Major Cyber Attacks Targeting the Finance Industry
Major Cyber Attacks Targeting the Finance Industry The finance industry is an attractive target for cybercriminals due to the large amount of sensitive data and financial assets at stake. Over the pas...

CISO Guide for Quantum Computing: Risks and Opportunities (Part I)
CISO Guide for Quantum Computing: Risks and Opportunities (Part I) For Chief Information Security Officers (CISOs) in charge of cybersecurity, quantum computing brings its paradox. It is both an oppor...
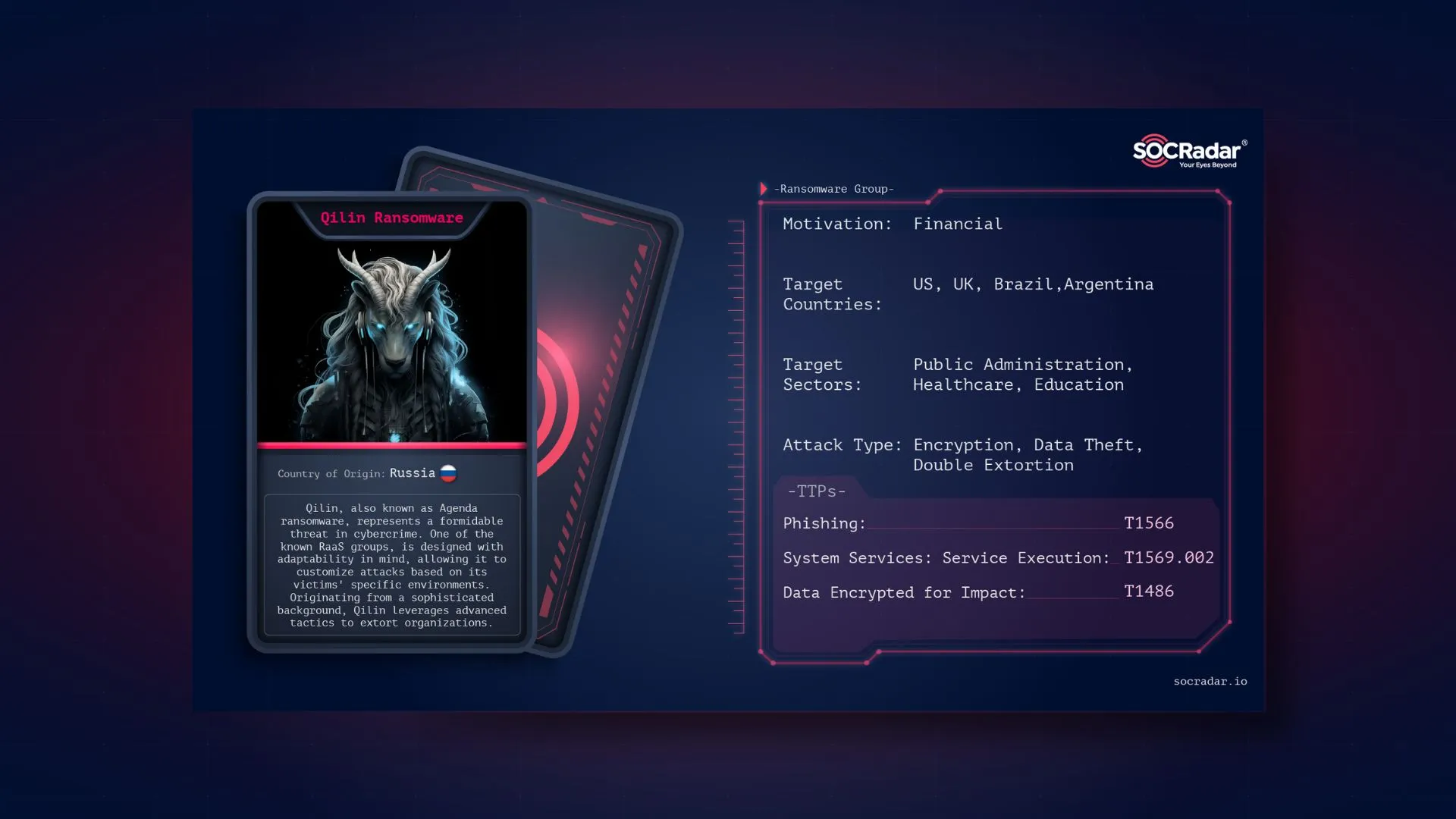
Dark Web Profile: Qilin (Agenda) Ransomware
Dark Web Profile: Qilin (Agenda) Ransomware [June 21, 2024] “Qilin Started Leaking Synnovis Data” Qilin, also known as Agenda ransomware, represents a formidable threat in cybercrime. This ransomware,...
Top 10 Cyber Threats in 2024 - CISO Edition
Top 10 Cyber Threats in 2024 – CISO Edition As organizations prepare for the challenges and opportunities of 2024, the critical importance of cybersecurity preparedness is increasingly apparent. In an...

