14 Million Credit Card Information Sold on Black Markets
14 Million Credit Card Information Sold on Black Markets The Q3 Finance Industry Threat Landscape Report prepared by SOCRadar analysts has been published this week. The report includes a detailed anal...

What is Operational Cyber Threat Intelligence?
What is Operational Cyber Threat Intelligence? As cyber threats become more sophisticated, many organizations are paying more attention to their security programs. Organizations of all sizes are build...

How Ransomware Groups Use Tor-Based Backdoors
How Ransomware Groups Use Tor-Based Backdoors In various incidents, threat actors leveraged Tor and Onion Services to create backdoors that gave them ongoing access to compromised networks. In this bl...

SOCRadar Recognized as DRPS Vendors in Two Gartner Reports
SOCRadar Recognized as DRPS Vendors in Two Gartner Reports SOCRadar is recognized as a DRPS sample vendor in Gartner’s latest reports on “Competitive Landscape: Digital Risk Protection Services”...
The Digital Industries Commonly Targeted by Phishing Attacks in Indone...
The Digital Industries Commonly Targeted by Phishing Attacks in Indonesia Indonesia is a prime target for nation-state-sponsored actors as well as financially motivated ransomware gangs in 2021. It is...

What is Extended Detection and Response (XDR)?
What is Extended Detection and Response (XDR)? Extended Detection and Response (XDR) is a security technology that delivers comprehensive visibility into data across networks and clouds in addition to...

The Week in Dark Web - 25 October 2021 - New Ransomware Attacks and Da...
The Week in Dark Web – 25 October 2021 – New Ransomware Attacks and Data Leaks Powered by DarkMirror™ This week’s edition covers the latest dark web news from the past week. Again, rise of...
What Is Ransomware-as-a-Service (RaaS)?
What Is Ransomware-as-a-Service (RaaS)? While informing you about ransomware since the beginning of October, we talked about how lucrative “E-crime” has become. With this information in mind, it’s cru...
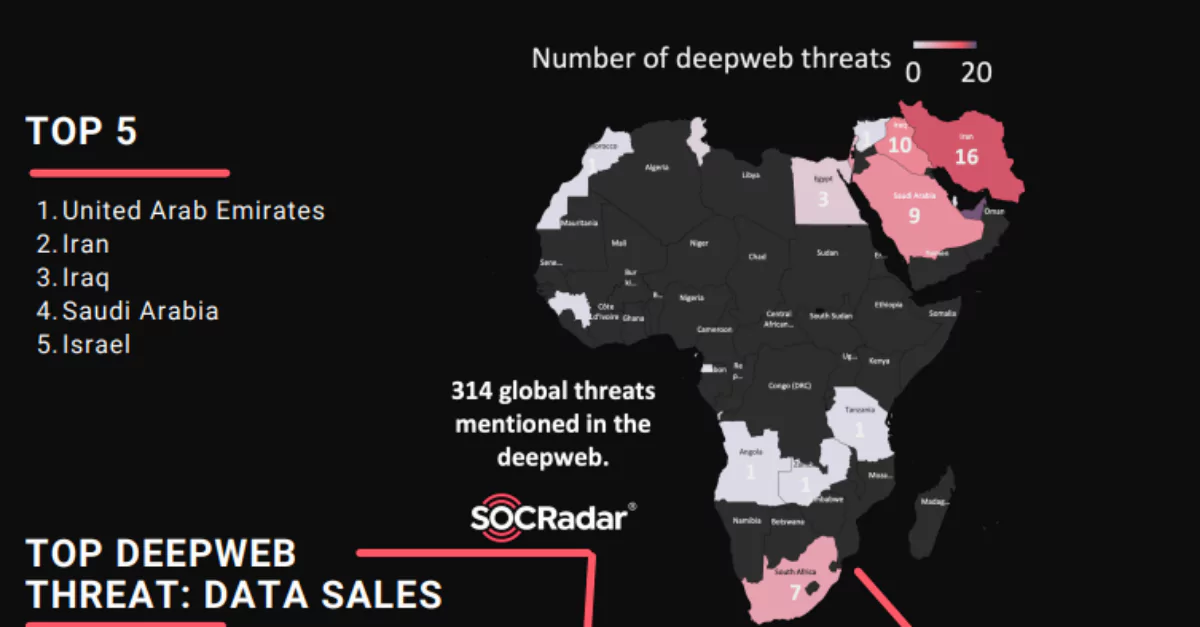
Data Sales Are The Biggest Deep Web Threat In MEA Region
Data Sales Are The Biggest Deep Web Threat In MEA Region The MEA Regional DeepWeb Report, which emerged with the research of the SOCRadar analyst team, is now available. Dark web incidents, hack...

