The Black Box of GitHub Leaks: Analyzing Companies' GitHub Repos
The Black Box of GitHub Leaks: Analyzing Companies’ GitHub Repos This research aimed to investigate the files that companies might have accidentally uploaded to GitHub and identify any sensitive...
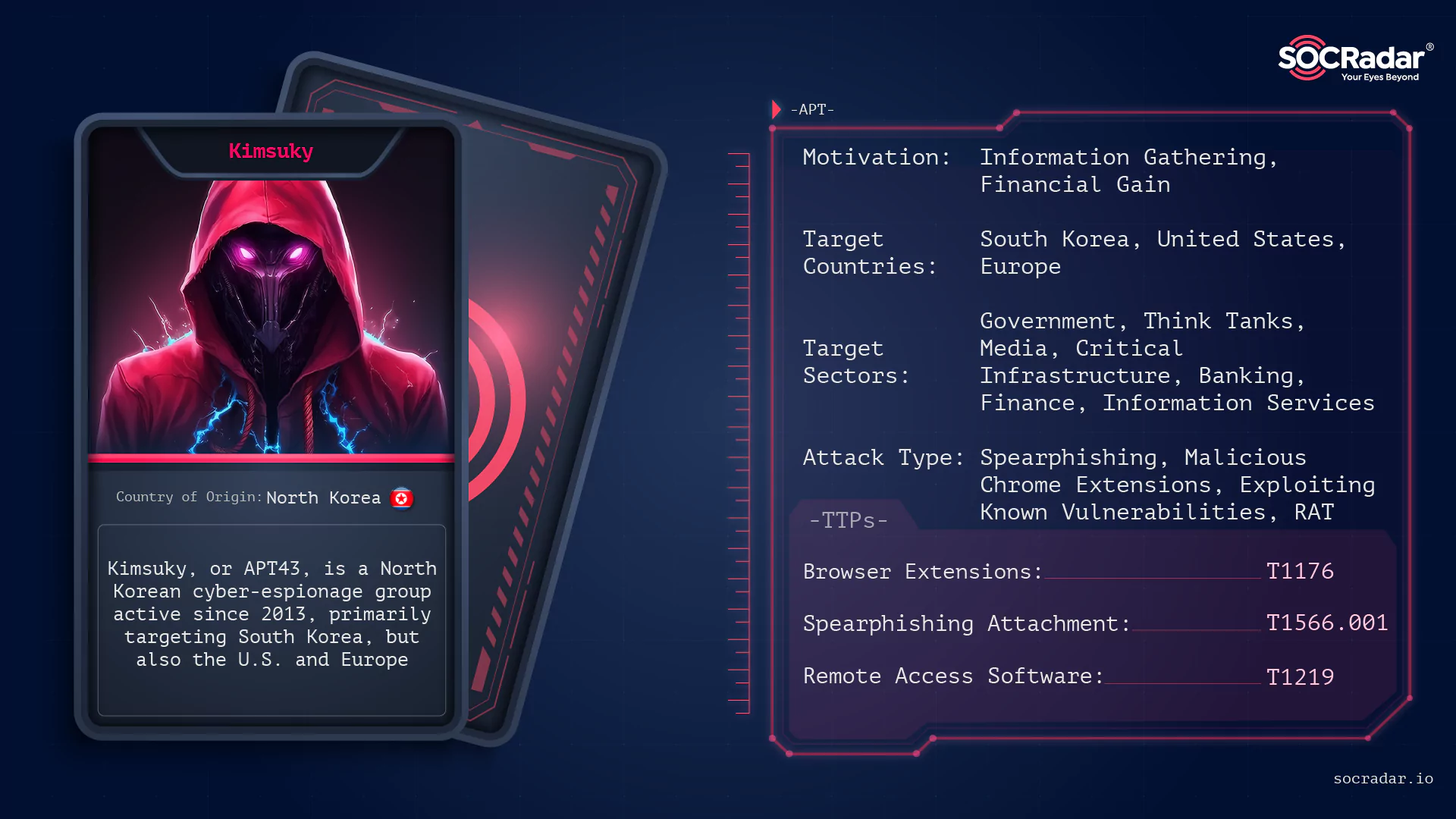
APT Profile: Kimsuky
APT Profile: Kimsuky In cyberspace, the Korean Peninsula has been a hotbed of activity for a while. With conflict unfolding between North and South Korea, North Korean Advanced Persistent Threats (APT...