BogusBazaar Scams 850K Shoppers Through Fraudulent E-Commerce Sites
BogusBazaar Scams 850K Shoppers Through Fraudulent E-Commerce Sites In a recent investigation, researchers exposed an expansive network of fraudulent e-commerce websites that scammed over 850,000 vict...

In the Crosshairs: Top 10 Threat Actors Targeting the USA
In the Crosshairs: Top 10 Threat Actors Targeting the USA As the digital landscape continues to evolve, the United States finds itself at the forefront of emerging cybersecurity challenges. With its c...
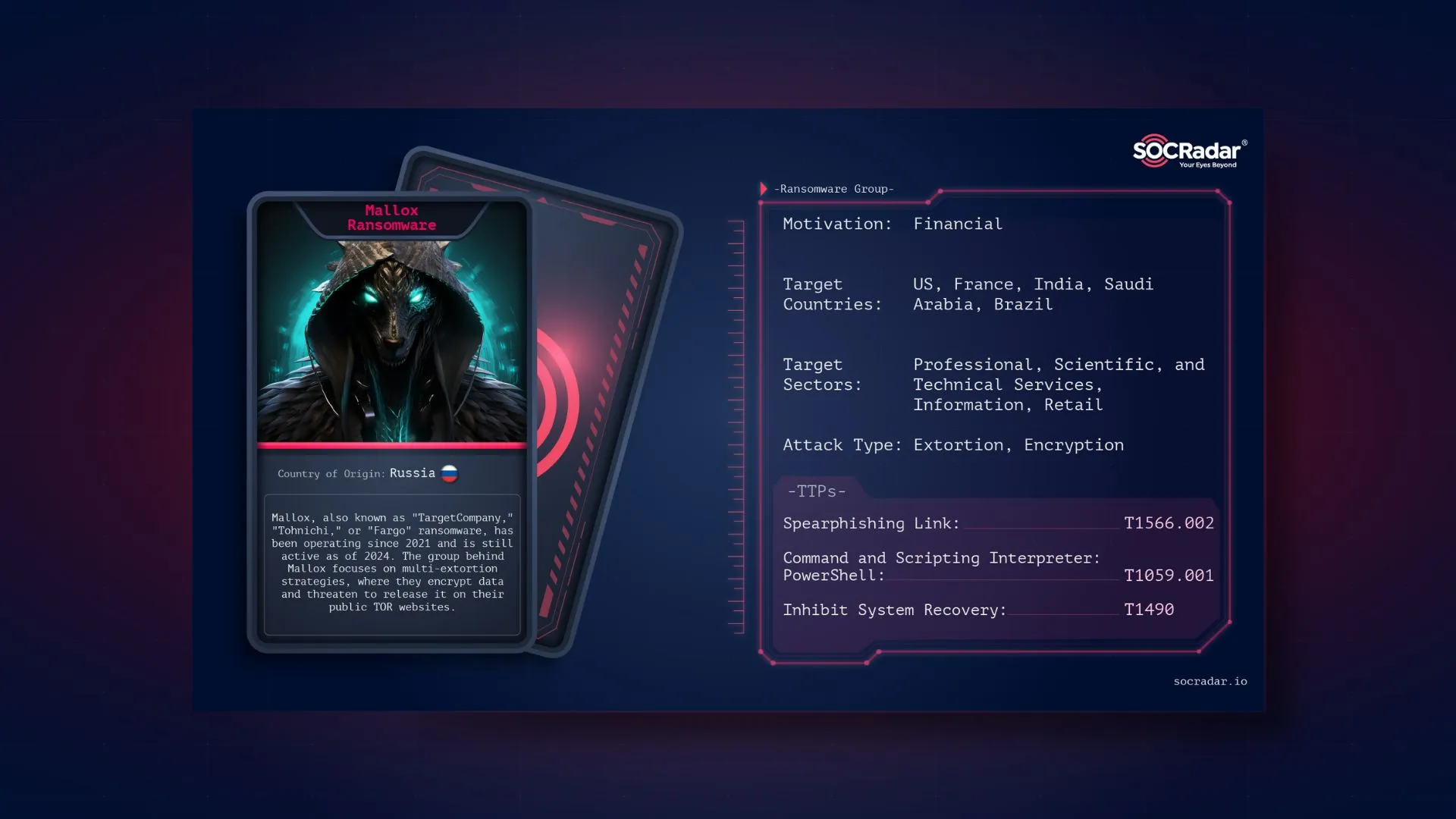
Dark Web Profile: Mallox Ransomware
Dark Web Profile: Mallox Ransomware Mallox, a strain of ransomware and a group with the same name, encrypts its victims’ data and subsequently demands a ransom, typically in cryptocurrency, in return ...

