Inside the Mind of a Ransomware Boss: An Interview with the LockBit Ad...
Inside the Mind of a Ransomware Boss: An Interview with the LockBit Administrator As the effectiveness of ransomware attacks continues to escalate, they have emerged as the most significant challenge ...

Threat Landscape in the Aviation Industry for H1 of 2023
Threat Landscape in the Aviation Industry for H1 of 2023 The aviation industry relies on interconnected networks and systems to facilitate seamless operations. Airlines, airports, manufacturers of air...

Critical WooCommerce Vulnerability Enables Admin Privileges on WordPre...
Critical WooCommerce Vulnerability Enables Admin Privileges on WordPress Sites (CVE-2023-28121) Researchers have observed an active exploit campaign targeting a newly disclosed vulnerability, CVE-2023...

Critical Remote Code Execution Vulnerability in Adobe ColdFusion (CVE-...
Critical Remote Code Execution Vulnerability in Adobe ColdFusion (CVE-2023-29300) [Update] January 9, 2024: “CVE-2023-38203 and CVE-2023-29300 in Adobe ColdFusion Have Joined the CISA KEV Catalog” [Up...

From Azure AD to Microsoft Entra ID: Navigating the Name Change and St...
From Azure AD to Microsoft Entra ID: Navigating the Name Change and Strengthening Phishing Defense Azure AD, now known as Microsoft Entra ID, is undergoing a name change announced by Microsoft on 11 J...

Healthcare Data, Zero Day Exploit, and ATM & POS Malware Sales
Healthcare Data, Zero Day Exploit, and ATM & POS Malware Sales This week, there’s a chilling offer on the dark web involving sensitive data from the U.S. healthcare industry. But that’...
Docker Hub Images Expose Secrets and Private Keys, Potentially Leading...
Docker Hub Images Expose Secrets and Private Keys, Potentially Leading to Attacks Researchers at RWTH Aachen University in Germany have conducted a study, revealing that numerous Docker images shared ...

DDoS Alert for NATO Countries
DDoS Alert for NATO Countries The rise in DDoS attacks poses significant challenges to individuals, organizations, and even entire nations. The impending threat from Anonymous Russia against France, ...

Urgent Patching Required for High Severity Vulnerabilities in Zoom
Urgent Patching Required for High Severity Vulnerabilities in Zoom With the widespread adoption of Zoom during the pandemic, the video conferencing platform has become ubiquitous, installed on countle...
Under the Spotlight: State of Evolving Australian Threat Landscape in ...
Under the Spotlight: State of Evolving Australian Threat Landscape in 2023 While cyber-attacks gain momentum in parallel with the increase in digitalization, companies operating in both public and pri...
The added OWASP Top 10 for LLMs: An Overview of Critical AI Vulnerabil...
The added OWASP Top 10 for LLMs: An Overview of Critical AI Vulnerabilities with SOCRadar Large Language Models (LLMs) are artificial intelligence models that generate human-like text. They have becom...

Zimbra Zero-Day Vulnerability Actively Exploited, Apply the Fix Now
Zimbra Zero-Day Vulnerability Actively Exploited, Apply the Fix Now [Update] November 17, 2023: See the subheading: “Google Reports Four Campaigns Exploiting the Zimbra Zero-Day: CVE-2023-37580.” Zimb...

Multiple Critical (CVE-2023-29308) Vulnerabilities Discovered in Adobe...
Multiple Critical (CVE-2023-29308) Vulnerabilities Discovered in Adobe InDesign A series of important zero-day vulnerabilities in Adobe InDesign has been discovered recently, and promptly reported to ...

Chinese Threat Actors Target European Ministries and Embassies with HT...
Chinese Threat Actors Target European Ministries and Embassies with HTML Smuggling in Smugx Campaign The re-emergence of HTML smuggling can be linked to the global increase in remote work due to the p...