Who Is the BlackByte Ransomware Group and How Does the Decryptor Works...
Who Is the BlackByte Ransomware Group and How Does the Decryptor Works? Ransomware attacks impact organizations every single day. But it doesn’t always have to be bad news. Victims of BlackByte ...
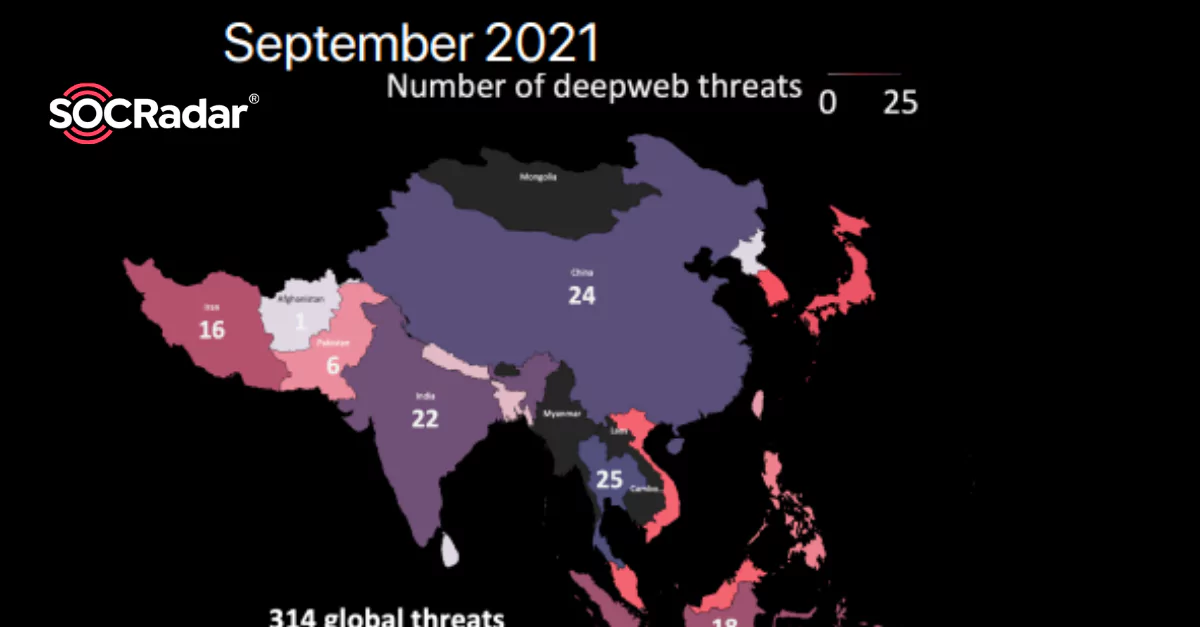
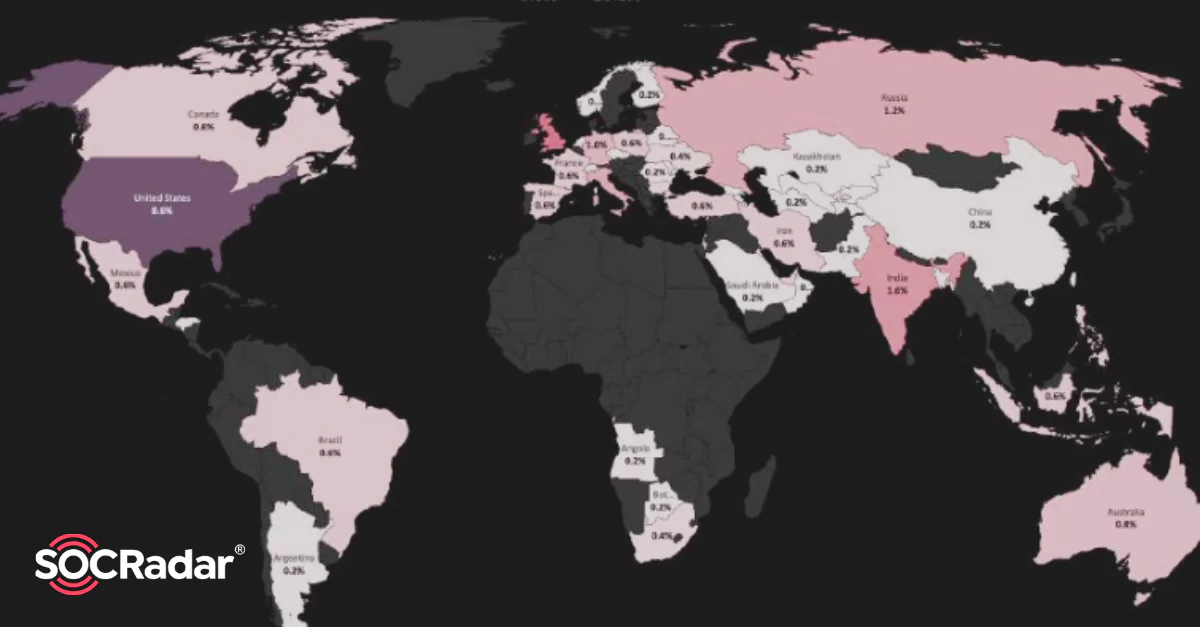
Countries More Affected by Cyber Attacks in September: China and Thail...
Countries More Affected by Cyber Attacks in September: China and Thailand The APAC Regional DeepWeb Report, which emerged with the research of the SOCRadar analyst team, is now available. Dark web inc...