Dark Web Profile: Hunters International
Dark Web Profile: Hunters International Originating in the latter part of 2023, this Ransomware-as-a-Service (RaaS) operation has drawn attention due to its technical lineage and operational tactics r...

Fortifying the Digital Frontier: Australia's Pioneering Cyber Shields ...
Fortifying the Digital Frontier: Australia’s Pioneering Cyber Shields Strategy In 2022, Following the Medibank breach in November, Australia’s Cyber Security Minister Clare O’Neil hi...
Major Cyber Attacks in Review: January 2024
Major Cyber Attacks in Review: January 2024 As January 2024 dawned, the digital atmosphere braced itself for another year’s cybersecurity challenges. Throughout the month, organizations experien...

How to Combat Fraud with Threat Intelligence: Cutting-Edge Pathway
How to Combat Fraud with Threat Intelligence: Cutting-Edge Pathway Organizations have increasingly moved significant portions of their operations online to streamline customer service processes. Inste...

Cybersecurity Predictions: What Trends Will Be Prevalent in 2024?
Cybersecurity Predictions: What Trends Will Be Prevalent in 2024? The evolving digital environment and expanding attack surface demand vigilant adaptation to stay one step ahead of adversaries. Recogn...

EU & US Credit Cards, 750M Indian Mobile Data at Risk; Subway Hit by L...
EU & US Credit Cards, 750M Indian Mobile Data at Risk; Subway Hit by LockBit The SOCRadar Dark Web Team identified critical incidents in the cyber threat landscape over the last week. These includ...

Okta Customer Support System Breach: Lessons in Supply Chain Risks and...
Okta Customer Support System Breach: Lessons in Supply Chain Risks and Cybersecurity How successful are you in ensuring your cybersecurity in the digital environment? Personal and corporate data secur...

LockBit’s New Regulations Sets Minimum For Ransom Demands
LockBit’s New Regulations Sets Minimum For Ransom Demands Recently, the notorious LockBit ransomware group has initiated a significant discussion among its affiliates regarding potential cha...

MGM Resorts Hacked by BlackCat Affiliate, ‘Scattered Spider’
MGM Resorts Hacked by BlackCat Affiliate, ‘Scattered Spider’ A cybercriminal gang employing a combination of impersonation and malware is the prime suspect behind the cyberattack that crippled the ope...

