Dark Web Sales: Unauthorized Citrix Access, Credit Cards, and Student ...
Dark Web Sales: Unauthorized Citrix Access, Credit Cards, and Student Documents The SOCRadar Dark Web Team has been tirelessly monitoring the deep corners of the internet, and their efforts have unear...

Critical Microsoft Power Platform Vulnerability: Proactive Security Me...
Critical Microsoft Power Platform Vulnerability: Proactive Security Methods to Prevent Exploitation Microsoft fixed a critical vulnerability in its Power Platform after facing criticism for the delaye...

Threat-Informed Defense (TID): A Threat Intelligence Perspective
Threat-Informed Defense (TID): A Threat Intelligence Perspective Cyberattacks are increasing in frequency worldwide, posing significant challenges for organizations as they strive to protect their cyb...

Threat Actors Employ New Phishing Tactic Using Google AMP
Threat Actors Employ New Phishing Tactic Using Google AMP Researchers have uncovered a highly effective phishing tactic, which utilizes Google AMP (Accelerated Mobile Pages). Google AMP is an open-sou...
Living Off the Land (LOTL): The Invisible Cyber Threat Lurking in Your...
Living Off the Land (LOTL): The Invisible Cyber Threat Lurking in Your System [Update] January 10, 2024: “Countering Living Off the Land (LOTL) Attack Methods with AI and ML” ...

Threat Profile: Rhysida Ransomware
Threat Profile: Rhysida Ransomware [Update] November 16, 2023: See the subheading: “Collaborative Advisory by CISA, FBI, and MS-ISAC on Rhysida Ransomware.” [Update] February 13, 2024: “A Free D...

Major Cyberattacks in Review: July 2023
Major Cyberattacks in Review: July 2023 The major cyberattacks of July 2023 included waves of data breaches, affecting both private and public sector entities, including healthcare organizations, fina...

Top 10 Ransomware Demands
Top 10 Ransomware Demands In cyberspace, few threats rival ransomware attacks’ pervasive and destructive nature. As our interconnected world grows, these digital extortionists demonstrate unpara...

Zero-Day RCE Sale, Pizza Hut Access Sale & More
Zero-Day RCE Sale, Pizza Hut Access Sale & More Welcome to the twisted world of the Dark Web, where the illicit trade of cyber weapons and stolen data thrives under the cover of anonymity. In thi...

P2Pinfect: A Worm-Like Botnet Malware Targeting Redis Deployments
P2Pinfect: A Worm-Like Botnet Malware Targeting Redis Deployments [Update] June 26, 2024: “P2PInfect Botnet: Recent Developments and Ransomware Deployment” Researchers have identified an unknown group...

DepositFiles Config File Exposes Multiple Databases: Users’ Privacy at...
DepositFiles Config File Exposes Multiple Databases: Users’ Privacy at Risk DepositFiles, a well-known web hosting service, left its environment configuration file publicly accessible, leading to unau...
Android Vulnerabilities That Do Not Get Fixed Function as a Zero-Day
Android Vulnerabilities That Do Not Get Fixed Function as a Zero-Day Maddie Stone of Google’s Threat Analysis Group (TAG) authored the fourth annual year-in-review of zero-day vulnerabilities that att...