Dark Web Threat Profile: BlackMatter Ransomware Group
Dark Web Threat Profile: BlackMatter Ransomware Group We continue to convey the latest news on ransomware on our blog. Cybersecurity researchers have warned of emerging ransomware groups almost every ...

The Week in Dark Web - 18 October 2021 - Ransomware Attacks and Data L...
The Week in Dark Web – 18 October 2021 – Ransomware Attacks and Data Leaks Powered by DarkMirror™ This week’s edition covers the latest dark web news from the past week. Again, rise of ran...

Why Do States Take Various Steps to Stop Ransomware Attacks?
Why Do States Take Various Steps to Stop Ransomware Attacks? Thirty-one countries and European Union’s representatives involved in a two-day “ransomware summit” led by the US have re...
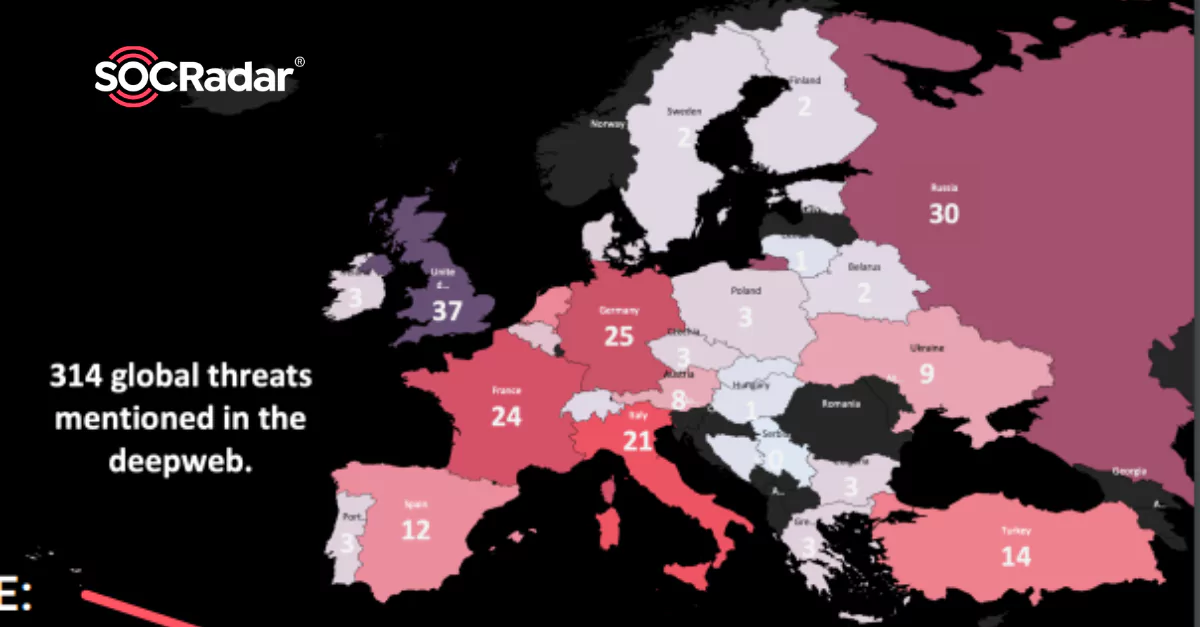
Ransomware Attacks on the Rise Around Europe
Ransomware Attacks on the Rise Around Europe The Europe Regional Deep Web Report, which emerged with the research of the SOCRadar analyst team, is now available. Dark web incidents, hacker forum...