On the Horizon: Ransomed.vc Ransomware Group Spotted in the Wild
On the Horizon: Ransomed.vc Ransomware Group Spotted in the Wild [Update] November 9, 2023: “End of an Era, the Sinking of Ransomed.VC” [Update] October 5, 2023: See the subheading: “RansomedVC De-ano...
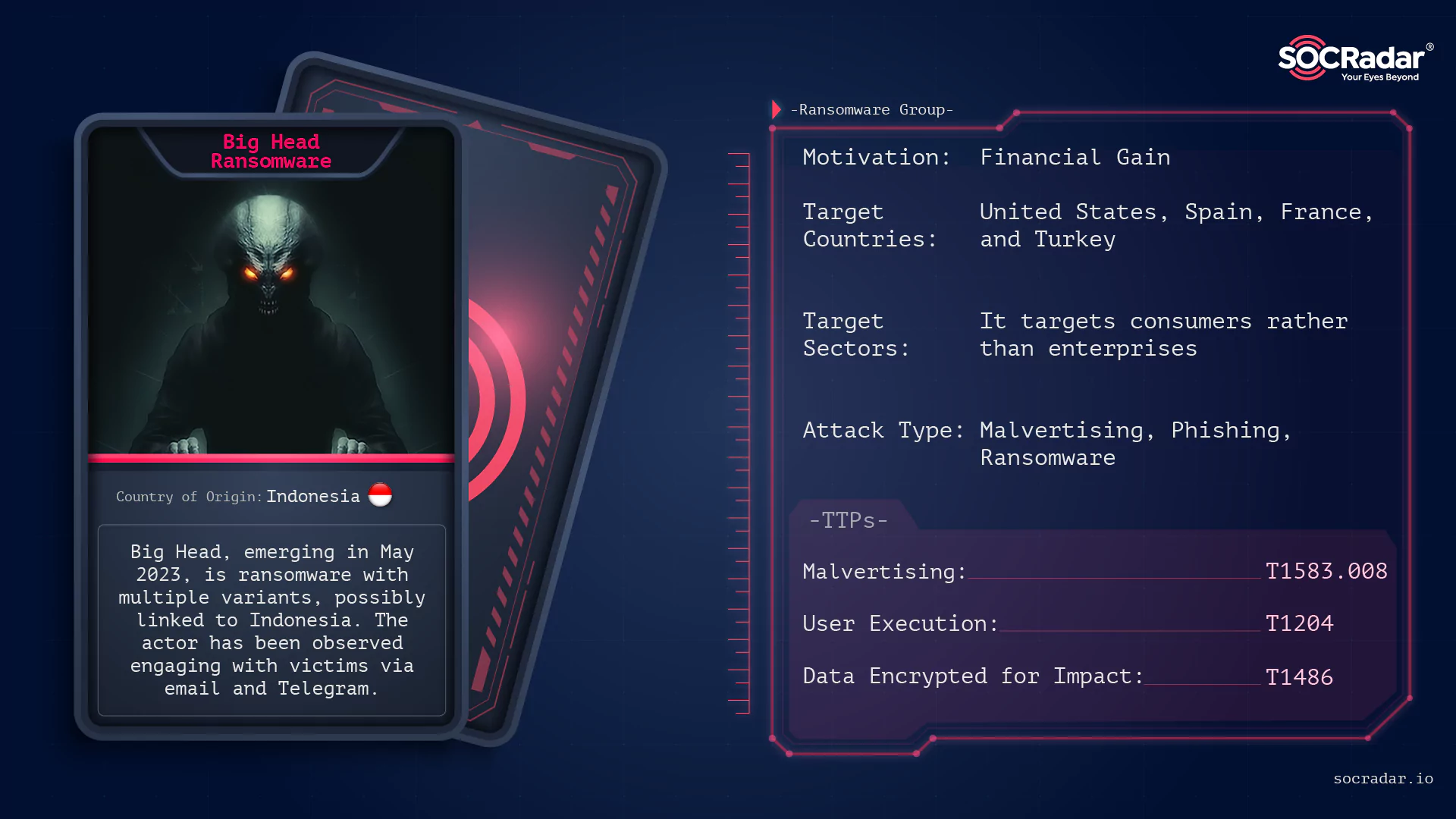
Dark Web Profile: Big Head Ransomware
Dark Web Profile: Big Head Ransomware While ransomware groups such as ALPHV and Lockbit 3.0 continue to hit big companies and make headlines with the large-sized files they steal, there are also actor...

Major Cyberattacks in Review: July 2023
Major Cyberattacks in Review: July 2023 The major cyberattacks of July 2023 included waves of data breaches, affecting both private and public sector entities, including healthcare organizations, fina...

Critical WooCommerce Vulnerability Enables Admin Privileges on WordPre...
Critical WooCommerce Vulnerability Enables Admin Privileges on WordPress Sites (CVE-2023-28121) Researchers have observed an active exploit campaign targeting a newly disclosed vulnerability, CVE-2023...