Top 10 Malware Analysis Platforms & Tools
Top 10 Malware Analysis Platforms & Tools While cyberspace constantly expands, some dangers like malware come to the surface in parallel. A mail attachment, an innocent-looking application downloa...
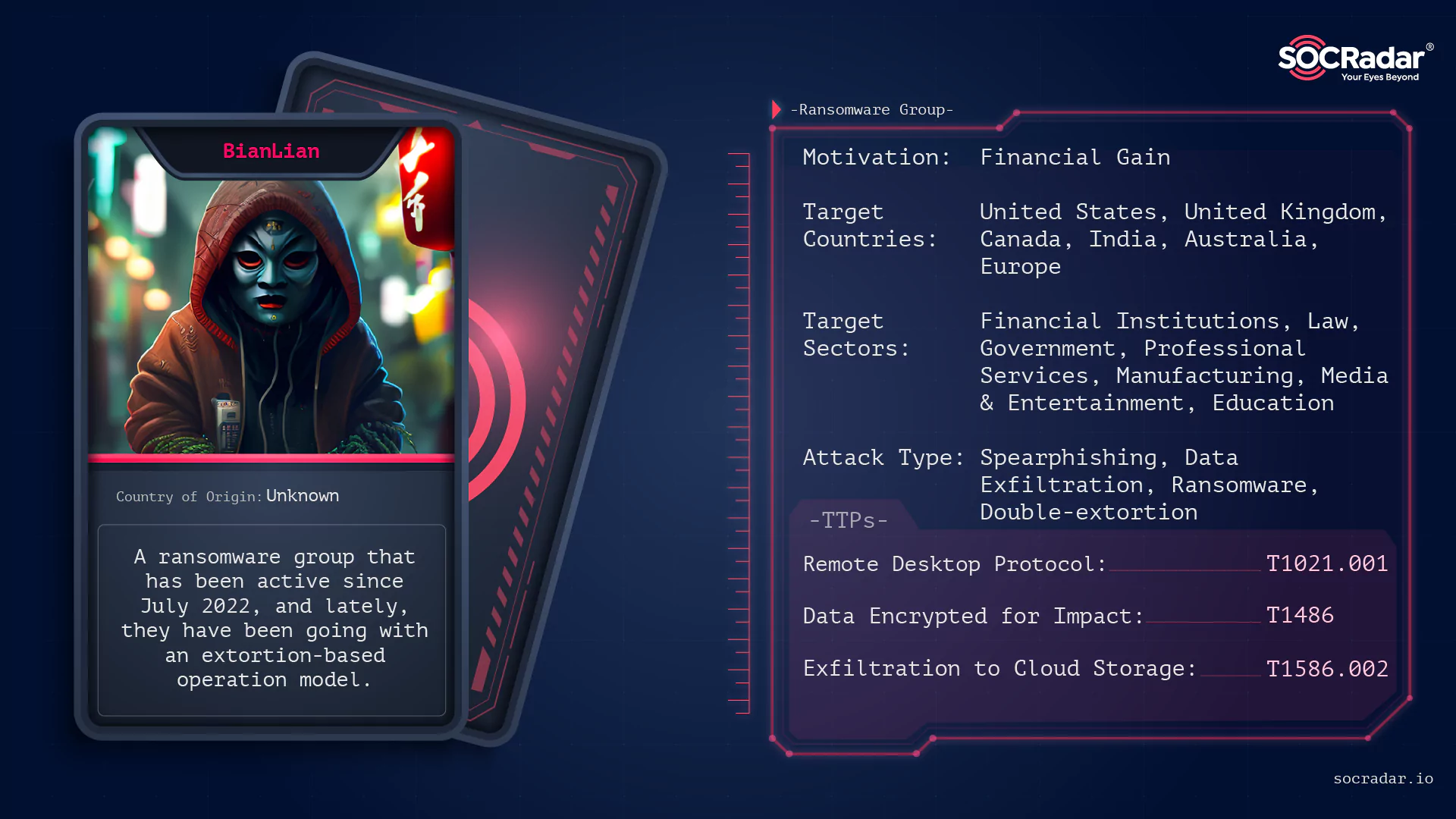
Threat Actor Profile: BianLian, The Shape-Shifting Ransomware Group
Threat Actor Profile: BianLian, The Shape-Shifting Ransomware Group Nowadays, there is a rise in the number of ransomware groups with names that mean something. For example, Yanluowang is a deity in C...

Critical Auth Bypass Vulnerabilities: SonicWall Urges Immediate Patchi...
Critical Auth Bypass Vulnerabilities: SonicWall Urges Immediate Patching for GMS/Analytics SonicWall has issued an urgent security notice regarding critical vulnerabilities impacting their Global Mana...

Joint CISA and FBI Advisory: APT Activity Targeting Outlook Online
Joint CISA and FBI Advisory: APT Activity Targeting Outlook Online In a recent joint advisory, the Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI)...

Critical RCE Vulnerability (CVE-2023-33308) in FortiOS and FortiProxy:...
Critical RCE Vulnerability (CVE-2023-33308) in FortiOS and FortiProxy: Immediate Security Update Required Fortinet has recently addressed a critical Remote Code Execution (RCE) vulnerability that affe...

Microsoft's July 2023 Patch Tuesday Fixes Five Zero-Days, Nine Critica...
Microsoft’s July 2023 Patch Tuesday Fixes Five Zero-Days, Nine Critical Vulnerabilities Microsoft has released the July 2023 Patch Tuesday update, which includes 130 security vulnerabilities and...