What Is Babuk? The Ransomware Gang You Should Know About
What Is Babuk? The Ransomware Gang You Should Know About [Update] January 10, 2024: “Babuk Tortilla Ransomware Variant Decrypted” Babuk, also known internally as Babyk, initially “Vasa Locker,” is a...

Why Ransomware Is a Major Threat to Certain Industries
Why Ransomware Is a Major Threat to Certain Industries Ransomware attacks are on the rise and continue to be disruptive in the cybersecurity industry, affecting everything from financial institution...

The Week in Dark Web - 11 October 2021 - Rise of Ransomware Attacks
The Week in Dark Web – 11 October 2021 – Rise of Ransomware Attacks Powered by DarkMirror™ This week’s edition covers the latest dark web news from the past week. Again, rise of ransomware...
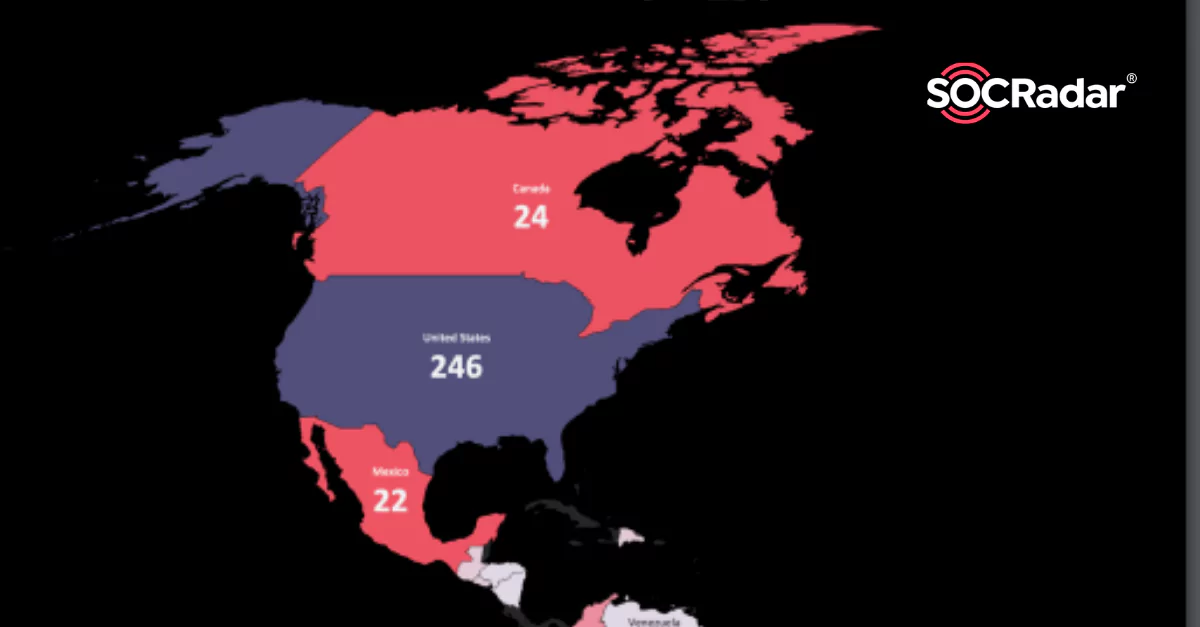
Top Ransomware Group is LockBit 2.0 in the Americas
Top Ransomware Group is LockBit 2.0 in the Americas The Americas Regional DeepWeb Report, which emerged with the research of the SOCRadar analyst team, is now avaible for the first time. Dark we...

Top Five Causes of Ransomware Attacks
Top Five Causes of Ransomware Attacks Ransomware attacks deeply affect our lives nowadays. Every day we wake up to the news of another attack. To better prevent these attacks, it is critical to unders...