RCE Vulnerability in OpenSSH’s SSH-Agent Forwarding: CVE-2023-38408
RCE Vulnerability in OpenSSH’s SSH-Agent Forwarding: CVE-2023-38408 SSH-Agent is a widely used program that holds private keys for public key authentication, providing a secure and convenient way to l...
Critical Zero-Day in Ivanti EPMM (Formerly MobileIron Core) Is Activel...
Critical Zero-Day in Ivanti EPMM (Formerly MobileIron Core) Is Actively Exploited (CVE-2023-35078) Ivanti, a U.S. IT software company, has resolved an actively exploited zero-day authentication bypass...
Critical Vulnerabilities in Atlassian and Apple Products: Apple Zero-D...
Critical Vulnerabilities in Atlassian and Apple Products: Apple Zero-Day Actively Exploited (CVE-2023-38606) Atlassian and Apple have each promptly addressed critical vulnerabilities threatening their...

Zero-Days (CVE-2023-26077, CVE-2023-26078) in Atera Windows Installers
Zero-Days (CVE-2023-26077, CVE-2023-26078) in Atera Windows Installers Recent revelations have exposed critical zero-day vulnerabilities in Atera Windows installers. Cyber attackers could potentially ...

300% Increase in the Number of Dark Web References to Manufacturing Or...
300% Increase in the Number of Dark Web References to Manufacturing Organizations SOCRadar’s Manufacturing Threat Landscape Report is out now! This report provides valuable insights into the cybersecu...
A Snapshot of 2023 CWE Top 25 Most Dangerous Software Weaknesses
A Snapshot of 2023 CWE Top 25 Most Dangerous Software Weaknesses Figure 1: Top 25 CWE logo (MITRE) The 2023 CWE Top 25 Most Dangerous Software Weaknesses is a list that ranks the most widespread and c...

Roblox Data Breach, Unauthorized Access Sales, and Global Leaks
Roblox Data Breach, Unauthorized Access Sales, and Global Leaks Welcome to SOCRadar’s weekly dark web news digest. This week, we spotlight several critical cybersecurity incidents: a significant...

Google Partially Patches Cloud Build’s Critical Design Flaw: Bad.Build...
Google Partially Patches Cloud Build’s Critical Design Flaw: Bad.Build Researchers discovered a critical security design flaw in Google Cloud Build, which they dubbed as “Bad.Build”. The d...

First-Known Targeted Open-Source Supply Chain Attacks Strike the Banki...
First-Known Targeted Open-Source Supply Chain Attacks Strike the Banking Sector The cybersecurity threat landscape continues to witness new and sophisticated threats, and the banking sector is no exce...
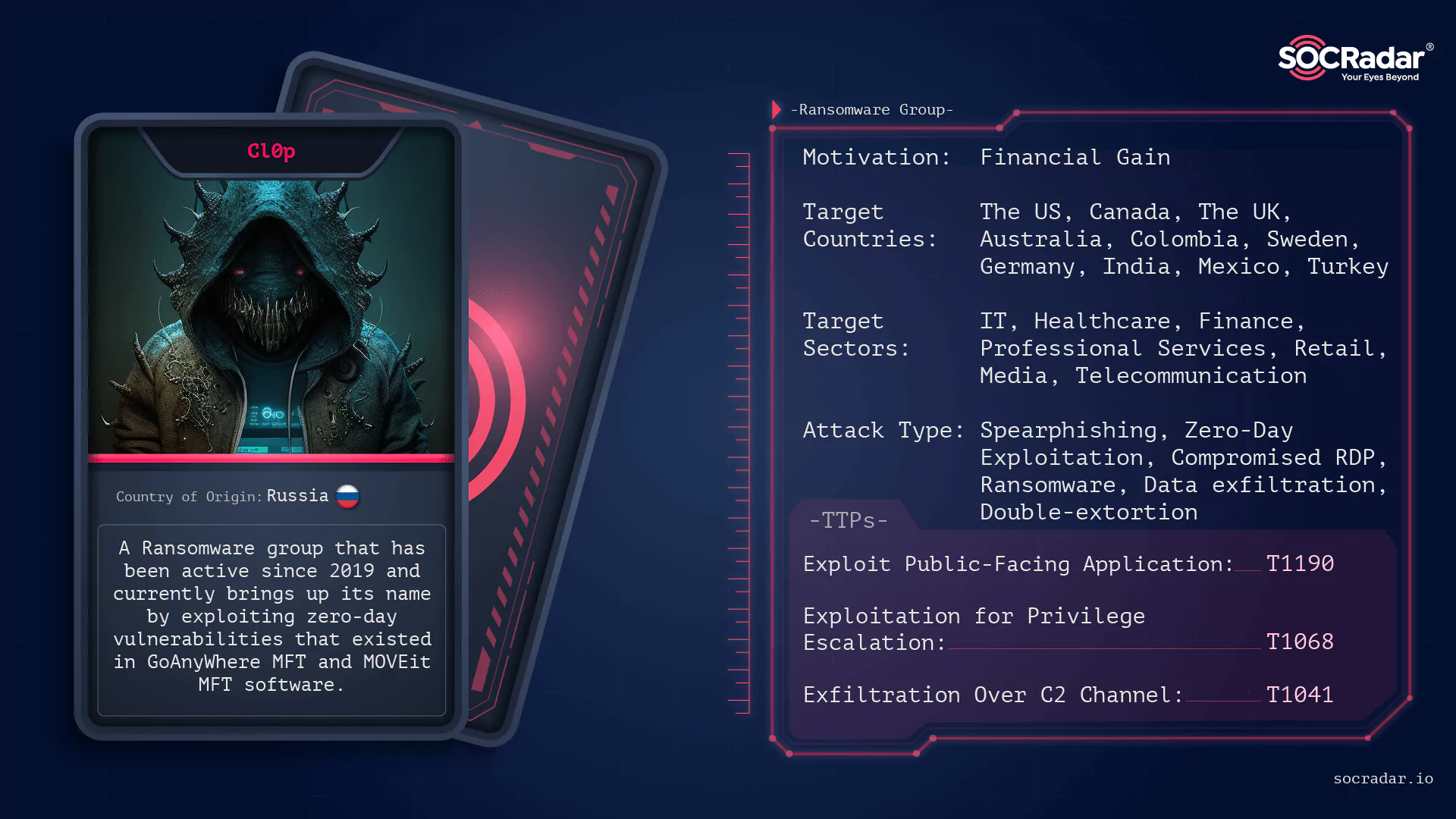
Dark Web Threat Profile: CLOP Ransomware
Dark Web Threat Profile: CLOP Ransomware [Update] August 7, 2023: Clop ransomware has now adopted Torrents as a distribution method for the stolen data. See more under: “Clop Adopts New Extortion Appr...