Ransomware Attacks on Banking Industry
Ransomware Attacks on Banking Industry Due to the escalating illicit pursuits of cybercriminals seeking unlawful financial gains, particular sectors and specific types of cyber attacks tend to gain pr...
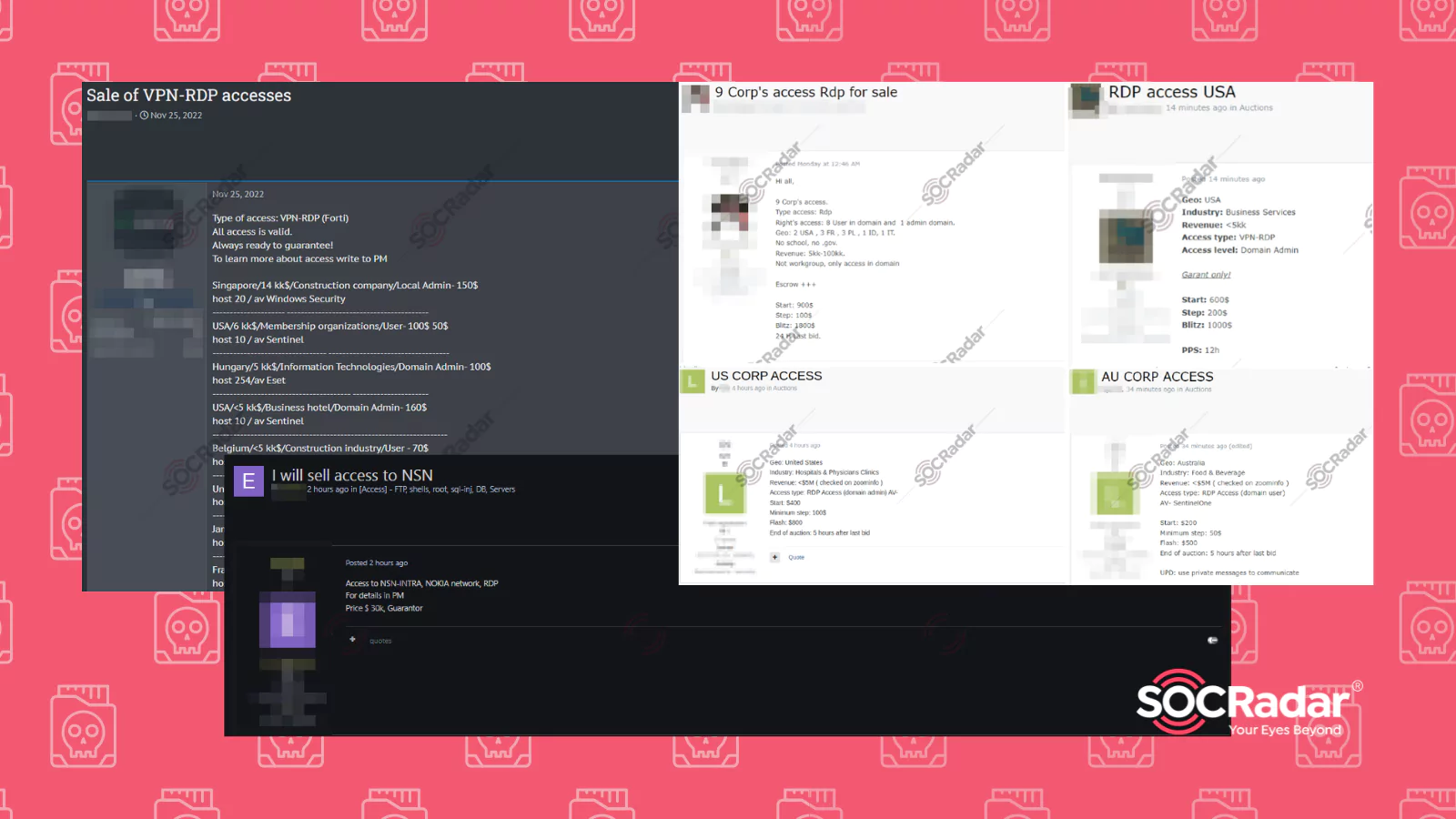
RDP Access Sales on Dark Web Forums Detected by SOCRadar
RDP Access Sales on Dark Web Forums Detected by SOCRadar Remote Desktop Protocol, or RDP, is a protocol developed by Microsoft. It allows the user to control another computer over a network connection...

Exploring the Dark Web Job Market
Exploring the Dark Web Job Market The dark web, notorious for its illicit activities, has evolved into a bustling marketplace for various illegal purposes. It serves as a hub for cybercriminals, offer...

Journey into the Top 10 Vulnerabilities Used by Ransomware Groups
Journey into the Top 10 Vulnerabilities Used by Ransomware Groups Once upon a time, in cyberspace, a menacing threat emerged. It would forever change the landscape of digital security. This threat was...
Cyclops Ransomware: Cross-Platform Threat with RaaS and Advanced Featu...
Cyclops Ransomware: Cross-Platform Threat with RaaS and Advanced Features [Update] August 7, 2023: After officially rebranding as Knight, Cyclops has shared their new stealer named “Knight steal...