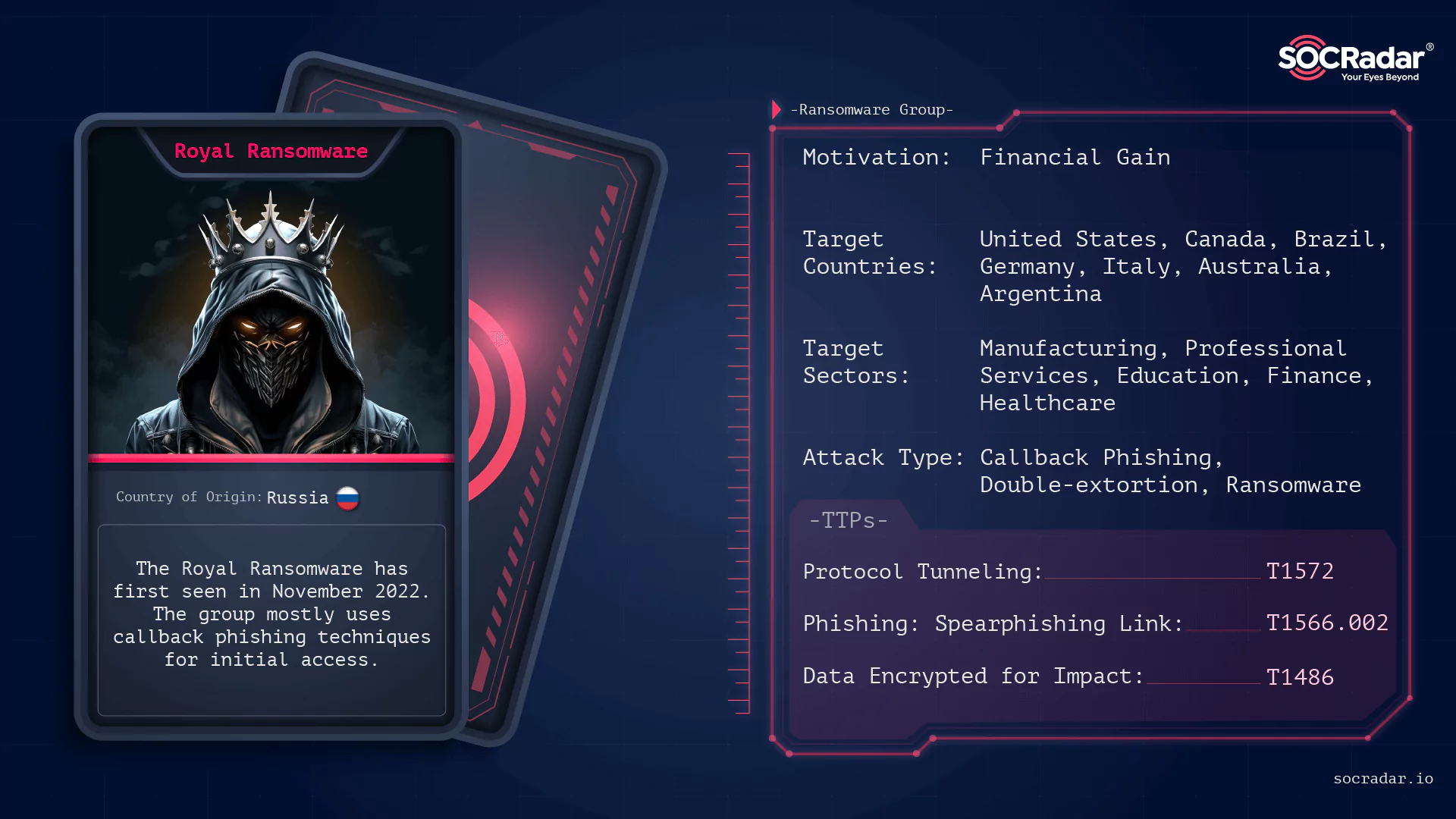
Dark Web Profile: Royal Ransomware
Dark Web Profile: Royal Ransomware By SOCRadar Research [Update] November 14, 2023: See the subheading: “CSA Update from CISA and FBI: Royal Ransomware’s Possible Rebranding to ‘Blacksuit’” Ran...

The Week in Dark Web – 9 January 2023 – Access Sales and Data Leakes...
The Week in Dark Web – 9 January 2023 – Access Sales and Data Leakes Powered by DarkMirror™ Threat actors continue to target popular social networking platforms. Twitter was awash with two significant...

Major Cyber Attacks in Review: December 2022
Major Cyber Attacks in Review: December 2022 In the last month, we have seen many cyber incidents, ranging from data breaches at retailers to various cyberattacks on cryptocurrency exch...

200M+ Twitter Users' Email Addresses and 250M+ Deezer Users' Informati...
200M+ Twitter Users’ Email Addresses and 250M+ Deezer Users’ Information Leaked Online On a well-known hacker forum, a data leak containing the email addresses of 235 million Twitter users was made pu...

The Week in Dark Web – 4 January 2023 – Access Sales, Data, and Malwar...
The Week in Dark Web – 4 January 2023 – Access Sales, Data, and Malware Leakes Powered by DarkMirror™ Entering the first week of the year, the most sensational incident on the dark web was the sale of...
Synology Fixes a Max Severity RCE Vulnerability in VPN Server Products
Synology Fixes a Max Severity RCE Vulnerability in VPN Server Products Taiwanese NAS device manufacturer Synology has released a security update to address a critical vulnerability with a&nb...

How Easy Is It to Guess Fortune 500 Executives' Passwords?
How Easy Is It to Guess Fortune 500 Executives’ Passwords? Recently, many cyberattacks on large corporations have begun with acquiring credentials via multiple methods, particularly social ...

Secure Your Cloud Environment: 5 Best Practices
Secure Your Cloud Environment: 5 Best Practices With the increasing adoption of cloud computing, cloud security has become a major concern for businesses that rely on cloud-based services to...

10 Questions to ChatGPT: How It Can Change Cybersecurity
10 Questions to ChatGPT: How It Can Change Cybersecurity This blog is written with the help of OpenAI’s ChatGPT. In November 2022, OpenAI -an Artificial Intelligence research and depl...

Dark Web Profile: MuddyWater APT Group
Dark Web Profile: MuddyWater APT Group [Update] April 19, 2023: Added subheading: “MuddyWater Uses SimpleHelp Tool for Persistence on Victim Devices” Security concerns grow day by day with the rise of...