Fixed Critical Severity Vulnerabilities (CVE-2022-45788) in Schneider ...
Fixed Critical Severity Vulnerabilities (CVE-2022-45788) in Schneider Electric EcoStruxure Products, Modicon PLCs, and PACs In the realm of industrial control systems (ICS), vulnerabilities pose signi...

An Ongoing DDoS Campaign Targeting Sweden
An Ongoing DDoS Campaign Targeting Sweden Following an Islamophobic incident where the Qur’an was burned in Stockholm, Sweden, a new wave of cyber attacks, named #OpSweden, has emerged with sign...
WormGPT: Blackhat AI Module Surges to 5,000 Subscribers in Just Few Da...
WormGPT: Blackhat AI Module Surges to 5,000 Subscribers in Just Few Days Artificial Intelligence (AI) has brought groundbreaking innovations, and one of its remarkable subsets is generative AI. While ...

High Severity Vulnerabilities Fixed by Chrome 115 Update (CVE-2023-372...
High Severity Vulnerabilities Fixed by Chrome 115 Update (CVE-2023-3727, CVE-2023-3728, CVE-2023-3730, CVE-2023-3732) Google recently announced the release of the latest Chrome update, Chrome 115, to ...

Critical Patches for Oracle Products including MySQL (CVE-2023-20862),...
Critical Patches for Oracle Products including MySQL (CVE-2023-20862), WebLogic Server (CVE-2023-26119) and VirtualBox VM (CVE-2023-22018) with critical vulnerabilities Oracle has recently released 50...

Underground Fully UnDetectable (FUD) Crypter Market
Underground Fully UnDetectable (FUD) Crypter Market The rapidly evolving threats in the field of cybersecurity are being met with sophisticated methods such as “FUD” (Fully UnDetectable) c...

Overview of Cloudflare’s 2023 Q2 DDoS Threat Report
Overview of Cloudflare’s 2023 Q2 DDoS Threat Report Cloudflare, a renowned internet security company, has recently released a comprehensive report concerning DDoS attacks (Distributed Denial-of-Servic...

Critical and High Vulnerabilities in Citrix ADC and Citrix Gateway (CV...
Critical and High Vulnerabilities in Citrix ADC and Citrix Gateway (CVE-2023-3519, CVE-2023-3466, CVE-2023-3467) ...