Collective Security in Cyberspace with NATO
Collective Security in Cyberspace with NATO The North Atlantic Treaty Organization (NATO) is an intergovernmental military alliance formed to ensure collective defense and security for its member nati...
New Advanced Attack Technique Exploiting “search-ms” URI Protocol Hand...
New Advanced Attack Technique Exploiting “search-ms” URI Protocol Handler The Windows operating system boasts a robust search feature for locating files and folders; there also is a less-known element...
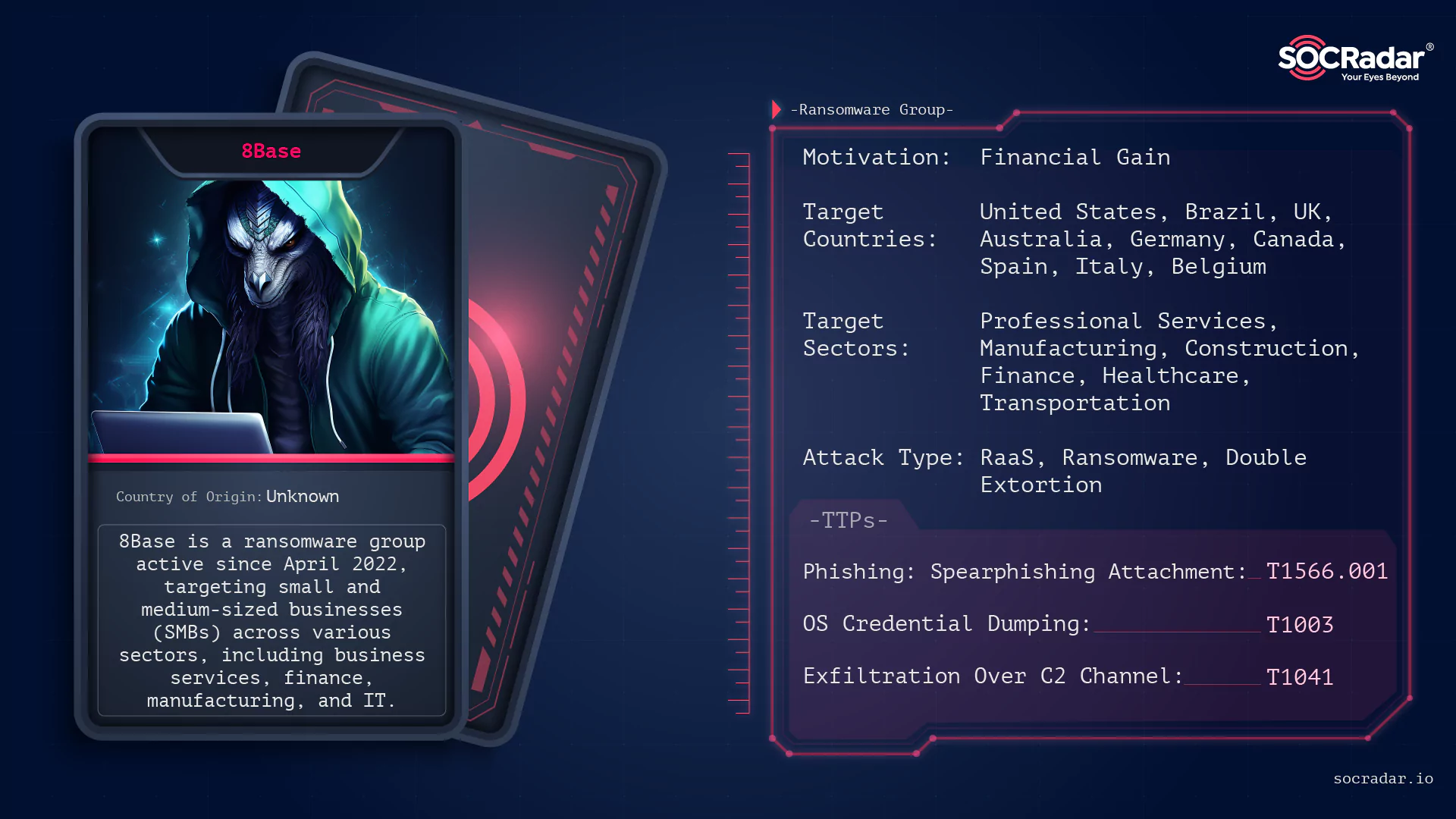
Dark Web Profile: 8Base Ransomware
Dark Web Profile: 8Base Ransomware In today’s cyber world, while the ransomware scene remains dynamic and active, new actors are emerging with significant numbers of victims. In this article, we...
Nitrogen: A Malware Campaign Leveraging Search Ads
Nitrogen: A Malware Campaign Leveraging Search Ads Researchers have uncovered a new initial access malware campaign dubbed “Nitrogen”. This campaign employs Google and Bing search ads to promote fake ...

The Phishing Risks of Twitter's Name Change to X
The Phishing Risks of Twitter’s Name Change to X In today’s digital playground, social media swings both ways, offering a fun-filled space for individuals to connect and share, while also ...
7 Lessons Learned from Cyber Attacks in the Manufacturing Industry
7 Lessons Learned from Cyber Attacks in the Manufacturing Industry SOCRadar’s Manufacturing Threat Landscape Report provides valuable insights into the manufacturing industry’s c...

Russia-Linked APT Group Gamaredon Starting Extortion 30-50 Minutes Aft...
Russia-Linked APT Group Gamaredon Starting Extortion 30-50 Minutes After First Initial Access The threat group, Gamaredon, linked to Russia, has been observed engaging in data exfiltration activities ...
VMware Responses to the Critical CVE-2023-20891 Vulnerability Exposing...
VMware Responses to the Critical CVE-2023-20891 Vulnerability Exposing CF API Admin Credentials Virtual machines have revolutionized the world of cybersecurity, offering a myriad of benefits to cybers...